1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231
232
233
234
235
236
237
238
239
240
241
242
243
244
245
246
247
248
249
250
251
252
253
254
255
256
257
258
259
260
261
262
263
264
265
266
267
268
269
270
271
272
273
274
275
276
277
278
279
280
281
282
283
284
285
286
287
288
289
290
291
292
293
294
295
296
297
298
299
300
301
302
303
304
305
306
307
308
309
310
311
312
313
314
315
316
317
318
319
320
321
322
323
324
325
326
327
328
329
330
331
332
333
334
335
336
337
338
339
340
341
342
343
344
345
346
347
348
349
350
351
352
353
354
355
356
357
358
359
360
361
362
363
364
365
366
367
368
369
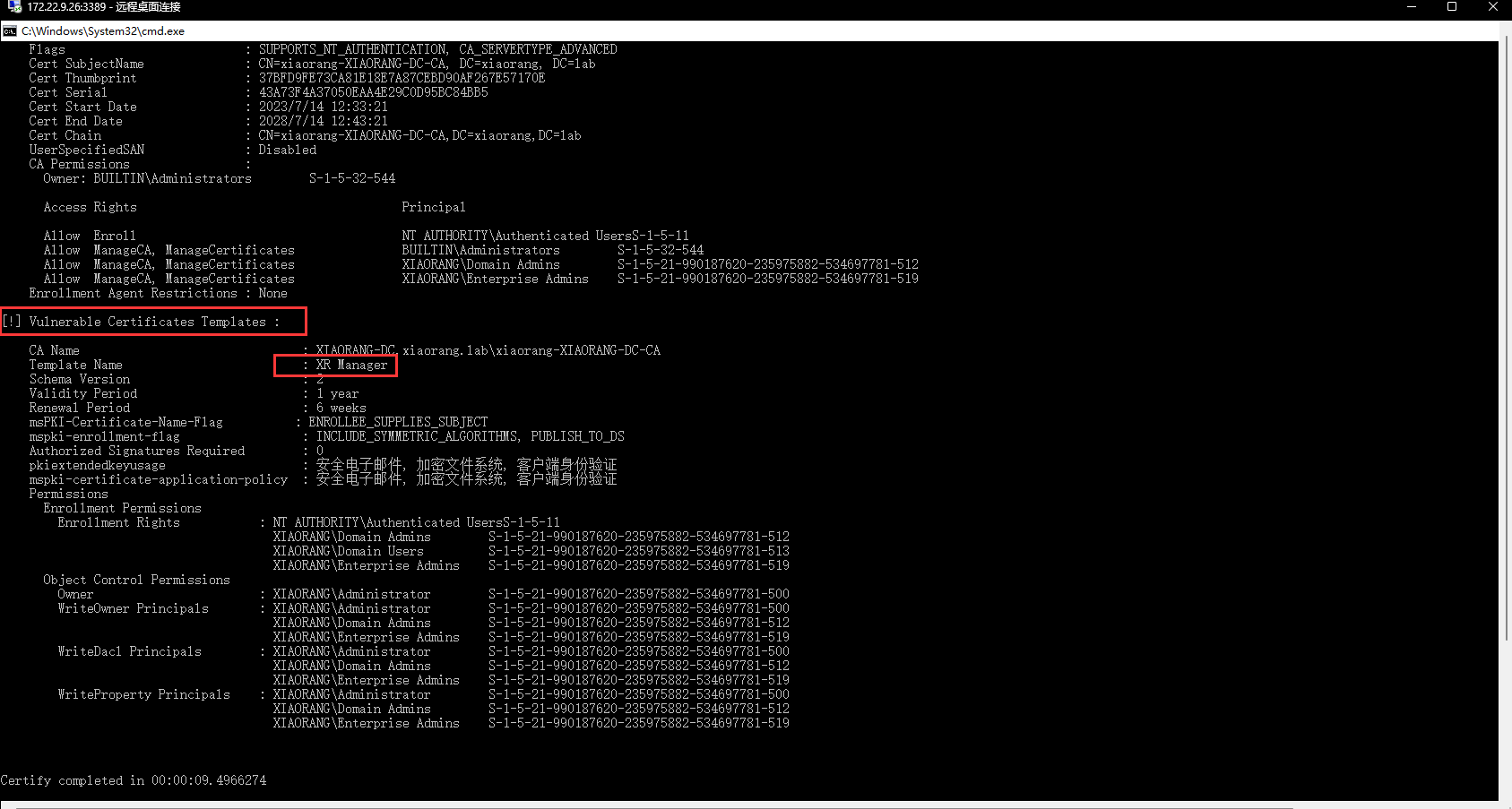
| C:\Users\chenchen\Desktop\hvv>Certify.exe find -u 'liupeng@xiaorang.lab' -password 'fiAzGwEMgTY' -dc-ip 172.22.9.7 -vulnerable -stdout
_____ _ _ __
/ ____| | | (_)/ _|
| | ___ _ __| |_ _| |_ _ _
| | / _ \ '__| __| | _| | | |
| |___| __/ | | |_| | | | |_| |
\_____\___|_| \__|_|_| \__, |
__/ |
|___./
v1.0.0
[*] Action: Find certificate templates
[*] Using the search base 'CN=Configuration,DC=xiaorang,DC=lab'
[*] Listing info about the Enterprise CA 'xiaorang-XIAORANG-DC-CA'
Enterprise CA Name : xiaorang-XIAORANG-DC-CA
DNS Hostname : XIAORANG-DC.xiaorang.lab
FullName : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA
Flags : SUPPORTS_NT_AUTHENTICATION, CA_SERVERTYPE_ADVANCED
Cert SubjectName : CN=xiaorang-XIAORANG-DC-CA, DC=xiaorang, DC=lab
Cert Thumbprint : 37BFD9FE73CA81E18E7A87CEBD90AF267E57170E
Cert Serial : 43A73F4A37050EAA4E29C0D95BC84BB5
Cert Start Date : 2023/7/14 12:33:21
Cert End Date : 2028/7/14 12:43:21
Cert Chain : CN=xiaorang-XIAORANG-DC-CA,DC=xiaorang,DC=lab
UserSpecifiedSAN : Disabled
CA Permissions :
Owner: BUILTIN\Administrators S-1-5-32-544
Access Rights Principal
Allow Enroll NT AUTHORITY\Authenticated UsersS-1-5-11
Allow ManageCA, ManageCertificates BUILTIN\Administrators S-1-5-32-544
Allow ManageCA, ManageCertificates XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
Allow ManageCA, ManageCertificates XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
Enrollment Agent Restrictions : None
[*] Available Certificates Templates :
CA Name : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA
Template Name : User
Schema Version : 1
Validity Period : 1 year
Renewal Period : 6 weeks
msPKI-Certificate-Name-Flag : SUBJECT_ALT_REQUIRE_UPN, SUBJECT_ALT_REQUIRE_EMAIL, SUBJECT_REQUIRE_EMAIL, SUBJECT_REQUIRE_DIRECTORY_PATH
mspki-enrollment-flag : INCLUDE_SYMMETRIC_ALGORITHMS, PUBLISH_TO_DS, AUTO_ENROLLMENT
Authorized Signatures Required : 0
pkiextendedkeyusage : 安全电子邮件, 加密文件系统, 客户端身份验证
mspki-certificate-application-policy : <null>
Permissions
Enrollment Permissions
Enrollment Rights : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Domain Users S-1-5-21-990187620-235975882-534697781-513
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
Object Control Permissions
Owner : XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteOwner Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteDacl Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteProperty Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
CA Name : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA
Template Name : EFS
Schema Version : 1
Validity Period : 1 year
Renewal Period : 6 weeks
msPKI-Certificate-Name-Flag : SUBJECT_ALT_REQUIRE_UPN, SUBJECT_REQUIRE_DIRECTORY_PATH
mspki-enrollment-flag : INCLUDE_SYMMETRIC_ALGORITHMS, PUBLISH_TO_DS, AUTO_ENROLLMENT
Authorized Signatures Required : 0
pkiextendedkeyusage : 加密文件系统
mspki-certificate-application-policy : <null>
Permissions
Enrollment Permissions
Enrollment Rights : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Domain Users S-1-5-21-990187620-235975882-534697781-513
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
Object Control Permissions
Owner : XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteOwner Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteDacl Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteProperty Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
CA Name : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA
Template Name : Administrator
Schema Version : 1
Validity Period : 1 year
Renewal Period : 6 weeks
msPKI-Certificate-Name-Flag : SUBJECT_ALT_REQUIRE_UPN, SUBJECT_ALT_REQUIRE_EMAIL, SUBJECT_REQUIRE_EMAIL, SUBJECT_REQUIRE_DIRECTORY_PATH
mspki-enrollment-flag : INCLUDE_SYMMETRIC_ALGORITHMS, PUBLISH_TO_DS, AUTO_ENROLLMENT
Authorized Signatures Required : 0
pkiextendedkeyusage : Microsoft 信任列表签名, 安全电子邮件, 加密文件系统, 客户端身份验证
mspki-certificate-application-policy : <null>
Permissions
Enrollment Permissions
Enrollment Rights : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
Object Control Permissions
Owner : XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteOwner Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteDacl Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteProperty Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
CA Name : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA
Template Name : EFSRecovery
Schema Version : 1
Validity Period : 5 years
Renewal Period : 6 weeks
msPKI-Certificate-Name-Flag : SUBJECT_ALT_REQUIRE_UPN, SUBJECT_REQUIRE_DIRECTORY_PATH
mspki-enrollment-flag : INCLUDE_SYMMETRIC_ALGORITHMS, AUTO_ENROLLMENT
Authorized Signatures Required : 0
pkiextendedkeyusage : 文件恢复
mspki-certificate-application-policy : <null>
Permissions
Enrollment Permissions
Enrollment Rights : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
Object Control Permissions
Owner : XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteOwner Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteDacl Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteProperty Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
CA Name : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA
Template Name : Machine
Schema Version : 1
Validity Period : 1 year
Renewal Period : 6 weeks
msPKI-Certificate-Name-Flag : SUBJECT_ALT_REQUIRE_DNS, SUBJECT_REQUIRE_DNS_AS_CN
mspki-enrollment-flag : AUTO_ENROLLMENT
Authorized Signatures Required : 0
pkiextendedkeyusage : 服务器身份验证, 客户端身份验证
mspki-certificate-application-policy : <null>
Permissions
Enrollment Permissions
Enrollment Rights : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Domain Computers S-1-5-21-990187620-235975882-534697781-515
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
Object Control Permissions
Owner : XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteOwner Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteDacl Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteProperty Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
CA Name : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA
Template Name : DomainController
Schema Version : 1
Validity Period : 1 year
Renewal Period : 6 weeks
msPKI-Certificate-Name-Flag : SUBJECT_ALT_REQUIRE_DIRECTORY_GUID, SUBJECT_ALT_REQUIRE_DNS, SUBJECT_REQUIRE_DNS_AS_CN
mspki-enrollment-flag : INCLUDE_SYMMETRIC_ALGORITHMS, PUBLISH_TO_DS, AUTO_ENROLLMENT
Authorized Signatures Required : 0
pkiextendedkeyusage : 服务器身份验证, 客户端身份验证
mspki-certificate-application-policy : <null>
Permissions
Enrollment Permissions
Enrollment Rights : NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERSS-1-5-9
XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Domain Controllers S-1-5-21-990187620-235975882-534697781-516
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
XIAORANG\Enterprise Read-only Domain ControllersS-1-5-21-990187620-235975882-534697781-498
Object Control Permissions
Owner : XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteOwner Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteDacl Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteProperty Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
CA Name : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA
Template Name : WebServer
Schema Version : 1
Validity Period : 2 years
Renewal Period : 6 weeks
msPKI-Certificate-Name-Flag : ENROLLEE_SUPPLIES_SUBJECT
mspki-enrollment-flag : NONE
Authorized Signatures Required : 0
pkiextendedkeyusage : 服务器身份验证
mspki-certificate-application-policy : <null>
Permissions
Enrollment Permissions
Enrollment Rights : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
Object Control Permissions
Owner : XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteOwner Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteDacl Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteProperty Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
CA Name : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA
Template Name : SubCA
Schema Version : 1
Validity Period : 5 years
Renewal Period : 6 weeks
msPKI-Certificate-Name-Flag : ENROLLEE_SUPPLIES_SUBJECT
mspki-enrollment-flag : NONE
Authorized Signatures Required : 0
pkiextendedkeyusage : <null>
mspki-certificate-application-policy : <null>
Permissions
Enrollment Permissions
Enrollment Rights : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
Object Control Permissions
Owner : XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteOwner Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteDacl Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteProperty Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
CA Name : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA
Template Name : DomainControllerAuthentication
Schema Version : 2
Validity Period : 1 year
Renewal Period : 6 weeks
msPKI-Certificate-Name-Flag : SUBJECT_ALT_REQUIRE_DNS
mspki-enrollment-flag : AUTO_ENROLLMENT
Authorized Signatures Required : 0
pkiextendedkeyusage : 服务器身份验证, 客户端身份验证, 智能卡登录
mspki-certificate-application-policy : 服务器身份验证, 客户端身份验证, 智能卡登录
Permissions
Enrollment Permissions
Enrollment Rights : NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERSS-1-5-9
XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Domain Controllers S-1-5-21-990187620-235975882-534697781-516
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
XIAORANG\Enterprise Read-only Domain ControllersS-1-5-21-990187620-235975882-534697781-498
Object Control Permissions
Owner : XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteOwner Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteDacl Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteProperty Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
CA Name : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA
Template Name : DirectoryEmailReplication
Schema Version : 2
Validity Period : 1 year
Renewal Period : 6 weeks
msPKI-Certificate-Name-Flag : SUBJECT_ALT_REQUIRE_DIRECTORY_GUID, SUBJECT_ALT_REQUIRE_DNS
mspki-enrollment-flag : INCLUDE_SYMMETRIC_ALGORITHMS, PUBLISH_TO_DS, AUTO_ENROLLMENT
Authorized Signatures Required : 0
pkiextendedkeyusage : 目录服务电子邮件复制
mspki-certificate-application-policy : 目录服务电子邮件复制
Permissions
Enrollment Permissions
Enrollment Rights : NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERSS-1-5-9
XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Domain Controllers S-1-5-21-990187620-235975882-534697781-516
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
XIAORANG\Enterprise Read-only Domain ControllersS-1-5-21-990187620-235975882-534697781-498
Object Control Permissions
Owner : XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteOwner Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteDacl Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteProperty Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
CA Name : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA
Template Name : KerberosAuthentication
Schema Version : 2
Validity Period : 1 year
Renewal Period : 6 weeks
msPKI-Certificate-Name-Flag : SUBJECT_ALT_REQUIRE_DOMAIN_DNS, SUBJECT_ALT_REQUIRE_DNS
mspki-enrollment-flag : AUTO_ENROLLMENT
Authorized Signatures Required : 0
pkiextendedkeyusage : KDC 身份验证, 服务器身份验证, 客户端身份验证, 智能卡登录
mspki-certificate-application-policy : KDC 身份验证, 服务器身份验证, 客户端身份验证, 智能卡登录
Permissions
Enrollment Permissions
Enrollment Rights : NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERSS-1-5-9
XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Domain Controllers S-1-5-21-990187620-235975882-534697781-516
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
XIAORANG\Enterprise Read-only Domain ControllersS-1-5-21-990187620-235975882-534697781-498
Object Control Permissions
Owner : XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteOwner Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteDacl Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteProperty Principals : XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
CA Name : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA
Template Name : LDAPS
Schema Version : 2
Validity Period : 1 year
Renewal Period : 6 weeks
msPKI-Certificate-Name-Flag : SUBJECT_ALT_REQUIRE_DOMAIN_DNS, SUBJECT_ALT_REQUIRE_DNS
mspki-enrollment-flag : AUTO_ENROLLMENT
Authorized Signatures Required : 0
pkiextendedkeyusage : KDC 身份验证, 服务器身份验证, 客户端身份验证, 智能卡登录
mspki-certificate-application-policy : KDC 身份验证, 服务器身份验证, 客户端身份验证, 智能卡登录
Permissions
Enrollment Permissions
Enrollment Rights : NT AUTHORITY\ENTERPRISE DOMAIN CONTROLLERSS-1-5-9
XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Domain Controllers S-1-5-21-990187620-235975882-534697781-516
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
XIAORANG\Enterprise Read-only Domain ControllersS-1-5-21-990187620-235975882-534697781-498
Object Control Permissions
Owner : XIAORANG\Administrator S-1-5-21-990187620-235975882-534697781-500
WriteOwner Principals : XIAORANG\Administrator S-1-5-21-990187620-235975882-534697781-500
XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteDacl Principals : XIAORANG\Administrator S-1-5-21-990187620-235975882-534697781-500
XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteProperty Principals : XIAORANG\Administrator S-1-5-21-990187620-235975882-534697781-500
XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
CA Name : XIAORANG-DC.xiaorang.lab\xiaorang-XIAORANG-DC-CA
Template Name : XR Manager
Schema Version : 2
Validity Period : 1 year
Renewal Period : 6 weeks
msPKI-Certificate-Name-Flag : ENROLLEE_SUPPLIES_SUBJECT
mspki-enrollment-flag : INCLUDE_SYMMETRIC_ALGORITHMS, PUBLISH_TO_DS
Authorized Signatures Required : 0
pkiextendedkeyusage : 安全电子邮件, 加密文件系统, 客户端身份验证
mspki-certificate-application-policy : 安全电子邮件, 加密文件系统, 客户端身份验证
Permissions
Enrollment Permissions
Enrollment Rights : NT AUTHORITY\Authenticated UsersS-1-5-11
XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Domain Users S-1-5-21-990187620-235975882-534697781-513
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
Object Control Permissions
Owner : XIAORANG\Administrator S-1-5-21-990187620-235975882-534697781-500
WriteOwner Principals : XIAORANG\Administrator S-1-5-21-990187620-235975882-534697781-500
XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteDacl Principals : XIAORANG\Administrator S-1-5-21-990187620-235975882-534697781-500
XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
WriteProperty Principals : XIAORANG\Administrator S-1-5-21-990187620-235975882-534697781-500
XIAORANG\Domain Admins S-1-5-21-990187620-235975882-534697781-512
XIAORANG\Enterprise Admins S-1-5-21-990187620-235975882-534697781-519
Certify completed in 00:00:10.6943600
|